Babuk Ransomware makes New Year Entrance
The first week of 2021 is almost up and it has already seen its fair share of news. In the InfoSec community, we have already seen the fallout of the SolarWinds hack and credit card details being leaked online for free. 2020’s most prevalent and destructive threat, ransomware, surely would not the new year begin without some development. True to form, a new variant emerged looking to target enterprises so as to demand higher ransoms emerged.
Called Babuk Locker the ransomware can be summarized as learning the lessons from the other human-operated ransomware strains like Conti, Sodinokibi, and Ryuk but with less professionalism and polish. That being said the ransomware strain has already notched up several victims and must still be seen as dangerous. Base on research conducted by Bleeping Computer and security researcher Chuong Dong operations involving the spread of the ransomware began in 2021 and the ransomware operators are demanding anywhere between 60,000 USD and 85,000 USD in Bitcoin to decrypt data. The operators are also using the ransomware in a highly targeted manner typical of modern human-operated ransomware variants. Each executable that has been analyzed by researchers showed that the executable itself was customized for each victim and included a hardcoded extension, ransom note, and a Tor victim URL further customized to the specific victim.
According to Chuong Dong’s analysis, the coding is amateurish; however, the code does boast a sophisticated encryption routine. The routine implemented is its version of SHA256 hashing, ChaCha8 encryption, and Elliptic-curve Diffie–Hellman (ECDH) key generation and exchange algorithm to protect its keys and encrypt files. The routine can spread to network resources, making it capable of targeting larger enterprise networks.
The use of amateur code should not lull defenders of networks into a false sense of security as the encryption routine is incredibly solid with little chance of a decryptor been released soon unless the operators of the ransomware make a significant mistake moving forward. If a victim does not have a sufficient backup policy to defend against ransomware then they may be forced to pay the ransom.
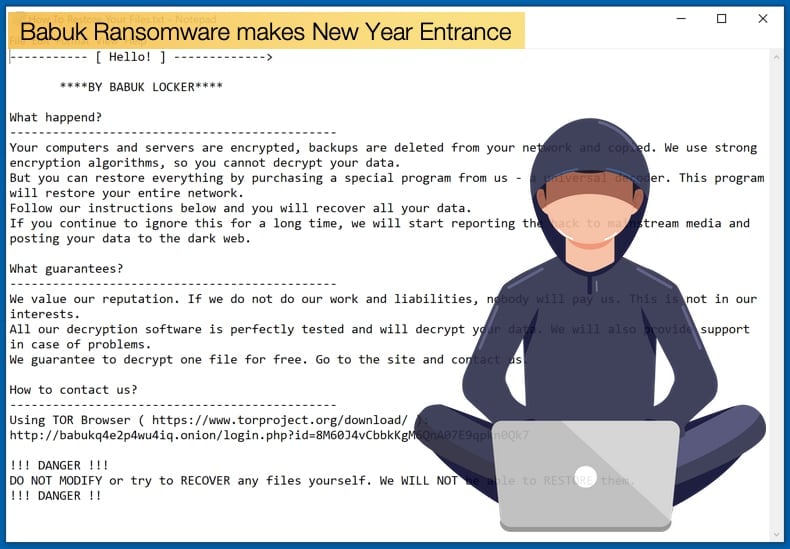
When the ransomware is executed, the operators make use of the command line to give the malware instructions on how to proceed. Once launched, the ransomware will terminate various Windows services and processes known to keep files open and prevent encryption. The terminated programs include database servers, mail servers, backup software, mail clients, and web browsers. The ransomware is also capable of deleting shadow copies potentially making recovery more difficult if the organization’s backup policy only revolves around the creation of shadow copies. During encryption, the ransomware will add a hard-coded extension to the end of encrypted files. So far the extension seen is .__NIST_K571__. Once encryption is complete a ransom note will be dropped into each folder with the file name How To Restore Your Files.txt.
The ransom note will inform the victim that their files have been encrypted and a link to a tor site is provided where the victim can negotiate with the operators as to what to pay to have their files decrypted. Here again, the amateur nature of the attack is on display as the website used by the attackers shows all the communication between themselves and all the victims. Most of the analysis done was achieved because the attackers did not obfuscate the code. This is typical of new ransomware strains and is likely to change in the future given the number of obfuscation tools available to hackers currently.
Unlike many other human-operated ransomware gangs those behind Babuk have decided on another method to leak data stolen before encryption other than a leak site. Perhaps more lo-fi than other gangs with leak sites Babuk uses hacker forums to announce victims and leak data. While more lo-fi the use of these forums has been a staple marketing tactic used by hackers to advertise their skills, malware, or look for affiliates to help spread the malware. It is easy to say this is amateurish when compared to more well-known ransomware gangs. However, if the ransomware works then the extra bells and whistles are academic. Currently, there are five known victims of Babuk with one victim already paying 85,000 USD to decrypt files. Victims include:
- An elevator and escalator company
- An office furniture manufacturer
- A car parts manufacturer
- A medical testing products manufacturer
- An air conditioning and heating company in the USA
Possible Ransomware Trends for 2021
With Babuk making its entrance the problem posed by ransomware has once again been framed. With that in mind, it is wise to look at the possible direction the scourge might take in the year to come. This is most certainly speculation however the researchers’ guesses as to trends are based on real events. The guessing then is less crystal ball worthy but more looking to the past to determine a possible future.
The president of BlackBerry, Tom Eacobacci, wrote his predictions for the year that is now in its infancy. For Tom Eacobacci, there are several easy predictions to make as they still currently form the modus operandi of ransomware operators. The first being that ransomware associated with advanced persistent threat (APT) groups, typically nation-state groups, will continue to come from Russia, China, Iran, and North Korea. In the case of North Korea, we have already seen active attempts to spread the VHD ransomware strain which has been attributed to the Lazarus group who has a history of conducting both financially motivated cybercrime and cyber espionage. Ransomware will continue to be the go-to malware strain, a trend that dominated 2020 and shows no sign of slowing in 2021.
While ransomware will dominate the malware seen in 2021, Eobacci believes that governments across the world will be taken a harder stance towards the crime and pursue perpetrators more doggedly. Further, the change in administration in the US, while not as smooth as people would like, will bring a change in policy that will have an impact globally. Eobacci noted,
“There are also signs that the institutional response to ransomware is going to change, at least in the USA, with the installation of a new President in January. The incoming Biden administration has already signaled that it will take a stance that is more hands-on than the last, and has sought to clarify whether cities should pay ransomware demands….Specifically, it appears that ransomware operators will be pursued more doggedly than they have been to date. Jaimie Collier, cyber threat intelligence consultant, told SecurityWeek recently the United States government declared that ransom payment would be contrary to national security interests. “The Australian Signals Directorate,” he added, “has also stated publicly that they will be proactive in going after financial/ healthcare criminals. It’s going to be interesting to see how other governments react, and see if other intelligence agencies start to go after financial criminals more than they have in the past.”
Another trend likely to continue is the rising cost of ransomware, this trend has been driven by the increasing sophistication of the malware, adoption of better extortion tactics, and the ability to successfully target high profile victims in the form of Fortune 500 companies. In 2019 ransomware damages surpassed 10 Billion USD, in 2020 this is estimated to rise to 20 billion USD once the analysis is complete. To protect yourself and your business from ransomware Eobacci advises the following,
“As many sources are reporting, 2020 is likely to have seen the most cyberattacks of any year on record, and by a fair margin. This is largely because so many people started working from home this year, and the advent of this shift was so sudden that companies were left desperately searching for ways to mitigate attacks in the COVID-19 era. Ransomware was no exception to this shift, and in fact ransomware operators might just turn out to be one of the only beneficiaries of 2020. With more money and support than ever, ransomware developers are entering a golden age, just at a time when the rest of us are suffering the economic consequences of the pandemic and the lockdowns. Given that, it’s not hard to predict what is going to happen – unless we all get a lot smarter, and quick, the ransomware pandemic is going to get worse as we move into 2021.”
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion