Two New Cryptominers to Worry About
Malware designed to mine cryptocurrencies, more often Monero due to the platforms increased anonymity, are increasing in use and sophistication. The malware referred to as crypto miners, or crypto-jacking , use the infected victims CPU resources to mine for cryptocurrencies. The attackers rely on infecting as many devices as possible in order to turn some impressive profits. Researchers at TrendMicro have detected two new crypto miners with each targeting Linux and Windows users respectively. The latest miner to be discovered by researchers has been called KORKERDS. In a blog article published by TrendMicro discovered the strain mining cryptocurrencies on Linux computers. The interesting thing about KORKERDS is that unlike regular crypto miners, the malware employs a rootkit to assist in hiding itself. A rootkit is commonly seen as a program or collection of tools that give the attacker remote access to and control over a computer or other system. Rootkits are also used, as in the case KONKERDS, to prevent detection of the malware.
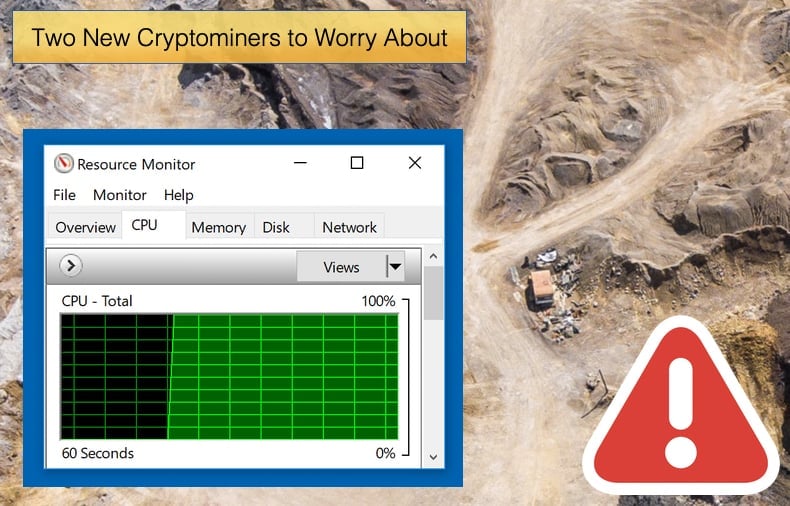
In this instance, the rootkit alters the operating system's behavior and hides the unwanted high CPU usage that is a hallmark of cryptocurrency mining. According to the article, the researchers have not yet identified the way in which the malware infects systems. They are confident, however, that this is not result of an intrusive mass-hacking campaign as has been seen employed by other similar malware strains. Rather it is believed that the attackers are using poisoned Linux applications that have been modified to silently download and install the KORKERDS crypto miners during the installation process of a legitimate app. The app in question is still unknown.
The actual miner can be seen as fairly run of the mill. It is the aforementioned rootkit that got the interest of researchers. Other than been able to mask CPU usage as previously mentioned, the rootkit allows the malware to survive OS reboots and , oddly, to hide the crypto miner's main process from Linux's native process monitoring tools. Researchers found that “The rootkit hooks the readdir and readdir64 application programming interfaces (APIs) of the libc library,” and “The rootkit will override the normal library file by replacing the normal readdir file with the rootkit's own version of readdir.” This malicious version of readdir works by hiding processes named “kworkerds” resulting in the malware's name.
Linux process monitoring tools will still show 100 percent CPU usage, but admins won't be able to see (and kill) the kworkerds process causing the CPU resource consumption problems. Researchers further believe that because KORKERDS is distributed inside legitimate apps the malware might also be a threat to Linux desktop users as well, and not only to servers. With servers been the main target for crypto miners in the vast majority of cases in the past two years, KONKERDS may mark a significant step in the malware's evolution.
Cryptominer Embedded in Windows Installer
The second crypto miners discovered by researchers at TrendMicro detected as “Coinminer.Win32.MALXMR.TIAOODAM” uses multiple obfuscation and packing techniques as part of its routine. The blog article published four days before the Linux miner’s article details how this sneaky piece of malware attempts to avoid detection by pretending to be a Windows installation package. Researchers believe that this miner was specifically designed to avoid detection by employing multiple obfuscation techniques.
According to the researchers, the malware arrives on the victim’s machine as a Windows Installer MSI file a legitimate application used to install software. Researchers say that “Using a real Windows component makes it look less suspicious and potentially allows it to bypass certain security filters.” Further once installed the malware directory contains various files acting as a decoy. Among other things, the installer comes with a script that counteracts any anti-malware processes running on your machine. Last but certainly not least the mining module will be installed on the victim’s machine. Further, researchers discovered the malware has a built-in self-destruct mechanism to cover its tracks. It does this by deleting every file under its installation directory and removes any trace of installation in the system.
TrendMicro has yet been unable to say for certain who is behind the malware spread but the security firm did note the installer uses Cyrillic characters. It would be wrong to automatically assume that a Russian group or individual is behind it as the use of Cyrillic is popular amongst hackers, even those who are not from Russia or her neighbors.
Mining Epidemic
Since the start of 2018 researchers from security firms all over the globe have seen the drastic rise in crypto miners. At one stage researchers believed that it would supplant malware like ransomware entirely. This was not to be as ransomware attacks are still causing financial loss, what did change however was the tactics employed by attackers using ransomware to extort cryptocurrencies. What miners did do was take the initial shotgun approach employed by ransomware, that being to infect as many devices and machines as possible in the shortest amount of time to turn a massive profit.
Researchers have seen attackers hide crypto miners via other legitimate apps such as Adobe Flash updates, routers, and thousands of commercial and governmental sites. The latest real-world attack resulted in a Canadian university having to temporarily kill its entire network after it discovered the network was being used to secretly mine Bitcoin. Giving that research conducted indicates that crypto miners are capable of generating 250,000 USD a month it is little wonder that cybercriminals are pushing the evolution of the malware at a rapid pace.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion