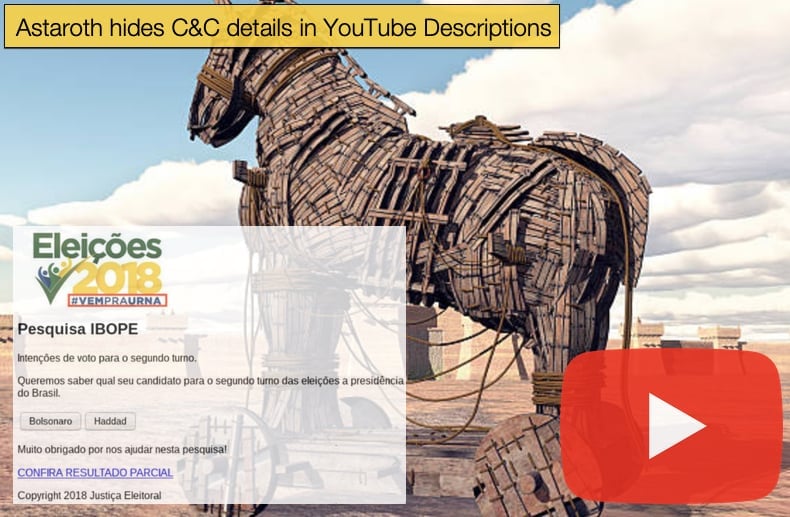
Astaroth hides C&C details in YouTube Descriptions
In the two years since its discovery Astaroth, been seen in the wild for the first time in September 2018, has continued to evolve and add features, showing the prowess of its developers. The info-stealing trojan has now been seen to have received a significant update, boasting, even more, features designed to help it evade detection and analysis. The latest campaign seen distributing the malware is confined to Brazil only, for the time being, but previous campaigns had targeted users in Europe. However, the majority of activity in the past has been confined to the South American nation.
Discovered by IBM’s X-Force the malware was described as,
“This Trojan has been around since 2017 and uses fake invoice emails that seem to be coming from a legitimate vendor using the cam.br domains. PDC estimated that approximately 8,000 of their customers' machines saw attacks of this nature in just one week. Using CloudFlare based URLs, the campaign appears to be targeting potential customers in South America. If a potential victim does not have a South American based IP address, the malware does not attempt to infect the system. The initial payload is a malicious .LNK file that points to the next stage of infection. The infection process uses the Windows Management Instrumentation Console (WMIC) and its command line interface to download and install the malicious payload in a non-interactive mode so that the user is not aware of what is happening. To "hide in plain sight", the malware uses a domain selected from a list of 154 domains within its code and the rest of the URL that points to the payload is added. All of the domains in the list were hosted on CloudFlare. Using a legitimate vendor like this, it is harder for companies to blacklist malicious communication.”
For the most part, the malware has continued on the same path, focused namely on stealing information, since its discovery subsequent feature additions have been focussed on making the malware harder to detect and analyze. The latest campaign analyzed by Cisco Talos continues this development path in a few novel, but not necessarily new, ways. In summary, the latest campaign has included COVID-19 lures to further aid in the distribution of the malware, a tactic adopted by numerous other malware developers to take advantage of the current crisis. Of particular interest to security, researchers were the new anti-analysis and anti-sandboxing features hidden within a maze of obfuscated code as well as innovative use of YouTube channel descriptions for encoded and encrypted command and control communications implemented by the malware.
As to how the malware is distributed, it still relies on spam email campaigns, living off the land tactics, and various other fileless execution methods. Living off the land is seen to typically involve the attacker exploiting legitimate operating system tools to execute pieces of code, which are not written to disk but reside in memory, which means that the tactic also employs fileless malware execution, meaning a user does not need to actively download the malware in the form by clicking on a malicious link or attachment.
While no changes were seen to the methods of distribution, as mentioned above the new anti-analysis and anti-sandboxing features are most definitely new. These new additions will check to see if the malware has found itself on a PC rather than a sandbox environment used by researchers for malware analysis. This is done primarily to prevent researchers from developing rules for security products to block the malware. If not analyzed the malware has a chance of being detected as software and not malware. Which in turn means that the malware can perform its task of stealing information for longer periods of time, creating more earning potential for selling information on the Dark Web. As the researchers pointed out in the report,
“Astaroth is evasive by nature and its authors have taken every step to ensure its success…They have implemented a complex maze of anti-analysis and anti-sandbox checks to prevent the malware from being detected or analyzed. Starting with effective and impactful lures, to layer after layer of obfuscation, all before any malicious intent was ever exposed. Then it finally proceeds through a rigorous gauntlet of checks for the tools and techniques of both researchers and sandbox technologies alike. This malware is, by design, painful to analyze,”
Hidden Command and Control Servers
The next additional feature that was of special interest is the developers using a cunning tactic to hide command and control (C&C) servers in YouTube descriptions. This allows the operators to keep communication channels open as security firms will look to block the communication between the infected machine and server, thus preventing the exfiltration of data. In the case of Astaroth, the URL associated with a C&C server is hidden in the description associated with a particular YouTube channel. Once the malware infects a PC it will seek to connect with a YouTube channel containing one of these descriptions and retrieve it. The description itself is encrypted with base64-encoded text with the URLs of its command and control server hidden within. After decoding the text, Astaroth connects to these URLs to receive new instructions and to send stolen information for future storage.
This tactic is not new and has been used in the past, however, it is not commonly seen. Perhaps one of the first instances of the tactic been detected in the wild involved a malware strain known as Janicab in 2015 which also used encoded messages on YouTube to try and keep communications up and not easily detected. In this instance, the encoded message was placed in the comments section. The malware would search for the number of comments that contained the message “our (.*)th psy anniversary” and then would apply a few maths operators to get the URL.
Another more recent example of this tactic dates to 2019, with a campaign seen distributing Stantinko a botnet which added a crypto mining module in the detected campaign. According to researchers,
“CoinMiner.Stantinko doesn’t communicate with its mining pool directly, but via proxies whose IP addresses are acquired from the description text of YouTube videos…The description of such a video consists of a string composed of mining proxy IP addresses in hexadecimal format. For example, the YouTube video seen in Figure 1 has the description “03101f1712dec626“, which corresponds to two IP addresses in hexadecimal format – 03101f17 corresponds to 3.16.31[.]23 in decimal dotted-quad format, and 12dec626 is 18.222.198[.]38. As of the time of writing, the format has been slightly adjusted. The IP addresses are currently enclosed in “!!!!”, which simplifies the very process of parsing and prevents possible changes of the YouTube video HTML structure turning the parser dysfunctional.”
Astaroth has one more trick up its sleeve to help ensure communication between infected machines and the C&C server remains open. The hiding of the URL in the address is one of three redundancy measures incorporated in the code. The practical implication of this is that if YouTube takes down channels with the hidden URLs there are two more methods that the malware can use, namely a fall-back C&C channel. Researchers concluded that the measures adopted in the latest campaign reinforce the malware operator's key aims, namely to remain undetected for as long as possible to steal information which can turn a profit either by being sold off or several other ways. Further, the malware is under constant development showing the developer's desire to keep the malware constantly improving so that it will continue to carry out the desired task efficiently.
For the time being the operators have been careful to keep the campaigns geographically limited to Brazil. This also helps keep operations agile and stealthy preventing the number of security firms trying to analyze the malware down to a minimum. However, if decided to, the malware can be distributed in much larger campaigns targeting users around the world. If that is the case defenders need to be prepared to mitigate the threat posed by Astaroth. Researchers further noted as a future warning,
“These financially motivated threats are continuing to grow in sophistication, as adversaries are finding more ways to generate large sums of money and profits. Astaroth is just another example of this and evasion/anti-analysis are going to be paramount to malware families success in the future. Organizations need to have multiple layers of technology and controls in place to try and minimize its impacts, or at the least facilitate fast detection and remediation. This would include security technologies covering endpoint, domain, web, and network. By layering these types of technologies organizations will increase the likelihood that evasive, complex malware like Astaroth, can and will be detected.”
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion