Astaroth Living off the Land
Depending on what circles you associate yourself with the name Astaroth has different meanings. From a character in the popular game Soulcalibur to a Great Duke of Hell according to Christian demonology. The InfoSec has its own identity placed on the name, that being an info-stealing Trojan. In a new campaign, the Microsoft Security Team warns, Asteroth is being distributed in a new campaign using “living off the land” techniques to avoid detection by anti-virus software packages. “Living off the land” tactics involve the attacker exploiting legitimate operating system tools to execute pieces of code, which are not written to disk but reside in memory, which means that the tactic also employs fileless malware execution, meaning a user does not need to actively download the malware in the form by clicking on a malicious link or attachment. Another factor which makes “living off the land” tactics a considerable threat to face is that the system tools exploited are often tools admins use for monitoring systems so they are whitelisted meaning that detection is further hampered as now researchers have to look at tools originally deemed safe.
In a report published by the security team behind Windows Defender ATP, the commercial version of the company's Windows Defender free antivirus. According to Andrea Lelli, a member of the Windows Defender ATP team, questions were raised when they detected a huge and sudden spike in usage of the Windows Management Instrumentation Command-line (WMIC) tool. The tool ships with all the latest versions of Windows, however, the sudden spike was seen as suspicious. Upon closer inspection, it was discovered that a massive malware campaign was underway been distributed by a spam email campaign. If the user clicks the .LNK file it would launch the WMIC tool, and then a plethora of other legitimate Windows tools, one after the other.The use of multiple Windows tools allows for the hacker to download additional code fragments and store them to memory rather than hard disk.
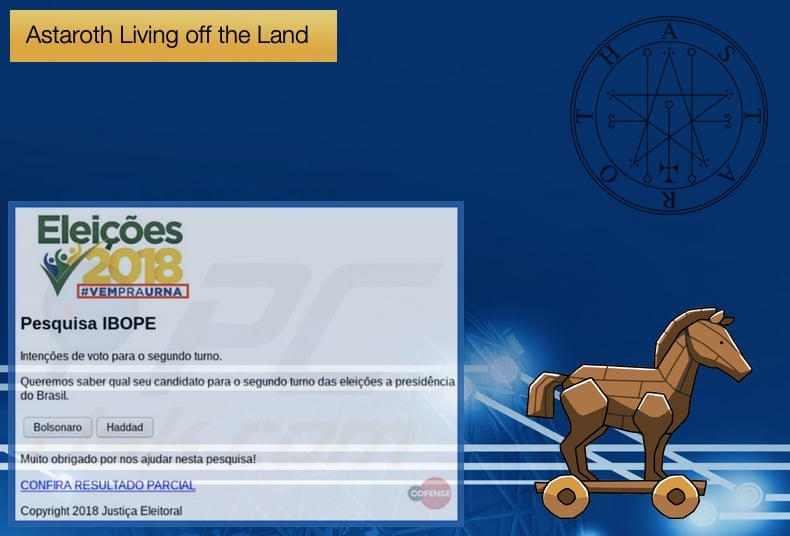
This results in the fileless execution of the malware. Further, by doing this the anti-virus products that scan the hard disk for malware will struggle to detect that a piece of malware is now on the computer and active. The final step of the infection process is the dropping of the Astaroth Trojan. The Astaroth Trojan was first seen in 2017, believed to originate from South America due to the first victims been geographically located on the continent. According to IBM XForce, they summarised the Trojan at the time as,
“This Trojan has been around since 2017 and uses fake invoice emails that seem to be coming from a legitimate vendor using the cam.br domains. PDC estimated that approximately 8,000 of their customers' machines saw attacks of this nature in just one week. Using CloudFlare based URLs, the campaign appears to be targeting potential customers in South America. If a potential victim does not have a South American based IP address, the malware does not attempt to infect the system. The initial payload is a malicious .LNK file that points to the next stage of infection. The infection process uses the Windows Management Instrumentation Console (WMIC) and its command line interface to download and install the malicious payload in a non-interactive mode so that the user is not aware of what is happening. To "hide in plain sight", the malware uses a domain selected from a list of 154 domains within its code and the rest of the URL that points to the payload is added. All of the domains in the list were hosted on CloudFlare. Using a legitimate vendor like this, it is harder for companies to blacklist malicious communication.”
Recently, Astaroth was seen targeting users in Brazil and Europe. In this instance, the malware was spread through a .zip file loaded with malicious attachments and files. Further, the Trojan evaded detection by masquerading as a JPEG, .GIF. Employing a similar tactic to the latest campaign, once the spam email is clicked and downloaded the legitimate Microsoft Windows BITSAdmin tool is used to download the full payload from a command-and-control server. From there the Trojan will get to work stealing information relating to target machines, passwords, key state data and any content on the clipboard. Astaroth can further log keystrokes, intercept calls if installed on a suitable device, and terminate processes.
In the latest campaign, discovered to be active during May and June, almost all the same tools were exploited as in previous campaigns and what separates these campaigns from other campaigns to spread Trojans is that at no point during the attack chain is any file run that is not a system tool. The use of “living off the land” tactics is becoming an increasingly difficult problem for researchers to combat. As they can avoid anti-virus packages that solely rely on scanning hard disks to find malware questions have been raised to the effectiveness of such products.
It is important to note that such malware campaigns are not undetectable and do leave a trail of evidence. It has been suggested that anti-virus packages need to shift from a classic file signature detection mode of operation to a behavioral-driven approach, something which many firms are currently adopting. By adopting this approach so-called “invisible” actions like fileless execution and living-off-the-land techniques where legitimate tools are abused for bad operations can be detected and dealt with. The increase in popularity of fileless malware execution as a tactic will certainly be a driving force behind this change from traditional to behavioral-driven detection.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion