eCh0raix Ransomware Activity Surges
The previous two weeks have seen a surge in eCh0raix activity. Active from roughly June 2019 the eCh0raix ransomware gang has targeted mainly vulnerable QNAP NAS devices. Recently detected activity suggests that this preferred target has not changed. QNAP NAS are network-attached storage systems that can be simply defined as hard drives that constantly connect to the Internet. They are often used as backup hubs by businesses to store vital data essential to business operations. This makes the device built by QNAP a target for ransomware gangs due to the data held on the device. NAS devices have been targeted in the past by attackers to distribute Internet of Things malware.
eCh0raix’s recent surge in activity can be attributed to the recent public disclosure of three critical vulnerabilities which impact QNAP devices. Henry Huang discovered the flaws in 2019 and stated in a Medium post,
“…I discovered multiple vulnerabilities in QNAP PhotoStation and CGI programs. These vulnerabilities can be chained into a pre-auth root RCE. All QNAP NAS models are vulnerable, and there are ~312K vulnerable QNAS NAS instances on the Internet (statistical prediction). These vulnerabilities have been responsibly reported, fixed, and assigned CVE-2019–7192 (CVSS 9.8), CVE-2019–7193 (CVSS 9.8), CVE-2019–7194 (CVSS 9.8), CVE-2019–7195 (CVSS 9.8). This article is the first public disclosure, but only 3 of the vulnerabilities are disclosed, because they’re enough to achieve pre-auth root RCE.”
The terse tone and technical language make reading Henry Huang’s article difficult for those not so technically minded. In summary, the three disclosed vulnerabilities reside within QNAP’s Photo Station, an album app that comes preinstalled on QNAP devices. This app comes preinstalled on approximately 80% of the devices produced by the manufacturer. Researchers have provided several estimates regarding the number of affected devices, Huang’s statistical prediction is that over 300,000 devices are affected but by using Shodan the number may be as high as 450,000.
Either number represents a target opportunity to any ransomware gang that is nearly impossible to ignore. If properly exploited CVE-2019-7192 allows authentication protocols to be bypassed, CVE-2019-7194 allows for the inserting of malicious code via the app’s PHP session, and CVE-2019-7195 allows for the installation of a web shell on unpatched devices.
It is important to note that the vulnerabilities received a patch in November 2019. QNAP released an advisory which provides information on how to patch devices if they have not been patched already as well as other security information to help prevent further attacks. As there has been a spike in ransomware related activity targeting NAS devices attempting to make use of the flaws discussed above, owners of such devices are advised to disconnect their devices if they are unable to patch right away. Further, it is advised that user passwords are changed as the ransomware gang has been known to use brute-force attacks in order to gain access to the hard drives.
Activity Spike
eCh0raix activity has been on the quiet side since a freely available decryptor was made available in August 2019. While on the quite side they never disappeared, even developing a newer version of the ransomware which is yet to be decrypted, making it even more vital for owners of targeted devices to install the already released patch. Another reason for the group's decline in activity may be as a result of fierce competition between ransomware gangs which target NAS devices. The competition includes Muhstik and QSnatch both of which have developed reputations for encrypting data on QNAP NAS devices. QSnatch in particular pulled off an attack that infected approximately 7,000 devices in Germany alone. Competition amongst rival ransomware gangs is becoming fiercer, especially amongst those with unique targets and tactics for targeting those targets. eCh0raix, named due to string found in the code, has historically used two main methods of distribution, namely the scanning for vulnerable devices and brute-force attacks in order to gain access. From recent reports, it appears that the ransomware gang sees no reason to change their tactics.
After ZDNet published their coverage of the vulnerabilities detailed above they started receiving support requests from desperate QNAP NAS owners looking for a way to recover files that have been encrypted by a mysterious ransomware. Upon examination, the ransomware in question was determined to be eCh0raix. These support requests were deferred to Bleeping Computer’s ransomware forum topic. Over the last two weeks, a steady stream of users began reporting that they had been infected, however, recently the number of users reporting a potential infection has spiked rapidly. This spike in activity has been confirmed by both a Bleeping Computer article and requests made to the ID Ransomware website.
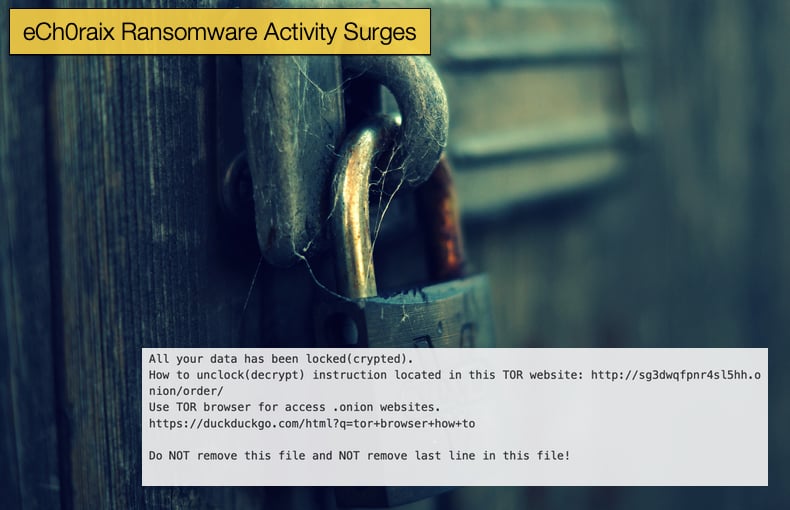
As to recent spikes in activity, there has been no evidence released to the public that the disclosure of the flaws is the definitive cause. However, it can be safely assumed that the disclosure and the spike in activity, which both happened recently, cannot be attributed to pure coincidence. Given that the disclosed flaws have been determined by researchers to be relatively easy to exploit and that they grant the attacker unfettered access to the device, the argument of coincidence becomes even less likely. It must be reiterated that for the version of eCh0raix currently being distributed now decryptor is yet available meaning that decryption can only occur by paying the ransom specified by the gang via a Dark Web portal controlled by the attackers. Typically it appears that the ransom demanded by the gang is 0.05 or 0.06 Bitcoin. This number appears to have remained constant throughout the ransomware’s lifecycle. It is further advised that victims do not pay the ransom as this funds criminal activity and will keep the gang looking for the next victim if they know cash can be swindled.
eCh0raix’s Brief History
Shortly after eCh0raix’s discovery both Anomali and TrendMicro both published reports attempting to shine a light on the gang's operations in July 2019. Summarising their findings Anomali stated,
“The eCh0raix ransomware, named after a string found in the malware, is a ransomware used in targeted attacks. It appears to not be designed for mass distribution. The samples with a hardcoded public key appear to be compiled for the target with a unique key for each target. Otherwise the decryptor sold by the threat actor could be used for all victims. The samples that fetch the public key and ransom note from the C2 server, also send a request when it starts and when it is done. This is probably used to provide the threat actor with live feedback. The request does not include any identifiable information for the threat actor to discern multiple targets.
The threat actor targets QNAP NAS devices that are used for file storage and backups. It is not common for these devices to run antivirus products and currently the samples are only detected by 2-3 products on VirusTotal, Figure 6, which allows the ransomware to run uninhibited. It is not known how these devices are infected. According to a post on Bleeping Computer’s forum, some infected systems were not fully patched and others reported detections of failed login attempts"
Trend Micro’s findings were similar and the security firm provided some sage advice on how to secure QNAP NAS devices against ransomware infections including those of other gangs known to target such devices. Advice includes the adoption of the following best practices:
- Changing default credentials or considering adding authentication and authorization mechanisms used to access NAS devices
- Updating the NAS device's firmware to patch exploitable vulnerabilities
- Ensuring that other systems or devices — particularly routers, which are connected to or built into NAS devices — are also updated
- Enforcing the principle of least privilege: enable features or components only when necessary (e.g., opening a port on the router) or use a VPN when accessing NAS devices over the internet
- Enabling the NAS device’s built-in security features; QNAP’s network access protection, for instance, helps thwart brute-force attacks or similar intrusions
Despite the development of a yet to be decrypted version of the ransomware, the gang has still stuck to the same tactics which placed the ransomware on the threat landscape. Further, the ransomware is written in GoLang, a programming language that is seeing increased used cybercriminals for use in malware, Kaiji being one of the more recent examples of malware to use the language.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion