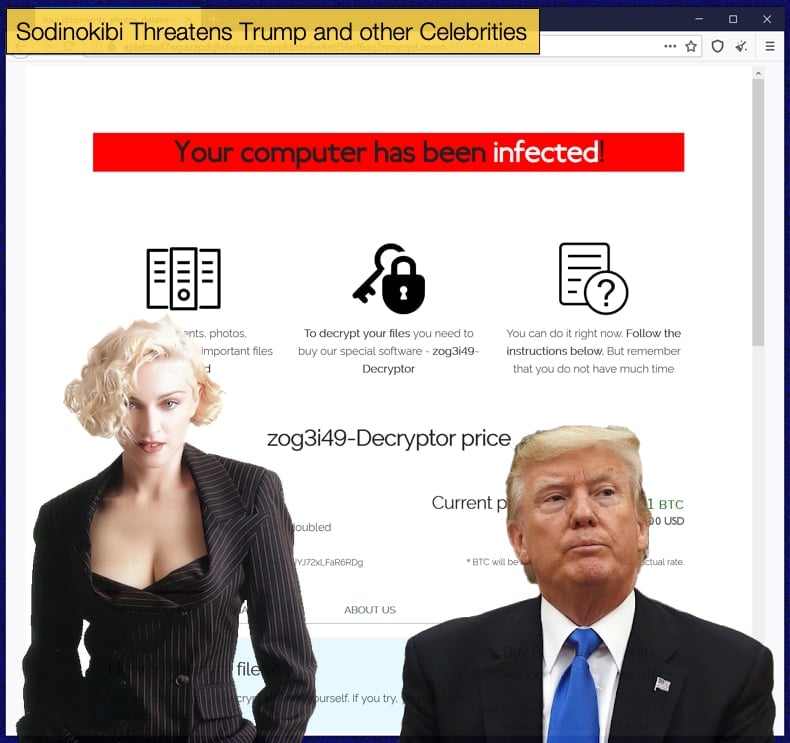
Sodinokibi Threatens Trump and other Celebrities
Sodinokibi’s, also referred to as REvil, infamy has long been covered by this publication. From exploiting Window’s zero-day flaws to how both it and Ryuk almost single-handed caused ransomware demands to spike to nearly double. Again the gang behind the ransomware has caused a stir surrounding the latest victim to fall prey to the gang. Law firm to the stars, Grubman Shire Meiselas & Sacks, is that victim. The law firm currently represents John Mellencamp, Elton John, David Letterman, Robert DeNiro, Christina Aguilera, Barbra Streisand, Bruce Springsteen, and Madonna. Further, the firm also represents large companies including, Facebook, Activision, iHeartMedia, IMAX, Sony, HBO, and Vice Media. Given the high profile of the victim and who is represented by the firm the incident garnered far more attention from large media houses than would normally be the case. News of the incident was published through media houses like Variety, who are subsequently following the story closely.
However, news of the incident initially broke on May 8, 2020, via Info-Security Magazine which claimed that the firm had fallen victim to Sodinokibi. As to who broke the story, it was the Sodininokibi gang themselves via their blog hosted on the Dark Web, ironically called “Happy Blog”. The gang claimed to have stolen 756GB of data that includes contracts, telephone numbers, email addresses, personal correspondence, and non-disclosure agreements. At the time threats were made to the extent that batches of the stolen data would be released in phases if the group was not paid the ransom amount. The amount was initially undisclosed but this was not to remain the case. Initially, the group published sensitive data pertaining to Christina Aguilera and Madonna as proof they had in their possession what they claimed.
The threat to release data is a tactic of the Sodinokibi gang with the gang moving beyond threats to releasing stolen data which is done before the gang encrypting files. This tactic was only adopted recently by gangs conducting highly targeted campaigns on high profile targets, sometimes referred to as “big game hunting”. The first ransomware operators to adopt this tactic was those behind Maze with most of the bigger ransomware players like Sodinokibi and Ryuk following suit. The threat of releasing data soon became a reality for the embattled law firm who subsequently confirmed it had indeed suffered a cyberattack.
The gang again took to its blog to make an announcement stating,
“Next. The hottest news, which we associate with GRUBMAN SHIRE MEISELAS & SACKS. Our demand was only 21.000.000$. The work was also done with the above-mentioned coveware. After 10 days, we asked how much money had been collected from the amount. The answer was 365k. Of course, we realized that people are not determined to solve the problem. Correspondingly, our tactics the same:
The initial price of the contract is currently not valid and will be increased by the timer x2, as expected;
The data will be published every week in parts. It is inevitable and systematic. Up to the payment of the ransom up to a cent.”
President Trump Allegedly Caught in the Cross Hairs
Along with the announcement the gang released sensitive documents about Lady Gaga. More was yet to come as the gang backed up their threat by doubling the demanded 21 million USD to 42 million USD. This time to apply more pressure to the Law Firm the group alleges to have sensitive information pertaining to President Donald Trump. Again the announcement was made via their blog with the gang stating,
“Grubman, we will destroy your company to the ground if we don’t see the money. Read the story of Travelex, it’s very instructive. You repeating their scenario one to one.
The next person we’ll be publishing is Donald Trump. There’s an election race going on, and we found a ton of dirty laundry on time. Mr. Trump, if you want to stay president, poke a sharp stick at the guys, otherwise, you may forget this ambition forever. And to you voters, we can let you know that after such a publication, you certainly don’t want to see him as president. Well, let’s leave out the details. The deadline is one week.
There's an election race going on, and we found a ton of dirty laundry on time. Mr Trump, if you want to stay President, poke a sharp stick at the guys, otherwise you may forget this ambition forever…To you voters, we can let you know that after such a publication, you certainly don't want to see him as President. Well, let's leave out the details. The deadline is one week.
Brazen only begins to describe the entire scenario. It is perhaps hoped that by turning the screws tighter on both the law firm and the president of the United States of America the gang can ensure that massive payday they are hoping for. As it stands the president has refused to release tax information his predecessors have as a matter of tradition, however, he is under no obligation to release his tax returns. This refusal has led to more questions than answers and combined with the fact that he is currently under investigation from a variety of different departments as to whether he committed tax fraud and was unduly influenced by a foreign power. As to whether the law represents Trump in any of his capacities is a matter for debate as no evidence currently points to the firm representing the president.
Brazen Attack
The attack has got the attention of security researchers like MalwareHunterTeam but despite the attention the attack has garnered, as well as the high profile victim’s list, the gang is operating with relative impunity. As to why the group can act with little reason to fear being caught comes down to their operation and geopolitical realities. The gang is believed to be based in Eastern Europe, likely Russia, the evidence for this comes from the malware’s code as it specifically does not target certain languages, the majority of which are spoken in Eastern Europe. The list of blacklisted languages effectively prevents the malware from running on machines with one of those languages set as the default. The language lists also include Syrian and Persian so as not to step on Russian foreign interests.
Most of Sodinokibi’s victims tend to come from Western Europe and North America, areas that have experienced a significant cooling of their relationships with the Kremlin. What does the Kremlin have to do with a ransomware gang? Very little in actual involvement but the Kremlin has tended to ignore hackers as long as they do not specifically target the Russian people or its interests. This grants those operating in Russia a certain level of immunity as long as they don’t stand on the government's toes. While the idea of allowing criminals to act with relative immunity may be shocking to the western world it may help to further Russia’s geopolitical interests as well as providing talent for state-sponsored cyber espionage and warfare operations. Viewed in that light the blacklisting of the specific languages mentioned above does make sense. This also means that unless the gang stands on the toes Putin and his allies the likelihood of the hackers being brought in front of a judge in unlikely.
Western law enforcement organizations have relied on suspected hackers traveling abroad to other nations that will allow the organization to operate or extradite a suspect. This generally involves not only an intensive investigation dependent on agreements between nations but an element of luck. Catching those responsible is not impossible but under the right circumstances can be as close to impossible as to make no difference. Reports have suggested that the Kremlin is struggling to keep a vice grip on its cyber operations, if this is true it may be harder for the Kremlin to ignore hackers within its borders as they may no longer serve the governments interest albeit non-directly. This may force the government to crack down on financially motivated hackers in the future. However, this is purely speculation and the current attitude of the Kremlin may exist as long as the current gatekeepers to power still hold the keys.
For Grubman Shire Meiselas & Sacks, it is not an academic debate about geopolitical scenarios but rather how to best to control the damage already incurred and whether or not 42 million and a potentially angered President on the re-election path are not enough to make the firm fold to demands.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion