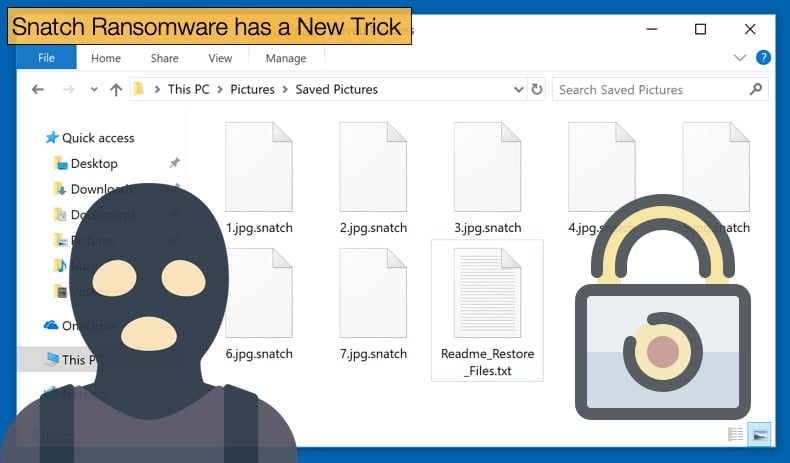
Snatch Ransomware has a New Trick
New and novel ways to further a malware main objectives do not happen too often. Hackers prefer to use tried and tested means to distribute and deploy malware. Even the development of new malware is generally done by veteran groups of hackers with a certain skillset. When a new trick is seen interest is raised accordingly amongst researchers and journalists. The trick that has gotten all the attention lately was created by the malware authors behind the Snatch ransomware. The trick involves rebooting the infected machine into Safe Mode and then encrypting files. This is done in an attempt to avoid detection.
In a recent report published by Sophos, researchers noted that the trick works because some antivirus packages do not start in Safe Mode, the mode is used to recover from a corrupted operating system. This is likely the first time such a tactic has been seen in the wild. This is novel for a second reason as the majority of malware currently circling the Internet does not persist on the machine after a reboot, meaning Snatch has been designed to persist and function after the machine has been rebooted in Safe Mode.
To do this Snatch’s malware authors discovered that they could use a Windows registry key to schedule a Windows service to start in Safe Mode. This service would run their ransomware in Safe Mode without the risk of being detected by antivirus software, and subsequently having its encryption process stopped.
Researchers discovered the trick while investigating a ransomware infection which occurred a few weeks prior. Calling this a trick may be a little facetious as it is feared that other ransomware operators and hackers will look to deploy similar tactics in the future. This trick may indeed start a trend that could be devastating to users and enterprises. Andrew Brandt, a malware researcher and network forensic analyst at Sophos noted,
“SophosLabs feels that the severity of the risk posed by ransomware which runs in Safe Mode cannot be overstated and that we needed to publish this information as a warning to the rest of the security industry, as well as to end-users,”
Those behind Snatch also employ other tactics that mark them as potentially dangerous to end-users and enterprise networks. One such tactic is that they are not reliant on mass-distribution methods like email spam campaigns or browser-based exploit kits. Instead, they are seemingly hyper-focused on only a few targets at a time. The group seems to have started active operations in the summer of 2018, and only appears to target companies and government organizations. This approach has been termed “big game hunting”
Snatch another Big Game Hunter
Big game hunting, the term is given to hackers who purposefully target large corporations and government organizations, has been adopted by several ransomware operators including Sodinokibi and Ryuk two of the most prolific ransomware strains currently being encountered. The idea behind big game hunting is that instead of going after the small ransom fees malware authors can extract from home users, crooks go after large corporations and government organizations, from where they can ask for ransom fees that are hundreds of thousands of times bigger. Another reason for targeting much larger networks is often the costs associated with data recovery, company downtime, and the hiring of forensic specialists can far outweigh the ransom, placing those paid to make the important decisions more tempted to pay the ransom.
How the operators of Snatch breach networks is also a matter of interest to researchers. According to Sophos rather than using advanced hacking techniques the group buys their way into corporate networks. Researchers say they tracked down ads the Snatch team has posted on hacking forums, ads meant to recruit partners for their scheme. According to a translation of the ad, the Snatch team was “looking for affiliate partners with access to RDP\VNC\TeamViewer\WebShell\SQL inj [SQL injection] in corporate networks, stores, and other companies.” Once a partner in crime was found, the group bides their time rarely moving onto the network once access can be granted. Rather they linger on the network undetected for days or in certain instances weeks. During this time the hackers slowly escalate access to internal domain controllers, from where they'd spread to as many computers on an internal network as possible. To do this, the Snatch crew used legitimate sysadmin tools and penetration testing toolkits such as Cobalt Strike, Advanced Port Scanner, Process Hacker, IObit Uninstaller, PowerTool, and PsExec. Since these are common tools, most antivirus products will not register anything untoward and raise any alarms.
Once this level of access is achieved on the corporate network they add the registry key and Windows service that starts Snatch in Safe Mode on all infected hosts and force a reboot of all workstations. Once the reboot begins so does the ransomware’s file encryption process. That is not the only way the operators of Snatch look to make money, Sophos researchers discovered evidence suggesting that the group also steals data from infiltrated networks. This data can be sold or leaked at a later date, even if the ransom was paid.
The only publically known instance of a Snatch infection occurred when SmarterASP.NET announced they had suffered a ransomware infection. This number is expected to steadily rise given how potentially dangerous the group is. Sophos recommends that companies secure ports and services that are exposed on the internet with either strong passwords or with multi-factor authentication. Since the Snatch crew is also interested in experimenting with VNC, TeamViewer, or SQL injections, securing a company's network for these attack points is also a must.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion