Pdfcastle.com Redirect
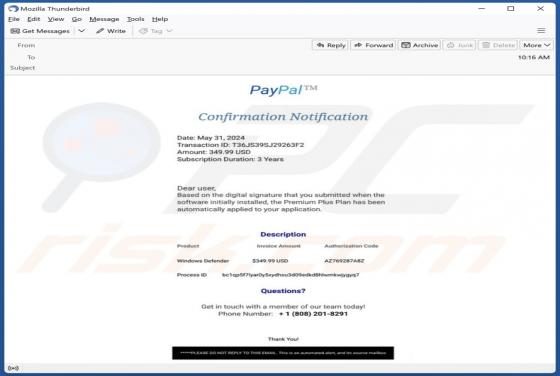
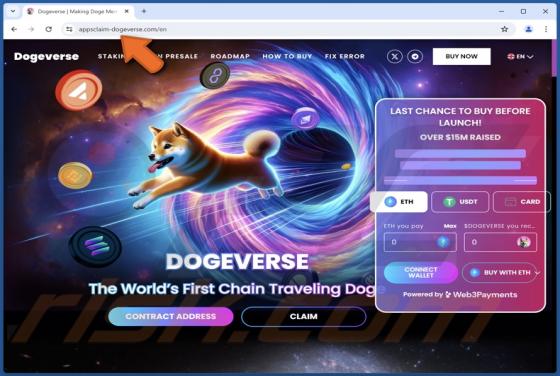
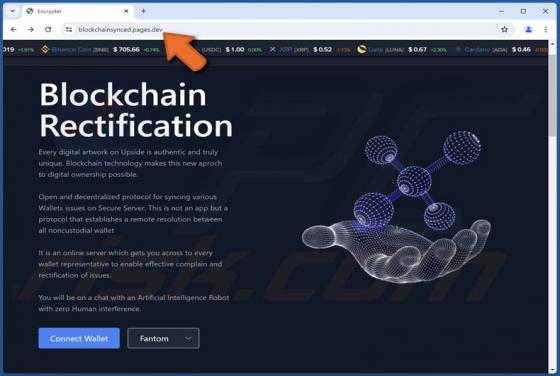
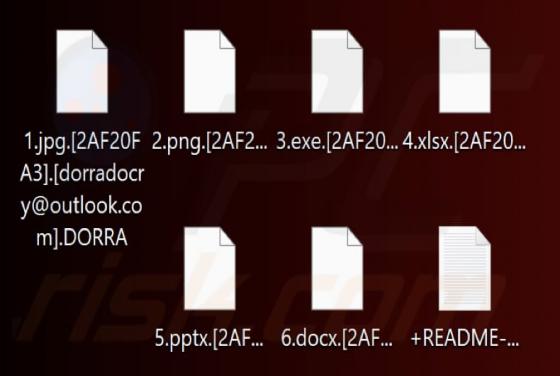
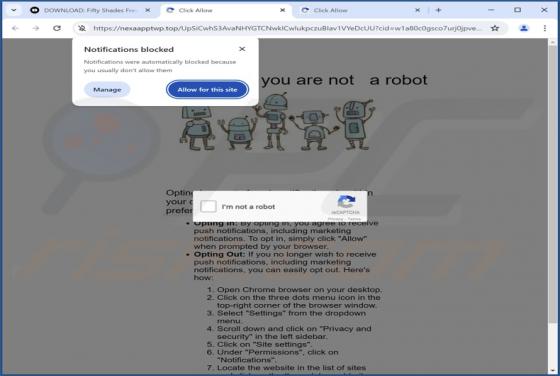
Our researchers discovered PDFCastle PUA (Potentially Unwanted Application) while inspecting untrustworthy websites. According to its promotional material, this app allows users to view, create, edit, and convert PDFs to other formats (including Microsoft Word documents). Instead of operating as