New BlackGuard Variant Capable Of Targeting 57 Wallets And Extensions
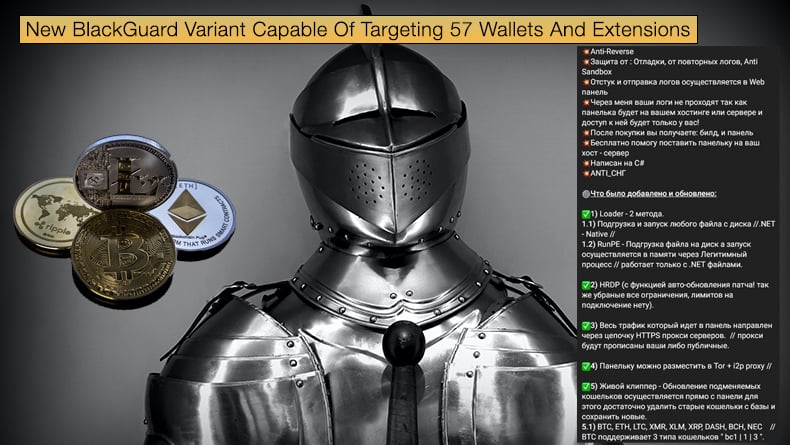
Security researchers for the major telecommunications company AT&T have discovered a new variant of BlackGuard, a new info stealer that is gaining popularity with threat actors using underground hacking forums.
This new variant is actively being distributed in the wild and boosts several new features, including targeting crypto wallets and related cryptocurrency extensions.
The malware was initially discovered by researchers based at Zscaler who noted a spike in activity regarding a previously unknown malware strain after Raccoon Stealer suspended operations, citing the Ukraine war and the death of one of the malware's developers to suspend operations.
Zscaler discovered BlackGuard in March 2022, but according to Bleeping Computer, BlackGuard was first mentioned on Russian-speaking underground hacking forums in January 2022.
Zscaler researchers noted that BlackGuard is currently being sold as malware-as-a-service with a lifetime price of 700 USD and a monthly fee of 200 USD. The malware can steal all types of information related to Crypto wallets, VPNs, Messengers, FTP credentials, saved browser credentials, and email clients.
Even upon the malware's discovery, there was a heavy emphasis on targeting crypto assets and software. According to Zscaler, the malware will look to steal information from the following software packages and applications:
- Web browsers: Passwords, cookies, autofill, and history from Chrome, Opera, Firefox, MapleStudio, Iridium, 7Star, CentBrowser, Chedot, Vivaldi, Kometa, Elements Browser, Epic Privacy Browser, uCozMedia, Coowon, liebao, QIP Surf, Orbitum, Comodo, Amigo, Torch, Comodo, 360Browser, Maxthon3, K-Melon, Sputnik, Nichrome, CocCoc, Uran, Chromodo, Edge, BraveSoftware
- Wallet browser extensions: Binance, coin98, Phantom, Mobox, XinPay, Math10, Metamask, BitApp, Guildwallet, iconx, Sollet, Slope Wallet, Starcoin, Swash, Finnie, KEPLR, Crocobit, OXYGEN, Nifty, Liquality, Auvitas wallet, Math wallet, MTV wallet, Rabet wallet, Ronin wallet, Yoroi wallet, ZilPay wallet, Exodus, Terra Station, Jaxx
- Cryptocurrency wallets: AtomicWallet, BitcoinCore, DashCore, Electrum, Ethereum, Exodus, LitecoinCore, Monero, Jaxx, Zcash, Solar, Zap, AtomicDEX, Binance, Frame, TokenPocket, Wassabi
- Email: Outlook
- Messengers: Telegram, Signal, Tox, Element, Pidgin, Discord
- Other applications: NordVPN, OpenVPN, ProtonVpn, Totalcommander, Filezilla, WinSCP, Steam
At the time of discovery, researchers discovered that evasion and anti-detection features were still under development. Still, several such features had made it into the malware being sold at the time. These included the ability to detect any Antivirus software and sandboxes running on the infected machine, then attempt to kill their processes and terminate their operation.
The malware also checks the victim's IP address. If it's running on a system in Russia or any other Commonwealth of Independent States (CIS) country, namely those countries determined to be within Russia's sphere of influence, it will stop and exit. This does provide a major indicator as to the origin of the malware.
Lastly, the malware is packed with a crypter, and all its strings are base64 obfuscated. This means that antivirus tools relying on static detection will miss it.
New BlackGuard Features
According to the new research published by AT&T, BlackGuard is not only capable of stealing information related to crypto wallets stored on the infected machine but can now also steal cryptocurrency addresses copied to a clipboard and replace them with wallet addresses under the attacker's control.
Any cryptocurrencies traded or sent to the hijacked addresses will never reach their intended wallet but that of the attackers. This is done by tracking any content copied to the clipboard and matching it to different crypto wallets stored in the malware via similarities in the malware regular expressions used to denote what wallet is used for a particular cryptocurrency.
The newer variant is also capable of propagating through removable devices. Researchers noted, "Although this feature was limited since Windows 7 to be used only for CDROM, the malware copies itself to each available drive with an "autorun.inf" file that points to the malware to execute it automatically.
This includes removable and shared devices. For example, if a USB device is connected to an old version of Windows, the malware will be executed automatically and infect the machine."
Further, the new variant can act like a malware dropper through process injection, with researchers stating,
"The new variant of BlackGuard downloads and executes additional malware from its command & control.
The newly downloaded malware is injected and executed using the "Process Hollowing" method. With that, the malware will be running under legitimate/whitelisted processes and can make detection more difficult…
The malware copies itself to every folder in C:\ drive recursively. The malware generates a random name to be copied to in each folder. This feature is not common for malware and is mostly annoying, as the malware gains no advantage from that… The malware added persistence to survive a system reboot by adding itself under the "Run" registry."
While it is unclear what features will be added in the future, it is clear that BlackGuard's increasing popularity will drive the development of the malware. This will further attract new customers looking to steal information easily from unsuspecting victims.
Researchers advise security teams to inspect all traffic and use malware prevention tools, including antivirus tools for known threats and sandboxing capabilities for unknown threats. Further researchers suggest the following mitigation strategies to be adopted:
- Don't use the same passwords for all the services, and replace them on a regular cadence.
- Use multi-factor authentication where applicable.
- Avoid visiting unknown sites.
- Avoid opening suspicious unknown files.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion