Big Tech and Security Firms Partner to take on TrickBot
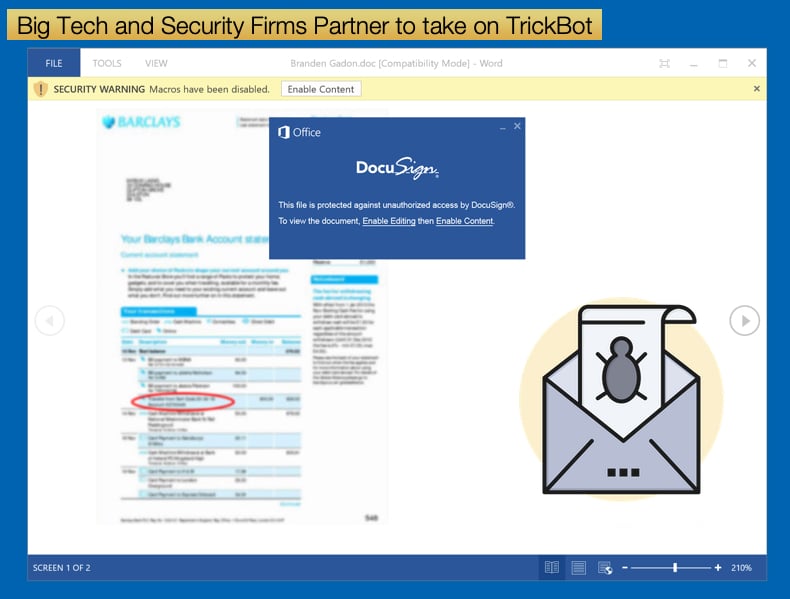
Since 2016, TrickBot has steadily become one of the major menaces faced by all those tasked with defending corporate networks. Over the last couple of years, this publication has covered several instances where TrickBot was central to causing no small amount of pain, misery, and financial loss. TrickBot began life as a banking trojan designed to steal any and all banking related credentials. It was not long until the malware evolved into a multi-faceted malware capable of conducting operations far above those of normal banking trojans seen previously.
Tracking TrickBot activity reveals this evolution rather nicely. In 2019, TrickBot was seen targeting healthcare providers acting as the initial assault on a network where it was not only there to harvest credentials but to create a backdoor onto the network so that other malware variants could be dropped onto the infected network. This led to a partnership between TrickBot and Emotet, where once TrickBot had successfully compromised a network and created a backdoor Emotet would then be dropped. This effectively turned a humble banking trojan into a hybrid trojan, malware dropper, and info-stealer. The partnership between TrickBot and Emotet was to evolve again, as Emotet partnered with the ransomware gang behind Ryuk. Now TrickBot would drop Emotet which in turn would drop Ryuk. This pattern has been seen on multiple occasions and may have been the infection vector behind the EMCOR and more recently UHS ransomware incidents.
The good news is that TrickBot’s ability to infect enterprise networks has been severely stunted. In a partnership between several key role-players, moves have been made to takeover TrickBot’s backend infrastructure including the servers known to be used by the malware’s operators. Involved in this co-ordinated takedown is Microsoft's Defender team, FS-ISAC, ESET, Lumen's Black Lotus Labs, NTT, and Broadcom's cyber-security division Symantec.
All involved spent months collecting more than 125,000 TrickBot malware samples, analyzing their content, and extracting and mapping information about the malware's inner workings. This was done to not only generate a comprehensive picture of the malware itself but the infrastructure that distributed and carried out tasks related to the malware. This backend infrastructure is often referred to as TrickBot’s botnet and included infected machines and servers used to further the aims of those behind the malware.
This information was also used as evidence when the courts were approached to grant Microsoft the power to seize control of the infrastructure. In court, Microsoft sought to place a restraining order on those operating the infrastructure, which in practice would cede control of the infrastructure over to authorities. All the relevant court documents have been made accessible to the public for all those interested in the legal wording of the court order. Since the court order, the relevant partners have approached internet service providers to notify affected parties. It is believed that over one million devices have been infected with TrickBot, effectively making it one of the world’s largest botnets. Summarizing the actions taken since the court order was given Microsoft stated,
“With this evidence, the court granted approval for Microsoft and our partners to disable the IP addresses, render the content stored on the command and control servers inaccessible, suspend all services to the botnet operators, and block any effort by the TrickBot operators to purchase or lease additional servers,”
By doing so many of TrickBot’s functions are effectively neutered. Many of the malware’s operations rely on a backend structure of servers and infected devices to carry out operations. Microsoft summarised these operations as,
“Trickbot sends information like domain names and IP ranges of compromised networks back to operators, who then select some of these networks for additional exploitation and reconnaissance activities. On selected networks, Trickbot operators installed additional tools like Cobalt Strike, and switch to a hands-on-keyboard attacks. Once the operators gain foothold on a network, they used tools like Mimikatz and LaZagne to steal additional credentials and tools like BloodHound and ADFind to perform reconnaissance actions. Apart from using the stolen credentials and collected data to further the attack, operators also exfiltrated data. They then leave multiple persistence points on the network to enable the eventual delivery of other payloads like Ryuk ransomware.”
Other Botnets Targeted
TrickBot is not the only Botnet that Microsoft has targeted this year. In March Microsoft and 35 partners across the world looked to take down the Necurs botnet. At the time it was believed to be one of the largest, if not the largest, botnets on the web consisting of nearly nine million infected devices. While the TrickBot takedown was achieved through the analysis of over ten thousand malware samples, the Necurs takedown was enabled by security researchers cracking the Necurs domain generation algorithm (DGA) used to generate seemingly random domain names to stay ahead of authorities.
The use of generated DGA domain names was often done weeks or months in advance of active campaigns. Once the campaign was active only then would devices infected with Necurs be connected to command and control servers operated by the attackers to complete instructions received by these servers.
By cracking the algorithm, security researchers were able to predict which domains would be created over a period of 25 months. In total some six million domain names were predicted to be potentially used by Necurs’ DGA. This list effectively allowed Microsoft and partners to block domain names generated by the algorithm so they could not be registered. Microsoft also approached the courts for an order to enable Microsoft to take over domains controlled by Necurs within the US. At the time it was hoped that this action and partnering with industry players around the rest of the world would effectively sinkhole the botnet by uncovering more locations across the globe used to house the malware’s backend infrastructure.
Unlike TrickBot, Necurs seems like it was specifically designed from the outset to be a botnet rather than a malware that slowly evolved to fill multiple roles. First appearing in 2012, the botnet grew to one of the largest spam-generating botnets the InfoSec community had seen. The botnet's main operation was to infect a machine than to use the infected machine to send thousands of spam emails a day when active. According to Microsoft, during a recent 58-day investigation, its engineers tracked one single Necurs-infected computer sending out more than 3.8 million emails to more than 40.6 million victims.
Typically, these spam emails are then used to deliver malware to unsuspecting users. To that extent, it is widely believed that the Necurs botnet was operated by Evil Corp, a collection of skilled cybercriminals best known for the development and deployment of the Dridex banking trojan.
Evil Corp made headlines this year when it was revealed that Garmin had suffered a major ransomware attack. The offending piece of malware was determined to be WastedLocker, Evil Corp’s ransomware variant used to extort exorbitant sums from victims. Necurs was not only used to drop malware but used in support of several scams including pump and dump stock scams, fake pharmaceuticals, and “Russian Bride” scams. It is believed that Evil Corp would rent out the botnet's infrastructure to send out spam-related scams, effectively offering scammers a botnet-as-a-service offering to the cybercriminal underground.
As to how effective the measures employed by Microsoft and partners are regarding the takedown of TrickBot and Necurs will only be answered in time. Some botnets have proved incredibly resistant to takedown attempts. One such was Kelihos which survived three takedown attempts. Authorities were only successful when the botnets creator was arrested in Spain while on vacation. The accused subsequently pleaded guilty. In the case of Necurs and TrickBot even arresting suspects may not be enough to truly sink their infrastructure given how organized the gangs that operated them have been, as well as a readiness to change tactics In an attempt to remain ahead of security researchers and authorities.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion