BadUSB Attack Targets US Hospitality Provider
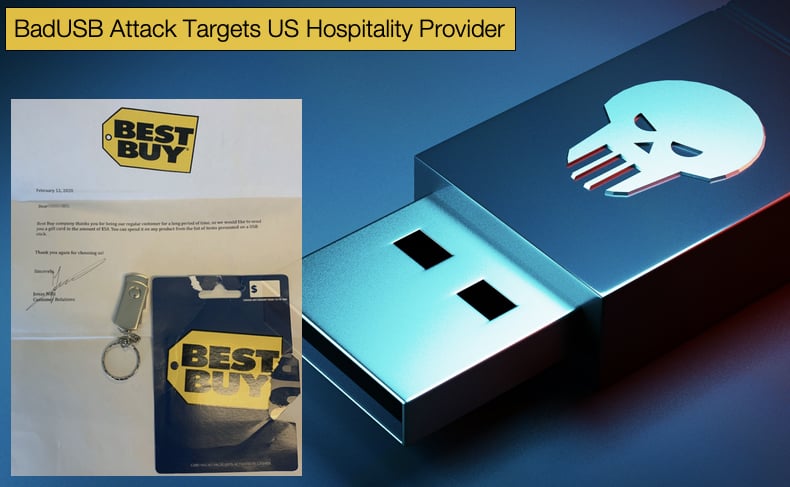
When covering malware incidents it is exceedingly rare to refer to hackers using conventional mail services, sometimes often snidely referred to as snail mail, to carry out attacks. It is equally rare to cover attacks that utilize a malware-laced USB drive to infect computers. These attacks have been labeled BadUSB attacks by the infosec community, while rare they are not unheard of. In a recent report published by security firm Trustwave, a US hospitality provider has been the target of a BadUSB attack.
Given the rarity of these attacks often a quick Google search won’t reveal exactly what such an attack entails or even a solid definition. “BadUSB” has come to be an umbrella term used to describe any type of universal serial bus (USB) firmware attack. A better explanation of such an attack was given in a research paper published by the Canadian Center of Science and Education in 2017, titled “Bad USB MITM: A Network Attack Based on Physical Access and Its Practical Security Solutions”.
The paper with the typically bland title explained that,
“Once “BadUSB” malware occurs, a USB device can emulate a keyboard and imitate a logged-in user (Wang et al., 2013). For example, a Plug-and-play USB can pretend keyboard or mouse input to launch the hidden attack code automatically when attaching to a computer. The infected USB device can also spoof the network card and alter the DNS setting in order to redirect the traffic. In addition, a modified USB flash drive or external HDD is able to launch a small virus and infect the computer’s OS when the device detects that the computer is booting (Moore et al., 2014).”
When BadUSB attacks entered the public’s attention in 2014 not many security software applications could effectively deal with the threat let alone scan the malicious USB drive. This situation has changed with better security measures in place, however, given the rarity of such attacks the general public is not as informed about them when compared to spam email s been used to distribute malware. This, in turn, means that some hackers believe that it may be a more effective distribution method for targeted attacks. In the latest attack detailed by Trustwave the unnamed company, for confidentiality reasons, received a letter via regular post which contained a USB thumb drive along with a fake BestBuy gift card and letter. The letter instructed the receiver to insert the thumb drive into a computer to access a list of items the gift card could be used for.
The reality of the situation was far different. Contained on the thumb drive was malware typically seen in other BadUSB attacks that emulated a keyboard. The emulated keyboard then simulates keypresses to launch a series of automated attacks via PowerShell. Once inserted and the malware executes, a larger file is downloaded via PowerShell commands. The larger file is hosted on a website and then installed on the victim’s machine. The larger file is a JavaScript-based bot. These bots are often used in the creation of Chatbots seen on numerous websites today. Hackers, however, use the technology for far more malicious aims.
Its malware but what exactly is it?
While much of the malware’s infection chain is known, very little is known about the third and final payload. This payload seems to be the meat and potatoes of the entire campaign but it is an unknown strain of malware. Researchers could not find a similar strain during their initial analysis to compare the found one too. The belief is that it is a custom-built strain but even that cannot be said for certain. This is far from a desirable outcome but further analysis will hopefully reveal what the malware does. Despite not knowing what the malware is researchers warned that
“In summary, once a USB controller chip is reprogrammed to unintended use (in this case as an emulated USB keyboard) these devices could be used to launch an attack and infect unsuspecting users’ computers without them realizing it. These types of USB devices are widely known and used by security professionals…The fact that they are also cheap and readily available to anyone meant that it was just a matter of time to see this technique used by criminals "in the wild." Since USB devices are ubiquitous, used, and seen everywhere, some consider them innocuous and safe. Others can be very curious about the contents of an unknown USB device. If this story teaches us anything, it's that one should never trust such a device.
It would seem that another thumb drive had been sent out as a sample of the malware was uploaded to VirusTotal. Further analysis was conducted by Michael Yip and Kaspersky Labs analyzed the uploaded sample and determined FIN7 to be behind the campaign. The known threat group which targeted mainly companies carried out attacks that potentially made off with millions of dollars’ worth of assets, often including stolen credit card details. Once assets are turned into money, the funds are sent to offshore accounts. The group is known to work in conjunction with another well-known APT group Carbanak with both sharing assets.
Fin7 members were arrested in 2018 but this did not seem to slow the group’s operations in any meaningful way. Since the arrests, numerous spear-phishing campaigns have been attributed to the group which targeted over 130 different companies. Further, it was discovered that the group created a fake company that claims to be a legitimate cybersecurity vendor with offices across Russia. The company website is registered to the server that Fin7 uses as a Command and Control center (C&C). The fake business has been used to recruit unsuspecting freelance vulnerability researchers, program developers, and interpreters through legitimate online job sites. The group, like other well established hacking groups, has proven to be as hard as the mythical Hydra to kill.
Bash Bunnies
To illustrate how rare BadUSB attacks are the last known incident occurred in 2018. The incident was analyzed by Kaspersky who labeled the attack DarkVishnya and involved the attackers bring a malicious device into a victim’s office and connecting it to the corporate network. Through that device, they can remotely explore the company’s IT infrastructure, intercept passwords, read information from public folders, as well as have been seen from the above example to execute commands and install malware. This incident in particular targeted Eastern European banks using three devices in particular, cheap laptops, raspberry pi boards, and bash bunnies. The last, bash bunnies deserves particular mention as they are cheap and freely available on hacker forums, they are often disguised as thumb drives but are far more malicious. Simply put these are miniaturized computers complete with USB interface designed to carry out malware attacks.
The subsequent result of this campaign was the estimated loss of tens of millions of dollars suffered by the victims. While this campaign targeted banks, the methods employed are equally useful at targeting companies. The evolution from DarkVishnya to the latest Fin7 campaign is not yet clearly seen. However, one difference is clear and that is how the malware loaded devices are hooked up to the network. In the DarkVishnya campaign cybercriminals entered the organization’s building under the guise of a courier, job seeker, or any other person commonly seen on the premise, and connected a device to the local network. In one instance a device was hooked up to a USB port found in a meeting room. In the latest attack the malicious devices were sent by mail and reliant on an employee inserting the malicious drive, there is far less risk involved in this method but requires far more patience and is reliant on an employee playing ball so to speak.
Defending against these attacks can be hard as many USB devices do not have unique identifiers added during manufacturing. By adding identifiers whitelists of devices could be added allowing for safer use. Given the universality of these devices, an untold number could be floating around waiting for a victim to simply insert the device. It is recommended that users disable automatic device installation as one countermeasure. Further, David Zou advises the following tips for Windows users:
- The best way to prevent unwanted changes to Windows system files is to use a Limited user account instead of an Administrator account. By doing this, Windows will always prompt you for the Administrator password before a program can get administrator access to your computer. This will prevent generic BadUSB attacks, as they will need your Administrator password.
- Avoid using wireless keyboards as you are broadcasting your keystrokes and anyone in range can pick them up.
- If you have a wireless keyboard and mouse combo receiver and are not using the keyboard, consider uninstalling the driver for the keyboard and disabling it. This will prevent an attacker from sending keyboard input to your computer. (Windows does not allow you to disable Keyboard devices in Device Manager while they are installed. You will need to use the group policy, mentioned above, to prevent Windows automatically installing the keyboard drivers. Uninstall the keyboard and only then will you be able to disable the keyboard device.)
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion