Microsoft’s Call to Stop Tech Support Scams
In the realm of cybersecurity, good news or even slightly positive news is rare. The community as a whole moves from crisis to crisis, malware variant to malware variant. There was perhaps more than a little surprise within the community when Microsoft published a veritable call to arms for teaming up with key players to put an end to the problem of tech support scams. All too often the Redmond tech giant is criticised for putting profit ahead of security, however, in recent months Microsoft has been working hard to correct this reputation. The latest article can be seen as a step in the right direction for the often criticised company.
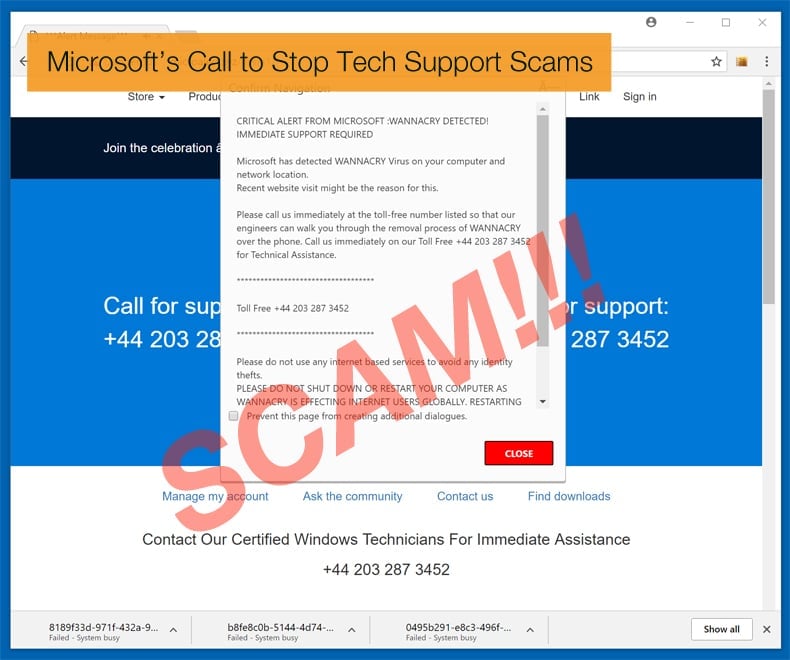
A tech support scam is simply when a scammer attempts to scare a victim into paying money for unnecessary technical support services that supposedly fix the contrived device, platform, or software problems. Here are a couple of examples of popular tech support scams: Dangerous Try To Get Access To Your Personal Logins Scam, Critical Alert WANNACRY DETECTED POP-UP Scam, Microsoft Warning Alert Scam, Google Chrome Critical ERROR Scam. This use of scare tactics may happen in a number of ways. Scammers may call you directly on your phone and pretend to be representatives of a software company. They might even effectively fake the caller ID so that it displays a legitimate support phone number from a trusted company. They can then ask you to install applications that give them remote access to your device. Using remote access, these experienced scammers can misrepresent normal system output as signs of problems.
According to Microsoft, in 2017 Microsoft Customer Support Services received 153,000 reports from customers who encountered or fell victim to tech support scams. This represented a 24% increase in incidents from the previous year. Complaints were received from 183 countries indicating that the problem is most certainly a global one. One of the reasons for the rise over the 2016 number is the scams effectiveness. On average 15% of people called paid the scammers, amounting to any amount between 200 and 400 USD. In December 2017, Microsoft received a report of a scammer emptying a bank account of 89,000 EUR during a tech support scam in the Netherlands. According to a research paper sponsored by Microsoft, it was revealed that two in three respondents reported experiencing some form of tech support scam in the previous 12 months, with nearly one in ten losing money. However, as with many social engineering attacks, it’s tricky to put an absolute number on the problem.
More than just Scammers
Tech support scams are seldom the work of one individual; they tend to be the work of organized cybercriminal organizations. While there are several different types of scam the result and aim are similar, that being trying to get a victim to part with their money. Whether the attackers use scam websites, cold calls, malware, or spam email campaigns many convince the victim to install Remote Administrative Tools (RAT). Such a tool allows the scammer control of the device.
Once a RAT is installed scammers can make changes to the device or point out common non-critical errors, and present these as problems needing an immediate and costly solution. This supposed solution is then provided by the scammer pretending to be a valid tech support company. A popular way to do this exploited the Event Viewer to convince victims that there is indeed a problem.
Microsoft’s proposed Solution
Microsoft contends that because the problem is a global and industry-wide problem it requires the industry as a whole to combat the problem. Its impact spans various platforms, devices, software, services. This has led Microsoft to create and support partnerships with other industry leaders including web hosting providers, telecommunication companies, and antivirus solution providers. One of the key partnerships will be the industry working with law enforcement agencies to go after scammers. A good example of this occurred in 2017. In May of that year, the Federal Trade Commission (FTC) announced that it was going after those behind tech support scams. Along with federal, state and international law enforcement partners, they called the plan “Operation Tech Trap”. However, it was not only law enforcement agencies in partnership but companies like Microsoft who also assisted the operation.
In the instance of Microsoft’s help, a group of Microsoft researchers at their dedicated Digital Crimes Unit used artificial intelligence to help unravel the complex web of technical tricks the scammers were using to swindle users and avoid law enforcement. To catch the scammers researchers had to first to figure out where the attacks were coming from. This was no easy task, since they often only used an IP address, or virtual home, for a day or less before moving on to another location to avoid being caught. Then to find those behind the scams a model was created that looked for content that behaved in a way that was consistent with the scam, such as creating a pop-up that refreshed in microseconds to give the appearance it wasn’t going away. This created massive amounts of data. So much data that the researchers could not hope to analyze it all themselves. The application of artificial intelligence was key to sift through all the data in order to make sense of it all and enable law enforcement to make arrests.
Education is the Key
While such partnerships are important Microsoft, like many experts, contend that education is the key. Educating all users as to how scammers operate is key to the crackdown. As these scams are classified as social engineering campaigns at heart they are dependent on convincing or intimidating a victim to do as they wish. Part of this education will involve all partners publishing blogs, websites, videos, and social media campaigns on the latest tech support scam trends and tactics. Enabling users to report such scams is also valuable.
With Microsoft looking increase industry partnerships to combat this scourge perhaps we will see far more cooperation with the aim of making cybercrime a less profitable and less appealing choice.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion