HorizonElite Adware (Mac)
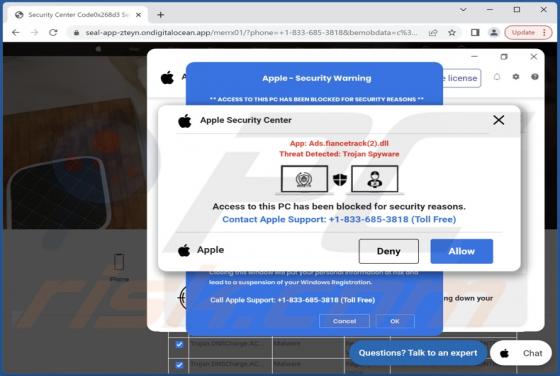
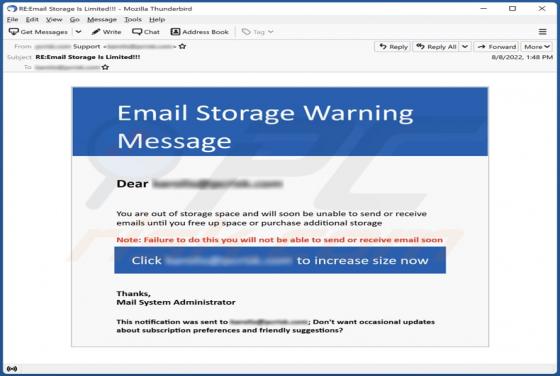
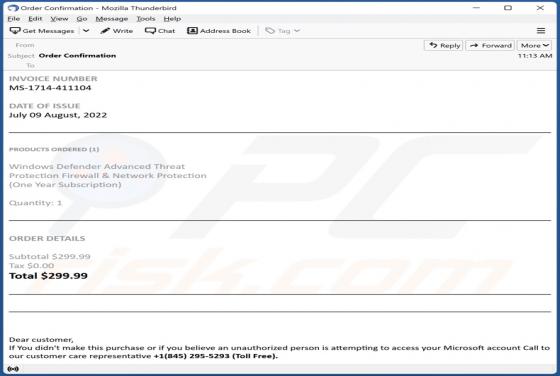
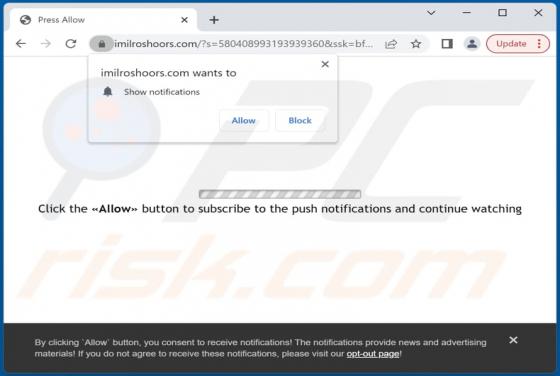
After examining HorizonElite, we learned that it is a useless application that generates intrusive advertisements. Apps that show ads are classified as adware. We discovered HorizonElite while analyzing deceptive web pages suggesting that installed software is outdated. This app is distributed v