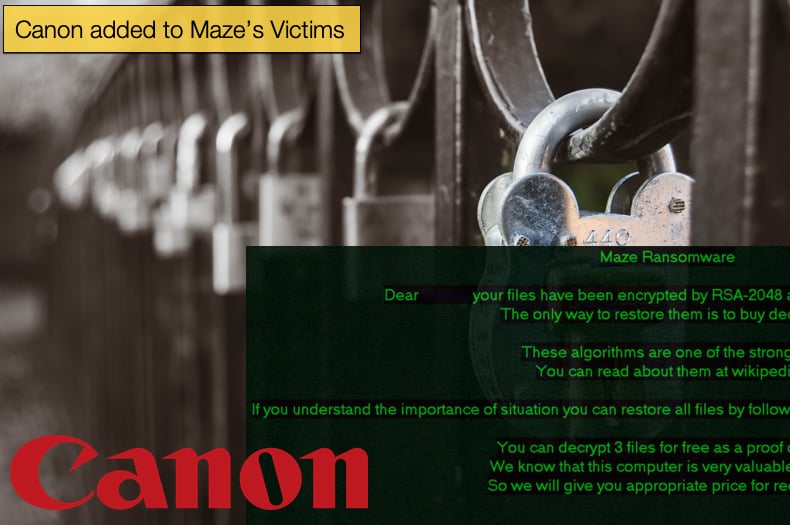
Canon added to Maze’s Victims
It seems that the world cannot go a week without yet another large company falling victim to one of the human-operated ransomware gangs. Last week Evil Corp, the gang behind WastedLocker successfully attacked Garmin resulting in the company having to shut down many of its services, including its call centers and customer chat lines. Further, fitness trackers and aviation products were severely affected by the attack. Now, the gang behind the Maze has claimed an impressive scalp in Canon, the world-famous camera and all things image-related company.
The news surfaced via a Bleeping Computer article when the writer, Lawrence Abrams, discovered that several of Canon’s services were offline. The outage impacted Canon's email, Microsoft Teams, USA website, and other internal applications. It was also noted that image.canon, the company’s cloud service for storing images, also suffered an outage, potentially putting at risk users’ data and images stored on the platform. It was later shown that the cloud service was not impacted by the ransomware attack that the image.canon outage was not related to the ransomware attack, but the same cannot be said for several other services. Further, Canon announced that no user data or images were leaked during the announcement.
 At the time of writing, it appeared that Canon had not released an official statement regarding the matter. Even the website Canon has dedicated to press releases was down. The complete list of websites offline includes:
At the time of writing, it appeared that Canon had not released an official statement regarding the matter. Even the website Canon has dedicated to press releases was down. The complete list of websites offline includes:
- www.canonusa.com
- www.canonbroadcast.com
- b2cweb.usa.canon.com
- canondv.com
- canobeam.com
- canoneos.com
- bjc8200.com
- canonhdec.com
- bjc8500.com
- usa.canon.com
- imagerunner.com
- multispot.com
- canoncamerashop.com
- canoncctv.com
- canonhelp.com
- bjc-8500.com
- canonbroadcast.com
- imageland.net
- consumer.usa.canon.com
- bjc-8200.com
- bjc3000.com
- downloadlibrary.usa.canon.com
- www.cusa.canon.com
- www.canondv.com
Bleeping Computer reached out to Canon employees to gain more information, as they suspected the company had suffered a ransomware attack. There are very few types of malware that can render an entire company’s network, ransomware being one and in particular, ransomware which targets and encrypts data shared on networks and network capable storage devices. Sources did come forward to share information including a company memo that states, “wide spread system issues affecting multiple applications, Teams, Email, and other systems may not be available at this time.” Also, a screenshot of the partial ransom note was also shared with Bleeping Computer, which revealed that it was Maze that attacked Canon and appears to have done so successfully. Bleeping Computer has a well-earned reputation for being at the forefront of ransomware analysis and news, so they can be considered more than a credible determiner of the ransomware used.
While Canon is still to confirm the incident, Maze operators have told Bleeping Computer that they have also stolen 10 TB of data. This will be in line with common tactics employed by the gang in stealing data to place increased pressure on victims to pay the ransom. Typically, if the ransom is not paid in time the data will be leaked or sold to the highest bidder. Maze was an early adopter of these tactics along with some of the more prolific ransomware gangs targeting large enterprises, sometimes referred to as big-game hunting. It was Maze, in communication with Bleeping Computer that stated the image.canon outage was not a result of their attack.
LG and Xerox have Stolen Data Leaked
In June 2020, it was revealed that South Korean electronics manufacturer, LG, was also successfully attacked by the Maze gang. Shortly, after the LG attack became news it was also revealed that business giant Xerox also suffered a Maze attack. The gang seems to be notching up big scalps at will, and this should have those tasked with defending large enterprise networks more than a little worried. However, it is now clear that the massive companies did not pay the ransom as the gang has released data pertaining to both companies. The announcement and leak were made via the gang's release portal. The gang released 50.2 GB they claim to have stolen from LG's internal network, and 25.8 GB of Xerox data.
The leak had been threatened by Maze since June and one can assume that nothing came of negotiations regarding the ransom. Of particular interest to the InfoSec community is how the gang managed to compromise the networks of such large companies, especially when it is considered that both companies operate in the technology sector with what one can assume as large budgets for cybersecurity. In an interview conducted in June with Bad Packets, the company’s founder revealed that both companies used Citrix ADC servers and probably left the vulnerability unpatched. One of Maze’s go-to vulnerabilities, CVE-2019-19781, is a flaw found in these servers but has received a patch. Other ransomware gangs are also known for exploiting this flaw to initially compromise a target network. Given that two major tech giants were compromised this way, it would not be a surprise if this was how Maze compromised Canon’s network and infrastructure. The flaw has been described by Citrix as,
“A vulnerability has been identified in Citrix Application Delivery Controller (ADC) formerly known as NetScaler ADC and Citrix Gateway formerly known as NetScaler Gateway that, if exploited, could allow an unauthenticated attacker to perform arbitrary code execution. The scope of this vulnerability includes Citrix ADC and Citrix Gateway Virtual Appliances (VPX) hosted on any of Citrix Hypervisor (formerly XenServer), ESX, Hyper-V, KVM, Azure, AWS, GCP or on a Citrix ADC Service Delivery Appliance (SDX). Further investigation by Citrix has shown that this issue also affects certain deployments of Citrix SD-WAN, specifically Citrix SD-WAN WANOP edition. Citrix SD-WAN WANOP edition packages Citrix ADC as a load balancer thus resulting in the affected status.”
The company advises users to do the following if they have not done so already,
“Exploits of this issue on unmitigated appliances have been observed in the wild. Citrix strongly urges affected customers to immediately upgrade to a fixed build OR apply the provided mitigation which applies equally to Citrix ADC, Citrix Gateway and Citrix SD-WAN WANOP deployments. Customers who have chosen to immediately apply the mitigation should then upgrade all of their vulnerable appliances to a fixed build of the appliance at their earliest schedule. Subscribe to bulletin alerts at https://support.citrix.com/user/alerts to be notified when the new fixes are available.”
Garmin Pays the Ransom
News reports began emerging on August 3, 2020, that Garmin, whose own incident was alluded to above, stating that the company had paid the ransom demanded by Evil Corp. According to reports, the company attempted to pay the ransom via another firm specializing in ransom payments. However, that firm declined to do as Evil Corp, the creators of the ransomware WastedLocker, are currently sanctioned by US authorities and negotiations or business dealing with them may result in a violation of said sanctions.
Despite this sources have said that Garmin still paid the ransom but again looked to manage negotiations through a third party. This time a firm, Arete, who is believed to handle ransom negotiations with Evil Corp managed the process for Garmin. Arete believes that US sanctions linking WastedLocker to the cybercriminal gang have not been sufficiently proven and thus believe that they can negotiate and have legal grounds to do so despite the sanctions. In support of this claim, the firm linked research disputing Evil Corps hand in Wasted Locker via Twitter. One of the article published by Sky News noted that,
“Sources with knowledge of the incident told Sky News that Garmin - an American multinational which is publicly listed on the NASDAQ - did not directly make a payment to the hackers. Separate sources confirmed to Sky News that Arete IR made the payment as part of its ransomware negotiation services, although Arete argues that WastedLocker is not conclusively the work of Evil Corp.”
Arete was contacted but declined to comment stating that the firm had contractual confidentiality clauses that it had to adhere to and subsequently would not discuss any client interactions nor client identities. The initial ransom amount has been reported at 10 million USD, it unclear whether this demand was met but often ransomware gangs are willing to negotiate. It is also unclear if data was stolen. However, in the past Evil Corp has not employed tactics similar to that of Maze that promotes the stealing and subsequent leaking of data. The truth is we may never know how much was paid to decrypt data if the allegations are true. Further, only time will tell if Garmin has run afoul of US sanctions and may face a lengthy court battle and subsequent fines in the near future.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion