Zeus Sphinx Re-emerges on the Back of COVID-19
It is not by any means new to say that hackers are looking to exploit the COVID-19 pandemic, despite the misery and loss of human life the disease has already caused, for their own benefit. At the start of February, this publication reported on several malware campaigns exploiting the health pandemic. As the situation has become worse globally so too has the number of campaigns increased looking to exploit panic sentiments and get users to unwittingly download malware. The latest example of such a morally apathetic campaign was discovered by researchers for IBM’s X-Force and involves the re-emergence of the Zeus Sphinx banking trojan.
Banking trojans typically are a family of malware designed to steal banking credentials in order to hijack accounts or sell stolen credit card details and other credentials on underground forums. In recent years many variants have upgraded their code to also hunt for cryptocurrency wallet credentials as this too has become a profitable market to exploit. One of the most well-known of these trojans is Zeus which was first detected in 2007 with widespread campaign making headlines in 2009. Eventually, Zeus’ code was leaked which in turn led to a whole host of other malware strains being created. One of those was Zeus Sphinx, sometimes also called Terdot and ZLoader, with the first major campaigns been tracked by IBM in 2017. However, the malware appears to have first emerged in 2015 and was subsequently sold on underground forums for 500 USD at the time.
During the malware’s early life it was seen targeting banking institutions across the UK, Australia, Brazil, and the US. This does not appear to have changed according to research published by IBM’s X-Force in that the same institutions from the same countries are being targeted as well as any who are clients of those institutions. This time however COVID-19 is used as the social engineering hook designed to get users to download malicious documents carrying the malware. In this case, spam emails are sent to potential victims instructing them that they have to fill out an attached form to receive monetary compensation for having to stay at home to help fight increasing infection rates.
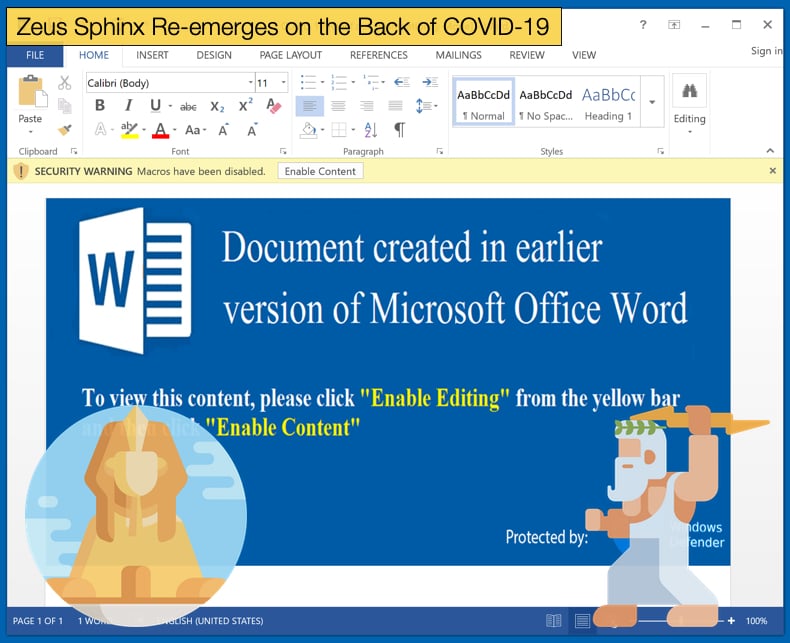
The document attached, often as .doc or .docx files, when opened will request the user to enable macros. It is requested that users do not enable macros as this is a favored tactic of hackers to begin the infection process. Once macros are enabled it allows the malware to run a malicious script using legitimate Microsoft processes to help prevent detection by anti-virus software packages.
The version of Zeus Sphinx has been determined by researchers to be a slight modification over older versions of the malware. It was also determined that once macros are enabled and the initial payload is run a downloader will begin to communicate with a command and control server under the attacker’s control. This infection stage allows for the next set of payloads, namely the newer version of Zeus Sphinx, to be downloaded and installed on the victim’s machine. In order to prevent analysis by potential victims and security software the new variant has another trick up its sleeve, its password protects the original malicious document sent via the spam email campaign. The malware relies on other tricks to remain persistent on the victim’s machine, those being namely to write itself to numerous other files as well as adding registry keys which not only help hide the malware but allow it to manage configuration files over time.
Popular Tactics
Zeus Sphinx employs other tried and tested tactics to carry out its tasks. Yet another tactic used to prevent detection by security software is the use of self-signed certificates, as signed trusted certificates attached to programs prevents them from being flagged by security software. The system is not without its flaws as it has been abused in the past to avoid detection by other malware operators. Researchers noted, in the case of Zeus Sphinx, that,
“Sphinx signs the malicious code using a digital certificate that validates it, making it easier for it to stay under the radar of common antivirus (AV) tools when injected to the browser processes. In the following example, that file is named ‘Byfehi.’”
Another popular tactic, seen in earlier versions of Zeus Sphinx which is a holdover from the Zeus v2.0 codebase, is the use of web injections. This tactic involves the injecting of malicious code in web applications, such as browsers, which then carry out specific actions depending on the malware. Zeus Sphinx will patch explorer.exe and browser processes, including those used by Google Chrome and Mozilla Firefox, to fetch injections when a user visits a target page, such as an online banking platform. The code then modifies these pages to trick them into handing over authentication details, which are then harvested and sent to the malware's command and control server. It is with this process that a potentially fatal flaw exists in the code of Zeus Sphinx. The malware appears to currently have no way of re-patching itself. This means that if the browser is updated the malware is unlikely to go through the entire process of web injections. This will further mean that the malware’s main purpose will not survive.
A Warning to COVID-19 Scammers
It has been estimated that thousands of malicious campaigns exploiting the current health crisis are currently circulating on the web. Scammers, phishers, and malware operators alike have all been quick to jump on the bandwagon and to the misery experienced. While many of the world’s health agencies and health departments have declared war on the actual disease, the UK government has further also warned scammers and the like that they will respond to their exploitative actions as well. Downing Street issued a statement stating that the government is working with social media platforms to stop the spread of misinformation which is preventing the British public from informing themselves and preventing the spread of the novel coronavirus. The statement also stated that a rapid response team will be created not only to stop the spread of misinformation but to also put an end to online scams looking to profit from the disease.
The rapid response team will consist of disinformation specialists working alongside academics along with the assistance of social media platforms. The government says it's currently dealing with up to 70 incidents a week, often based around false stories and misleading claims on coronavirus. Government ministers explained the rationale behind the creation of the rapid response team. Culture Secretary Oliver Dowden said,
“We need people to follow expert medical advice and stay at home, protect the NHS and save lives. It is vital that this message hits home and that misinformation and disinformation which undermines it is knocked down quickly…We’re working with social media companies, and I’ll be pressing them this week for further action to stem the spread of falsehoods and rumors which could cost lives.”
Further, Penny Mordaunt, Paymaster General, reiterated the need of the team, stating,
“Holding your breath for ten seconds is not a test for coronavirus and gargling water for 15 seconds is not a cure - this is the kind of false advice we have seen coming from sources claiming to be medical experts…That is why government communicators are working in tandem with health bodies to promote official medical advice, rebut false narratives and clamp down on criminals seeking to exploit public concern during this pandemic…But the public can also help with this effort, so today we implore them to take some simple steps before sharing information online, such as always reading beyond the headline and scrutinizing the source.”
The statement made by Downing Street follows warnings issued by the UK National Cyber Security Centre detailing how hackers and other cybercriminals are using the pandemic to further their aims. Paul Chichester, Director of Operations at the NCSC, said,
“We know that cyber criminals are opportunistic and will look to exploit people’s fears, and this has undoubtedly been the case with the Coronavirus outbreak…Our advice to the public is to follow our guidance, which includes everything from password advice to spotting suspect emails…In the event that someone does fall victim to a phishing attempt, they should look to report this to Action Fraud as soon as possible.”
Attacks looking to take advantage of the pandemic have been wide-ranging from ransomware attacks to the distribution of banking trojans as seen above. According to Proofpoint these attacks are steadily becoming more targeted, with greater numbers focusing on specific sectors like shipping, transport or retail to increase the likelihood of success.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion