How to eliminate the FormBook malware from the operating system
TrojanAlso Known As: FormBook malware
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is FormBook?
FormBook is a virus designed to steal personal data from victims' computers. Research shows that this malware is distributed using spam emails that contain malicious attachments. In addition, developers provide this virus as a 'service' - any aspiring cyber criminal can pay a subscription and gain access to the FormBook tool.
The list of victims is large, however, most FormBook infections have been detected in USA and South Korea.
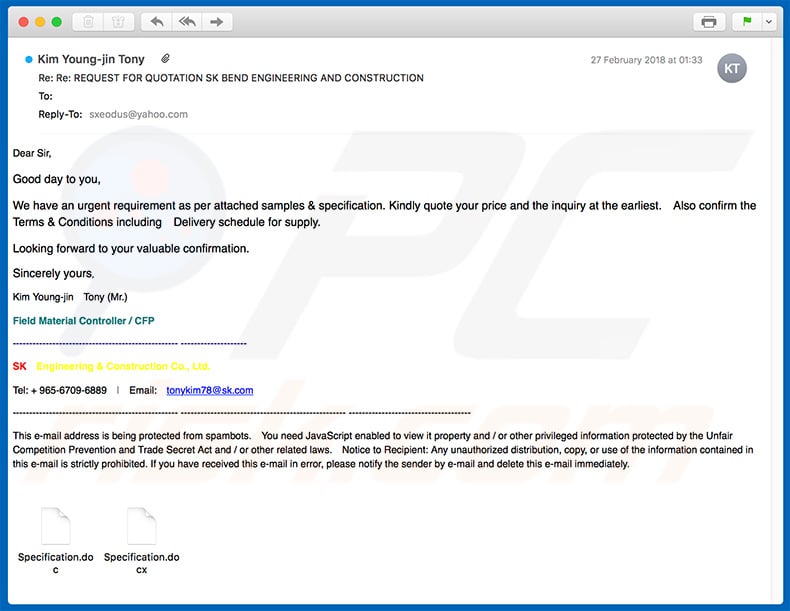
Screenshot of a spam email distributing FormBook virus:
More about the FormBook malware
Following infiltration, FormBook starts monitoring computer activity and gathers data. This malware records keystrokes, takes screenshots, and grabs other information such as visited websites, clipboard data, saved logins/passwords, etc. The information often includes personal details (e.g., banking information) that FormBook's distributor can misuse to generate revenue.
Therefore, the presence of this malware can lead to significant financial losses and serious privacy issues. In addition, FormBook is capable of executing commands sent from remote Command and Control (C&C) servers.
For example, the commands are able to reboot and shutdown the system, download various files/archives and run/extract them, and so on (full list of features). In this way, criminals can perform remote tasks, leading to other high-risk computer infections or system corruption (e.g., criminals might download and execute ransomware).
FormBook malware must be eliminated immediately. If you have recently opened suspicious email attachments and believe that your system is infected, use a legitimate anti-virus suite to perform a full system scan and eliminate all threats. In fact, you are strongly advised to have one installed and running. This will help to prevent further infections.
| Name | FormBook malware |
| Threat Type | Trojan, password-stealing virus, banking malware, spyware. |
| Detection Names | Avast (Win32:DangerousSig [Trj]), BitDefender (Trojan.GenericKD.31824150), ESET-NOD32 (A Variant Of Win32/Injector.EENG), Kaspersky (Trojan-Spy.Win32.Noon.ackv), Full List (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similarities with other malware
FormBook shares similarities with a number of other malware infections such as Adwind. Most are developed by different cyber criminals and have slightly differing functionality. In general, however, they are more or less identical.
These viruses typically record user-system information, open backdoors for other high-risk malware to infiltrate the system, misuse system resources to mine cryptocurrency, or run other unwanted processes (e.g., Botnet).
The presence of these viruses might cause various problems including (but not limited to) system corruption, hardware damage, file loss, and privacy issues (e.g., identity theft).
How did FormBook install on my computer?
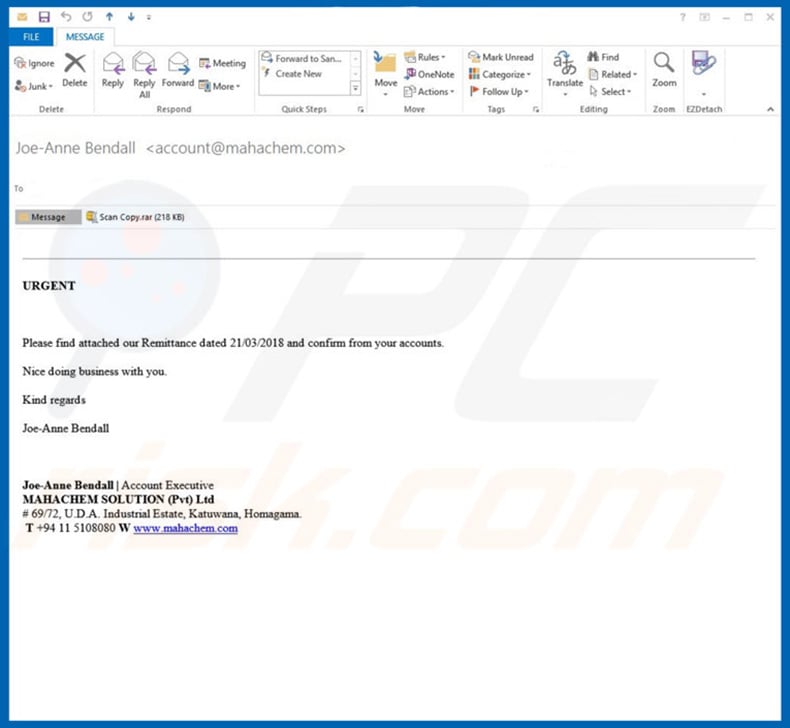
As mentioned above, FormBook is promoted using spam emails that contain messages relating to various business fields (e.g., engineering). These messages briefly describe the contents of malicious attachments (e.g., PDF file, MS Office document, or similar) and encourage users to open them.
Opening them, however, executes scripts that stealthily download and install malware. This distribution method is very popular amongst ransomware developers. Many regular users (especially those who know little about cyber security) are often tricked into downloading and opening such attachments.
How to avoid installation of malware?
The main reasons for computer infections are poor knowledge and careless behavior. If you want to prevent infections, be very cautious when browsing the Internet. We strongly advise you to think twice before opening email attachments - be sure that they are sent from trustworthy/recognizable addresses and that they are relevant.
Messages received via suspicious email addresses should be deleted immediately, without reading. Spam email is not the only way to proliferate malware. Therefore, be cautious when downloading/installing software. Download applications from official sources only, using direct download links.
Criminals monetize third party downloaders/installers by proliferating rogue apps, and thus, these tools should not be used. During downloading/installation, carefully analyze each step (especially "Custom/Advanced" settings) and opt-out of all additionally-included programs.
We also advise to keep installed applications up-to-date and, again, use a legitimate anti-virus/anti-spyware suite. Note, however, that criminals proliferate malware via fake updaters, so use implemented update functions only. As with download/installation tools, third party updaters should never be used. The key to computer safety is caution.
Another variant of spam email distributing FormBook:
List of FormBook's actions that can triggered using C&C server:
- Clear browser cookies
- Collect passwords and create a screenshot
- Download and execute file
- Download and unpack ZIP archive
- Launch a command via ShellExecute
- Reboot system
- Remove bot from host system
- Shutdown system
- Update bot on host system
Update May 18, 2020 - The outbreak of Coronavirus (COVID-19) has significantly affected the cyber world. Cybercriminals are taking advantage of the situation and attempting to spread malware in a variety of ways. One of the most popular methods is spam emails.
They send hundreds of thousands of Coronavirus-related emails containing malicious attachments to spread a variety of malware and FormBook is not an exception. You can read more about these spam emails in our "Coronavirus Email Virus" article.
Another spam email used to spread FormBook virus via attached malicious DMG file:
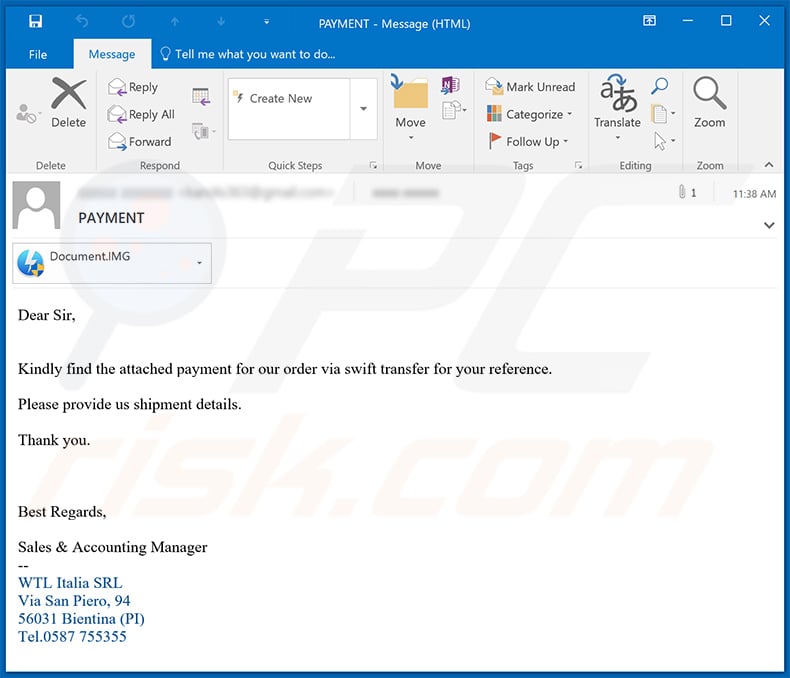
Text presented within:
Subject: PAYMENT
Dear Sir,
Kindly find the attached payment for our order via swift transfer for your reference.
Please provide us shipment details.
Thank you.
Best Regards,Sales & Accounting Manager
--
WTL Italia SRL
Via San Piero, 94
56031 Bientina (PI)
Tel.0587 755355
Update October 26, 2020 - Cyber criminals have recently "rebranded" FormBook malware which is now named XLoader. The entire malware remains the same, only the name used in cyber criminal forums while selling this malware has changed.
Screenshot of yet another spam email used to spread FormBook malware (the attachment is a .r00 archive containing a malicious executable):
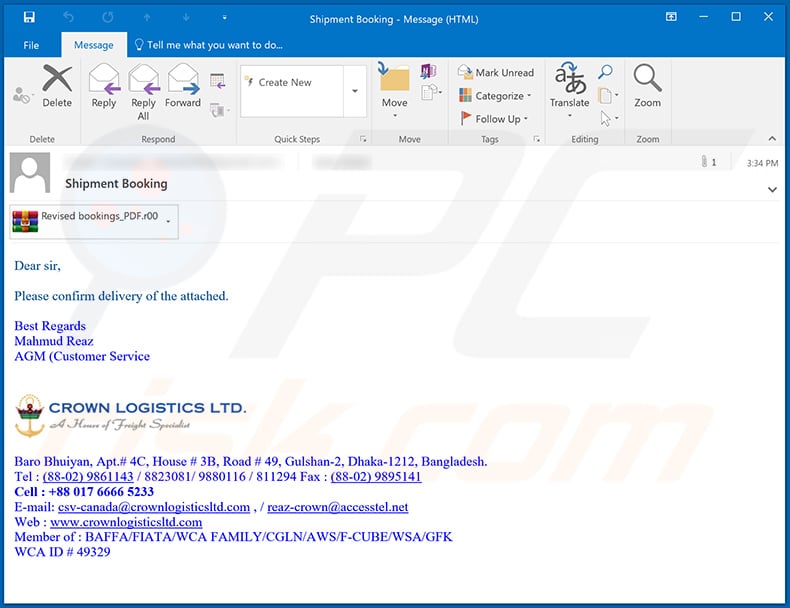
Text presented within:
Subject: Shipment Booking
Dear sir,
Please confirm delivery of the attached.
Best Regards
Mahmud Reaz
AGM (Customer Service)Baro Bhuiyan, Apt.# 4C, House # 3B, Road # 49, Gulshan-2, Dhaka-1212, Bangladesh.
Tel : (88-02) 9861143 / 8823081/ 9880116 / 811294 Fax : (88-02) 9895141
Cell : +88 017 6666 5233
E-mail: csv-canada@crownlogisticsltd.com , / reaz-crown@accesstel.net
Web : www.crownlogisticsltd.com
Member of : BAFFA/FIATA/WCA FAMILY/CGLN/AWS/F-CUBE/WSA/GFK
WCA ID # 49329
Example of a malicious MS Excel document used to spread FormBook trojan:
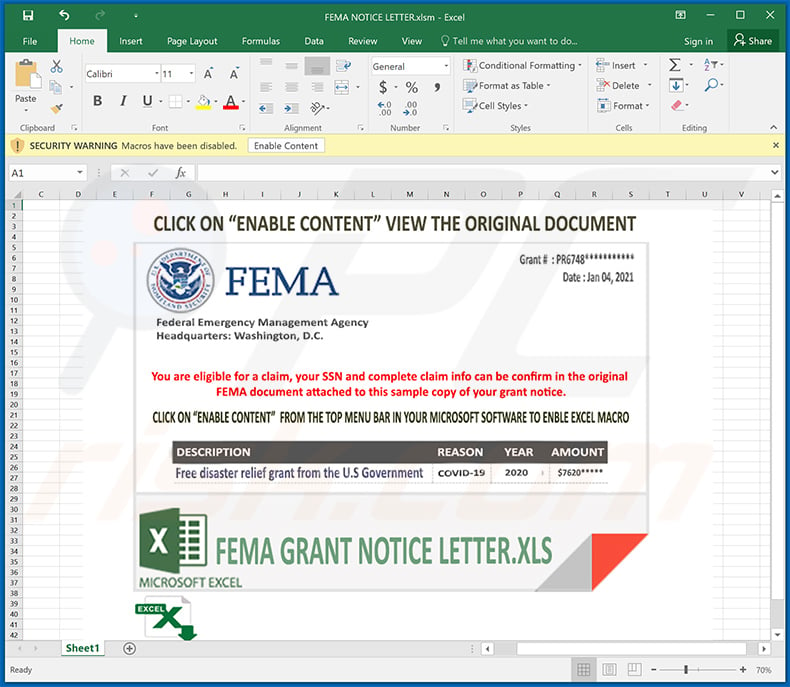
Another example of a spam email used to spread FormBook malware:
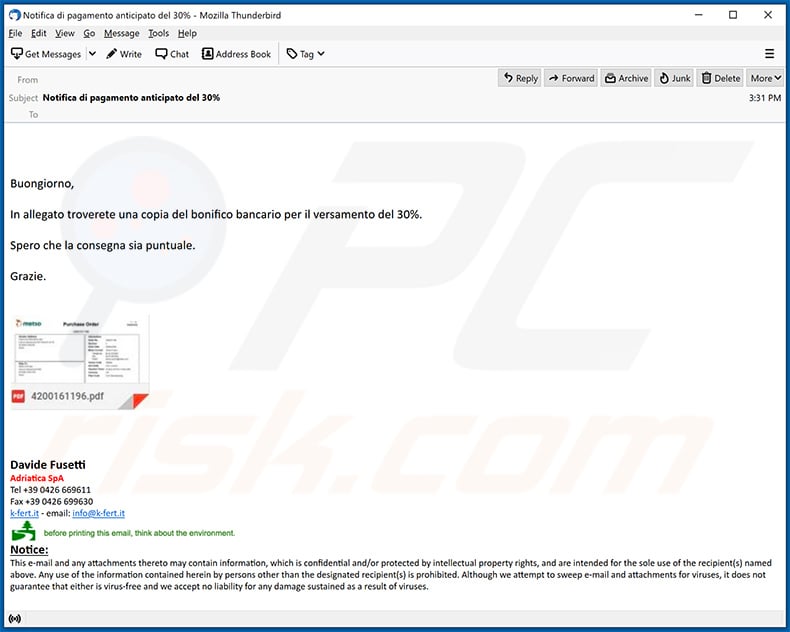
Text presented within:
Subject: Notifica di pagamento anticipato del 30%
Buongiorno,In allegato troverete una copia del bonifico bancario per il versamento del 30%.
Spero che la consegna sia puntuale.
Grazie.
Davide FusettiAdriatica SpA
Tel +39 0426 -
Fax +39 0426 -
k-fert.it - email: info@k-fert.it
before printing this email, think about the environment.
Notice:
This e-mail and any attachments thereto may contain information, which is confidential and/or protected by intellectual property rights, and are intended for the sole use of the recipient(s) named above. Any use of the information contained herein by persons other than the designated recipient(s) is prohibited. Although we attempt to sweep e-mail and attachments for viruses, it does not guarantee that either is virus-free and we accept no liability for any damage sustained as a result of viruses.
Yet another example of a spam email spreading FormBook:
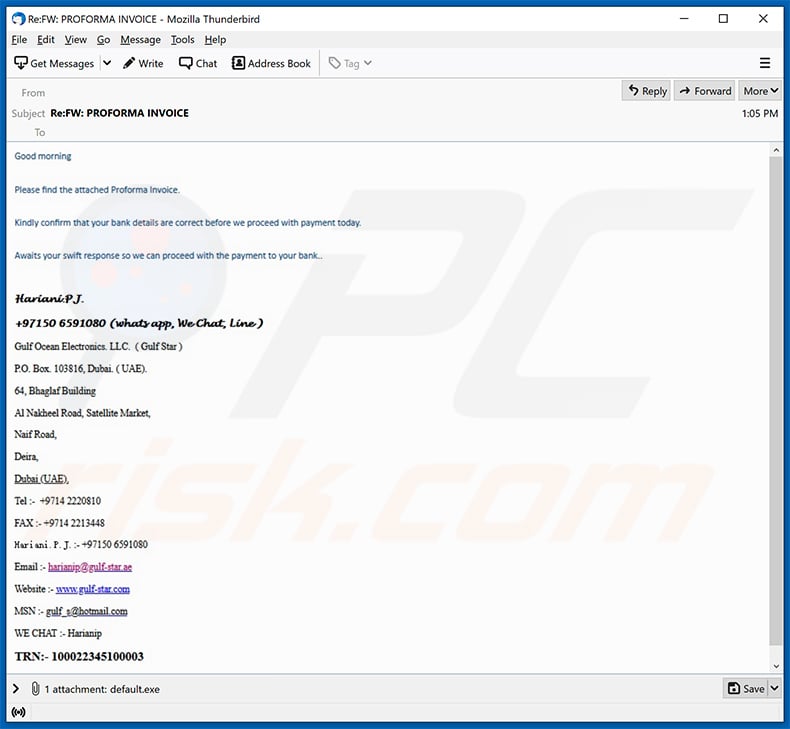
Text presented within:
Good morning
Please find the attached proforma invoice
Kindly confirm that your bank details are correct before we proceed with payment today.
Awaits your swift response so we can proceed with the payment to your bank..
Hariani.PJ.
+97150 6591080 (whats app, WeChat, Line)
Gulf Ocean Electronics. LLC. ( Gulf Star )
P.O. Box. 103816, Bubai. ( UAE)
64, Bhanglaf Building
Al nakheel Road, Satellite Market,
Naif Road,
Deira,
Dubai (UAE)
Tel :- +9714 2220810
FAX :- +9714 2213448
Hariani . P . J. :- +97150 6591080
Email :- harianip@gulf-star.ae
Website :- www.gulf-star.com
MSN :- gulf_s@hotmail.com
WE CHAT :- Harianip
TRN: - 100022345100003
Yet another spam email used to spread FormBook malware via attached malicious executables:
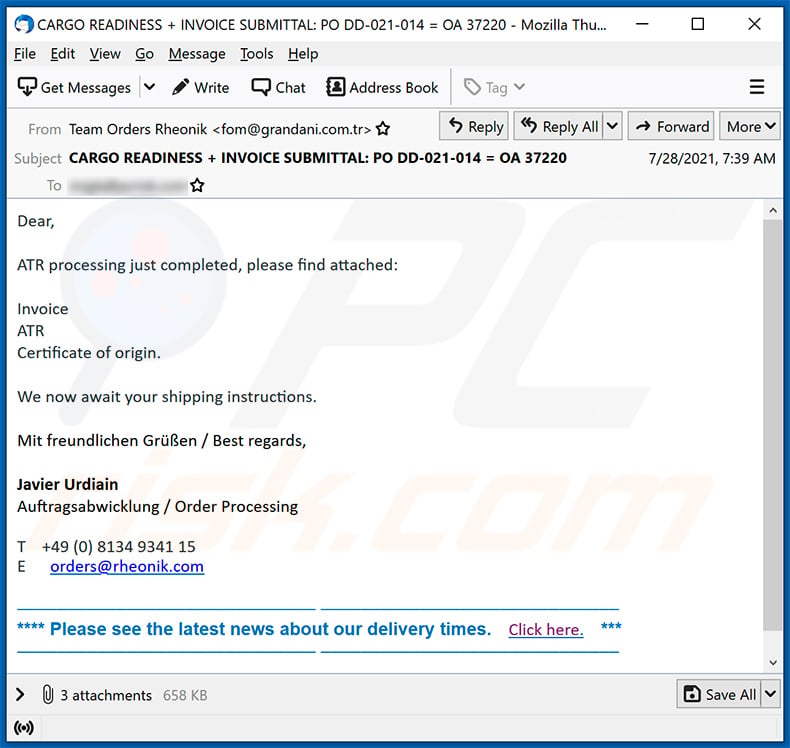
Text presented within:
Subject: CARGO READINESS + INVOICE SUBMITTAL: PO DD-021-014 = OA 37220
Dear,
ATR processing just completed, please find attached:
Invoice
ATR
Certificate of origin.
We now await your shipping instructions.
Mit freundlichen Grüßen / Best regards,
Javier Urdiain
Auftragsabwicklung / Order ProcessingT +49 (0) 8134 9341 15
E orders@rheonik.com
–––––––––––––––––––––––––––––– ––––––––––––––––––––––––––––––**** Please see the latest news about our delivery times. Click here. ***
–––––––––––––––––––––––––––––– ––––––––––––––––––––––––––––––
Another example of a spam email spreading FormBook malware:
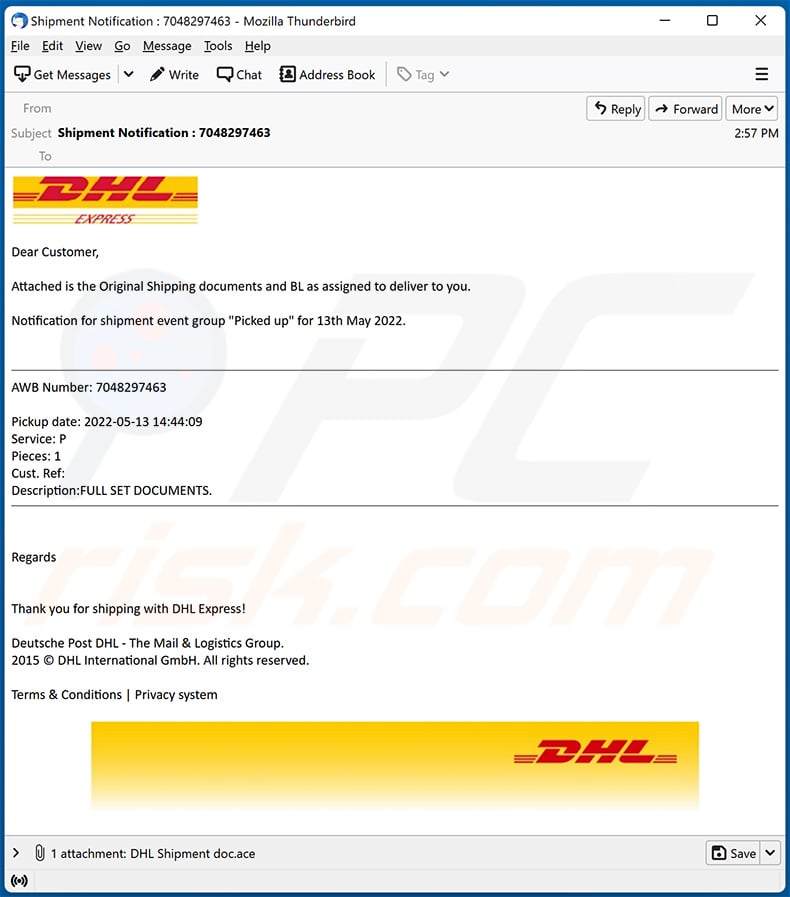
Text presented within:
Subject: Shipment Notification : 7048297463
DHL EXPRESS
Dear Customer,
Attached is the Original Shipping documents and BL as assigned to deliver to you.
Notification for shipment event group "Picked up" for 13th May 2022.
AWB Number: 7048297463
Pickup date: 2022-05-13 14:44:09
Service: P
Pieces: 1
Cust. Ref:
Description:FULL SET DOCUMENTS.
Regards
Thank you for shipping with DHL Express!Deutsche Post DHL - The Mail & Logistics Group.
2015 © DHL International GmbH. All rights reserved.Terms & Conditions | Privacy system
DHL
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is FormBook?
- STEP 1. Manual removal of FormBook malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with FormBook malware, should I format my storage device to get rid of it?
FormBook can be removed by following the steps described in our article. It is unnecessary to format the storage device to eliminate FormBook malware.
What are the biggest issues that malware can cause?
Malware can be used to encrypt files, steal identities, and personal accounts, make fraudulent transactions (steal money), mine cryptocurrency, and other purposes. It depends on the type of malware (its capabilities).
What is the purpose of FormBook malware?
FormBook can record keystrokes, capture screenshots, steal information such as visited websites, clipboard data, saved logins/passwords, and more. Also, it can receive commands from C2 server and execute them. This feature can be used to inject additional malware and perform other actions on computer.
How did a malware infiltrate my computer?
It is known that FormBook is delivered via email. Cybercriminals send emails containing malicious attachments or links to trick recipients into executing FormBook. In other cases, malware can infect computers via malicious drive-by downloads, cracked software download pages, files downloaed from untrustworthy sources, etc.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner scans the operating system and removes detected malware (it can detect almost all known malware). It is important to know that running a full system scan is a must when a computer is infected with high-end malware. Malware of this kind can hide deep in the system.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion