Adwind Trojan Seen Targeting Utility Companies
Last week this publication covered how the Cerberus banking trojan was filling a gap in the malware-as-a-service market (MaaS) left by a crackdown on other similar trojans. The threats posed by MaaS schemes was briefly looked at in that article. As if to put a finer point on threat security researchers have discovered a recent campaign of the trojan Adwind been distributed in a campaign targeting utility companies. Adwind, also called jRAT, AlienSpy, JSocket, and Sockrat, has been active in one form or the other since 2013 and like Cerberus adopted the MaaS model.
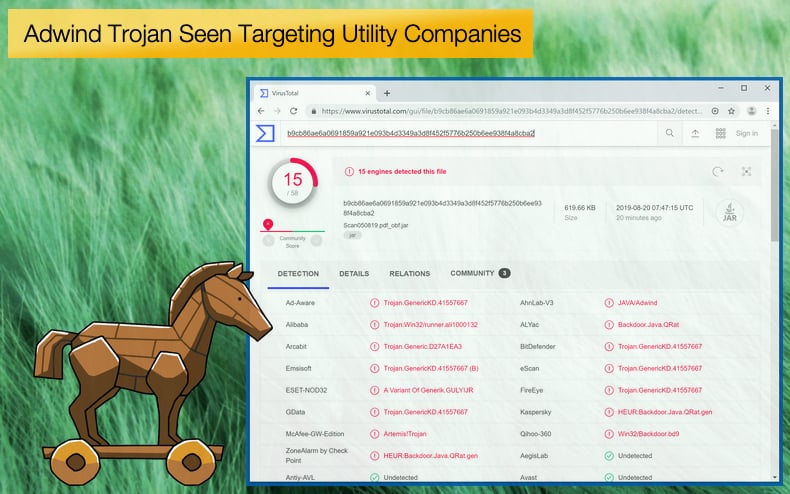
According to a report by security firm Cofense, the newest campaign distributing Adwind was discovered by its researchers. The malware is distributed by a phishing campaign using emails from a compromised company server. The email contains a PDF file which contains the malicious payload. Further, the malware is rented out to threat actors for a subscription fee. According to the researchers, the trojan is capable of defeating a broad spectrum of anti-virus products. However, if the product features a sandbox environment or behavior-based detection methods it will be able to detect the malware with little problem. This ability to avoid detection is critical to the malware's success but the infection chain begins earlier with the receiving of the phishing email.
The use of phishing emails attached with malicious files, or links redirecting victims to compromised servers, is the standard operating procedure for those wanting to illegally benefit from the malware. In the past, the trojan has been seen targeting a large array of industries, including finance, telecom, software, energy, and government. In the latest campaign, the emails favored by the attackers are been sent by a compromised business account for Friary Shoes, the malware is also been hosted on the company server.
The malicious PDF file is in truth a jpeg file which contains a malicious hyperlink which when opened will redirect the user to the malicious URL and then download the malware. Once downloaded on the targeted machine the malware will contact the attacker's command and control server so that data can be transferred. The next step of the infection chain is to avoid detection the trojan does this by exploiting the Windows taskkill used by the operating system to end processes. The malware uses taskkill to detect and end processes associated with popular anti-virus detection and analysis processes, thus evading detection.
The Adwind Trojan boasts the following features with information stolen been able to be successfully exfiltrated to the attacker's servers:
- Takes screenshots
- Harvests credentials from Chrome, IE, and Edge
- Accesses the webcam, record video and take photos
- Records audio from the microphone
- Transfers files
- Collects general system and user information
- Steals VPN certificates
- Serves as a Key Logger
Phishing Still an Effective Distribution Method
Phishing by definition is when cybercriminals pretend to a reputable entity and send out emails with malicious payloads. The whole aim is to get the user to click the link or attachment harboring the payload. This means that the emails can be tailored in any number of methods to try to get the user to click. When targeting businesses, or utility companies as in the example above, emails pretending to be bills or other business correspondence, in the hope that they will convince the receiver to open and with it the malware.
Given how tailored these messages are and how hackers can compromise legitimate business email accounts solely blaming the victim for the infection is far from useful. In an article published by ZDNet argues that more needs to be done to better prevent such attacks. In the case of businesses often employees have to deal with hundreds of emails nearly daily, with all it takes is one compromised email to infect an entire network. Added to this often those sending the emails to pretend to be powerful individuals within an organization, be it a CEO or CFO. This power play psychologically urges the receiver to open the email.
It is argued that employees are treated as the last line of defense to prevent cyber incidents. This seems to be a flawed plan considering some of the factors mentioned above. Another factor to consider is the cybersecurity knowledge of the employees themselves. This will vary from employee to employee and expecting them to have a baseline knowledge to prevent an attack seems unfair given their other duties. The article argues that,
“While training is all very well and good, the only way the problem of phishing attacks can get solved for good is if email and cybersecurity policies are built around the needs of the users and security providers can build software that automatically detects suspicious emails…That's difficult because attackers are constantly evolving their tactics, but some of the most basic phishing attacks are still able to bypass protections, indicating it's the technology which needs to be improved, rather than the blame being put on people.”
While the current tactics are not working and better technology needs to be developed, waiting on that technology is not an option. It has long been argued that educating workforces is key. This education needs to be done in a way that accepts the limitations of the employees. Part of this will be shifting the blame game away from the employee and accepting cyber attacks as a reality even the most aware employee could still fall victim to. In another article published by ZDNet, a comprehensive analysis of phishing is given along with advice in detecting such emails. In summary, employees should analyze the spelling and grammar, double check URLs, and email addresses for anything suspicious. It is further advised that macros are disabled and should not be enabled even though it can make life easier when dealing with repetitive tasks.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion