Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Astaroth?
Astaroth is high-risk trojan-type virus. It is typically distributed using spam email campaigns. Criminals send hundreds of thousands of emails that contain deceptive messages encouraging users to open attached files (Microsoft Office documents). Once opened, these files run commands that inject Astaroth into the system.
Following infiltration, Astaroth injects other malicious apps. At time of research, it was used to proliferate a keylogger designed to steal personal data, however, Astaroth is also used to proliferate other malware.
Astaroth trojan overview
After successful system infiltration, Astaroth performs a chain of actions to inject malware, however, the ultimate result is identical: infiltration of other malware. At time of research, Astaroth targeted users mainly from South America. The keylogger proliferated via Astaroth records browsing activity on the Internet Explorer web browser.
To ensure that people will use this browser, the malware terminates Google Chrome and Mozilla Firefox (the most popular browsers) processes if they are executed. In this way, keylogger attempts to trick users into believing that these browsers are not working properly. With no other browsers available, users are thus encouraged to launch Internet Explorer.
The keylogger targets Brazilian banks and businesses. The malware will only record keystrokes when a specific website is opened, however, if cyber criminals gain access to bank accounts, they will certainly attempt to steal funds. Cyber criminals aim to generate as much revenue as possible.
In some cases, however, these people proliferate viruses with destructive purposes (they attempt to cause data and financial loss). Note that the keylogger developers also target business websites. If criminals gain access to the admin panel of a website, they can cause various issues. E.g., they can remove existing content, add malicious content, delete user accounts, etc.
In addition, these people might inject hijacked websites with scripts used to mine cryptocurrency. In this case, each visitor's computer is used as a cryptomining tool when the website is opened.
Many services provide these functionalities legitimately (e.g., GRIDCASH, CoinImp, Coinhive, etc.), however, criminals misuse cryptomining techniques to generate revenue. Furthermore, many regular users (who are not familiar with cyber security) use an identical password for many accounts.
Thus, after gaining access to one account, criminals can often access others (e.g., emails, social networks, etc.). In any case, the keylogger distributed using Astaroth might cause serious financial/data loss and privacy issues.
Although Astaroth currently distributes keylogging malware, in future, criminals might use this trojan to proliferate other viruses, such as ransomware, cryptominers, and so on. Therefore, Astaroth poses a significant threat to any user.
| Name | Astaroth virus |
| Threat Type | Trojan, Password stealing virus, Banking malware, Spyware |
| Detection Names | Avast (Other:Malware-gen [Trj]), BitDefender (Trojan.LNK.Agent.AJC), ESET-NOD32 (LNK/TrojanDownloader.Agent.SM), Kaspersky (Trojan.WinLNK.Agent.uu), Full List (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate victim's computer and remain silent thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software cracks. |
| Damage | Stolen banking information, passwords, identity theft, victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Trojan examples
There numerous trojan-type viruses distributed using spam email campaigns (e.g., Qakbot, ExileRat, Ave Maria, TrickBot, FormBook, etc.).
The developers of these viruses are different and, thus, the functionality might also differ (some gather information, others inject other viruses, and so on), however, all pose a significant threat to your privacy and computer safety. Therefore, removal of this malware is paramount.
How did Astaroth infiltrate my computer?
As mentioned above, Astaroth is proliferated using spam email campaigns. Criminals send emails with malicious attachments - Microsoft Office documents (Excel, Word, etc.). Once opened, these files ask users to enable macro commands. In doing so,, users grant files permission to execute macros that download and install Astaroth into the system.
This, however, is just the start. After successful infiltration, Astaroth performs many actions to inject additional malware. Astaroth downloads and runs a .lnk file leading to an external URL (.lnk files are typically used as shortcuts to access content stored within the system). Astaroth then downloads a .php file from the URL.
This downloaded .php file contains a style sheet with JavaScript embedded within. The JavaScript code generates a random number to select a CloudFlare URL from which the next payload (another style sheet with JavaScript) is downloaded. The second JavaScript places the malware (a keylogger at time of research).
It also randomly selects a download URL and then copies two Windows OS executables ("certutil" [the copy is renamed to "certix"] and "regsvr32") to the "%TEMP%" folder. Those are later used to finish the malware download. The last step is to check the Program Files folder to determine if the Avast anti-virus suite is installed.
If it is not, the script executes a .dll file and terminates itself. Once all these steps are performed, Astaroth finally executes the downloaded malware (keylogger). Again, bear in mind that Astaroth's behavior (list of actions) might change, depending on whether criminals use this trojan to proliferate other malware.
How to avoid installation of malware?
To prevent these computer infections, be very cautious when browsing the internet. Think twice before opening email attachments. Files that seem irrelevant and those received from suspicious/unrecognizable email addresses should never be opened. These should be deleted without reading.
Furthermore, bear in mind that criminals often send deceptive messages claiming that the recipient will gain something free of charge (e.g., the recipient has won a lottery, received a package, someone has transferred money to the recipient's account, etc.). They hope that the recipient will be tricked into opening the attachment. Do not be fooled by this scam.
Having a reputable anti-virus/anti-spyware suite installed and running at all times is also paramount. These tools commonly detect and eliminate malware before it can harm the system. The main reasons for computer infections are poor knowledge and careless behavior.
The key to safety is caution. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
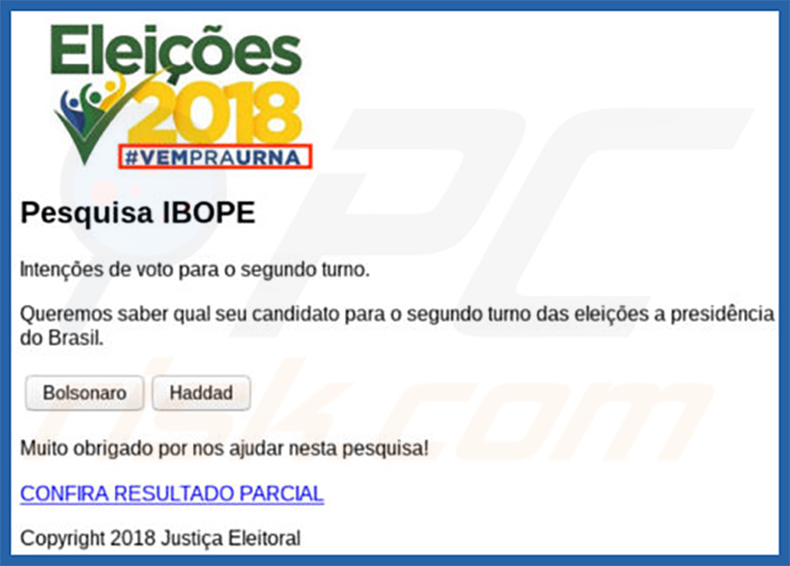
Another deceptive email promoting Astaroth trojan:
Update March 6, 2020 - Updated version of Astaroth is now capable of taking screenshots, blocking victims from using hotkeys (keyboard shortcuts), downloading and executing files, and restarting a computer. Cyber criminals can use this updated version to take screenshots of victim's computing activities.
For example, make screenshots of opened personal, confidential documents, accounts that contain sensitive information, and capture important data in other ways. Also, they can use it to prevent victims from using keyboard shortcuts. For example, they can prevent them from closing enabled/opened windows by blocking the Alt + F4 keyboard shortcut.
Furthermore, now Astaroth can be used to spread various malware (or other programs) by downloading and executing various files. It means that cyber criminals may infect systems with other malicious software like ransomware, cryptominers, etc. One more thing that now can be done with Astaroth is a system reboot.
For example, it is possible that in order for some changes to take affect it would be necessary to restart a computer and now cyber criminals behind Astaroth could easily do that.
Update March 24, 2020 - To bypass existing detections updated Astaroth version does not execute system tools and use Windows Management Instrumentation Command-line (WMIC). Now it hides malicious payloads by abusing ADS (Alternate Data Streams) and loads them by abusing the ExtExport.exe, a legitimate process.
At the moment cyber criminals attempt to spread Astaroth through a spam campaign, by sending emails with a website link in them.
The attack chain begins when recipients open that link which leads to an archive (ZIP) file containing a shortcut (LNK) file that runs obfuscated BAT commands to drop a one-line JavaScript file. Also, Astaroth is capable of detecting installed security software, if it detects one, then it attempts to disable it.
Update May 12, 2020 - The Astaroth trojan uses several methods to connect to its C&C (Control and Command) server. One of its recently observed techniques is by connecting to a YouTube channel and retrieving the text in its description. Within it lies an encrypted URL to the C&C server.
However, as Astaroth employs several methods, even if the channel is taken down by YouTube - the malware can fall back to its other tactics in order to establish contact with the C&C server.
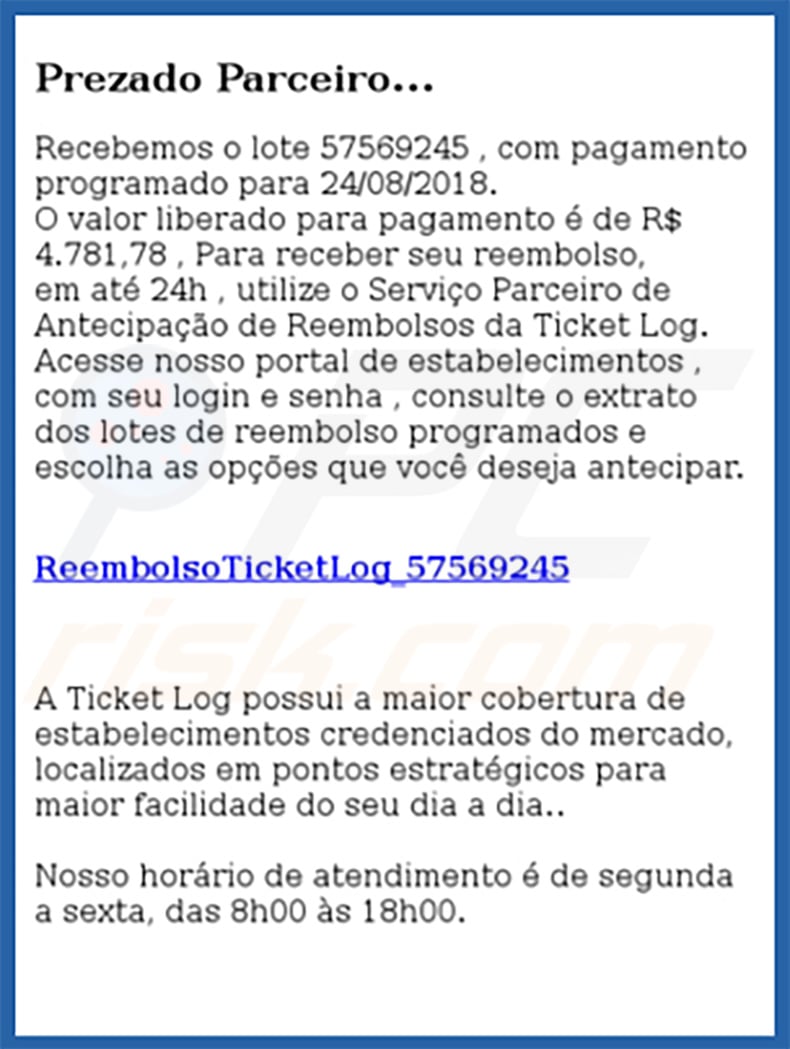
Other examples of emails promoting Astaroth trojan:
Sample 1:
Text presented within:
Subject: Vistoria do Corpo de Bombeiros - Comunicado Importante [22/02/2021] - [10:28:42]
AVISO DE VIGÊNCIA DE DOCUMENTOS VENCIDOS
Comunicado importante Nº 68585607
*Ultimo documento enviado VENCIDO*
Protocolo: Q0QXQCWML1X-00248
Serviço: (Segurança)
inicio automático do protocolo : 22/02/2021 - 10:28:42
Status atual: Regularizar pendente ou VENCIDOAlertamos que o prazo de validade do(s) documento(s) referente ao Termo de Colaboração nº 68585607 celebrado entre Secretaria Municipal dos bombeiros e CENTRO SOCIAL NOSSA SENHORA, para funcionamento da CEI: CR.P.CONV - CNPJ cadastrado para este e-mail ( - ) que devem ser regularizados com urgência está(ão) na situação de vencido. Encaminhe a respectiva documentação à DIR EDUC - DIRETORIA REGIONAL DOS BOMBEIROS
A não regularização dos itens informados pode implicar na suspensão de seu CNPJ em 30 DIAS bem como multa previstos no Art 37 da Lei 10.335 de 19 de Julho de 1988.# Documento Vencimento
05 - AVCB – Auto de Vistoria do Corpo de Bombeiros 12/2020
Providencie a sua regularização, com vistas à continuidade da prestação do serviço.
Atenciosamente,
SMB – Secretaria Municipal dos Bombeiros
Sample 2:
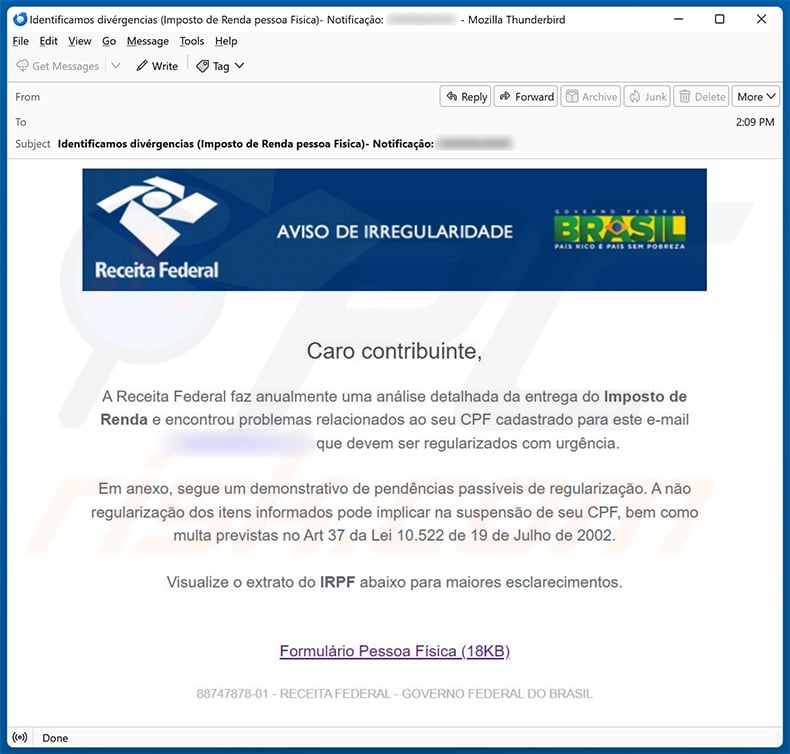
Text presented within:
Subject: Identificamos divérgencias (Imposto de Renda pessoa Fisica)- Notificaçâo: -.
Receita Federal
AVISO DE IRREGULARIDADE
GOVERNO FEDERAL BRASIL
PAIS RICO E PAIS SEM POBREZACaro contribuinte,
A Receita Federal Faz anualmente uma análise detalhada da entrega do Imposto de Renda e encontrou problemas relacionados ao seu CPF cadastrado para este e-mail que devem ser regularizados com urgência.
Em anexo, segue um demostrativo de pendências passíveis de regularização. A não regularização dos itens informados pode implicar na suspensão de seu CPF, bem como multa previstas no Art 37 da Lei 10.522 de 19 de Julho de 2002.
Visualize o extrato do IRPF abaixo para maiores esclarecimentos.
Formulário Pessoa Física (18KB)
88747878-01 - RECEITA FEDERAL - GOVERNO FEDERAL DO BRASIL
Sample 3:
Text presented within:
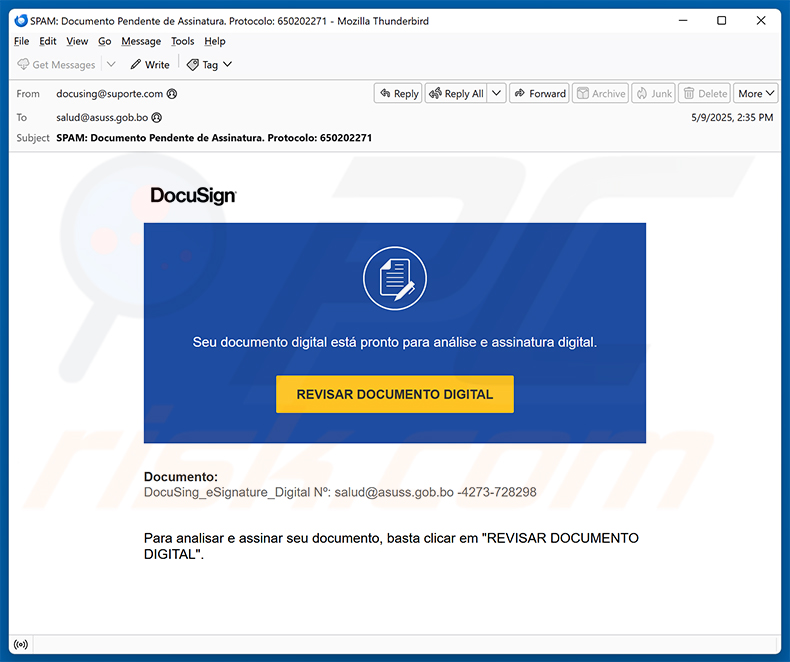
Subject: SPAM: Documento Pendente de Assinatura. Protocolo: 650202271
DocuSign
Seu documento digital está pronto para análise e assinatura digital.
REVISAR DOCUMENTO DIGITAL
Documento:
DocuSing_eSignature_Digital Nº: salud@asuss.gob.bo -4273-728298Para analisar e assinar seu documento, basta clicar em "REVISAR DOCUMENTO DIGITAL".
Sample 4:
Text presented within:
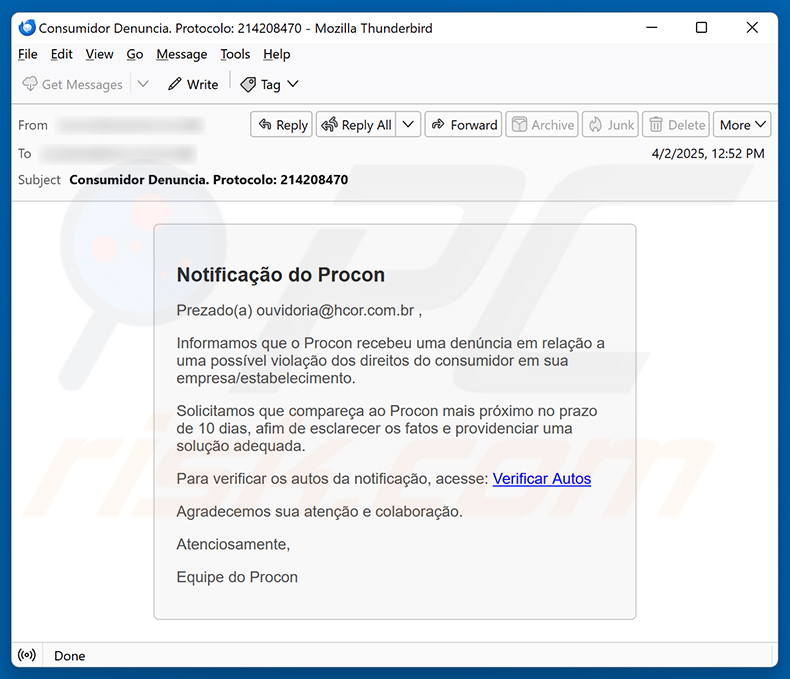
Subject: Consumidor Denuncia. Protocolo: 214208470
Notificação do Procon
Prezado(a) ouvidoria@hcor.com.br ,
Informamos que o Procon recebeu uma denúncia em relação a uma possível violação dos direitos do consumidor em sua empresa/estabelecimento.
Solicitamos que compareça ao Procon mais próximo no prazo de 10 dias, afim de esclarecer os fatos e providenciar uma solução adequada.
Para verificar os autos da notificação, acesse: Verificar Autos
Agradecemos sua atenção e colaboração.
Atenciosamente,
Equipe do Procon
Sample 5:
Text presented within:
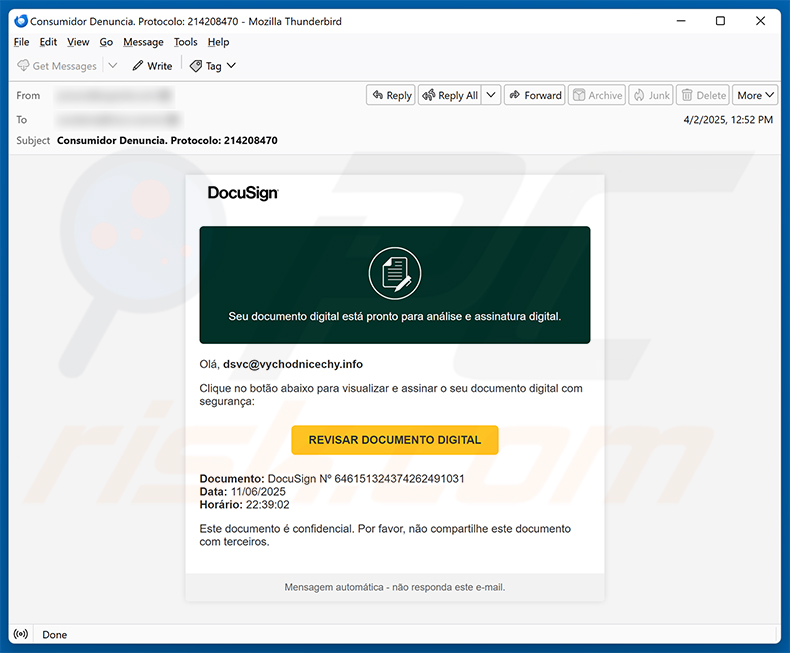
DocuSign
Seu documento digital está pronto para análise e assinatura digital.Olá, dsvc@vychodnicechy.info
Clique no botão abaixo para visualizar e assinar o seu documento digital com segurança:
REVISAR DOCUMENTO DIGITAL
Documento: DocuSign Nº 646151324374262491031
Data: 11/06/2025
Horário: 22:39:02
Este documento é confidencial. Por favor, não compartilhe este documento com terceiros.Mensagem automática - não responda este e-mail.
Update October 14, 2025 - Recently, a new campaign delivering Astaroth has been discovered. In this campaign, the malware exploits GitHub to store its setup information. The attack begins with a deceptive email containing a link to a compressed Windows shortcut (.lnk) file. Opening this file infects a computer with Astaroth.
The malware monitors visits to banking and cryptocurrency websites and captures login credentials using a keylogger. The stolen information is sent to the attacker through Ngrok. If the malware's control servers are unavailable, it can update its settings by hiding data inside images on GitHub. It is important to note that the malicious repositories have already been removed.
Update January 13, 2026 - It has been found that Astaroth now spreads through WhatsApp, mainly targeting users in Brazil. It arrives as a malicious ZIP file sent via WhatsApp messages. When executed, the malware infects the system and automatically sends itself to the victim's contacts, helping it spread further. Its main goal is to steal banking and financial information using trusted messaging platforms.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Astaroth?
- STEP 1. Manual removal of Astaroth malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Astaroth malware, should I format my storage device to get rid of it?
Malware removal rarely requires formatting.
What are the biggest issues that Astaroth malware can cause?
The dangers posed by an infection depend on the malware's capabilities and the cyber criminals' goals. Astaroth is a trojan that can cause chain infections (i.e., download/install additional malware) and possesses data-stealing capabilities. Generally, the presence of such software on devices can result in multiple system infections, severe privacy issues, financial losses, and even identity theft.
What is the purpose of Astaroth malware?
Malware is mainly used to generate revenue. However, cyber criminals can also use malicious programs to amuse themselves, carry out personal vendettas, disrupt processes (e.g., sites, services, companies, etc.), engage in hacktivism, and launch politically/geopolitically motivated attacks.
How did Astaroth malware infiltrate my computer?
Malware is most commonly distributed via spam emails/messages, drive-by downloads, online scams, malvertising, untrustworthy download sources (e.g., freeware and third-party websites, P2P sharing networks, etc.), pirated content, illegal software activation ("cracking") tools, and fake updates. Some malicious programs can self-proliferate through local networks and removable storage devices.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is capable of detecting and eliminating nearly all known malware infections. Note that performing a full system scan is paramount since high-end malicious software tends to hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion