News Archive October 2014
Monthly Cyber Security News Archive: October 2014 Summary
Table of contents:
- Limitless Keylogger Distribution Campaign Discovered
- ComputerCOP free Internet security software
- Windows Isn’t Safe from Shellshock-like Attacks After All
- Qbot Banking Trojan Botnet - 500,000 Victims and Counting
- Sandworm Targets NATO, European Union
- Salesforce Hack Could Be Merely the Tip of the Iceberg
- Cyberespionage Group Targets Office 365 Web App, High Level Targets
- Sweet Orange Virus Targets YouTube Users
Limitless Keylogger Distribution Campaign Discovered
05.10.14
A Greek security researcher recently uncovered a new malware campaign that takes advantage of two well-known programs to avoid detection by most antivirus solutions while functioning as a keylogger capable of stealing all keystrokes made on an infected machine. These keystrokes — which often include sensitive personal and financial data — are then sent discreetly to the cybercriminals behind the attack. This new threat is comprised of two unique pieces of software. The first is a well-documented keylogging program known as Limitless Keylogger.
This program is commercially-available and defined in most every antivirus solution currently available. The other program is known as AutoIT. This non-malware program is designed to automate day-to-day tasks on computers. Often, AutoIT is used by large corporations as a way to reduce the workload of the in-house IT staff. This means that many (if not most) antivirus solutions are designed not to detect AutoIT as malware. This is exactly why the hackers behind this latest threat decided to combine the two programs to create a dangerous keylogger designed specifically to avoid detection on large corporate networks. The current malware campaign is being distributed via spam email usually targeting large corporate targets. An email attachment that is actually a WinRAR SFX executable file contains four malicious files including:
- the AutoIT script (disguised as ‘update.exe’)
- a Python script designed to de-obfuscate the AutoIT script
- settings for AutoIT script (‘oziryzkvvcpm.AWX’)
- ‘sgym.VQA’ (another encrypted malicious binary file)
Within these files, the keylogging program has lots of additional features designed to prevent the malware from being detected.
Upon close evaluation by security researchers, it has been determined that this program sends all keystrokes to an email address controlled by the hackers behind the program using standard Simple Mail Transfer Protocol (SMTP) functionality.
The malware also sends screenshots and recovery information (which often includes passwords) to the same email address.

The discovery of this malware points to a larger problem that is becoming increasingly prevalent in malware creation and distribution operations. Keyloggers like this are almost completely undetectable and as the average PC user becomes more aware of various scams and potentially hazardous software on the Internet, hackers are turning to these solutions as a way to steal information and financial resources from unsuspecting victims. The best way to protect yourself from these threats is to avoid opening any unsolicited emails — especially those with attachments or links to potentially malicious websites where drive-by downloads could be waiting.
While the idea behind many of these keylogging programs is to remain undetected, many modern antivirus solutions may be capable of detecting Limitless Keylogger (even when combined with AutoIT) assuming the program is updated frequently.
Also, avoid logging into financial websites or other sites where personal information is required whenever possible. If these sites need to be accessed, consider using a secure password manager that allows you to log in without actually typing in username and password combinations. This is a surefire way to avoid the potential complications of using a computer infected with keylogging software.
ComputerCOP free Internet security software
08.10.14
Police officers exist to protect us, right? So it shouldn’t come as much of a surprise when the local police department offers us - citizens of the United States - a tool designed to protect our children from the dangerous place colloquially known as the Internet. Unfortunately, it appears local police departments would rather follow in the footsteps of the NSA and spy on everything we do online, illicit or not. ComputerCOP is a free Internet security software offered by law enforcement agencies around the country. This software is purportedly designed as a way for parents to keep an eye on what their children are doing online.
Unfortunately, ComputerCOP shares more in common with keylogging malware often discussed on this blog than the benign security tool it is advertised to be. While ComputerCOP is supposedly distributed as a way for parents to monitor the online activities of their children - flagging activity associated with sex, drugs and violence - online advocacy groups such as the Electronic Frontier Foundation have discovered that the program is, in fact, a dangerous keylogging program that puts the safety of the entire household at risk once installed.
Although the idea is sound, the problem with this software is that it records everything that anyone does on the computer. This information is then sent - unencrypted - to a third party server where it is collected for “law enforcement use.” The first problem is that the information is sent without any encryption whatsoever.
This means that any hacker sniffing packet streams can intercept and immediately view information sent via the Internet once this program has been installed.
This includes sensitive personal and financial information such as online banking username/password combinations and access to email accounts without the knowledge of the person(s) with ComputerCOP installed.
Another problem is that this software is being distributed, in some cases even pushed, by local enforcement personnel. The police officers may not even know exactly what this software is capable of...in fact, they probably don’t have a clue (but the title caught your attention, didn’t it?). Unfortunately, because this spyware is being distributed by law enforcement personnel, most people assume it is safe to use. This makes ComputerCOP especially dangerous compared to other known keylogging variants. It should also be mentioned that most distributed versions of this program include prominent branding specific to the law enforcement department or District Attorney of the area. This PR feature adds to the “credibility” of this dangerous program.
Finally, since ComputerCOP is freely distributed, it’s possible for hackers to begin distributing a modified version of this program designed to trick victims into installing this dangerously powerful program.
While law enforcement is most likely trying to assist the general public by offering ComputerCOP to households within their jurisdiction, the reality is that this program is a potentially dangerous invasion of privacy with consequences that go far beyond the intended use.
Windows Isn’t Safe from Shellshock-like Attacks After All
09.10.14
You may have heard about a recent security scare that many websites have been quick to compare to Heartbleed and other serious vulnerabilities that have been recently discovered. In case you are unfamiliar, Shellshock is a vulnerability affecting Linux/Unix and some OSX (Apple) computers whereby a hacker can remotely execute code from the terminal (known as Bash). This vulnerability is due to a coding oversight that allows certain variables to be read as commands by the terminal. Although the use of Linux for home computers is still relatively limited, Shellshock could spell big trouble for many large corporations that rely on Linux or Unix-based systems for many backend functions. This blog decided not to cover Shellshock previously because it does not affect Windows machines. However, security researchers have recently discovered that Windows has many similar vulnerabilities that could allow for remote code execution via the Windows terminal.
Windows servers are especially at risk based on the research done by The Security Factory, a Belgian IT security firm. This company recently reported discovering a command line injection vulnerability that takes advantage of environment variables much like Shellshock does in Unix-based machines. Specifically, this vulnerability works because once an environment variable has been set up, Windows will execute anything contained within that variable name.
This vulnerability affects all current versions of Windows including the new Windows 10 Preview, but the biggest concern is for Windows Server deployments because they rely on batch files and scripts that contain environment variables.
It’s important to note that this remote code execution (RCE) vulnerability is not as serious as Shellshock simply because in order to create environment variables in Windows, the user must already have elevated privileges (administrator rights on the system). Shellshock, on the other hand, affects all Unix-based OSs — mostly because of the way DHCP and Apache web servers access the terminal during normal Web browsing. In other words, this newly discovered RCE capability must be executed locally in most cases.
The exception would be if a hacker were able to gain administrative login credentials, log into the system remotely and create environment variables that execute malicious code when called via Windows command line tools. The simple way to avoid accidentally executing code within a defined environment variable is to enclose the variable in quotes. This is Windows’ failsafe. By adding quotes, the vulnerability is non-existent. Unfortunately, forgetting to add quotes could result in unintended, or even malicious, code execution on the system.
According to a statement by Microsoft, the company has no intention of updating current or future software releases to prevent RCE while using command line tools, so the burden falls on system admins to keep an eye on what is being typed into the command line interface.
The discovery of this vulnerability occurred only a couple of weeks after Shellshock was first discovered meaning that many other RCE vulnerabilities could be present within common Windows command line tools that have yet to be discovered.
Qbot Banking Trojan Botnet - 500,000 Victims and Counting
11.10.14
Security experts recently uncovered a new and extremely dangerous botnet that has already infected an estimated 500,000 computers worldwide. Known as Qbot or Qakbot, this new botnet is designed to sniff packets related to online banking transactions. At the time of this writing, over 800,000 unique online financial transactions have been intercepted. Most of these are from at least five major United States banks, although security firm Proofpoint (the firm responsible for discovering Qbot) states that many large European banks are also being actively targeted. According to reports, Qbot started when a group of Russian cybercriminals obtained administrative login credentials for Wordpress sites via an underground marketplace. Malware was uploaded to these sites so visitors would become victim to the ever-so-popular drive-by download.
What’s interesting about Qbot, however, is that malware is not distributed to every visitor of a compromised site. Using a technique known as Traffic Distribution System (TDS) filtering, the cybercriminals behind this malware attack can determine whether or not a potential target is worthy based on geographical location and vulnerability of the OS being used to visit the malicious site.
The TDS filter also ensures that the visitor isn’t, in fact, a security company scanning for nefarious activity. If a particular visitor is determined to be a worthwhile target, the Qbot malware is downloaded in the background without the knowledge of the user by exploiting vulnerabilities in the Web browser or specific Web browser plug-ins including Java, Flash and Silverlight.
Additional victims have also become infected via malicious content distributed through the compromised sites email newsletter. Another aspect of this malware that makes it especially dangerous is that the hackers have incorporated a third-party obfuscation service called Scan4U. This service prevents Qbot from being detected by most security scans and even notifies the hackers if Qbot is detected in a scan. This allows the hackers to re-obfuscate the code to avoid further detection.
 Once infected, that PC becomes part of the Qbot botnet - one of the largest banking Trojan-based botnets in history. In addition to sniffing Internet packets related to secure online banking transactions, Qbot is capable of being used to create private cloud networks available for lease to other cyber criminal organizations. Basically, the hackers have created a tunneling service using SockS5 known as SocksFabric. This service is available for $10 per day or $100 for 30 days, comes complete with an instruction manual, and allows criminals to create private clouds using infected machines. These private clouds provide infection points for other malware attacks while generating an additional revenue stream for the Russians behind Qbot.
Once infected, that PC becomes part of the Qbot botnet - one of the largest banking Trojan-based botnets in history. In addition to sniffing Internet packets related to secure online banking transactions, Qbot is capable of being used to create private cloud networks available for lease to other cyber criminal organizations. Basically, the hackers have created a tunneling service using SockS5 known as SocksFabric. This service is available for $10 per day or $100 for 30 days, comes complete with an instruction manual, and allows criminals to create private clouds using infected machines. These private clouds provide infection points for other malware attacks while generating an additional revenue stream for the Russians behind Qbot.
Although no one knows how much money these hackers have made using banking credentials stolen through this malware, security experts do know that similar cybercriminal rings are often able to pull as much as $25,000 from each compromised bank account.
With over 800,000 sessions already sniffed, it’s possible these hackers could make millions (if they haven’t already). Like so many other modern malware threats, the best way to protect yourself from Qbot is to avoid using Web plug-ins with known vulnerabilities unless absolutely necessary. If those plug-ins are necessary, check for updates at least once per week to avoid being compromised by a zero-day exploit.
Sandworm Targets NATO, European Union
15.10.14
Russian hackers, operating under the name of the “Sandworm team”, are targeting government leaders and institutions including the North Atlantic Treaty Organization (NATO), European Union and Ukrainian governments and academic targets in the United States. At least one U.S. academic was specifically targeted for his work and focus on Ukrainian issues. Based on recent analysis by security firm iSight, a company that has been watching Sandworm since last year, this cyber espionage campaign has been slipping into Windows computers for over five years — specifically extracting information pertaining to intelligence and diplomatic affairs in Ukraine.
Since 2009, Sandworm has been silently spreading around the globe, infiltrating computers using a variety of strategies. Favored methods for this group include spear phishing (spam email campaigns with malicious files attached), the BlackEnergy crimeware and, most recently, a recently discovered zero-day vulnerability that affects nearly every Windows operating system produced since Windows Vista. This vulnerability also extends to Windows Server 2008 and 2012 — making it a serious threat for computer systems around the world.
The vulnerability, officially known as CVE-2014-4114, has been used by the Sandworm team since August of last year. Typically, the malware is spread using infected PowerPoint files spread via spam email campaigns within corporate networks around the world.
At this time, there is no estimate has to how much and what type of information Sandworm has successfully taken using this exploit. What security researchers do know, however, is that the vulnerability was completely unknown until just recently and most, if not all, organizations that have been targeted have been compromised to some degree. That said, it appears that the vulnerability used to infiltrate computer systems using Sandworm is not well-known amongst cyber criminals.
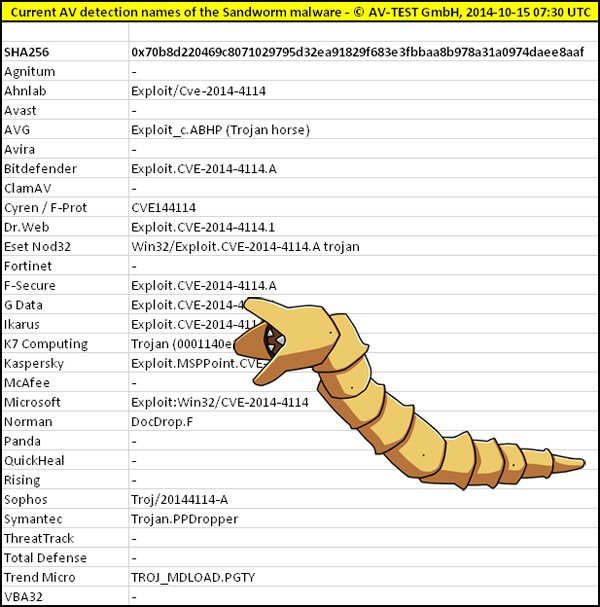
In fact, it’s entirely possible that Sandworm kept information about this vulnerability quiet in an attempt to protect Sandworm from detection using conventional antivirus tools. Sandworm works by exploiting a vulnerability in the way Windows handles PowerPoint files. Once a malicious PowerPoint file is opened on the target system, remote code can be executed on the system. Ultimately, a malicious executable installs a backdoor into the system that allows the hackers to remotely access the computer in search of files related to conflicts in Ukraine. Due to the nature of the information being sought in this attack, it is unlikely that the average PC user would be targeted with malware like Sandworm — at least not at this time.
Unfortunately, the same backdoor that allows the Sandworm team to access intelligence and diplomatic information could be used to steal passwords and financial information from consumers.
Microsoft just released a patch to protect Windows computers from the Sandworm vulnerability. This automatic fix eliminates the code vulnerability that allows for remote code execution via PowerPoint. When a new vulnerability of this magnitude is discovered, plenty of hackers will try to exploit the new vulnerability on unpatched systems. The best way to protect your PC from Sandworm is to ensure all Windows security updates are installed in a timely manner.
Salesforce Hack Could Be Merely the Tip of the Iceberg
19.10.14
Recently, hackers released a variant of the Dyre banking Trojan designed to target users of the popular sales platform Salesforce.com. In early September, Salesforce notified customers that they may be targeted by Dyre (also known as Dyreza) — a key logger designed to harvest user login credentials. More traditional Dyre campaigns target large financial institutions, but the variant affecting Salesforce customers was attached to an email that installed Dyre once opened.
While this may not be groundbreaking security news alone, new information calls into question what the motives of the hackers behind the Salesforce campaign actually are. These hackers have now released an improved version of Dyre that has been seen in the wild already. This variant offers many of the same password-stealing tactics as previous versions; however, the new version also includes functionality that allows it to steal client certificates and browser cookies.
In other words, Dyre allows hackers to hijack a remote encrypted connection — like one between a home PC and an online banking platform. What’s interesting is that the malware is targeting these client certificates because it is a tactic that doesn’t work well with large scale banking campaigns.
Combined with the elaborate Salesforce.com attack, security researchers agree that this campaign is well-orchestrated and the hackers likely know exactly you is being targeted — somehow combining information gained from breaches Salesforce accounts with online banking information.
Unfortunately, no one can yet determine what the possible connection between the two campaigns is. There’s no doubt that the same group is responsible. We also know that, at least thus far, the hackers have had no interest in selling any of the compromised Salesforce credentials. As experts analyze mechanisms within Salesforce that could be used as an attack vector, the only thing that remains clear is the large scale implications that an attack of this magnitude could have.
So far, researchers have been able to determine that the hackers have coded Dyre with two separate configurations based on the URL of the infected machine. If a machine URL is detected that is on Dyre’s target list, a much more elaborate version of the malware is installed which is capable of performing man in the middle attacks.
Machines not on the target list receive a much more generic version that only sends information back to the hackers via a plain text file. The Salesforce data is being stored on a separate server designed to target websites using compromised Salesforce data based on unknown criteria. Despite the troubling connection between these attacks, Dyre is still a serious risk for most PC users as it is a dangerous banking Trojan often spread via spam email campaigns. While a definition of this malware is included with most modern antivirus solutions that have been properly updated, you should refrain from opening unsolicited emails and any attachments they may contain to avoid accidentally installing Dyreza or another dangerous banking Trojan variant.
Cyberespionage Group Targets Office 365 Web App, High Level Targets
23.10.14
A still-unidentified cyberespionage group has been discovered that is using advanced spear phishing techniques to steal email login credentials from employees at high level targets including embassies, military agencies, international media outlets and defense contractors. Although the origin and whereabouts of the group behind this attack are still unknown, security experts are referring to the attack as Operation Pawn Storm and it appears this operation has been going on covertly since 2007. In the past, this group has relied heavily on spear phishing email campaigns to distribute malicious Microsoft Office file attachments that are designed to install a backdoor in the operating system for remote code execution.
SEDNIT has been the backdoor malware of choice for Pawn Storm in the past. The group has also used drive-by download techniques in conjunction with compromised - albeit legitimate - websites. More recently, however, it appears Operation Pawn Storm has developed a new tactic that uses spam email to specifically target users of Microsoft’s increasingly popular Office 365 web-based productivity platform. Part of that cloud-based platform is the Outlook Web App - a service which allows users to log into email accounts from anywhere with Internet access. This is what Pawn Storm is now targeting as a way to infiltrate potentially important email correspondence within important organizations around the world. Each phishing attack works by creating two fake domains.
The first fake domain is something similar to a third-party website already known to the intended victim. For example, this first domain might be similar to that of an upcoming industry conference. The second fake domain name is designed to look like the domain name of the targeted organization’s Outlook Web-based deployment.
The phishing emails are then deployed to the targeted organization. Within this email is a link to a third-party site where non-malicious Javascript code opens the legitimate site in a new tab while simultaneously redirecting the already-active Outlook Web App session to a separate phishing site.

The purpose of the Javascript is to make the victim think his or her Outlook session has expired and prompts them to re-enter login credentials. Unfortunately, these credentials are actually entered on the fake domain and sent to the hackers behind Pawn Storm where they can be used to search for useful information within the compromised email account. This technique is especially interesting because it doesn’t rely on exploitation of known vulnerabilities and appears to work in all popular Web browsers.
Furthermore, because the victim already had an active Outlook Web App session, the victim is much more likely to re-enter login credentials than they otherwise be from an unsolicited request to enter this information.
In some versions of this attack, researchers have noticed that the hackers even went so far as to purchase legitimate SSL certificates for the fake domains to make them appear even more authentic when being used to phish for email login credentials. To avoid compromising your own email account using the Outlook Web App, always look carefully at the URL in the top of the browser before entering personal information. If there is any difference between the current URL and the one typically used to login into the Outlook Web service, refrain from entering any information until prompted to by IT personnel overseeing the deployment. If you feel that your email may already have been compromised by Pawn Storm, change your email password immediately and notify your company’s IT department.
Sweet Orange Virus Targets YouTube Users
25.10.14
Malvertising is becoming increasingly prevalent as an effective way for hackers to spread malware across the Internet. Now, it seems that one of the largest and most popular websites in the world, YouTube, is being targeted by hackers who have successfully inserted malicious advertisements into legitimate advertising channels in an effort to install malware on the computers of people clicking on YouTube advertisements. When a user clicks on an ad, traffic is directed through legitimate advertising aggregators before the traffic is rerouted to compromised websites serving malicious follows. It appears hackers are doing this by modifying the Domain Name Service information to automatically redirect advertising traffic to malicious sites serving Sweet Orange and other malware variants.
The Sweet Orange Exploit Kit
Although sometimes referred to as the Sweet Orange virus, Sweet Orange is actually an exploit kit (similar to the Black Hole Exploit Kit) designed to make serving malicious content via drive-by download extremely easy for hackers — even hackers with little or no actual programming experience. Kits like these are a favorite among “wanna-be hackers” (often referred to as script kiddies) who do not possess enough knowledge to compromise most PCs without the use of pre-written code such as that found in the Sweet Orange Exploit Kit.
This exploit kit provides many of the same features as other popular cybercrime offerings including a database that keeps track of successful infections and statistics about various exploits for popular products such as Java, Flash and Microsoft Silverlight.
Additionally, the crime kit provides users with updates about zero-day exploits for all popular Web browsers and regular Windows vulnerabilities that could allow for remote code execution. Sweet Orange allows offers hackers some improved features when compared to other popular crimeware kits including the notorious Black Hole Exploit Kit. For instance, Sweet Orange has a much smaller footprint and a higher infection rate.
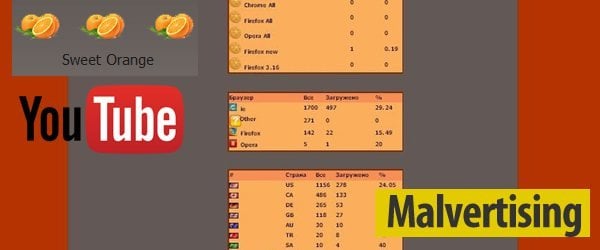
In fact, the hackers behind the development of Sweet Orange claim they can drive 150,000 unique visitors to an infected site every day. This bold claim is most likely a direct result of redirecting YouTube advertising traffic to the malicious site of the hacker’s choosing. What makes Sweet Orange especially troublesome from an Internet security standpoint is that the criminals behind the exploit kit claim that between 10% - 25% of all Internet traffic redirected to the malicious site will become infected.
If a hacker were to actually get 150,000 unique visitors per day, that means a botnet could grow by 10,000 - 15,000 machines each day (assuming the lowest stated infection rate of the exploit kit).
It’s worth noting that Sweet Orange is nothing new. In fact, this exploit kit was first observed in the wild almost three years ago. However, combining the powerful, yet lightweight exploit techniques of Sweet Orange with the massive traffic to a site such as YouTube creates a unique and dangerous malware threat that could affect millions of people within a matter of months.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion