Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is kind of malware is XLoader?
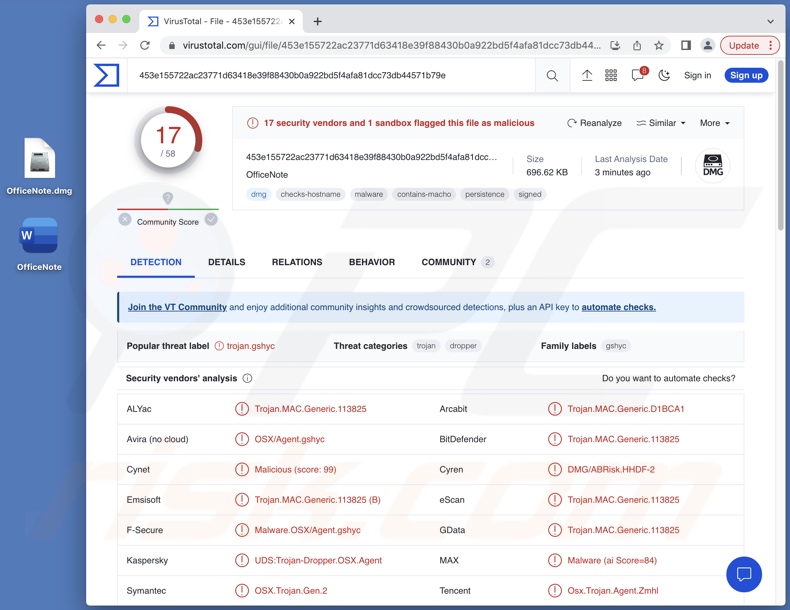
XLoader is a new variant of a malware of the same name. This XLoader version was first submitted to the VirusTotal website in July 2023. Previous versions had dependencies on Java, but this latest iteration does not. The newest malware version is written in the C programming language as well as Objective-C.
XLoader has been observed infiltrating systems under the guise of an office productivity application, which potentially means that this malware targets sensitive information related to working environments.
XLoader malware overview
XLoader has anti-detection and anti-analysis capabilities; it uses sleep commands to avoid automatic detection by security tools and includes mechanisms to complicate debugging processes.
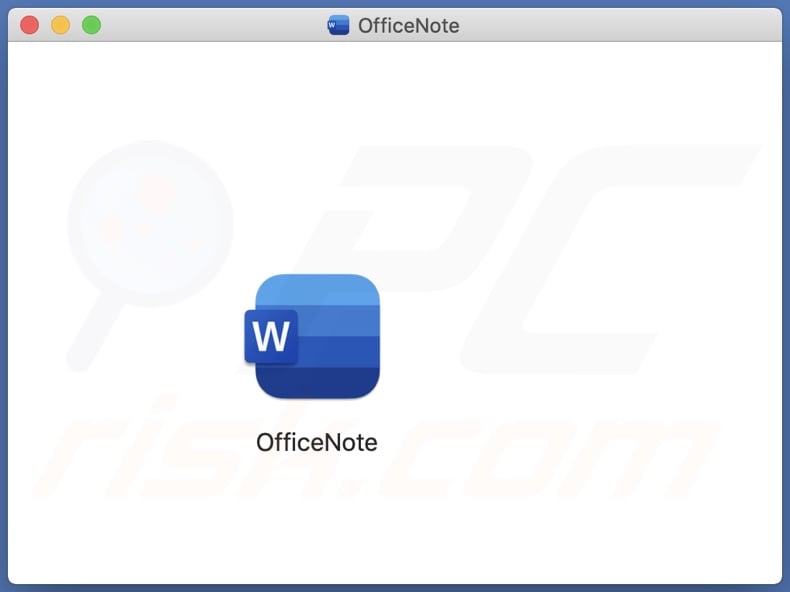
At the time of research, XLoader infiltrated systems disguised as an app named OfficeNote. The malware arrives onto devices bundled within an Apple Disk Image file titled "OfficeNote.dmg" (filename may vary).
XLoader's appearance on VirusTotal is close to the date that its Apple developer signature ("MAIT JAKHU (54YDV8NU9C)") was registered – July 17, 2023. While the signature is no longer valid, this might not stop XLoader's launch and infection chain.
After the malicious file is executed, the OfficeNote app displays an error alert claiming that it cannot be opened as the original item cannot be found. In the background, the malware's payload and LaunchAgent are dropped.
The former is placed in the home directory and launched. The payload fashions a minimalistic application in a hidden directory, while a copy of itself is utilized as the primary executable. Note that the names of the app, executable, and hidden directory are created randomly.
The LaunchAgent is inserted in the Library folder; much like in previous XLoader's variants, the agent is used to distinguish run sequences.
The main functionalities of this malware relate to data theft. XLoader targets browsers, specifically Google Chrome and Mozilla Firefox.
Generally, cyber criminals seek to acquire the following data from browsers: browsing and search engine histories, Internet cookies, log-in credentials (i.e., usernames/passwords), personally identifiable details, credit card numbers, and other sensitive information. Another feature of XLoader is stealing content copied into the clipboard (copy-paste buffer).
It is noteworthy that malware developers often improve upon their software; hence, potential future iterations of XLoader could have additional/different abilities or features.
In summary, the presence of software like XLoader on devices can result in severe privacy issues, financial losses, and identity theft.
| Name | XLoader virus |
| Threat Type | Mac malware, Mac virus, Trojan, password-stealing virus, spyware. |
| Detection Names | Combo Cleaner (Trojan.MAC.Generic.113825), Emsisoft (Trojan.MAC.Generic.113825 (B)), ESET-NOD32 (OSX/XLoader.C), Kaspersky (UDS:Trojan-Dropper.OSX.Agent), Sophos (OSX/XLoadr-B), Full List Of Detections (VirusTotal) |
| Symptoms | Malware is designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Mac malware examples
We have investigated countless malware samples; Realst stealer, KEYSTEAL, ShadowVault, and Geacon are just a few of our articles on malicious programs targeting Mac operating systems.
Malware can have a broad range of functionalities that can be in varied combinations. However, regardless of how it operates, whether a program causes chain infections or steals passwords, its presence on a system endangers device integrity and user safety. Therefore, it is paramount to eliminate all threats immediately upon detection.
How did XLoader infiltrate my computer?
At the time of writing, XLoader was offered for sale online. Hence, how it is spread depends on the cyber criminals using it at the time. Malware is predominantly proliferated by employing phishing and social engineering tactics. Malicious software is usually disguised as all bundled with ordinary program/media files.
The most commonly used distribution techniques include: drive-by (stealthy/deceptive) downloads, dubious download channels (e.g., freeware and free file-hosting websites, Peer-to-Peer sharing networks, etc.), malicious attachments and links in spam mail (e.g., emails, PMs/DMs, SMSes, etc.), online scams, malvertising, pirated programs/media, illegal software activation ("cracking") tools, and fake updates.
Furthermore, some malicious programs can self-spread through local networks and removable storage devices (e.g., USB flash drives, external hard drives, etc.).
How to avoid installation of malware?
We highly recommend being careful while browsing since fake and dangerous online content usually appears legitimate and innocuous. Caution must be extended to incoming emails and other messages. We advise against opening attachments or links present in dubious/irrelevant mail, as they can be malicious.
Another recommendation is to download only from official and verified sources. Additionally, all programs must be activated and updated by using genuine functions/tools, as those acquired from third-parties may contain malware.
We must emphasize the importance of having a dependable anti-virus installed and kept up-to-date. Security software must be used to run regular system scans and to remove threats/issues. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
XLoader malware disguised as the OfficeNote app:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
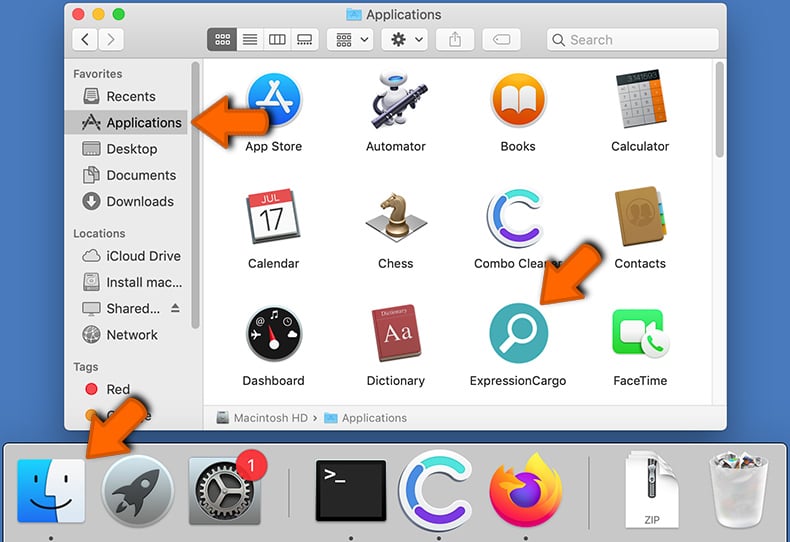
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Frequently Asked Questions (FAQ)
My computer is infected with XLoader malware, should I format my storage device to get rid of it?
No, XLoader's removal does not necessitate formatting.
What are the biggest issues that XLoader malware can cause?
The dangers associated with an infection depend on the malicious program's capabilities and the cyber criminals' aims. XLoader has data-stealing functionalities. It infiltrates systems under the guise of "OfficeNote" – an office productivity app, which tentatively suggests that this malware targets work environments.
In general, such infections can lead to severe privacy issues, financial losses, and identity theft. However, targeted attacks against companies or other large entities can carry threats of greater significance.
What is the purpose of XLoader malware?
In most cases, malware is used for profit. However, attackers can also use malicious software to amuse themselves, carry out personal vendettas, disrupt processes (e.g., services, sites, companies, etc.), and even launch politically/geopolitically motivated attacks.
How did XLoader malware infiltrate my computer?
Malware is predominantly proliferated through drive-by downloads, online scams, spam emails and messages, malvertising, dubious download sources (e.g., freeware and third-party websites, P2P sharing networks, etc.), illegal software activation tools ("cracks"), and fake updates. Some malicious programs can even self-spread via local networks and removable storage devices.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is designed to scan devices and remove all manner of threats. It can detect and eliminate nearly all known malware infections. It must be stressed that performing a full system scan is crucial since sophisticated malicious programs tend to hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion