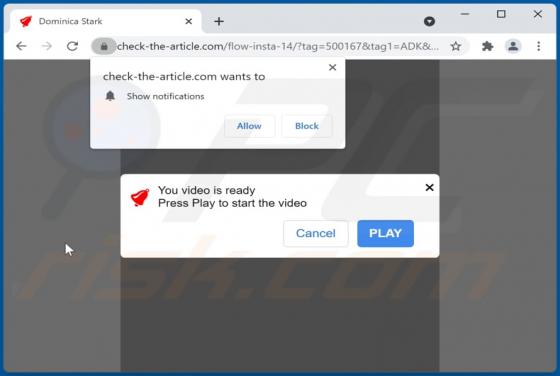
Check-the-article.com Ads
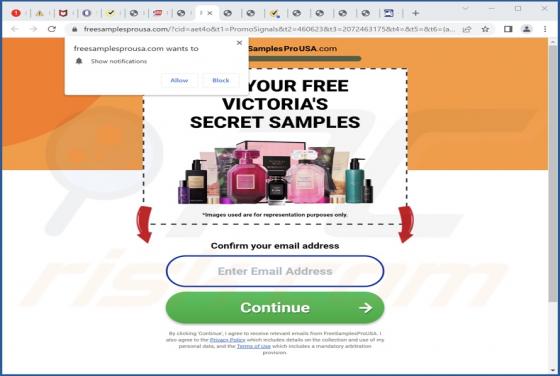
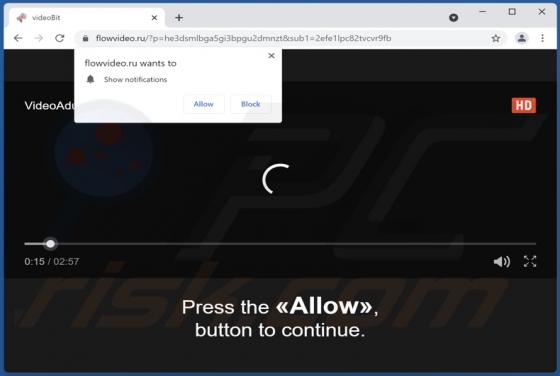
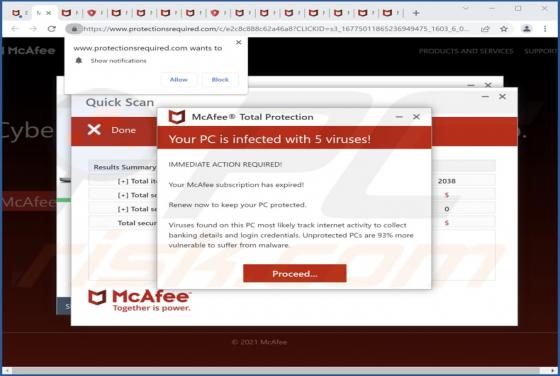
Check-the-article[.]com is a deceptive page that we have found while inspecting other pages of this kind (illegal movie streaming pages, torrent sites, and similar). It displays deceptive content to trick visitors into allowing it to show notifications. Also, it redirects visitors to other untrust