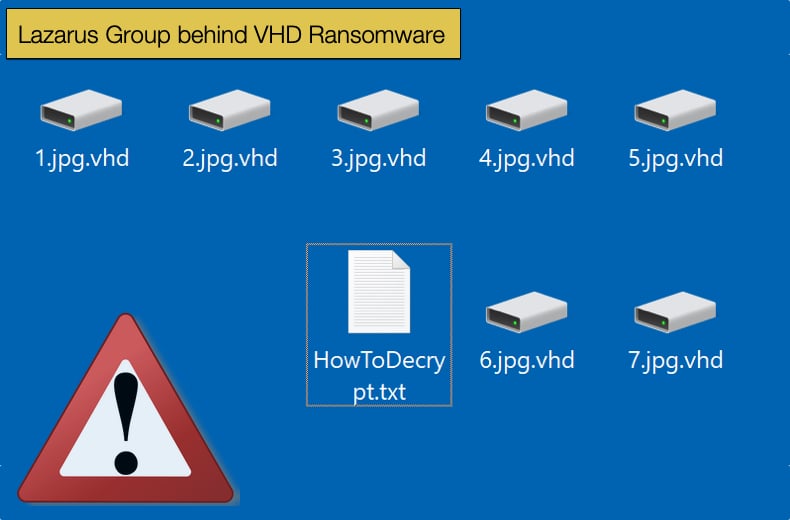
Lazarus Group behind VHD Ransomware
When Kaspersky Labs provided evidence the North Korean state-sponsored hacker collective named Lazarus was behind the WannaCry ransomware debacle that propelled ransomware into the limelight of malware, some scoffed. Those that believed it not to be the case seemingly also ignored evidence provided by several Western intelligence agencies. State-sponsored groups did not participate in for-profit, or financially motivated, hacking campaigns was the wisdom of the time. That time being 2017, now a better understanding of the group has led to wisdom on such matters. State-sponsored groups can indeed be financially motivated and perform cyber espionage. There was not a rule chiseled in stone, and there was most certainly no hacking rulebook being published in North Korea, raids on banks and cryptocurrency exchanges can attest to the mindset exhibited by Lazarus.
Now the wisdom of the day suggests that Lazarus consists of two groups, one for traditional cyber espionage, the other for helping finance government projects like the drive to develop intercontinental missiles and nuclear arms. The use of WannaCry was an example of this, although it can be regarded as a failure despite the damage it caused. It was a failure because the ransomware’s infrastructure could not adequately determine who paid the ransom and who did not mean files would remain encrypted even if the ransom was paid. It soon became the norm not to pay the ransom, meaning the main aim of the attack was left uncompleted and a failure.
Since WannaCry, the group has used other methods to source funds via extortion, targeting banks and crypto exchanges, and other methods to steal funds. Based on recently published research by Kaspersky Labs, Lazarus has once again decided to experiment with ransomware. The security firm believes that Lazarus group is behind VHD, a new ransomware only recently discovered being distributed between March and May 2020.
It would seem that here again, Lazarus is content to defy conventional thought. Typically, modern ransomware operators will often piggyback on botnets and backdoors that will initially compromise a targeted network. This has been the case seen multiple times with both Emotet and TrickBot. Both of which actively partner with ransomware operators for a share in the eventual profits. Lazarus, seemingly adopting big game hunting tactics, seems to rely on its infrastructure to distribute VHD, not willing to partner with the bigger names in the cybercriminal underground. Researchers pointed to this as evidence Lazarus is behind VHD as one incident involved the deployment of the MATA framework, known to be exclusively used by Lazarus Group.
VHD Ransomware
In the article published by Kaspersky, two incidents were investigated alluding to Lazarus’s hand behind the attacks. The first case saw the use of VHD in the wild. The ransomware itself is fairly unremarkable and does what ransomware should do. However, there were two peculiarities, one with how the ransomware encrypts data as well as how it treats files over a certain size. Researchers described these peculiarities as:
- The ransomware uses Mersenne Twister as a source of randomness, but unfortunately for the victims the RNG is reseeded every time new data is consumed. Still, this is unorthodox cryptography, as is the decision to use the “electronic codebook” (ECB) mode for the AES algorithm. The combination of ECB and AES is not semantically secure, which means the patterns of the original clear data are preserved upon encryption. This was reiterated by cybersecurity researchers who analyzed Zoom security in April 2020.
- VHD implements a mechanism to resume operations if the encryption process is interrupted. For files larger than 16MB, the ransomware stores the current cryptographic materials on the hard drive, in clear text. This information is not deleted securely afterwards, which implies there may be a chance to recover some of the files.
The first mention of the ransomware in the wild seemed to appear on ID Ransomware's website while Kaspersky was investigating the incident. It was further discovered that the ransomware was spread laterally across the target network via a spreading utility. Its operation contained a list of administrative credentials and IP addresses specific to the victim and leveraged them to brute-force the SMB service on every discovered machine. When it found and made a suitable connection the ransomware was shared and copied to the new network location using WMI calls.
This tactic is unusual for cybercrime groups and researchers noted that not one typically seen being used to spread ransomware. It is a technique typically used by state-sponsored groups during espionage campaigns. The tactic has been seen used in distributing wipers, malware that deletes data from hard drives, and is malware associated with North Korean and Iranian state-sponsored groups. Further, evidence suggesting that VHD was the work of a state-sponsored group resided in the fact that there are very few samples of the ransomware meaning it is not widely traded on cybercriminal platforms as is the case with several other ransomware families.
The second incident was detected by Kaspersky’s incident response team some two months after the first. This time researchers could piece together a complete picture of VHD’s infection chain. In this case, the initial foothold on the compromised network was attained through the use of a VPN vulnerability. After that, the attackers obtained administrative privileges, deployed a backdoor on the compromised system, and were able to take over the Active Directory server. They then deployed the VHD ransomware to all the machines in the network. In this instance, there was no spreading utility, but the ransomware was staged through a downloader written in Python. What may be the smoking gun in proving Lazarus is behind VHD is that in this instance the backdoor was created using the above mentioned MATA framework. This led researchers to say with a high degree of probability that Lazarus is again looking to experiment with ransomware to open up another revenue stream for the heavily sanctioned North Korean government.
A sign of things to come
In concluding researchers stated,
“The data we have at our disposal tends to indicate that the VHD ransomware is not a commercial off-the-shelf product; and as far as we know, the Lazarus group is the sole owner of the MATA framework. Hence, we conclude that the VHD ransomware is also owned and operated by Lazarus…Circling back to our introduction, this observation is at odds with what we know about the cybercrime ecosystem. Lazarus has always existed at a special crossroads between APT and financial crime, and there have long been rumors in the threat intelligence community that the group was a client of various botnet services. We can only speculate about the reason why they are now running solo ops: maybe they find it difficult to interact with the cybercrime underworld, or maybe they felt they could no longer afford to share their profits with third parties…It’s obvious the group cannot match the efficiency of other cybercrime gangs with their hit-and-run approach to targeted ransomware. Could they really set an adequate ransom price for their victim during the 10 hours it took to deploy the ransomware? Were they even able to figure out where the backups were located? In the end, the only thing that matters is whether these operations turned a profit for Lazarus.”
Given the ransom demands of the human-operated big game hunting ransomware gangs, recently WastedLocker demanded 10 million USD from victim Garmin, Lazarus Group wants a piece of the pie. What is clear, however, is that the group seems to be experimenting and approaching the endeavor rather shyly. This may be because the WannaCry debacle caused too much attention to be focused on the group. Further, it would seem that the group is not as capable as the other infamous ransomware strains, as the deployment and execution of VHD took 10 hours in one instance. This would give experienced security teams far too much time to respond and prevent further damage from occurring. This in turn would leave the attacker with little leverage to demand the millions of dollars they have been seeing pasted across headlines.
That being said, Lazarus Group has earned a well-earned reputation, and experimenting with ransomware is an ominous sign of things to come. It is early days for VHD, and while being slightly stunted for now by not partnering with cybercriminal organizations like TrickBot and Emotet to assist in distribution does not mean that no partnership will be forthcoming in future. If no partnerships are struck, there might come a need to develop better infrastructure and a more effective version of VHD. Then Lazarus would again be rewriting the rulebook and notching up high profile victims.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion