Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is Dridex?
Dridex (also known as Bugat and Cridex) is a malicious program that is used to steal banking credentials from users of Windows computers.
Cyber criminals proliferate this rogue software when it is downloaded and installed through a malicious Microsoft Word or Excel document. Once installed, it targets banking information. Therefore, users with computers infected by Dridex are likely to experience financial loss.
Dridex malware in detail
The main goal of this malware is to steal sensitive details relating to victims' bank accounts, such as online banking credentials. Therefore, this malicious software helps distributors and cyber criminals to access victims' bank accounts and make fraudulent transactions - effectively stealing money from unsuspecting people.
This malicious software operates as a key logger and records keystrokes (keys pressed). Cyber criminals seek to infect computers with these key loggers so they can steal logins, passwords, and other sensitive details, including banking credentials. This program is also capable of performing several 'injection attacks'.
These attacks allow injection of malware into a computer system to execute remote commands or inject code into a specific program and modify its execution/behavior. Furthermore, the latest Dridex variant is difficult to detect, since it is capable of evading anti-virus detections.
It uses file signatures that go undetected as threats, and thus Dridex bypasses virus detection engines. Additionally, this malware uses an Application Whitelisting technique to block elements of WSH (Windows Script Host). It takes advantage of a WMIC (WMI command-line) flaw by targeting a weak spot (execution policy) in the application whitelisting process.
To bypass mitigation efforts, Dridex malware loads XLS scripts that contain malicious Visual Basic Script. In summary, this is advanced malware, which is goes undetected. If you have reason to believe that your computer is infected with Dridex, remove it immediately.
| Name | Dridex virus |
| Threat Type | Trojan, Password-stealing virus, Banking malware, Spyware |
| Detection Names | Avast (Win32:Trojan-gen), BitDefender (Trojan.GenericKD.41400500), ESET-NOD32 (Win32/Dridex.CO), Kaspersky (Trojan.Win32.Chapak.druk), Full List (VirusTotal) |
| Payload | Banking trojan, keylogger |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments and compromised FTP websites. |
| Damage | Stolen banking information, logins, passwords. Injection attacks. |
| Additional Information | The latest Dridex version is capable of avoiding detection by virus detection engines. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Malware of this type in general
There are a number of malware infections used to steal personal details. Some examples are Emotet, Adwind, FormBook, and AZORult.
Typically, cyber criminals spread these programs to generate revenue by stealing personal details, distributing other malware such as ransomware, and so on. These programs can cause serious problems (financial, data loss, privacy issues, etc.). For this reason, it is important to eliminate them immediately.
How did Dridex infiltrate my computer?
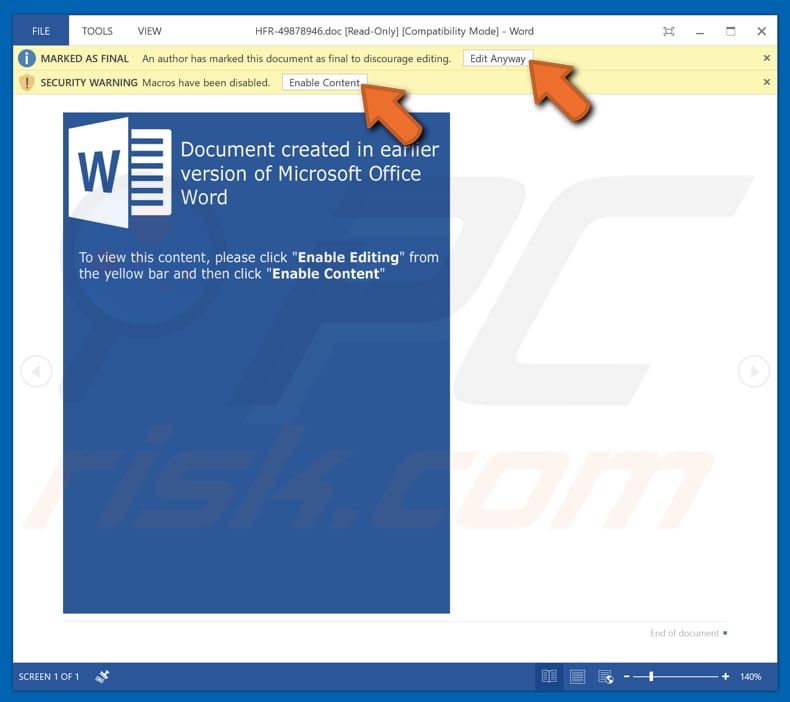
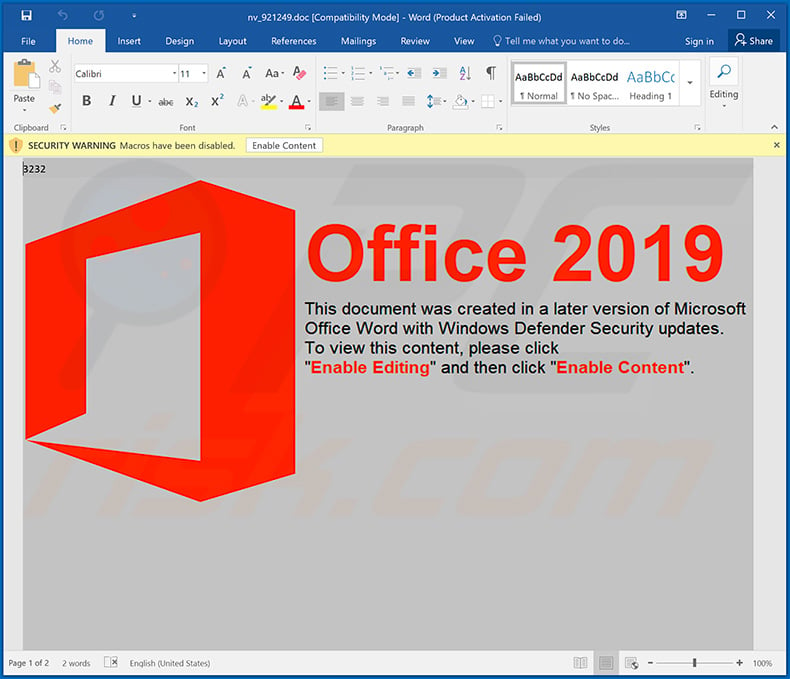
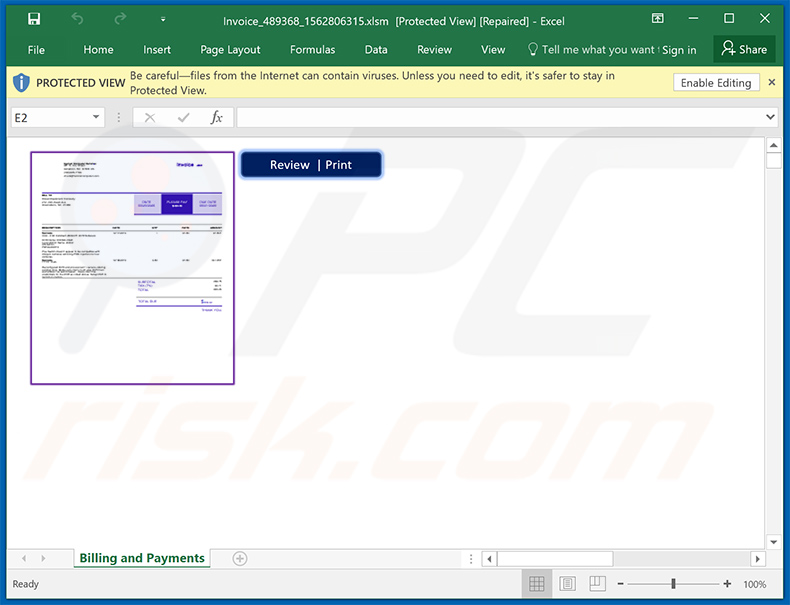
Research shows that cyber criminals poliferate Dridex through spam campaigns. They send emails that contain attached Microsoft Word or Excel files. Typically, these emails are presented as official and important. In our example, the email is disguised as a message regarding an invoice.
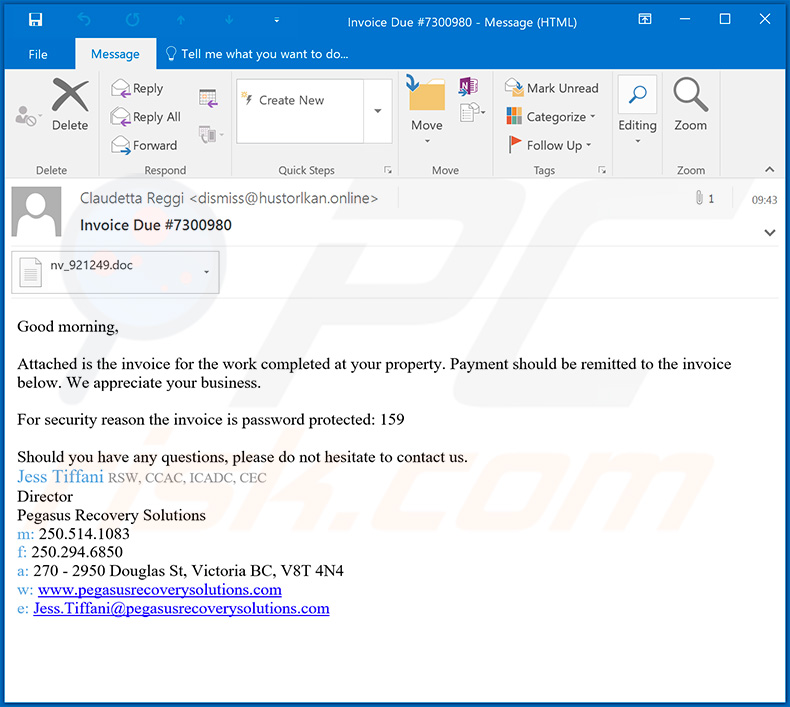
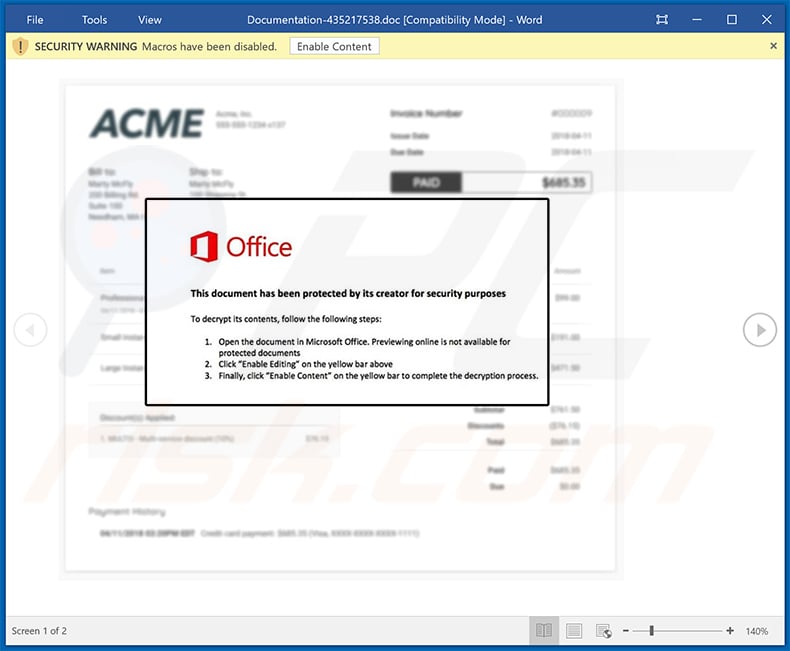
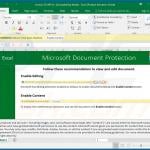
The main purpose of this spam campaign is to trick people into opening the attached file, which then causes download and installation of a malicious program. In this case, an MS Office file infects computers with Dridex. Typically, these files demand permission to enable macro commands (thus allowing content/editing).
Once this permission is given, a document starts downloading (and then installing) malicious software. In summary, these documents cannot do any damage unless they are opened and permission to enable macros is granted.
Other examples of files that cyber criminals send to proliferate malware are PDF documents, JavaScript files, executables (.exe files), and archive files such as ZIP and RAR.
How to avoid installation of malware?
Be careful with files that are attached to emails received from suspicious or unknown email addresses. Typically, these emails are irrelevant and disguised as 'important'. The best way to deal with them is to ignore them and leave files and links within them unopened. Download software and files from official websites and use direct download links.
Third party downloaders, unofficial websites, various Peer-to-Peeer networks should not be trusted. Downloading files or programs via these sources might lead to computer infections. Keep installed programs and operating systems up-to-date, however, use implemented functions or tools created by official developers only.
Do not activate installed programs with 'cracking' tools, since this is illegal and they are often designed to distribute malicious programs (infect computers with malware).
Have a reputable anti-virus or anti-spyware suite installed and enabled at all times. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Screenshot of an email that contains a malicious attachment, which is used to spread Dridex:
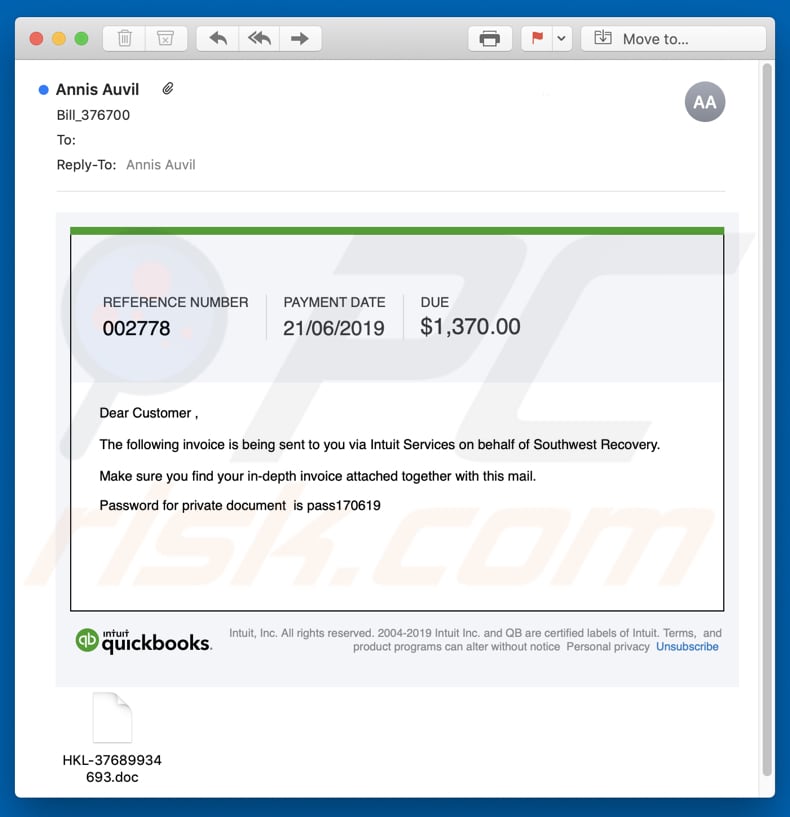
Screenshot of another spam email used to spread Dridex malware:
Text presented within this email:
Subject: Invoice Due #7300980
Good morning,
Attached is the invoice for the work completed at your property. Payment should be remitted to the invoice below. We appreciate your business.
For security reason the invoice is password protected: 159
Should you have any questions, please do not hesitate to contact us.
Jess Tiffani RSW, CCAC, ICADC, CEC
Director
Pegasus Recovery Solutions
m: 250.514.1083
f: 250.294.6850
a: 270 - 2950 Douglas St, Victoria BC, V8T 4N4
w: www[.]pegasusrecoverysolutions[.]com
e: Jess.Tiffani@pegasusrecoverysolutions.com
Screenshot of the malicious attachment (Microsoft Word document):
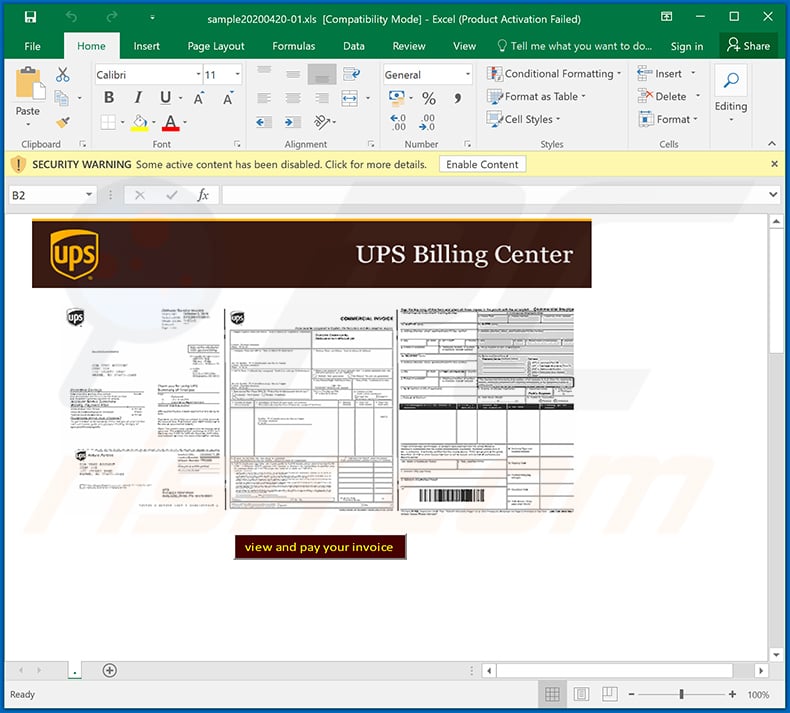
Update April 22, 2020 - Crooks have recently started yet another spam campaign disguising as UPS delivery company. They send deceptive emails encouraging recipients to open a malicious document which is presented as an invoice. Once opened, the document executes a number of commands in order to inject Dridex malware into the system.
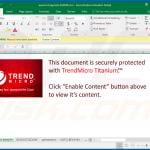
Screenshot of the malicious MS Excel document ("sample20200420-01.xls"):
Update April 28, 2020 - Crooks have recently started a Fedex-related email spam campaign to promote Dridex malware.
Screenshot of the aforementioned spam email:
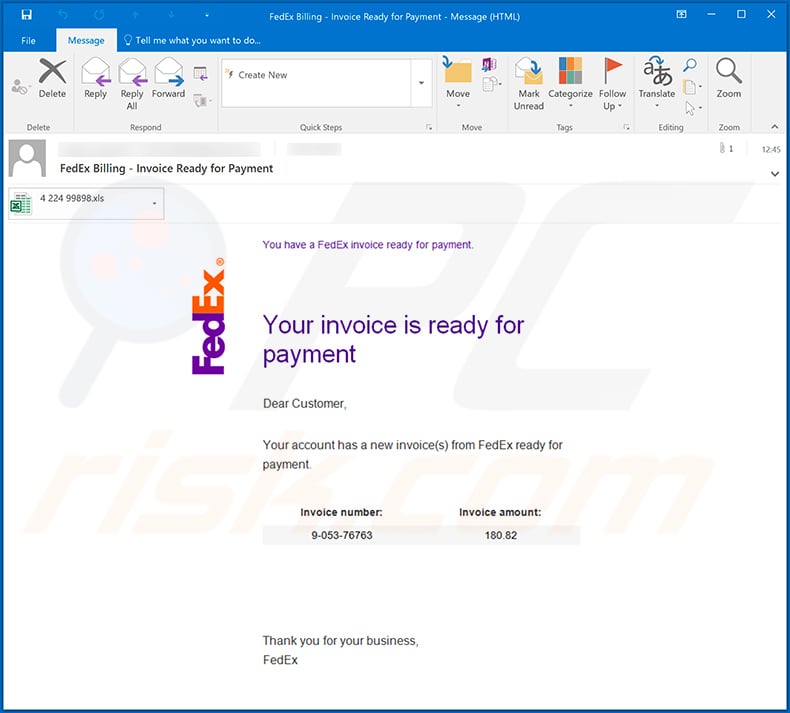
Text presented within:
Subject: FedEx Billing - Invoice Ready for Payment
You have a FedEx invoice ready for payment.
Your invoice is ready for payment
Dear Customer
Your account has a new invoice(s) from FedEx ready for payment.
Invoice number: Invoice amount:
9-053-76763 180.82Thank you for your business,
FedEx
Screenshot of the malicious attachment - Microsoft Excel document ("4 224 99898.xls"):
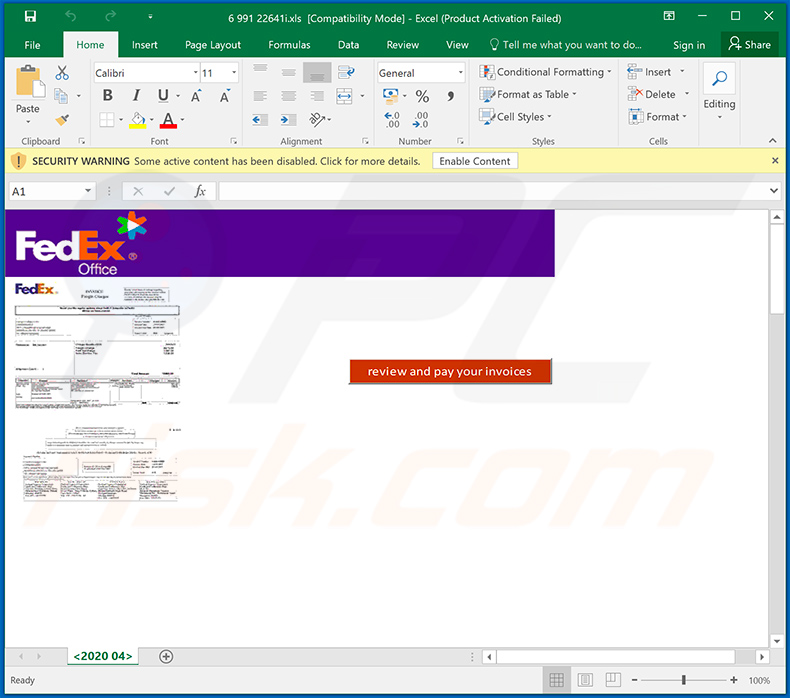
Examples of other MS Excel documents used to spread Dridex malware:
Examples of other invoice/payment/bill-relating spam emails that spread Dridex malware by delivering links that lead to malicious websites/files:
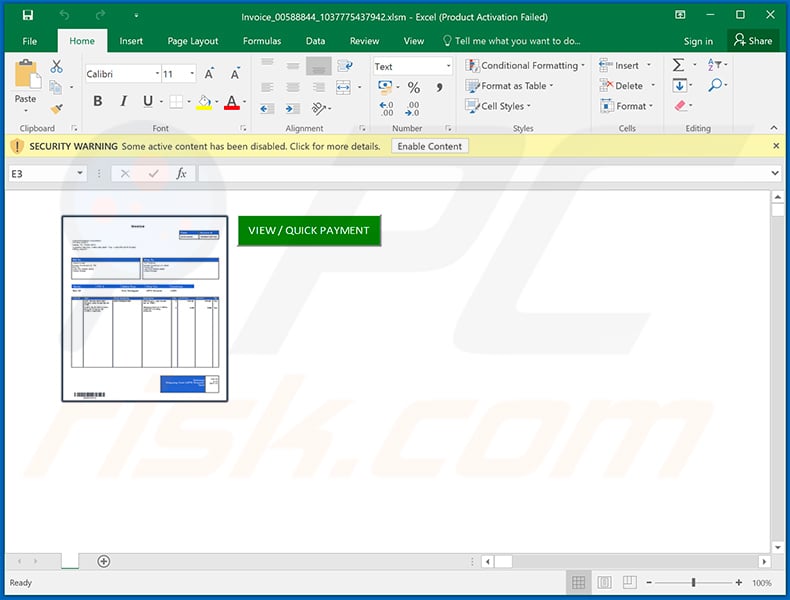
Screenshot of yet another spam campaign used to spread Dridex malware:
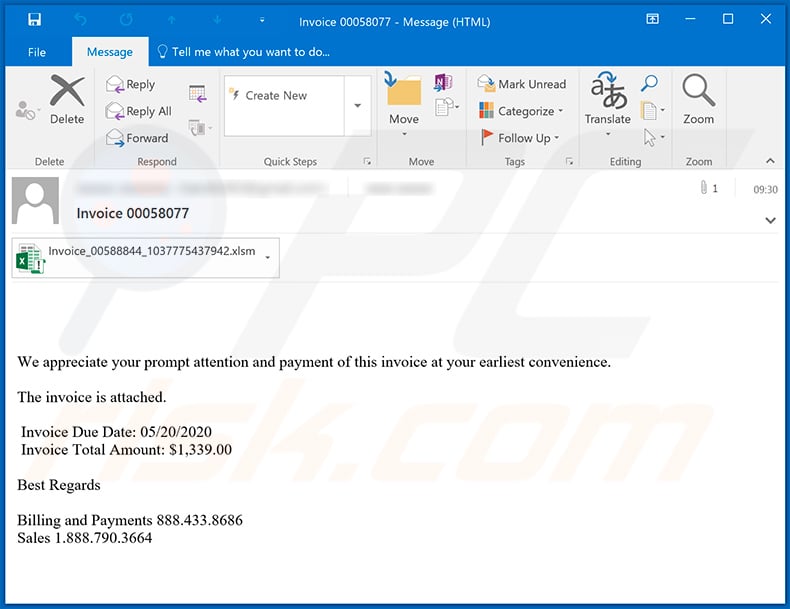
Text presented within:
Subject: Invoice 00058077
We appreciate your prompt attention and payment of this invoice at your earliest convenience.
The invoice is attached.
Invoice Due Date: 05/20/2020
Invoice Total Amount: $1,339.00Best Regards
Billing and Payments 888.433.8686
Sales 1.888.790.3664
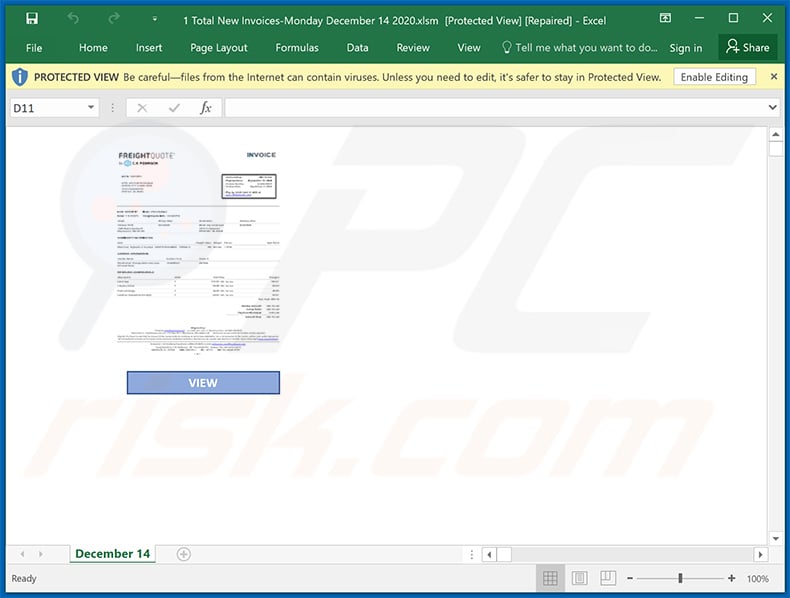
Screenshot of the malicious MS Excel attachment ("Invoice_00588844_1037775437942.xlsm") which injects Dridex into the system:
Example of a DHL-themed spam email used to distribute Dridex malware:
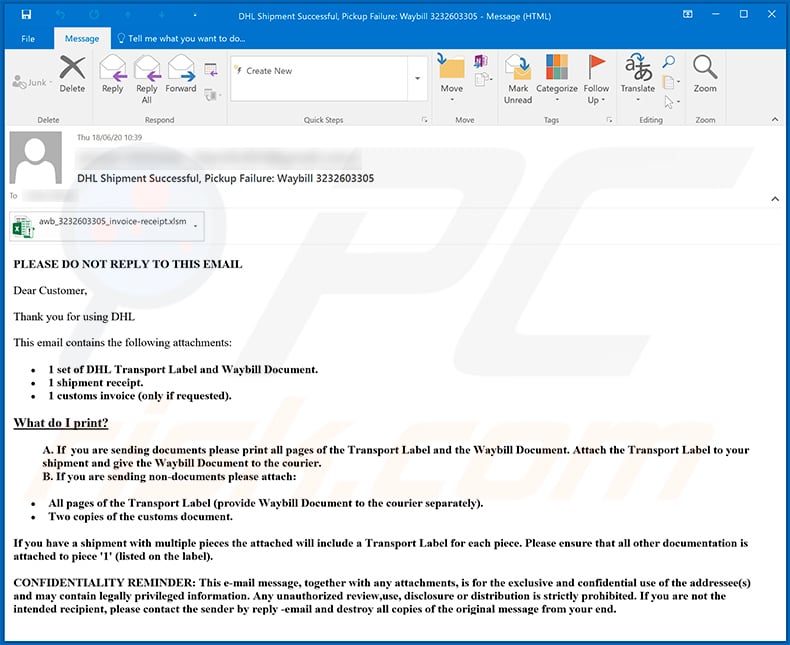
Text presented within:
Subject: DHL Shipment Successful, Pickup Failure: Waybill 3232603305
PLEASE DO NOT REPLY TO THIS EMAILDear Customer,
Thank you for using DHL
This email contains the following attachments:
1 set of DHL Transport Label and Waybill Document.
1 shipment receipt.
1 customs invoice (only if requested).What do I print?
A. If you are sending documents please print all pages of the Transport Label and the Waybill Document. Attach the Transport Label to your shipment and give the Waybill Document to the courier.
B. If you are sending non-documents please attach:All pages of the Transport Label (provide Waybill Document to the courier separately).
Two copies of the customs document.If you have a shipment with multiple pieces the attached will include a Transport Label for each piece. Please ensure that all other documentation is attached to piece '1' (listed on the label).
CONFIDENTIALITY REMINDER: This e-mail message, together with any attachments, is for the exclusive and confidential use of the addressee(s) and may contain legally privileged information. Any unauthorized review,use, disclosure or distribution is strictly prohibited. If you are not the intended recipient, please contact the sender by reply -email and destroy all copies of the original message from your end.
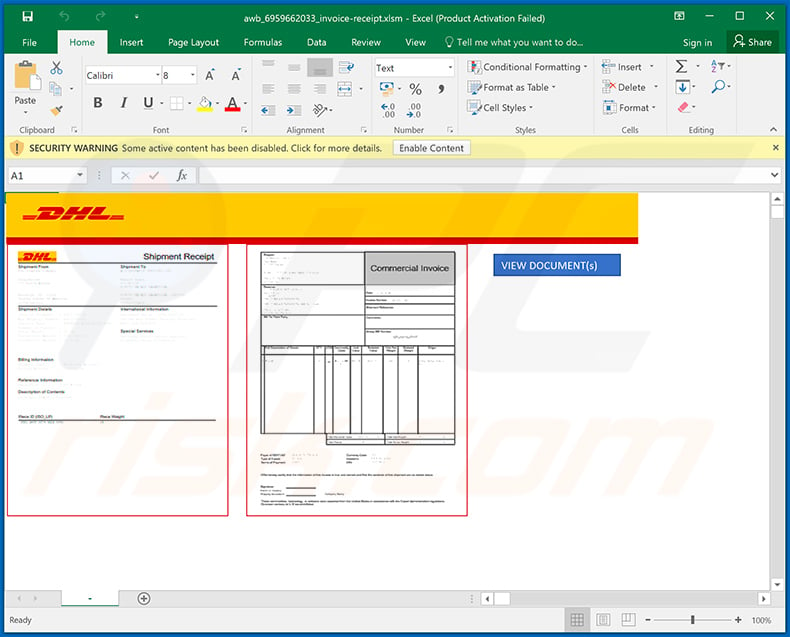
Screenshot of a malicious MS Excel document (which injects Dridex into the system) attached to this email:
Example of yet another spam email used to spread Driex malware via attached MS Excel document:
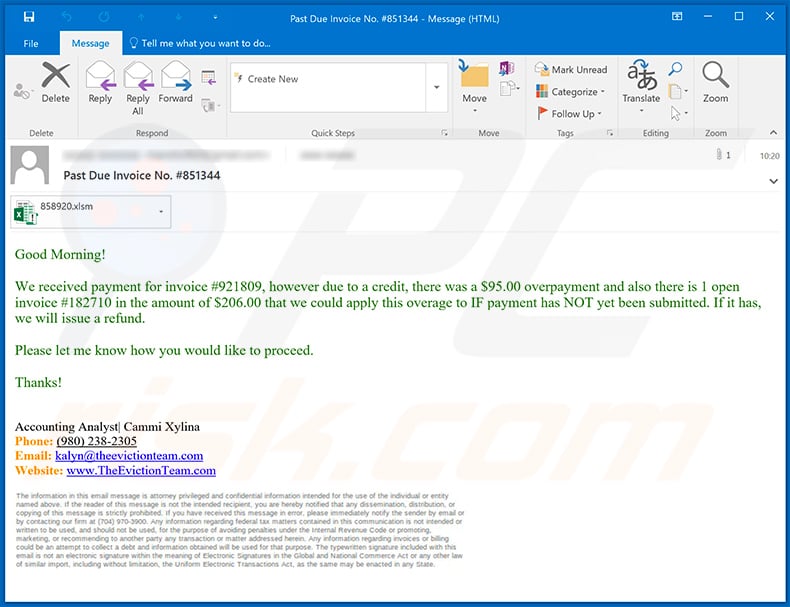
Text presented within:
Subject: Past Due Invoice No. #851344
Good Morning!We received payment for invoice #921809, however due to a credit, there was a $95.00 overpayment and also there is 1 open invoice #182710 in the amount of $206.00 that we could apply this overage to IF payment has NOT yet been submitted. If it has, we will issue a refund.
Please let me know how you would like to proceed.
Thanks!
Accounting Analyst| Cammi Xylina
Phone: (980) 238-2305
Email: kalyn@theevictionteam.com
Website: www.TheEvictionTeam.com
Screenshot of the attached document:
Other malicious MS Word documents used to spread Dridex malware:
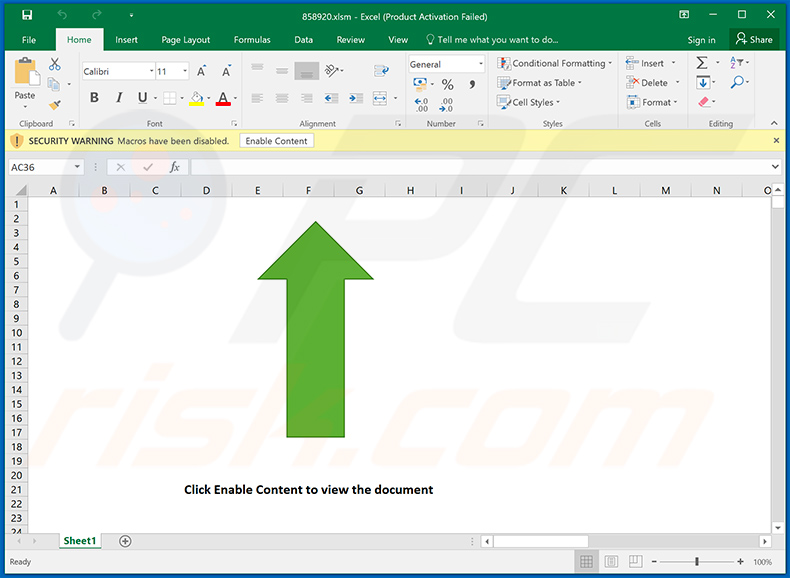
Two additional examples of invoice-themed spam emails that spread Dridex malware via attached malicious MS Excel document (the document is identical in both emails):
Example 1:
Text presented within:
Subject: Invoice 995151
We appreciate your prompt attention and payment of this invoice at your earliest convenience.
The invoice is attached.
Invoice Due Date: 09/23/2020
Invoice Total Amount: $3,778.00Best Regards
Billing and Payments 888.433.9371
Sales 1.888.790.3779
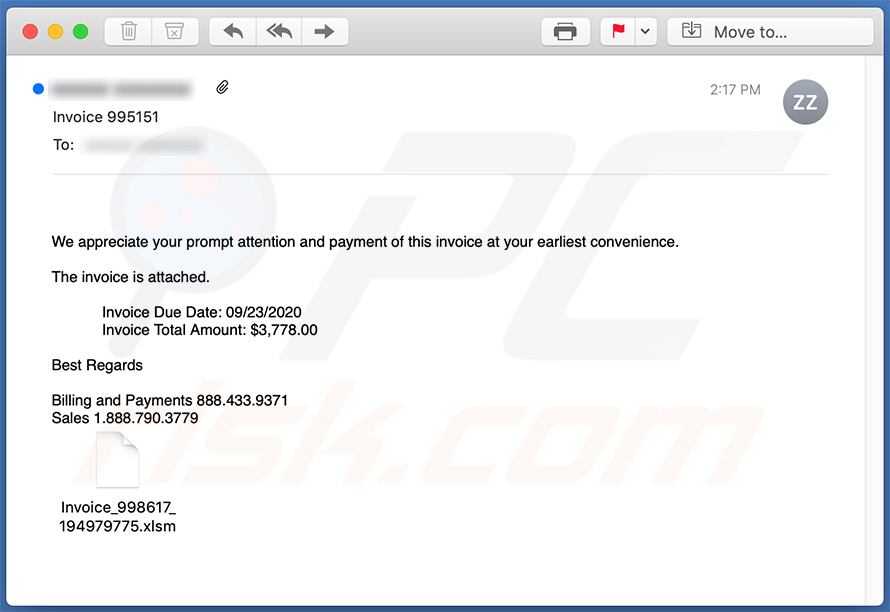
Example 2:
Text presented within:
Subject: Invoice 489368
Thank you very much for your business and continued support.
The invoice is attached.
Invoice Due Date: 09/23/2020
Invoice Total Amount: $3,541.00Best Regards
Billing and Payments 888.433.2671
Sales 1.888.790.4713
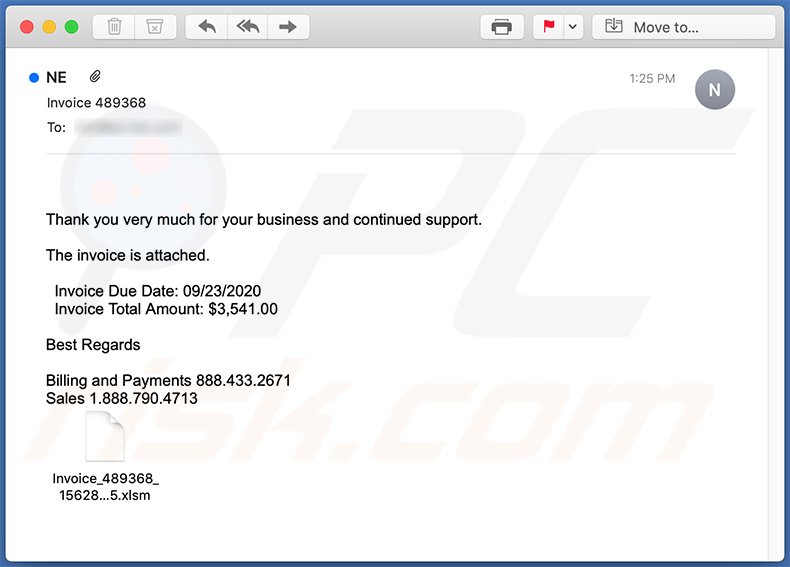
Screenshot of the attached MS Excel document:
Another spam email used to spread Dridex malware:
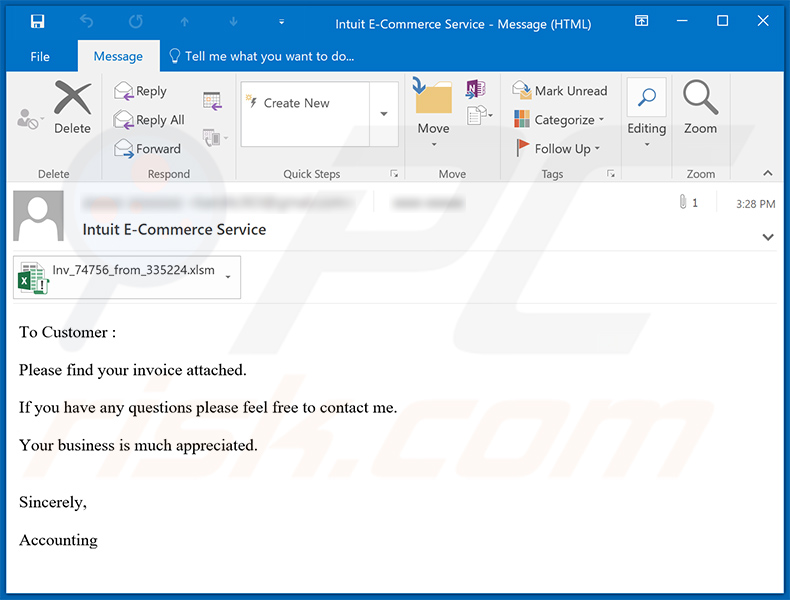
Text presented within:
Subject: Intuit E-Commerce Service
To Customer :
Please find your invoice attached.
If you have any questions please feel free to contact me.
Your business is much appreciated.
Sincerely,Accounting
Another invoice-themed spam email used to spread a malicious MS Word document designed to inject Dridex malware:
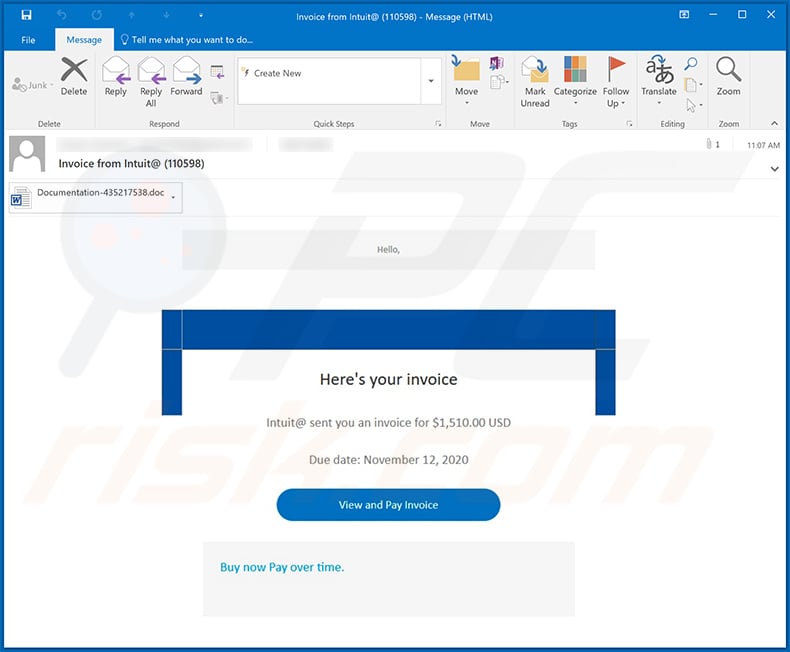
Text presented within:
Subject: Invoice from Intuit@ (110598)
Hello,
Here's your invoice
Intuit@ sent you an invoice for $1,510.00 USD
Due date: November 12, 2020
View and Pay Invoice
Buy now Pay over time.
Screenshot of the attached malicious MS Word document:
Yet another spam email used to spread a malicious MS Excel document which injects Dridex malware into the system:
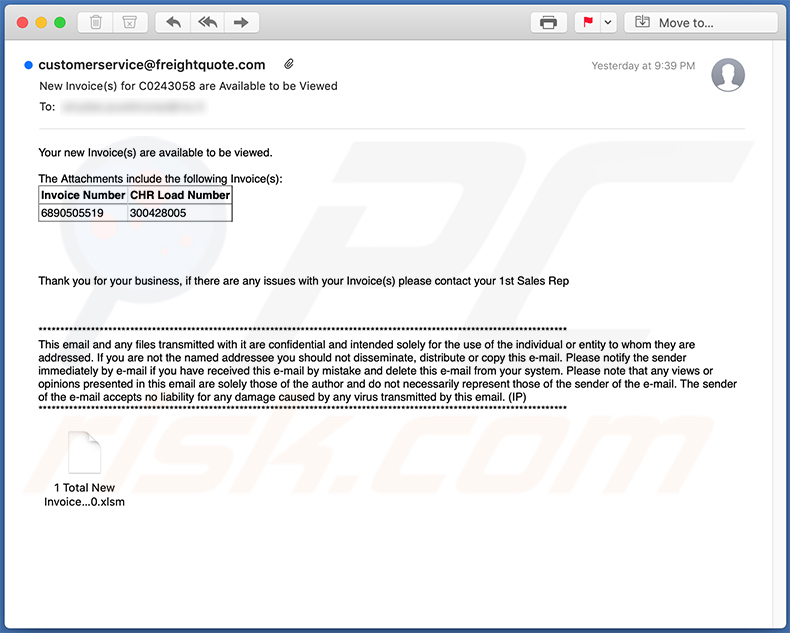
Text presented within:
Subject: New Invoice(s) for C0243058 are Available to be Viewed
Your new Invoice(s) are available to be viewed.
The Attachments include the following Invoice(s):
Invoice Number CHR Load Number
6890505519 300428005Thank you for your business, if there are any issues with your Invoice(s) please contact your 1st Sales Rep
**********************************************************
This email and any files transmitted with it are confidential and intended solely for the use of the individual or entity to whom they are addressed. If you are not the named addressee you should not disseminate, distribute or copy this e-mail. Please notify the sender immediately by e-mail if you have received this e-mail by mistake and delete this e-mail from your system. Please note that any views or opinions presented in this email are solely those of the author and do not necessarily represent those of the sender of the e-mail. The sender of the e-mail accepts no liability for any damage caused by any virus transmitted by this email. (IP)
**********************************************************
Screenshot of the attached MS Excel document:
Update March 16, 2022 - We have discovered that cybercriminals use Dridex as a tool to distribute ransomware. There are cases where Dridex was used to infect computers with a ransomware variant called Entropy. In those cases, Dridex was present in the systems before the ransomware was launched, which ultimately led to data encryption. We also learned that cybercriminals have performed attacks where Dridex injected remote administration tools.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with Dridex malware, should I format my storage device to get rid of it?
This malware can be removed without formatting the storage device. A removal guide for malware is provided above.
What are the biggest issues that malware can cause?
It depends on the type of malware. Typically, it is used to encrypt files, steal sensitive information, hijack online accounts, steal identities, cause additional computer infections, add computers to botnets.
What is the purpose of Dridex malware?
This piece of malware steals login credentials for banking accounts. It achives that by loggin keystrokes (recoreding keys pressed with the keyboard). Additionally, Dridex can execute remote commands or inject code into a specific program and modify its execution/behavior.
How did Dridex malware infiltrate my computer?
It is known that cybercriminals distribute this malware by sending emails containing malicious attachments. Computers get infected after executing a malicious file downloaded from an email. In other cases, malware is distributed using fake software cracking tools or installers for pirated software, untrustworthy sources for downloading files/software, fake updating tools.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner will run a system scan and eliminate malware. It can detect almost all known malware infections. When computers are infected with high-end malware, they must be scanned using a full scan option. High-end malware can hide deep in the system, which means running a quick scan is not enough.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate




































▼ Show Discussion