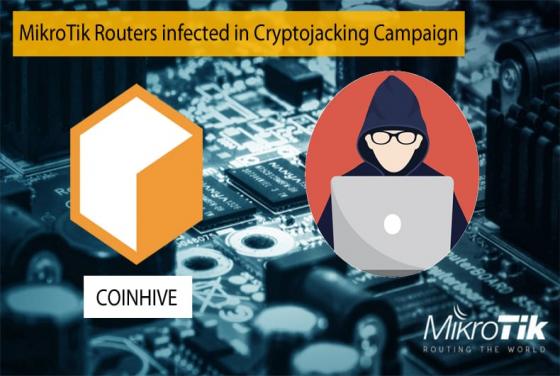

MikroTik Routers infected in Cryptojacking Campaign
Currently been exploited in mainly Brazil is a massive cryptojacking campaign infecting MikroTik routers. Central to the campaign is the hacker’s use of the now infamous Coinhive in-browser cryptocurrency miner. Cryptojacking is the unauthorized use of someone else’s computer to mine cryptocurrency.