Emotet Now Seen Dropping Cobalt Strike
In November 2021 this publication covered the return of Emotet after law enforcement agencies around the globe worked to cease the malware’s operations by seizing critical infrastructure. Since the return of the botnet, it has been incredibly active being distributed in several campaigns. Now researchers have seen the Botnet dropping the infamous penetration testing tool Cobalt Strike in an attempt to fast forward ransomware attacks.
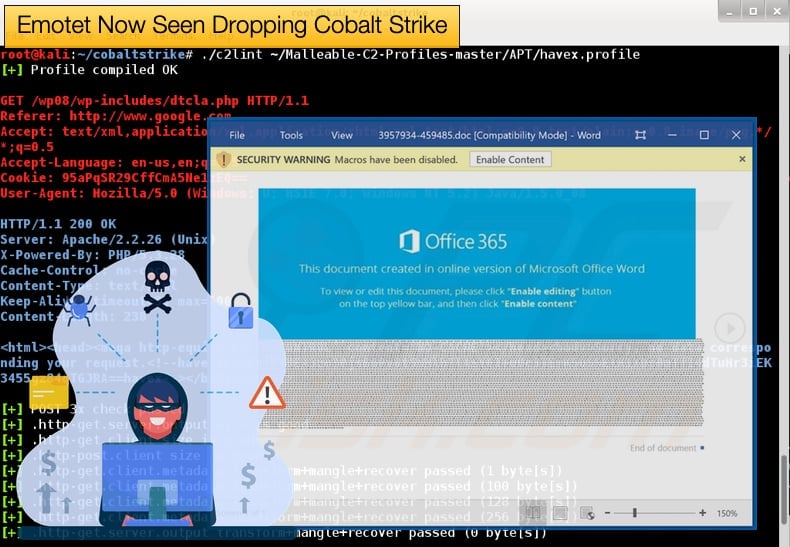
Historically, Emotet has been spread via malicious Word and Excel documents. The documents abuse the macro’s functionality in these applications to then download and install the malware if the recipient agrees to enable macros.
Emotet can then steal email credentials and access to the victim’s email account to then send more emails carrying the malicious documents, potentially allowing the malware to spread to yet another device. This functionality has firmly placed Emotet within the botnet that malware family.
It is not just the seizing of email accounts and distributing the malware to other devices that earned Emotet its feared reputation. The botnet has partnered with other threat actors including TrickBot and QakBot, also tracked as QBot. Emotet will install these trojans once it has compromised the system. In the past, this has been followed by ransomware infections.
It is interesting to note that TrockBot and QakBot would install Cobalt Strike to facilitate ransomware infections by ransomware gangs they had partnered with. Emotet’s latest evolution seems to bypass this step allowing a fast track to ransomware infections if necessary.
Returning briefly to Cobalt Strike, the simplified operation of the penetration testing tool involves the application, more commonly used as malware by threat actors, to drop “beacons”.
These are used to perform remote network surveillance on compromised machines and can also be used to execute certain commands. Threat actors can then use the “beacons” on compromised machines to facilitate ransomware attacks.
The discovery of Emotet now being able to directly drop Cobalt Strike, rather than relying on a partnered threat actor, was made by specialist Emotet research group Cryptolaemus (https://twitter.com/Cryptolaemus1) who stated on Twitter,
“WARNING We have confirmed that #Emotet is dropping CS [Cobalt Strike] Beacons on E5 Bots and we have observed the following as of 10:00EST/15:00UTC. The following beacon was dropped: Note the traffic to lartmana[.]com. This is an active CS Teams Server. 1/x”
Cofense then later confirmed this to be true and issued a flash alert to security partners including Bleeping Computer who then in an article reproduced some of the security alert’s content. The alert states,
“Today, some infected computers received a command to install Cobalt Strike, a popular post-exploitation tool…Emotet itself gathers a limited amount of information about an infected machine, but Cobalt Strike can be used to evaluate a broader network or domain, potentially looking for suitable victims for further infection such as ransomware…While the Cobalt Strike sample was running, it attempted to contact the domain lartmana[.]com. Shortly afterward, Emotet uninstalled the Cobalt Strike executable.”
Emotet’s Fast-Tracked Rise
The speed at which Emotet has returned from the grave has come as a shock. Shortly after Emotet’s return was made public it was also seen being distributed in active campaigns. At the time when Emotet resurfaced subsequent spam emails campaigns to spread the malware were seen. These used several lures to help trick recipients to enable macros and download the malware.
Lures used included reply-chains related to a "missing wallet," a CyberMonday sale, canceled meetings, political donation drives, and the termination of dental insurance. Attachments to the spam emails would contain malicious office documents be they Word or Excel documents.
Some attachments even included a .zip file that would contain the malicious office document. The .zip file would be password protected with the recipient providing the password in the email. It is assumed this is done to further add a veneer of legitimacy to the sam email.
Also at the time, security researchers for AdvIntel suggested an interesting theory as to the main driver behind Emotet’s return. In an article published by Bleeping Computer, it was suggested that the threat actors behind the Conti ransomware convinced Emotet’s developer to restart operations. Up until this point, there had been a steady decline in decentralized ransomware operations successfully infecting victims.
This was due in part to initial access brokers, a role that Emotet thrived in, no longer offering services. For Emotet, this was down to infrastructure being seized by law enforcement. This, in turn, led to less competition in the ransomware market with only ransomware gangs more associated with organized crime seeing a spike in infections.
Emotet’s forced end of operations must have hurt Conti, as ransomware operators no longer could rely on being able to access networks via TrickBot (which would drop Cobalt Strike Beacons to help facilitate later ransomware infections), for example, as TrickBot would not be dropped by Emotet.
This denied ransomware operators easy access to already compromised networks. Given that researchers are now seeing Emotet at least attempting to drop Cobalt Strike beacons this theory is given more credence as now Conti can be dropped onto an Emotet compromised machine without the use of a primary payload such as TrickBot being dropped first. Such an arrangement certainly would primarily benefit Conti.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion