No More Ransom Releases Free Lorenz Decryptor
The good work done by No More Ransom may be difficult to quantify but it is safe to say that their work releasing free decryptors to be used by victims of ransomware has possibly saved millions of dollars’ worth in damages and ransom payments funding criminal activity.
Now with the help of security firm Tesorion a decryptor for the Lorenz has been released to the public for free.
No More Ransom is a partnership between public, private, and law enforcement agencies, of which this publication is a partner to help educate the public and assist victims.
In providing free decryptors it is hoped that not only victims can recover important data that has been encrypted but also to disrupt ransomware operations as the decryptors allow victims to decrypt files without paying the ransom demanded. Lorenz is now the 120th decryptor released to the public since the project started in 2016.
It is important to note that the Lorenz decryptor works differently from other decryptors released in the past. In general, decryptors will include a decryption key, the same type of key the ransomware operator will provide. In theory, the decryption key allows for the victim to decrypt all encrypted data.
Speaking to Bleeping Computer, Tesorion researcher Gijs Rijnders that their decryptor can only decrypt certain file structures. The program is capable of decrypting Office documents, PDF files, some image types, and movie files.
Files that are regarded as uncommon file structures may not be decrypted by the program. This should not detract too much from the good the program can do as by covering common file structures victims will still be able to get away with not paying the ransom.
Not only has Tesorion developed a free decryptor, but they have also released information on how the ransomware runs its encryption routine. Rijnders explains that a bug in how they implement their encryption can cause data to become lost, which would prevent a file from being decrypted even if a ransom was paid.
It is not uncommon for ransomware strains to have bugs that prevent proper decryption of files and should serve as another reminder that paying the ransom is no guarantee the victim will regain access to their data. Rijnders further stated that,
“The result of this bug is that for every file which’s size is a multiple of 48 bytes, the last 48 bytes are lost. Even if you managed to obtain a decryptor from the malware authors, these bytes cannot be recovered,”
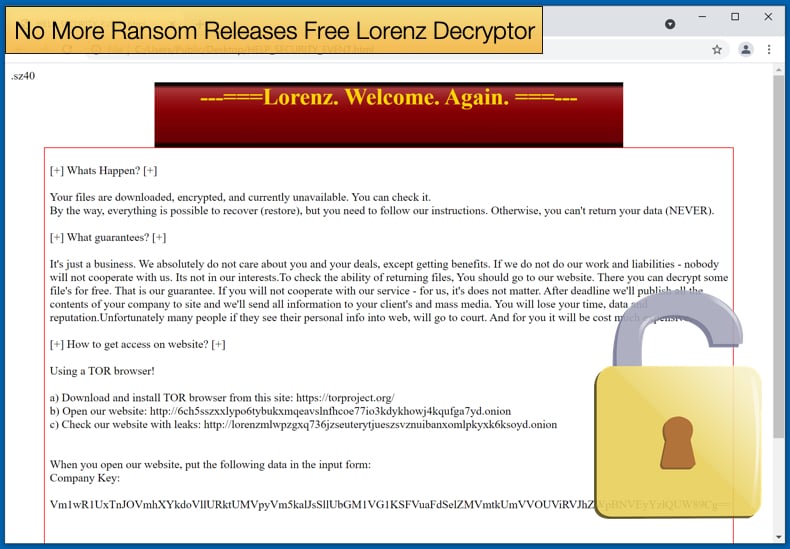
Lorenz Ransomware
Security experts have noticed that the ransomware’s activity has decreased over the last month or so when compared to other variants. While activity has dropped off it does not necessarily mean that the ransomware poses no threat. A quick review of the ransomware’s history illustrates this.
Discovered in April 2021, the ransomware appears to be related to two other ransomware strains ThunderCrypt and sz40. It is unclear if the source code for the two other variants was bought by Lorenz’s developers or it is developed by the same group.
Lorenz is considered a human-operated ransomware variant. This means that much of the ransomware’s operations are conducted by a human attacker, rather than relying on automating the malware.
This is done for several reasons including being able to compromise a victims’ network by moving laterally across it while avoiding being detected by security measures. Further, the ransomware’s encryption routine can be enabled when it would cause the most damage to the victim, placing more pressure on the victim to pay.
Lorenz has also adopted the double extortion technique popularized by the now-defunct ransomware Maze that involves data been stolen before data encryption. The data is then used to try and better leverage a ransom payment by threatening to release the data to the public if the ransom is not paid by a specific time.
Like other ransomware gangs, those behind Lorenz had a leak website to announce hacks and leaks, often referred to as a leak site. However, Lorenz had their own way to do it, rather than releasing the data if payment was not made, data would be released immediately if they had a buyer.
If the ransom was not paid the threat actors would release password-protected RAR archive files containing the data. Once the threat actors are convinced, they would receive no payment and the password for the RAR files would be released.
The ransom demand is typically anything between 500,000 and 700,000 USD to be paid in Bitcoin. Earlier versions of the ransomware included million-dollar ransom demands, but it is unclear if those were affiliated with the same operation. Bleeping Computer further noted that,
“Unlike other enterprise-targeting ransomware, the Lorenz sample we looked at did not kill processes or shut down Windows services before encrypting…Each folder on the computer will be a ransom note named HELP_SECURITY_EVENT.html that contains information about what happened to a victim's files. It will also include a link to the Lorenz data leak site and a link to a unique Tor payment site where the victim can see their ransom demand.”
Perhaps Lorenz’s most famous victim is Canada Post with the organization stating,
“After a detailed forensic investigation, there is no evidence that any financial information was breached. In all, the impacted shipping manifests for the 44 commercial customers contained information relating to just over 950 thousand receiving customers. After a thorough review of the shipping manifest files, we’ve determined the following:
The information is from July 2016 to March 2019
The vast majority (97%) contained the name and address of the receiving customer
The remainder (3%) contained an email address and/or phone number"
It was further discovered that the Lorenz leak site was advertising 35.3 GB of data allegedly stolen during the attack. Hopefully now with a decryptor being made available to the public, headlines featuring Lorenz will not include any victims.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion