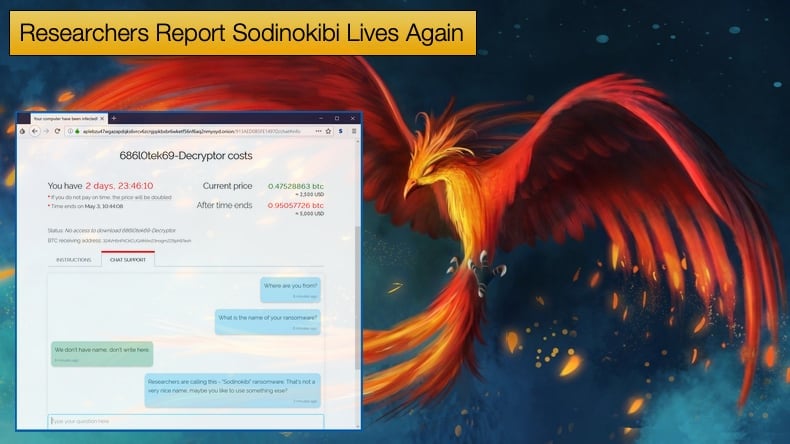
Researchers Report Sodinokibi Lives Again
Also known as REvil, and sometimes referred to as the Crown Prince of Ransomware, Sodinokibi has long been the thorn in the side of large enterprises and a headline maker. This year alone those behind the ransomware were responsible for both the JBS incident and the Kaseya incident. The latter prompted direct statements of intent by both US President Joe Biden and US law enforcement agencies. This in turn was the likely motivator for the gang to take a holiday.
The bad news is it appears the gang is back in action after taking a summer holiday. When websites and infrastructure known to be used by the ransomware gang were taken offline, many in the InfoSec hoped that the group has thrown in the towel. Lawrence Abraham, of Bleeping Computer, took to Twitter to report that the group's leak site, Happy Blog, was back online with activity dating back to July.
This surely dashed the hopes that the gang had retired. This was later ratified by other security firms who provided more evidence to suggest that not only was the leak site back online but much of the gang’s infrastructure.
At the time when the gang’s activity ceased some believed that either US or Russian government agencies may have seized critical components of the infrastructure, like servers, and taken down websites. Both governments denied they were involved in any search and seizure operation. The latest revelations of Sodinokibi being back in action would seem to support the statements by both governments.
Both Recorded Future and Emisoft were the security firms mentioned above that confirmed much of the gang's infrastructure was back online. Speaking to ZDNet ransomware expert Allan Liska said,
“Things definitely got hot for them for a while, so they needed to let law enforcement cool down. The problem (for them) is, if this is really the same group, using the same infrastructure they didn't really buy themselves any distance from law enforcement or researchers, which is going to put them right back in the crosshairs of literally every law enforcement group in the world (except Russia's)… I'll also add that I've checked all of the usual code repositories, like VirusTotal and Malware Bazaar, and I have not seen any new samples posted yet. So, if they have launched any new ransomware attacks there haven't been many of them.”
For some victims of Sodinokibi at the time of the Kaseya incident, Sodinokibi’s brief disappearance left them in a bind. Despite paying the ransom and receiving decryption keys they would not work because of the gang’s infrastructure.
Typically Sodinokibi had a help desk that assisted victims in retrieving lost data but with that being offline as well, victims were stuck. Speaking about this unfortunate turn of events, Mike Hamilton, former CISO of Seattle and now CISO of ransomware remediation firm Critical Insight, noted,
“Some of our customers got off really easily. If you had that agent installed on unimportant computers, you just rebuilt them and got back to life. But we got a distress call a few days ago from a company that got hit hard because they had a company that was managing a lot of their servers with the Kaseya VSA. They got a lot of their servers hit and had a lot of information on them and so they brought in their insurance company and decided to pay the ransom…They got their decryption key and when they started to use it, they found that in some places it worked and in other places it didn't. These ransomware gangs have customer support but all of a sudden they went dark. They're completely gone and so there is no help and these folks are just stuck. They're going to end up losing a lot of data and they're going to end up spending a lot of money to completely rebuild their network from scratch.”
Further evidence of Sodinokibi’s return was published by security firm Black Frog who noted that the gang was responsible for 23% of detected attacks for August.
All things considered, it certainly looks like Sodinokibi is back in business. Research conducted by Kela has shown who ransomware gangs consider an ideal victim. Such research might help victims realize that they may be high-profile targets for the likes of Sodinokibi.
The Perfect Victim
The report published by Kela consisted of researchers compiling listings made by ransomware operators active on underground forums and marketplaces, including initial access requests.
Initial access is seen by many as the primary way ransomware threat actors are gaining access to victims' networks. This can be done in a variety of ways including phishing for credentials, abusing insecure remote desktop protocol (RDP) connections, or by offering a financial reward to someone in a company or access to a company’s network.
The last method is becoming increasingly popular with ransomware gangs looking to target companies that have revenue over 100 million USD. For those who can buy access, it does reduce the amount of legwork needed to gain access. Researchers also noted that threat actors are willing to pay insiders for vulnerabilities that can be exploited to gain access to the network and not just for credentials.
For ransomware gangs, if initial access can be secured through simply paying a third party this frees up time to attack other targets. When ransomware attacks can result in a payout of millions of dollars paying a third party not only becomes inconsequential, but the potential advantages make it almost a no-brainer.
Researchers noted that insiders or those with intimate knowledge of organizations in the US, Canada, Australia, and Europe are the most prized. Those offering information about Russian organizations or those from countries perceived as the third world are almost always immediately dismissed.
This is because the perceived payouts are believed to be lower. Also, it should be noted that by not targeting Russian organizations those threat actors in the region typically stay off the local law enforcement's radar. Attacking a Russian interest or individual might result in that blind eye suddenly regaining sight.
Ransomware gangs will also have specific targets depending on their preferences. According to Kela nearly half of the ransomware operators will reject offers for access into organizations in the healthcare and education sector, irrespective of the country. In some cases, government entities and non-profits are also off the table.
Preferences also extend to how access to the network is granted. Remote Desktop Protocol (RDP), Virtual Private Network (VPN)-based access prove popular. Specifically, access to products developed by companies including Citrix, Palo Alto Networks, VMWare, Cisco, and Fortinet.
For those who offer access to a victim’s infrastructure, the level of privilege is also considered. In this regard, access with admin privileges is always preferred but interestingly, not critical. As to how much initial access is worth, researchers have seen payments as high as 100,000 USD but the average payout is 56,250 USD. It is not just access to a victim’s network that is sold but researchers saw offerings for e-commerce panels, unsecured databases, and Microsoft Exchange servers.
These would typically be of more interest to those who steal and peddle in data, rather than ransomware gangs. In looking to defend against ransomware attacks and the ever-present danger of an insider looking to sell access Kela advises that organizations apply the following mitigation strategies:
- Cybersecurity awareness and training for all key stakeholders and employees to ensure that key individuals know how to safely use their credentials and personal information online. This cyber training should include specifying how to identify suspicious activities, such as possible scam emails, or unusual requests from unauthorized individuals or email addresses.
- Regular vulnerability monitoring and patching to continually protect their entire network infrastructure and prevent any unauthorized access by Initial Access Brokers or other network intruders.
- Targeted and automated monitoring of key assets to immediately detect threats emerging from the cybercrime underground ecosystem. Constant automated and scalable monitoring of an organization’s assets could significantly improve maintaining a reduced attack surface, ultimately helping organizations thwart possible attempts of cyberattacks against them.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion