Varenyky Actively Targeting France
Researchers based at ESET, the well-known Slovakian security firm, have published an article detailing the emergence of a new spambot targeting those residing within the borders of France. A spambot is a malicious program designed to collect email addresses, once a list is created spam email is sent to those collected addresses. Most spambots will send malvertising with the intent to collect more information, sometimes credit card information, or redirect users to specific websites. What is of interest to researchers is that the campaign spreading the malware not only distributes a spam bot but has been leveraged to carry out in a sextortion campaign.
Varenyky, the name given to the malware by researchers, targets the users of Orange S.A., a French internet service provider. The first detections by ESET occurred in May 2019, these detections were subsequently verified by ANY.RUN with a twitter post on June 2019. The malware was named in July when researchers witnessed the first sextortion scam been launched. Researchers contend that,
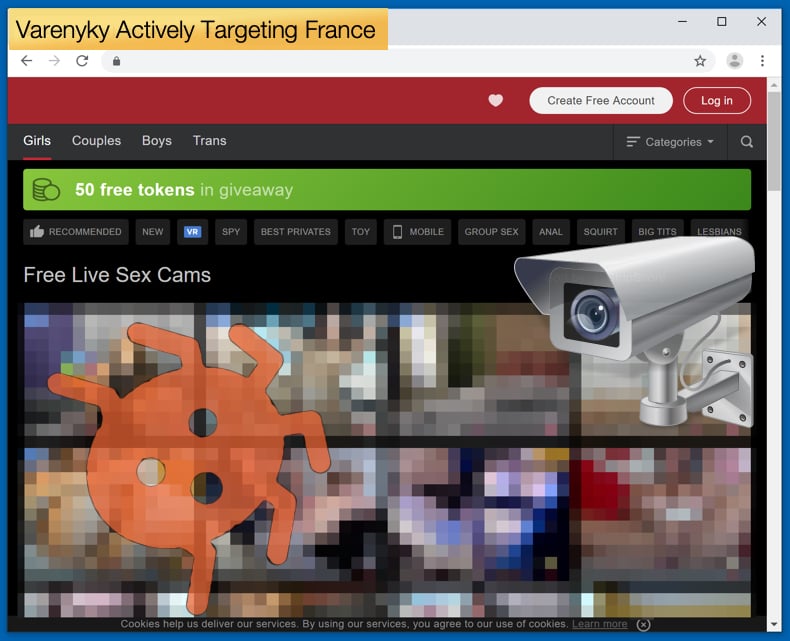
“This spambot is interesting because it can steal passwords, spy on its victims’ screen using FFmpeg when they watch pornographic content online, and communication to the C&C server is done through Tor, while spam is sent as regular internet traffic. This article describes the functionality of the malware.”
How the malware is distributed is not yet exactly known. However, it is believed that the chosen distribution method has been used since the earliest detections of the malware. It was noted that users are initially infected with malware via a malicious attachment. The email sent with the malicious attachment pretends to be a bill, asking for a payment to be made of 491.27 EUR. To further sell the idea that the bill is indeed legitimate the Microsoft Word document tells the user that it requires human authentication to open, in an attempt to convince users of its authenticity. This process of “human verification” serves a double purpose, once the user “authenticates” their humanity it enables macros so that the malware can be unpacked and installed. As a default setting Macros is not automatically enabled within Word, meaning that various malware infections require macros to be enabled to install the malicious payload.
Another point of interest to the researchers is how the malware targets those residing specifically in France. Within the macro used by the malware exists code designed to filter out non-French speakers. This is done by the code executing a function which finds out which language is used on the targets system. The language ID is set by the user upon installation of software like Microsoft Word. The code checks if the value returned is 1036 in decimal (or 0x40C in hexadecimal) and according to the Microsoft documentation this value corresponds to France and the French language. Further by doing this it also excludes users from other French-speaking nations from being infected, as countries like Canada and Belgium have different language IDs used by Word to differentiate between the various regions. For the malware’s authors, this was not enough to guarantee that only French-speaking people within France were targeted. To do this code checks for the keyboard layout used. If these checks are failed the malware will not execute and will display a message stating, “Not available in your country/region. Press OK to terminate this program. No changes to your computer have been made.”
Possibility of Sextortion
If those checks are passed the malware is unpacked and installed. The malware was gone through several variants which have included several changes. This suggests that the malware is under constant development. One of the older changes would scan for words associated with popular adult sites, the feature would scan open windows when looking for specified words. This feature was removed in later versions. Subsequently, another feature was added into later versions which would just scan for the word “sexe”, if found the malware would record the computer’s screen using an FFmpeg executable that it previously would have been downloaded by the malware. The video created by an FFmpeg could then be sent to the hacker’s command and control server (C&C). Researchers stated that,
“These videos could have been used for convincing sexual blackmail; a practice called sextortion. It’s unknown if these videos were recorded out of curiosity by the author(s) of the spambot or with an intention to monetize them through sextortion. Different versions of this malware used different strings to identify itself to the C&C server. One of them was “Bataysk”, which is a Russian city known to have a “monument that shows a man’s hand gripping a nubile female breast”. Another sample identified with “PH”, which probably stands for the initials of a popular pornography website. And another version identified with the string “Gamiani_MON”; Gamiani is a French erotic novel and “MON” probably means “monitoring”.”
Although Varenyky can record a video no evidence of it been used in a sextortion campaign has been seen. That does not mean that the hackers have not attempted such a scam. On July 22, researchers witnessed the start of such a campaign. The scam is of the common variety with an email been sent to the victim demanding an amount be paid into a cryptocurrency wallet within a certain time frame otherwise incriminating and embarrassing information will be posted on Facebook. The scam shows no evidence of incriminating evidence in the form of a video having been recorded at the time of writing. The researchers concluded that despite the many functions the malware has to record victims while visiting adult websites, the hacker has not leveraged these as far as we can tell. Many functions have been added and then quickly removed across many different versions in a short time. This is possibly an attempt to find other ways to monetize the malware in different ways.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion