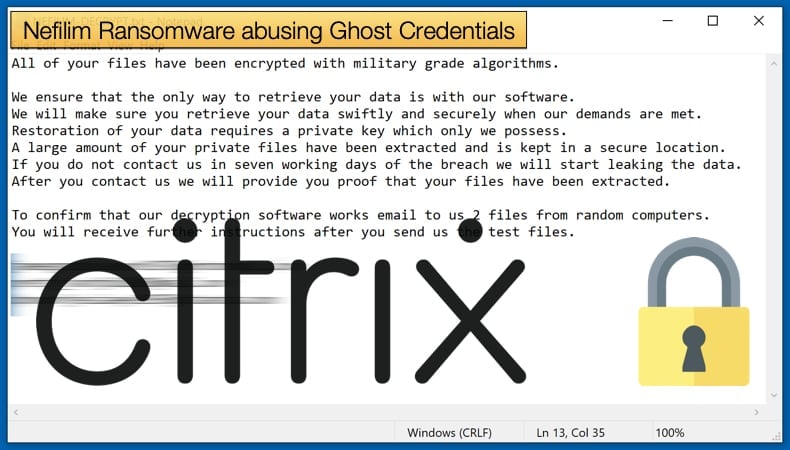
Nefilim Ransomware abusing Ghost Credentials
In a new report by security firm Sophos, the gang behind the Nefilim ransomware, also called Nemty, are using stolen credentials belonging to deceased individuals to compromise networks. Nefilim is perhaps best known for their successful attack on appliance manufacturing giant Whirlpool towards the very end of 2020. The ransomware has also been spread by the Phorpiex botnet in the past.
According to Sophos, a company reached out to the security firm in response to suffering a ransomware attack that managed to successfully target more than 100 systems. Once researchers began analyzing the attack, they soon discovered that an account previously belonging to a deceased employee was used to compromise the company network. It was noted that,
“The team determined the attacker had compromised an admin account with high level access about one month before launching Nefilim ransomware. Or more accurately, the attacker gained access to that admin account, then spent one month quietly moving around to steal credentials for a domain admin account, finding the trove of data they wanted, exfiltrating hundreds of GB of data, and then finally announcing their presence with the ransomware attack.”
Initial access to the network, not to be confused with the high-level access granted by using the deceased credentials, was gained by exploiting vulnerable versions of Citrix or Remote Desktop Protocol. Researchers believe that initial compromise was achieved through the use of exploiting vulnerable Citrix software, a common tactic used by Nefilim and its affiliates in a Ransomware-as-a-Service model. From there access was gained to the admin account, an account belonging to an employee who had sadly passed away three months prior. According to the report, the account was kept open as it was still used for certain services.
By using the account, it would make it harder to detect if anything untoward was happening; especially given that the account had high-level admin privileges and it was still in active use to facilitate the use of the above-mentioned services. It was only when analyzing the account activity did the researchers manage to join the dots, as much of the nefarious activity related to the attack was done after traditional business hours. Considering this, researchers commenting on accounts that belonged to employees who have left the company for any number of reasons advise that,
“If an organization really needs an account after someone has left the company, they should implement a service account and deny interactive logins to prevent any unwanted activity. Or, if they don’t need the account for anything else, disable it and carry out regular audits of Active Directory. Active Directory Audit Policies can be set to monitor for admin account activity or if an account is added to the domain admin group.”
Citrix Vulnerabilities again used as an Infection Vector
As to what Citrix vulnerability was exploited, the jury is still out. Researchers believe that a total of five could have been used, with one of those being the likely culprit. CVE-2019-11634 may have been the vulnerability exploited according to the report’s authors. The above-mentioned flaw was deemed critical and if properly exploited would allow for remote code execution. The vulnerability itself impacted the Citrix Workspace app and Receiver for Windows and involved the software not correctly enforcing local drive access preferences. Of the other possible guilty vulnerabilities, they include 4 High rated CVE vulnerabilities CVE-2019-13608, CVE-2020-8269, CVE-2020-8270, CVE-2020-8283.
The next step in the infection chain is not as easy as compromising the “ghost” account. The account and its credentials need to be found first. In order for the attackers to remain present and hopefully undetected on the network, they abuse the Remote Desktop Protocol, a common tactic used by modern ransomware gangs, which grants them access and keeps lines of communication open between them and the victim’s network. From there, the attackers will use the ever-popular Mimikatz post-exploitation tool which abuses Microsoft’s single sign-on feature to harvest credentials.
By using this tool the Nefilim gang would be capable of harvesting the credentials needed to successfully drop the ransomware and get it to encrypt network assets to cause the most damage to the victim. Defending against Mimikatz is difficult as the malware is only used once the network is compromised in order to gain access to an account with admin privileges. It is advised that organizations hand out admin privileges sparingly, and only to those that require them. J M Porup further recommends that,
“Upgrading to Windows 10 or 8.1, at least, is a start and will mitigate the risk of an attacker using Mimikatz against you, but in many cases this is not an option. Hardening the Local Security Authority (LSA) to prevent code injection is another proven strategy to mitigate the risk. Turning off debug privileges (SeDebugPrivilege) can also be of limited effectiveness, as Mimikatz uses built-in Windows debugging tools to dump memory. Disabling WDigest manually on older, unpatched versions of Windows will slow down an attacker for, oh, a minute or two — still worth doing, though. An unfortunately common practice is the reuse of a single administrative password across an enterprise. Ensure that each Windows box has its own unique admin password. Finally, on Windows 8.1 and higher running LSASS in protected mode will make Mimikatz ineffective.”
Nefilim in a Nutshell
Initially, when discovered in September 2019, the Nemty ransomware were seen distributed in the same methods of GandCrab and Sodinokibi. This led researchers to speculate if the ransomware was somehow related to the others, if at all. One of Nemty’s standout features to researchers was the level of encryption used to encrypt data. Described as “overkill” there would be little hope that a decryptor would be developed in a reasonable time, meaning they either had to restore from backups or pay the ransom if their backup policy was flawed. Built off such a solid foundation Nefilim was brought into existence, possibly to be Nemty’s successor. Nemty was not completely tossed aside, and versions were seen that had abandoned the ransomware-as-a-service business model and became used in smaller more private circles.
Nefilim seems currently content following the ransomware-as-a-service model, and as has been seen above abuses the remote desktop protocol is a favored infection vector, especially when it was discovered. Like Nemty, Nefilim has incredibly strong encryption protocols but has several traits that separate it from Nemty, including variances in the code and the use of .nefilim as an extension once files are encrypted. For encryption, Nefilim uses a combination of AES-128 and RSA-2048 algorithms to encrypt the victims’ files. First, the files are encrypted using AES-128 encryption and AES encryption key is further encrypted using the RSA-2048 public key. This key is then embedded in the executable file of the ransomware.
Nefilim was also quick to adopt double extortion tactics seen successfully employed initially by the Maze ransomware gang. The tactic involves stealing information from the victim before encryption then if the victim refuses to, or does not pay the ransom at a specific time the gang will release the information to the public. To do this the gang makes use of a website, often referred to as a “leak-site” where the gang will publish stolen information. Not only has Nefilim struck Whirlpool, adding a big name to its victim list but Orange, the telecommunications company, also suffered a Nefilim attack. Based on leaked images of the ransom note it was determined the offending ransomware was Nefilim, however, the company itself did not divulge which strain it was. In a statement the company said,
“A cryptovirus-type computer attack was detected by Orange teams during the night of Saturday 04 July to Sunday 05 July 2020. Orange teams were immediately mobilised to identify the origin of this attack and has put in place all necessary solutions required to ensure the security of our systems. According to initial analysis by security experts, this attack has concerned data hosted on one of our Neocles IT platforms, "Le Forfait informatique", and no other service has been affected. However, this attack seems to have allowed hackers to access the data of around 20 PRO / SME customers hosted on the platform. Affected customers have already been informed by Orange teams and Orange continues to monitor and investigate this breach. Orange apologises for the inconvenience caused.)”
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion