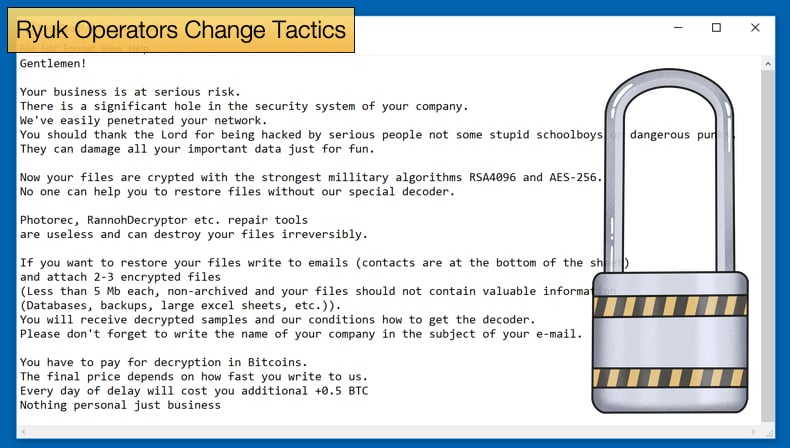
Ryuk Operators Change Tactics
In a recent report published by Advanced Intel, a threat intelligence firm, those behind recent Ryuk attacks have changed tactics. The change in tactics is used to gain initial access to targeted networks and according to Advanced Intel’s researchers, the new tactic involves exploiting hosts with public Internet-facing RDP (remote desktop protocol) connections. Using targeted phishing emails to deliver malware continues to be the favored initial attack vector, but researchers noted that the start of 2021 saw an increase in instances where operators looked to compromise RDP connections to gain initial access.
To be granted access to Internet-facing RDP connections threat actors will use brute-force attacks, using a weak password and username combinations or credentials that have been leaked. Once initial access is granted to a network, threat actors will begin the reconnaissance stage of the operation. Researchers have noticed distinct phases once this step of the operation is begun. The first stage is defined by the attackers looking for valuable resources on the now compromised network.
Researchers noted,
“Once a foothold has been established Ryuk operators will attempt to enumerate domain trusts such as local domains, network shares, users, and Active Directory Organization Units. During this stage, the actors attempt to gather information about the organization to determine what resources within the infected domain are of value to perpetrating the rest of the attack. Bloodhound and AdFind have become popular tools used by actors trying to enumerate active directory information within an infected domain.”
The second stage involves the attackers discovering information pertaining to the victim’s revenue so that a ransom can be set that the attackers feel the victim is more likely to pay. Elaborating further, researchers noted,
“Advintel has observed actors conducting OSINT research related to the compromised host domain to identify the infected victim company and evaluate their revenue. Ransomware operators use the total annual revenue of the victim’s company to assess what the ransom amount will be. Specifically, actors have been observed searching across services such as ZoomInfo to retrieve information about the victim company such as technologies used, recent mergers and acquisitions, corporate hierarchies, personnel, and various other elements of data related to the company that may be of value to their operations.”
New tactics not only include how to gain initial access to the target network is gained but also how security solutions are bypassed. Ryuk operators use several tried and tested tools to bypass both anti-virus packages and endpoint monitoring tools.
This stage is done after reconnaissance is completed and when the attacker has a better picture of the security solutions they have to contend with. Researchers noted that often such information, namely what software is used to protect the enterprise, amongst hacking networks so that if the network in question has been compromised in the past, the attacker will have a better picture of what they are up against.
Further, the attacker will hunt for the specific network administrator that has the credentials to endpoint monitoring and response solutions. The attacker will then use the popular KeePass tool to harvest those credentials, helping bypass the security solution. Another tactic employed by the attacker is to bypass PowerShell execution restrictions by deploying a portable Notepad++ version to run PowerShell scripts on the host system.
Host Privilege Execution
In order to increase system permissions so that the encryption malware can be run, Advanced Intel noticed that attackers were making use of two previously known vulnerabilities. It is important to note that both vulnerabilities do have patches available. The flaws exploited are:
- CVE-2018-8453: The vulnerability is an elevation of privilege vulnerability in Windows when the win23k.sys component fails to properly handle objects in memory. The exploitation of this vulnerability allows an attacker to run an arbitrary kernel with read/write privileges.
- CVE-2019-1069: Researchers pointed out that the flaw is a privilege escalation vulnerability that leverages the way Windows Task Scheduler handles saved tasks. Task Scheduler stores tasks as files in two locations, C:\Windows\Tasks, and C:\Windows\System32\Tasks. If an RPC client modifies a task using the service in the C:\Windows\Tasks location when modifications are saved the task will be migrated to C:\Windows\System32\Tasks. When saving a task file, the Task Scheduler service will set ownership and full control of the file to the owner of the task. This process allows an attacker to perpetrate a hard link attack. Therefore, if an attacker manually places a file within C:\Windows\Tasks the attacker will be able to run this file with the highest level of privilege since the Task Scheduler service runs at the maximum level of privilege defined by the local machine.
With the following new tactics been discovered, Advanced Intel researchers have provided the following mitigation strategies:
- Detections for use of Mimikatz and PsExec execution within the network.
- Detections and alerts for the presence of AdFind, Bloodhound, and LaZagne within the network.
- Ensure all operating systems and software are up to date with the latest updates and security patches.
- Implement multi-factor authentication for RDP access.
- Implement network segmentation and controls to scrutinize SMB and NTLM traffic within the network.
- Routinely review account permissions to prevent privilege creep and maintain the principle of least privilege.
- Routinely review Group Policy Objects and logon scripts.
- Update systems to prevent exploitation of CVE-2018-8453 and CVE-2019-1069.
Not Just RDP Abuse and Phishing Emails
Given that Ryuk has been such a persistent player on the ransomware scene and a dangerous one at that, Ryuk operators have been known to adopt new tactics regularly. What is written above is only a few of the tactics adopted. This year has already seen several. One such that deserves special mention is the use of BazarCall as an infection vector. This infection vector is typically seen in the use of call centers to distribute malicious Office documents. This is also not the first time call centers have been leveraged to help complete ransomware operators’ objectives. In the past, call centers have been used to place increased pressure on victims to pay the ransom after encryption has occurred.
Returning to BazarCall, at the start of the year security researchers were seeing malware being distributed, then being used to drop other malware strains like TrickBot and Ryuk. The BazarCall campaign got its name as it was initially seen distributing BazarLoader to act as the malware that initially compromises a victims machine by creating a backdoor which can then be used to drop other malware strains. Those behind the campaign then began to use other pieces of malware to compromise machines but researchers still identify the campaign as BazarCall.
Rather than the initial infection vector being a malicious email bundled with malware, victims will be instructed to call a call center to cancel a subscription before they are automatically charged. These call centers would then direct users to a specially crafted website to download a "cancellation form" that installs the BazarCall malware. The campaign does begin with an email that targets corporate users and states the recipient's free trial is about to run out. However, these emails do not provide any details regarding the alleged subscription, just an instruction to call the number provided.
Once the call is made, the victim is given a customer ID and directed to a website when they are instructed, they can cancel the subscription. The website instructs the victim to enter their unique ID and then they must download the malicious cancellation form. If the form is downloaded and macros enabled the BazarCall malware will be installed on the victim’s machine. Once a backdoor is created on the machine threat actors can drop ransomware like Ryuk onto the machine.
It is believed that Ryuk operators employ the BazarCall operators in a distribution-as-a-service scheme. Central to falling victim to the BazarCall operator's plan is to enable macros, to this extent users are advised to think twice about enabling macros on Office documents even if they trust the source of the document. In some instances, researchers noted that during calls to the malicious call center, victims were instructed to turn off anti-virus applications, this is done to help prevent detection and remediation of malware.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion