Microsoft finally Block Macros but Hackers Find New Attack Vectors
A favored attack vector exploited by hackers has long been Microsoft Office’s Macros functionality. Microsoft initially introduced macros to help users automate procedures making use of Excel or Word a much more convenient prospect, but that convenience came with price hackers were far too keen to claim.
How macros worked was to allow customized scripts to run in the background. This meant that a hacker could run malicious scripts to fetch malware if macros were enabled on the victim’s machine.
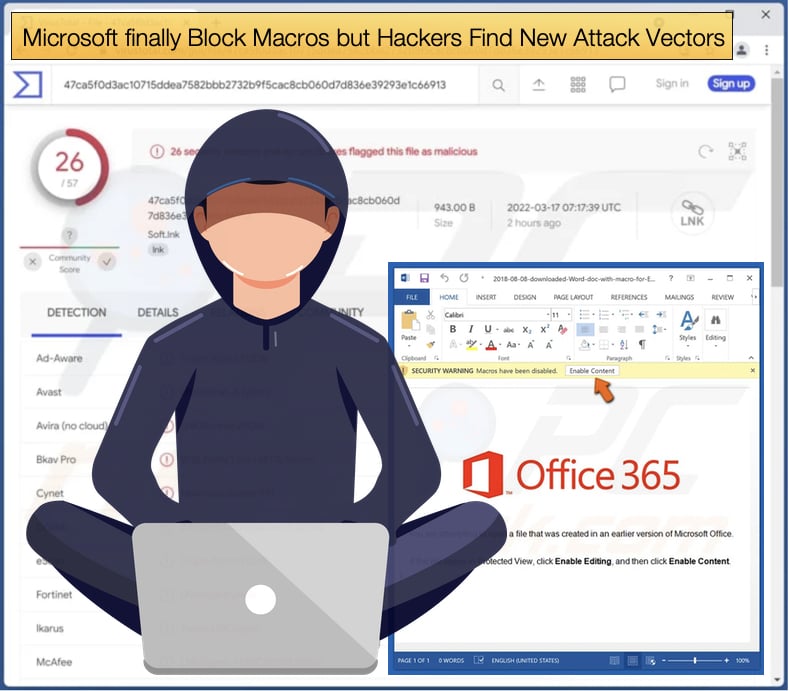
Hackers would apply all sorts of social engineering tactics to get victims to enable macros to run malicious scripts. This attack vector has been exploited by numerous malware families, several prominent families include Emotet, TrickBot, Qakbot, and Dridex.
Microsoft announced in February 2022 that it would be blocking macros by default and this would come into effect in April 2022. MIcrosoft further noted that,
“We will continue to adjust our user experience for macros, as we’ve done here, to make it more difficult to trick users into running malicious code via social engineering while maintaining a path for legitimate macros to be enabled where appropriate via Trusted Publishers and/or Trusted Locations,”
Microsoft missed its deadline of April to impose these changes but the changes did come into effect on July 21, 2022.
The changes were implemented earlier but due to significant negative user feedback, the blocking of macros was rolled back and only came into effect towards the end of July 2022.
Despite the to and fro between blocked and not blocked, hackers began moving away from exploiting macros as soon as Microsoft made its initial announcement.
Once the announcement was made security researchers began seeing a drop in macros exploitation and hackers experimenting with other attack vectors.
The Move Away From Macros
In a report published by Proofpoint, malicious campaigns were logged from October 2021 to June 2022 and it was revealed that there was 66% decrease over the period in macros being used as an attack vector.
At the same time, the use of container files such as ISOs, ZIPs, and RARs has grown steadily, rising by almost 175%.
Interestingly enough, the use of malicious LNK files exploded in February when Microsoft made its announcement to block macros. LNK file exploitation increased by a whopping 1,675% compared to October 2021.
It was determined that this soon became the weapon of choice of ten individual threat groups tracked by Proofpoint. It was not only Proofpoint that noticed a trend developing but McAfee also published a blog article detailing the increase in abuse of LNK files.
An LNK file is s a Windows Shortcut that serves as a pointer to open a file, folder, or application. McAfee researchers provided a more detailed definition stating,
“LNK files are based on the Shell Link binary file format, which holds information used to access another data object. These files can be created manually using the standard right-click create shortcut option or sometimes they are created automatically while running an application. There are many tools also available to build LNK files, also many people have built “lnkbombs” tools specifically for malicious purposes.”
It was also noted that hackers distributing Emotet, QakBot, and BazarLoader were seen using LNK files to distribute their malware payloads. Hackers were seen using email spam and malicious URLs to deliver LNK files to victims.
These files instruct legitimate applications like PowerShell, CMD, and MSHTA to download malicious files.
Emotet, for example, used an LNK file to execute a VBS script via the Windows Command Processor, this would then be used to fetch the main Emotet payload.
McAffee broke down the attack chains for two more families, with bot being similar in execution to Emotet. McAfee researchers concluded,
“As we saw in the above three threat campaigns, it is understood that attackers abuse the windows shortcut LNK files and made them to be extremely dangerous to the common users. LNK combined with PowerShell, CMD, MSHTA, etc., can do severe damage to the victim’s machine. Malicious LNKs are generally seen to be using PowerShell and CMD by which they can connect to malicious URLs to download malicious payloads…These types of attacks are still evolving, so every user must give a thorough check while using LNK shortcut files. Consumers must keep their Operating system and Anti-Virus up to date. They should beware of phishing mail and clicking on malicious links and attachments.”
While the use of LNK files and other file types like ISO, ZIP, and RAR do pose a significant risk to users there is a silver lining to these methods being adopted.
Convincing a recipient of a spam email to open an LNK file is a much more difficult prospect than with Word and Excel files, as the LNK file needs to be unpacked from an archive and then opened.
This extra step is likely to raise suspicion and it is easier for companies to instruct employees to not open these files when compared to file types used daily like Microsoft Office files.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion