How to remove the Quick access to Chat GPT malicious app
TrojanAlso Known As: Quick access to Chat GPT malware
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Quick access to Chat GPT?
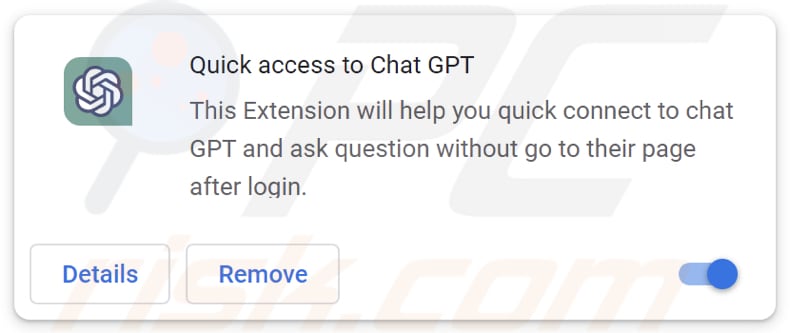
Quick access to Chat GPT is the name of a fake Chrome extension designed to steal Facebook accounts. Although most of the targeted accounts are used for business/advertising, regular users are also at risk. It is being advertised on Facebook-sponsored posts as a tool allowing users to quickly access ChatGPT directly from their browser. Although the extension provides access to Chat GPT, it also collects various data from browsers.
Quick access to Chat GPT in detail
The malicious Quick Access to Chat GPT app gathers information from the victim's browser, seizes cookies from active authorized sessions with the victim's services, and uses customized methods to take control of the victim's Facebook account.
After gaining possession of the victim's data, cybercriminals can sell it to third parties and misuse it for malicious purposes. It is known that the fake Quick Access to Chat GPT app focuses on Facebook business accounts.
Upon discovering that the victim possesses a business page, Quick Access to Chat GPT will amass Facebook account information, existing ad configurations, and financial data. Threat actors can use hijacked Facebook accounts to promote additional sponsored posts and engage in other activities (including draining the business account's funds).
Furthermore, when the malevolent Quick Access to Chat GPT is integrated into a web browser, it is capable of sending requests to any other service. This gives threat actors swift access to all of the victim's information and also permits them to act on behalf of the victim directly within their Facebook account.
More about the malicious campaign
Also, this cybersecurity threat involves a malicious (fake) Facebook application that can gain full control over the victim's Facebook profile, activity, groups, pages, businesses, advertisement accounts, and even connected WhatsApp and Instagram accounts.
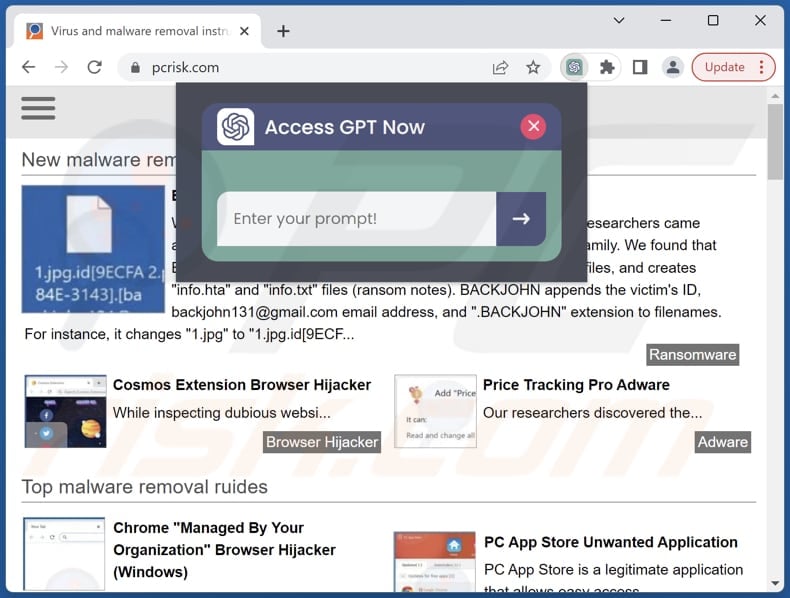
Threat actors behind this attack are using a specifically developed module called "Potal" in the extension code (Portal.ts), which automates the process of registering the malicious app on a victim's account and approving it to gain full admin mode. The "Potal" module abuses the ChatGPT popup context to send requests to Facebook servers on the victim's behalf.
The malicious Facebook app is able to request all available permissions, allowing the threat actor to access and manipulate the victim's real Facebook and associated accounts (e.g., WhatsApp and Instagram accounts).
| Name | Quick access to Chat GPT malware |
| Threat Type | Information stealer |
| Symptoms | Your computer becomes slower than normal, you cannot access Facebook or other accounts. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), torrent file downloads. |
| Damage | Loss of private information, monetary losses, identity theft, hijacked personal and business accounts. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Possible damage
The malicious app Quick Access to Chat GPT can cause significant damage if it gains control of a victim's Facebook account, particularly if it is a business account. Once in control, the threat actors behind the app can access and collect sensitive information such as Facebook account data, existing ad configurations, and financial data.
Cybercriminals can then exploit this information for malicious purposes, such as selling it to third parties, using it to drain the business account's funds, promoting additional sponsored posts, and more.
How did this app install on my computer?
It is known that cybercriminals behind the hazardous Quick access to Chat GPT used Facebook and the official Google Chrome Store for malware distribution. As for the official Google Chrome Store, the app was disguised as a legitimate extension, and cybercriminals found a way to bypass the store's security checks.
The malicious Quick access to Chat GPT app on Google Chrome Store was promoted using sponsored Facebook posts - victims ended up on the Quick access to Chat GPT's download site after clicking malicious sponsored links on Facebook.
How to avoid installation of unwanted applications?
Download software and applications from trusted sources, such as official websites and reputable app stores. Always read reviews before installing/adding apps. Avoid downloading apps with no or few reviews. Be cautious when clicking on links or downloading attachments in emails, social media messages, or other online communications.
If you are unsure if a link or attachment is safe, do not click on it. Keep your operating system, web browser, and other software up-to-date with the latest security updates and patches. Install and use anti-malware software on your devices. If your computer is already infected with rogue applications, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Quick access to Chat GPT's pop-up window:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
Remove adware from Internet browsers:
Video showing how to remove unwanted browser add-ons:
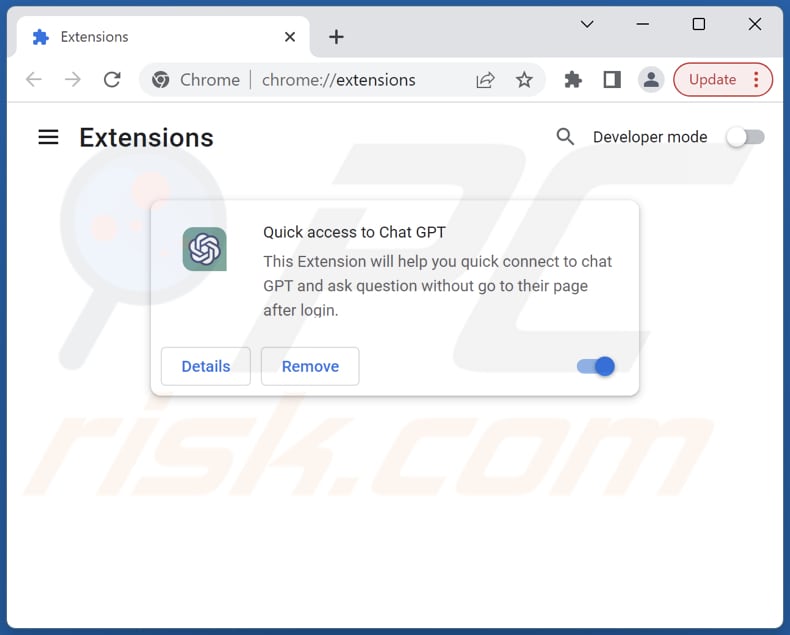
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
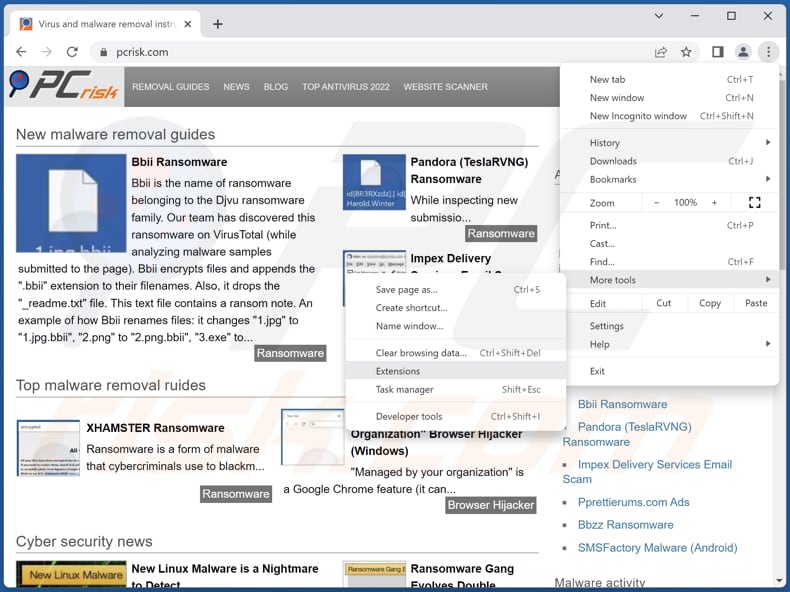
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate "Quick access to Chat GPT" and other suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate "Quick access to Chat GPT" and other suspicious extensions, select these entries and click "Remove".
Optional method:
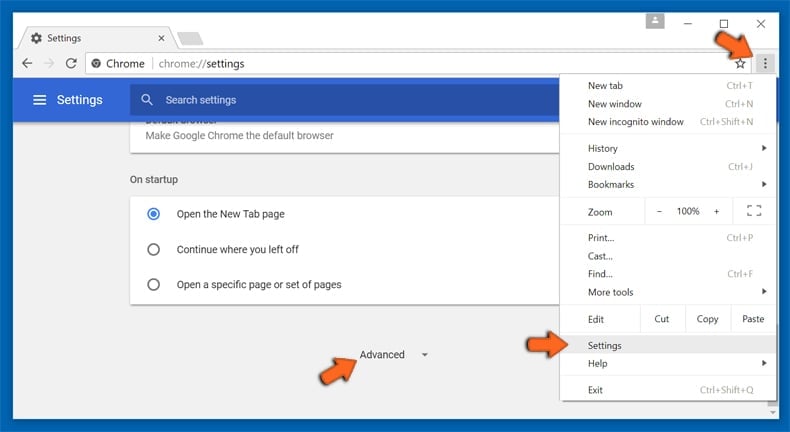
If you continue to have problems with removal of the quick access to chat gpt malware, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
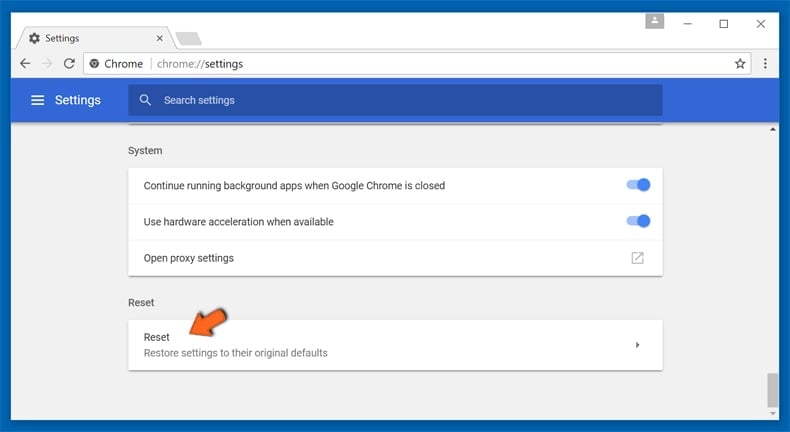
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
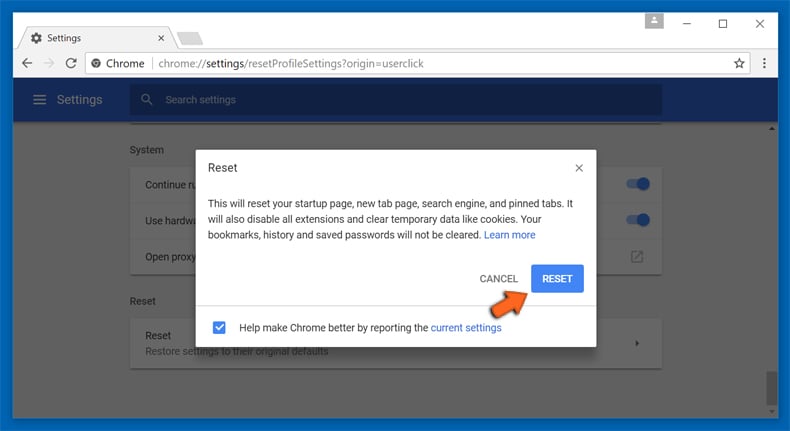
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
Frequently Asked Questions (FAQ)
My computer is infected with Quick Access To Chat GPT malware, should I format my storage device to get rid of it?
No, Quick Access To Chat GPT can be removed by following the steps provided in our removal guide above.
What are the biggest issues that malware can cause?
The consequences of malware can vary depending on the malware type. They can include identity theft, financial losses, additional infections, data loss, loss of access to online accounts, and more.
What is the purpose of Quick access to Chat GPT stealer?
Quick access to Chat GPT hijacks Facebook accounts and installs hidden account backdoors. Also, it collects various information from infected browsers, steals cookies of authorized active sessions to services.
How did malware infiltrate my computer?
Malware is distributed using malspam (emails containing malicious files or links), fake system warning messages, drive-by downloads, P2P networks, unverified software download sites, etc. Certain malware can propagate via local networks and removable storage devices like external hard drives and USB flash drives.
Will Combo Cleaner protect me from malware?
Combo Cleaner can identify and remove nearly all known malware infections. However, it is important to note that sophisticated malware often conceals itself deeply within the system. Therefore, a complete system scan is required to eliminate such malware.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion