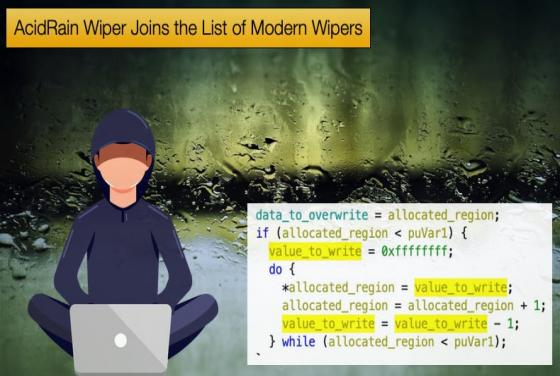

AcidRain Wiper Joins the List of Modern Wipers
This publication has covered how malicious malware called wipers have seen an uptick in use following the start of the Ukrainian war. Several new wipers have been discovered since the outbreak of war. Following these discoveries, the FBI warned that satellite communication infrastructure was coming