Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is BiBi?
BiBi is a type of malware known as a wiper, and it targets both Linux and Windows users (there are two variants of BiBi targeting different operating systems). Wiper malware is a destructive form of malicious software designed to erase or damage data on infected systems irreversibly. A group of hackers with ties to Hamas may be responsible for creating BiBi.
More about the BiBi data wiper
BiBi wiper represents a class of malicious software designed with a singular and destructive purpose: to irreversibly erase or damage data on infected systems. Unlike other types of malware that may focus on data theft, surveillance, or financial gain, wiper malware is characterized by its intent to cause significant disruption and destruction to targeted systems.
The primary goal is to render data and often entire systems unusable, leading to operational paralysis and data loss. Wiper malware can manifest in various forms, utilizing techniques that make data recovery challenging, if not impossible. It may overwrite critical files, modify system configurations, or encrypt data beyond recovery.
The motivations behind wiper malware attacks can vary widely, encompassing ideological, political, or strategic objectives. In the case of BiBi, it appears to be used by hackers affiliated with the Hamas group.
BiBi is noted for its selective destruction of files, excluding those bearing .exe, .dll, and .sys extensions, as these file types are integral for the proper functioning of a computer. These specific extensions are hardcoded within the malware's code, ensuring they are bypassed during the wiping process, allowing the malware to execute its intended course of destruction.
During the wiping operation, the targeted files undergo a transformation where they are filled with random bytes, rendering them both unusable and irrecoverable. The malware's functionality extends to the deletion of shadow copies within the system, presenting a significant hurdle for users attempting to recover their files unless they possess an offline backup.
| Name | BiBi data wiper |
| Threat Type | Data Wiper |
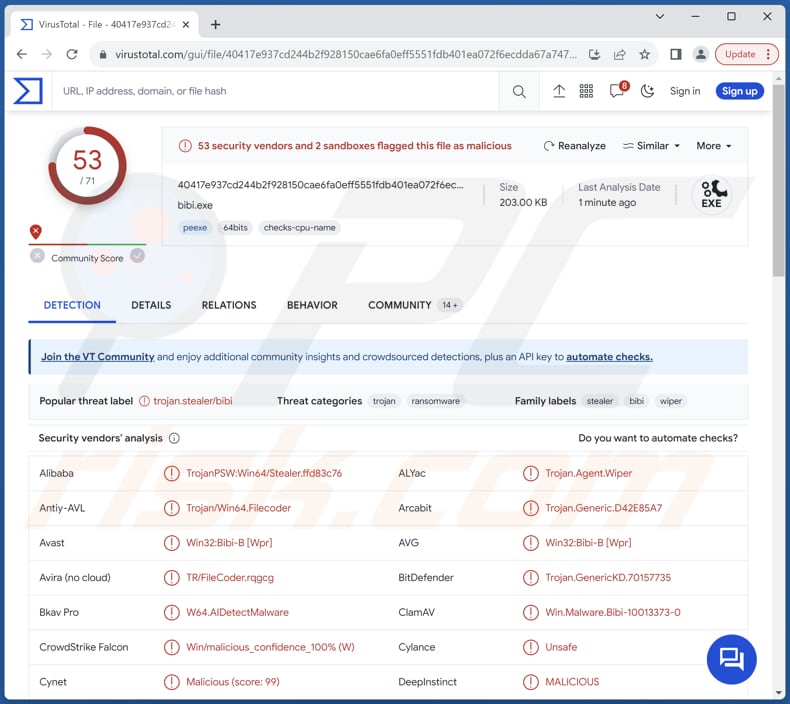
| Detection Names | Avast (Win32:Bibi-B [Wpr]), Combo Cleaner (Trojan.GenericKD.70157735), ESET-NOD32 (Win64/Filecoder.KL), Kaspersky (Trojan-PSW.Win64.Stealer.grj), Microsoft (DoS:Win32/WprBlightre.B!dha), Full List (VirusTotal) |
| Symptoms | Targeted files are destroyed |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Data loss |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Possible damage
In conclusion, BiBi emerges as a distinctive and destructive form of malware with a notable capacity for selectively targeting files crucial for a computer's functionality, while sparing essential system files with specific extensions. The malware employs a meticulous wiping process, filling targeted files with random bytes and rendering them irrecoverable.
Users and cybersecurity professionals alike are advised to remain vigilant and implement robust protective measures to mitigate the risks associated with this destructive malware.
How did BiBi infiltrate my computer?
Users may unknowingly download and execute malware when opening attachments or clicking on links received from cybercriminals via email, leading to a ransomware infection. Another avenue for malware infection is malvertising, where attackers inject malicious code into advertisements on websites. Clicking on these ads can open malicious websites or trigger the automatic download of malware.
Pirated software, cracking tools, key generators, P2P networks, third-party downloaders, etc., are other channels commonly used for malware distribution. In other cases, threat actors use Trojans or exploit software vulnerabilities to infect computers.
How to avoid installation of malware?
Exercise vigilance when receiving emails, particularly from unfamiliar or unexpected origins. Refrain from clicking on links or downloading attachments sent by unverified sources. Download apps and files from reliable sources such as official websites and stores, and avoid downloading pirated software, cracking tools, or similar content.
Do not click suspicious advertisements and pop-ups, especially while on questionable pages. Install reputable antivirus or anti-malware software on your computer. Keep the operating system, security software, and all applications up to date. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Update May 21, 2024 – new variants of BiBi malware have been discovered. These versions do not delete shadow copies, nor do they disable Error Recovery screens. Instead, BiBi now erases the disk partition table, thus further complicating recovery processes.
Additionally, the latest variants corrupt files (as in the previous versions, excluding critical system files) with random data, and they add an extension containing its name – "BiBi" – to the filenames. These wiper programs are set to target Israeli systems exclusively.
Certain attacks involving BiBi have been linked to a threat actor referred to as Void Manticore (aka Storm-842), which it is speculated is associated with The Ministry of Intelligence of the Islamic Republic of Iran (MOIS). There is some evidence suggesting that Void Manticore has carried out BiBi infections in cooperation with a different Iranian threat actor named Scarred Manticore.
The multistage attacks were initiated by exploiting a Microsoft Sharepoint vulnerability tracked as CVE-2019-0604. It is believed that the initial stages are handled by Scarred Manticore, while the later payloads, lateral movement on the network, and data wiper (e.g., BiBi) execution – are managed by Void Manticore.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with malware, should I format my storage device to get rid of it?
Erasing malware by formatting your storage device is a potent solution, albeit a drastic one that entails the complete loss of data on the device. Prior to opting for formatting, it is advisable to explore alternative methods, such as employing trustworthy antivirus or anti-malware software to scan and eliminate the malicious software.
What are the biggest issues that malware can cause?
Malware can cause many serious issues, from compromising personal privacy to disrupting critical infrastructure. One major concern is data theft, where sensitive information like passwords, financial details, or personal documents is pilfered for illicit purposes. Additionally, malware may lead to system crashes, slowdowns, or unauthorized access, jeopardizing the integrity and functionality of computers and networks.
What is the purpose of BiBi malware?
The purpose of the BiBi wiper is to destroy data on infected systems irreversibly.
How did a malware infiltrate my computer?
Malware often gains entry through various channels, such as harmful email attachments, deceptive phishing links, or visits to compromised websites. Outdated software or operating systems provide another pathway for malware infiltration. Furthermore, downloading files from unreliable sources, interacting with misleading ads, or utilizing infected external devices are potential vectors for introducing malware to a system.
Will Combo Cleaner protect me from malware?
Combo Cleaner effectively detects and removes almost all known malware infections. Running a full system scan is crucial as high-end malware tends to hide deeply within the system.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion