Sliver and Brute Ratel Replace Cobalt Strike
For some time now the penetration testing tool Cobalt Strike has long had its somewhat legitimate functions abused by hackers to compromise targeted machines. The creation of Cobalt Strike beacons was also a favored malware and ransomware delivery method for several threat actors, generally following an infection from TrickBot amongst others to signal a machine is compromised.
Then a malware payload can be dropped through the backdoor while hoping nobody notices.
Due to the penetration tool's popularity, those tasked with defending IT infrastructure became well-versed at detecting and mitigating threats reliant on Cobalt Strike. This has led some threat actors to look for other alternatives.
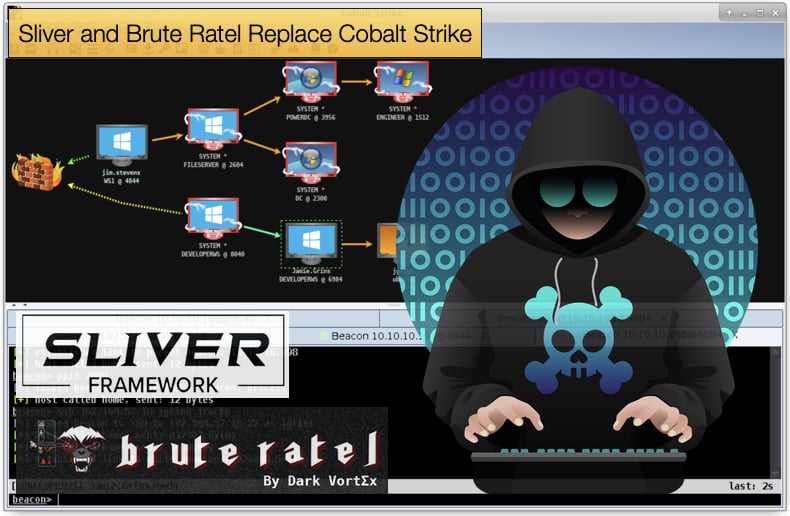
Recently, Microsoft researchers have discovered some threat actors are using another framework called Sliver.
In a blog article published by the Redmond tech giant, summarised the command-and-control framework’s main functions as supporting various network protocols such as DNS, HTTP/TLS, MTLS, and TCP.
Further, the framework can accept implant or operator connections and host files to impersonate a benign web server. Lastly, Sliver can deliver payloads and execute arbitrary code.
For a more detailed analysis and indicators of compromise, it is advised that the blog published be your first port of call. As for why such a framework is important to threat actors, Microsoft researchers noted,
“Threat actors use C2 frameworks to manage their access to compromised hosts and networks during an intrusion. A C2 framework usually includes a server that accepts connections from implants on a compromised system, and a client application that allows the C2 operators to interact with the implants and launch malicious commands…Many threat actors integrate public, open-source C2 framework options into their arsenal because these have a low barrier to entry and offer several advantages for attackers like low cost, ease of modification, and difficult attribution. As previously mentioned, Sliver is one such open-source framework. Although Sliver is somewhat new, the TTPs it implements are common across many frameworks.”
Currently, active use of Sliver has been detected by not only Microsoft but the UK’s Government Communications Headquarters (GCHQ).
In an advisory published by the latter, it was noted that Russian state-sponsored groups including APT29, also known as Cozy Bear, The Dukes, and Grizzly Steppe, are using Sliver to maintain persistence on targeted machines and networks. It was stated,
“The use of the Sliver framework was likely an attempt to ensure access to a number of the existing WellMess and WellMail victims was maintained following the exposure of those capabilities. As observed with the SolarWinds incidents, SVR [GCHQ’s catogorization of Russian state-sponsored threat actors] operators often used separate command and control infrastructure for each victim of Sliver. SVR actors have used methods other than malware to maintain persistence on high value targets, including the use of stolen credentials.”
Brute Ratel
In July of this year, researchers discovered another group of threat actors moving away from Cobalt Strike and the use of beacons for another tool.
This time researchers saw Brute Ratel being used to evade detection by endpoint detection and response (EDR) and antivirus solutions. Palo Alto’s Unit 42 describes Brute Ratel as,
“...the newest red-teaming and adversarial attack simulation tool to hit the market. While this capability has managed to stay out of the spotlight and remains less commonly known than its Cobalt Strike brethren, it is no less sophisticated. Instead, this tool is uniquely dangerous in that it was specifically designed to avoid detection by endpoint detection and response (EDR) and antivirus (AV) capabilities. Its effectiveness at doing so can clearly be witnessed by the aforementioned lack of detection across vendors on VirusTotal.”
Again, researchers detected APT29, making use of the newer less well-known tool kit. Researchers stated that the unique sample was packaged in a manner consistent with known APT29 techniques and recent campaigns involving the state-sponsored group.
Typically, these campaigns leverage well-known cloud storage and online collaboration applications. Specifically, this sample was packaged as a self-contained ISO.
The file contained a Windows shortcut (LNK) file, a malicious payload DLL, and a legitimate copy of Microsoft OneDrive Updater.
However, while packaging techniques alone are not enough to definitively attribute this sample to APT29, these techniques demonstrate that users of the tool are now applying nation-state tradecraft to deploy Brute Ratel.
Brute Ratel has also been maliciously abused by ransomware gangs, according to Bleeping Computer and AdvIntel.
Both noted how it is believed that ex-Conti ransomware gang members are forking out 2,500 USD for a Brute Ratel license to further attack campaigns. They are able to get their hands on licenses by setting up fake US companies.
For those tasked with defending networks, rules for detecting Sliver and Brute Ratel need to be made and implemented. This is no small task but are needed to prevent state-sponsored groups and ransomware operators from gaining unrestricted access to IT infrastructure.
Share:

Karolis Liucveikis
Experienced software engineer, passionate about behavioral analysis of malicious apps
Author and general operator of PCrisk's News and Removal Guides section. Co-researcher working alongside Tomas to discover the latest threats and global trends in the cyber security world. Karolis has experience of over 8 years working in this branch. He attended Kaunas University of Technology and graduated with a degree in Software Development in 2017. Extremely passionate about technical aspects and behavior of various malicious applications.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion