Giuliano Ransomware
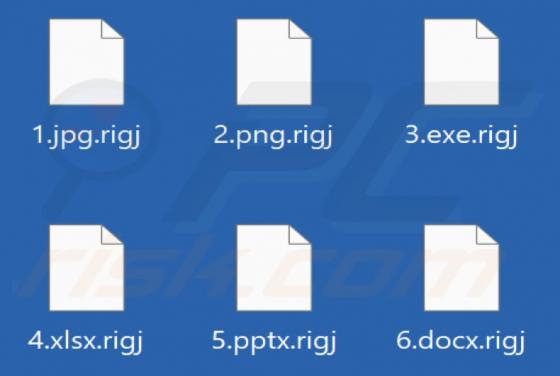
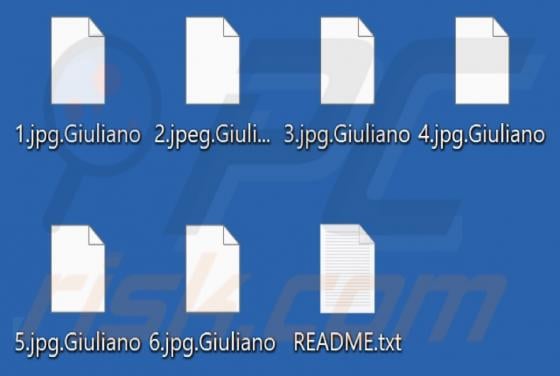
Giuliano is a piece of malicious software classified as ransomware. This type of malware encrypts data (i.e., renders files inaccessible) and demands payment for the decryption. This ransomware appends files with a ".Giuliano" extension. For example, a file initially titled "1.jpg" would appear a