New Backdoor Malware Targets Windows, Mac, and Linux
A group of cybersecurity researchers at Intezer have discovered a new malware strain that is capable of creating backdoors on Windows, Mac, and Linux machines. The malware was discovered in December 2021 and hints at a trend of new malware being developed that is capable of targeting multiple operating systems.
According to a blog article published the malware was discovered during an attack against a Linux-based web server at an undisclosed educational institution in December. The new backdoor malware was not the cause of the investigation but was discovered already present on the compromised web server.
The malware, now named SysJoker, operates by creating a “backdoor” into a compromised system, generally, without being detected, that will further allow the attacker to execute commands as well as download and upload files.
Typically backdoors are used prolifically in cyber espionage operations or to act as a dropper for other malware strains. The malware is written in C++ and depending on the operating system targeted be it Windows, Mac, or Linux the code bose is altered to run on the targeted operating system.
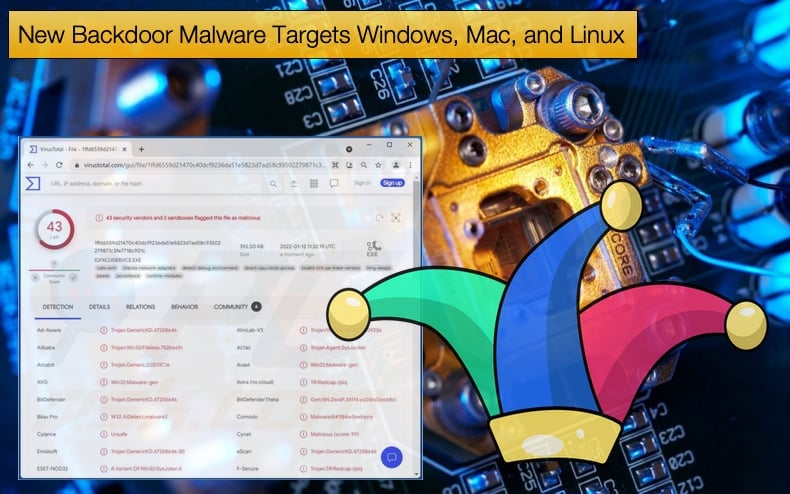
Currently, Intezer has discovered Linux and Mac variants in the wild. At the time of writing, those variants were not being detected as malware on Virus Total.
Researchers determined that the malware compromises machines by appearing as a system update. On Mac and Linux machines the update masquerades as a system update. On Windows machines, the malware masquerades as an Intel update. As it stands, the exact way these “updates” are pushed to victims is unknown.
Researchers did note that the names of the update names like "updateMacOs" and "updateSystem" are relatively generic, which is something that could potentially arouse suspicion. Based on further analysis of the malware, it was discovered that the malware started being actively deployed in attacks in the second half of 2021 and the attackers behind it are paying close attention to campaigns.
Even during the period of analysis after the malware was initially discovered in December, the command and control domain behind the attacks had changed at least three times. This indicates that those behind the campaign are actively monitoring targets.
Researchers believe that the attacker behind the campaign may be classified as an advanced threat actor given the measures adopted by the attacker.
Those measures are developing malware for the three main operating systems used in the wild and close monitoring of victims. Further, the attack on the unnamed educational system is in line with targets favored by any number of advanced threat groups.
Other indicators that an advanced threat actor is at large is that the code was written from scratch, the attack campaigns discovered are not widespread, and now second-stage payload was seen deployed. This indicates that victims are chosen in a very targeted way and by not deploying a second-stage payload the attackers may not be financially motivated.
Vermillion Strike
SysJoker is not the only recently discovered malware strain discovered developed to target multiple operating systems. Also discovered by Intezer in September 2021, Vermilion Strike is a repurposed Cobalt Strike capable of targeting both Windows and Linux users.
This is novel in that while Cobalt Strike, a popular penetration testing tool also used by threat actors, has a Windows version but to the best of the writer’s knowledge, no official Linux distribution is available. Researchers noted,
“In August 2021, we at Intezer discovered a fully undetected ELF implementation of Cobalt Strike’s beacon, which we named Vermilion Strike. The stealthy sample uses Cobalt Strike’s Command and Control (C2) protocol when communicating to the C2 server and has Remote Access capabilities such as uploading files, running shell commands, and writing to files. The malware is fully undetected in VirusTotal at the time of this writing and was uploaded from Malaysia.
Based on telemetry with collaboration from our partners at McAfee Enterprise ATR, this Linux threat has been active in the wild since August targeting telecom companies, government agencies, IT companies, financial institutions, and advisory companies around the world. Targeting has been limited in scope, suggesting that this malware is used in specific attacks rather than mass spreading.”
Like SysJoker, it appears Vermilion Strike is used primarily for espionage purposes given the feature set copied over from Cobalt Strike.
Researchers also believe that the attacker is skilled in that the malware’s codebase has not been seen before and the fact that it targets specific entities in the wild. Regarding Vermilion Strike, researchers concluded,
“Vermilion Strike and other Linux threats remain a constant threat. The predominance of Linux servers in the cloud and its continued rise invites APTs to modify their toolsets in order to navigate the existing environment…Vermilion Strike is not the only Linux port of Cobalt Strike’s Beacon. Another example is the open-source project geacon, a Go-based implementation. Vermilion Strike may not be the last Linux implementation of Beacon.”
There are several reasons why more attention should be paid to Linux-based malware. One of the biggest reasons is the low detection rates of known Linux malware strains. This is due in part to several reasons but one of the major contributors to this fact is the rapid adoption of cloud computing.
This has placed increasing reliance on Linux web servers, for example, for cost and ease of deployment through popular cloud services providers. In helping to mitigate the impact of Linux malware the following security measures can be taken:
- Keep your systems patched and updated across all Linux servers and devices.
- Ensure signature-based detection solutions are if present are kept up to date.
- Secure SSH login and connections with an SSH key. In the past username password combinations have been compromised via brute force attacks. This has made SSH keys that use encryption a safer option.
- Perform a routine review of important system files.
- Disable root accounts. The root account on a Linux machine has access to all files and commands on a Linux system. What’s more root accounts have full read, write and execute permissions meaning if the account is compromised the attacker can execute malware and steal all the data on the machine.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion