Avoid having your account credentials stolen by this email
Phishing/ScamAlso Known As: Email Credentials Phishing spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "Email credentials phishing"?
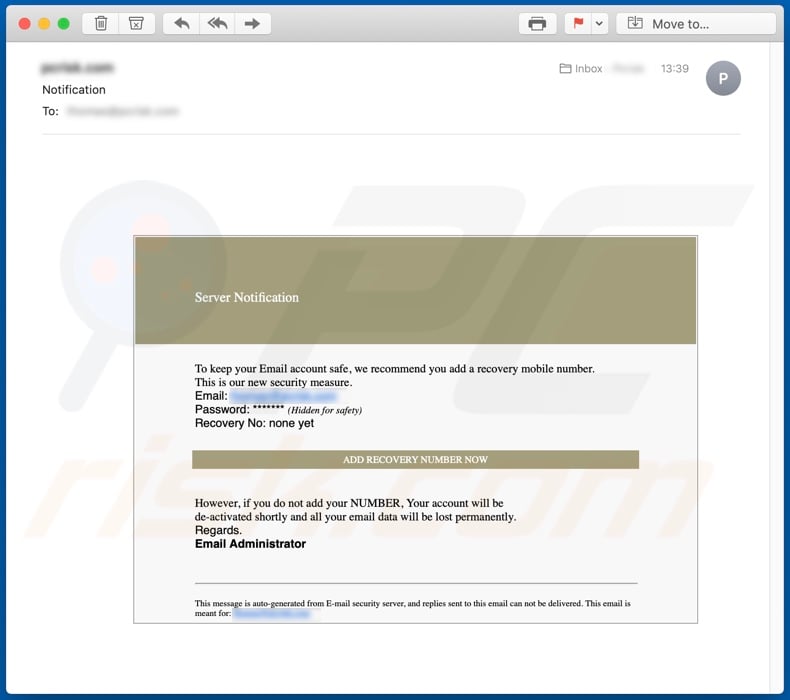
Email credentials phishing describes a deceptive message claiming to be an official notification from the recipient's email service provider. It alerts users of a 'new security measure' in an attempt to steal their email credentials. This scam tactic is called "phishing" and is a form of social engineering.
Note that most deceptive/scam emails are disguised as "official", "important", "priority". and similar. You are expressly advised against opening suspicious mail or opening attachments/links present within them.
More about this phishing email
This message is supposedly from the "Email Administrator", an automatically generated message from the "E-mail security server". It states that, to keep their email accounts safe, users must add a recovery mobile number. This is allegedly a newly-added security measure.
It attempts to alarm users by specifying that, unless a recovery number is added, their accounts will be deactivated, and all associated data, permanently lost.
If users are tricked into 'updating' their email account security in this way, the link in the message redirects them to a hijacked website built using the WordPress template system.
In the site, users are encouraged to enter their email credentials (log-ins and passwords), however, rather than this being an account confirmation allowing users to add recovery numbers, the inputted information is stolen. While this is not a malware infection attempt, it is nonetheless a potentially harmful scam.
If you have already trusted such an email and attempted to log-in with your account details via a third party site, you are strongly advised to immediately change the password within your email service.
| Name | Email Credentials Phishing. |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Scam claims that the user's email security requires updating with a recovery mobile number. |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similar emails in general
Deceptive/scam emails are a frequent occurrence and they serve various purposes. The mail can be employed to obtain private data ("phishing"), infect devices (via dangerous file attachments and/or links leading to them), or to generate profit for cyber criminals in some other way.
You should routinely scan your systems to ensure email account safety. "HARASSMENT COMPLAINT", "On This Day I Hacked Your OS", "Ministry of Justice", and "TOYOTA LOTTERY ORGANIZATION" are some examples of other email scams.
How do spam campaigns infect computers?
Spam campaigns send thousands of deceptive emails. These messages cause infections through malicious files or links leading to them. The emails are typically marked as "official", "important", "urgent" or otherwise highlighted as priority mail.
The attachments come in various formats, such as archive (RAR, ZIP) and executable (.exe, .run) files, Microsoft Office and PDF documents, JavaScript and many others. When these infectious files are opened (executed, run, etc.), they are triggered to initiate the infection and begin downloading/installing malware.
For example, Microsoft Office documents ask to enable macro commands (i.e., to enable editing). If macro commands are enabled, the infection process starts. Note that, in Microsoft Office versions released prior to 2010, this process begins immediately after the document is opened.
How to avoid installation of malware
You are strongly advised not to open suspicious and/or irrelevant emails, especially those received from unknown senders (addresses). Any attachments or links found in suspicious mail must never be opened, as they are the source of a potential system infection.
Users who receive a large influx of emails are advised to regularly run system scans to ensure that none of them have infiltrated an infection into the device. To prevent Microsoft Office documents from downloading/installing malware, use Microsoft Office versions released after 2010.
The newer versions have "Protected View" mode, which stops dangerous documents from automatically enabling macro commands, thereby preventing them from infecting the system with malicious content.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "Email credentials phishing" email message:
Server Notification
To keep your Email account safe, we recommend you add a recovery mobile number.
This is our new security measure.
Email:
Password: ******* (Hidden for safety)
Recovery No: none yet
ADD RECOVERY NUMBER NOW
However, if you do not add your NUMBER, Your account will be
de-activated shortly and all your email data will be lost permanently.
Regards.
Email Administrator
This message is auto-generated from E-mail security server, and replies sent to this email can not be delivered. This email is meant for: **********
Screenshots of the website to which "Email credential phishing" redirects:
Appearance of the website "Email credential phishing" redirects to (GIF):
Another variant of email credentials phishing spam campaign, which contains an attachment: an HTML file ("email_verification_processor.html"). This file imitates an email login page and contains two input fields (login and password). Once entered, this data is saved to a remote server controlled by cyber criminals.
Screenshot of this email spam campaign:
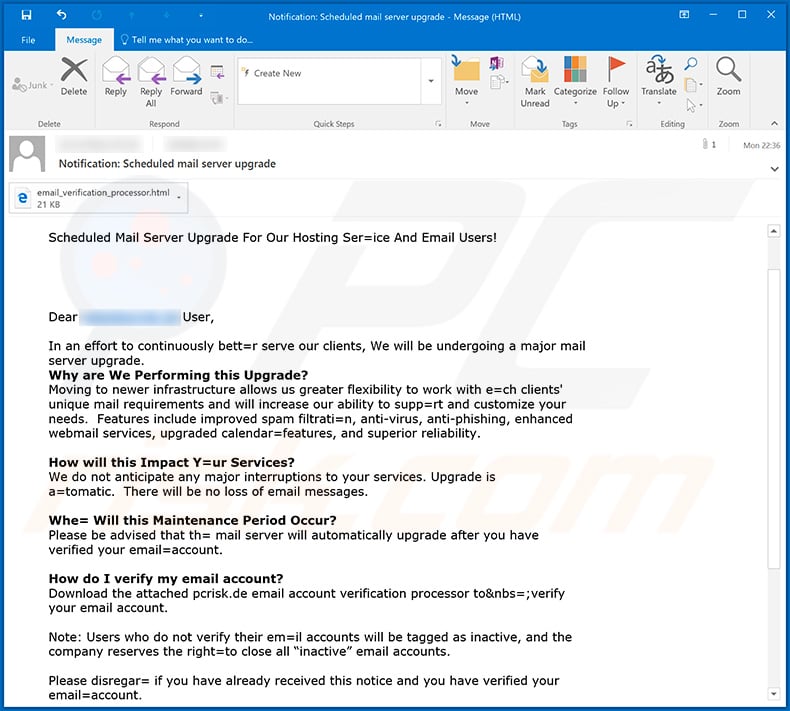
Text presented within this email:
Subject: Notification: Scheduled mail server upgrade
Scheduled Mail Server Upgrade For Our Hosting Ser=ice And Email Users!Dear ******** User,
In an effort to continuously bett=r serve our clients, We will be undergoing a major mail server upgrade.
Why are We Performing this Upgrade?
Moving to newer infrastructure allows us greater flexibility to work with e=ch clients' unique mail requirements and will increase our ability to supp=rt and customize your needs. Features include improved spam filtrati=n, anti-virus, anti-phishing, enhanced webmail services, upgraded calendar=features, and superior reliability.How will this Impact Y=ur Services?
We do not anticipate any major interruptions to your services. Upgrade is a=tomatic. There will be no loss of email messages.Whe= Will this Maintenance Period Occur?
Please be advised that th= mail server will automatically upgrade after you have verified your email=account.How do I verify my email account?
Download the attached ******** email account verification processor to&nbs=;verify your email account.Note: Users who do not verify their em=il accounts will be tagged as inactive, and the company reserves the right=to close all “inactive” email accounts.
Please disregar= if you have already received this notice and you have verified your email=account.
Thanks,
******** Hosting Service Providersale=********
Screenshot of the attached HTML file ("email_verification_processor.html"):
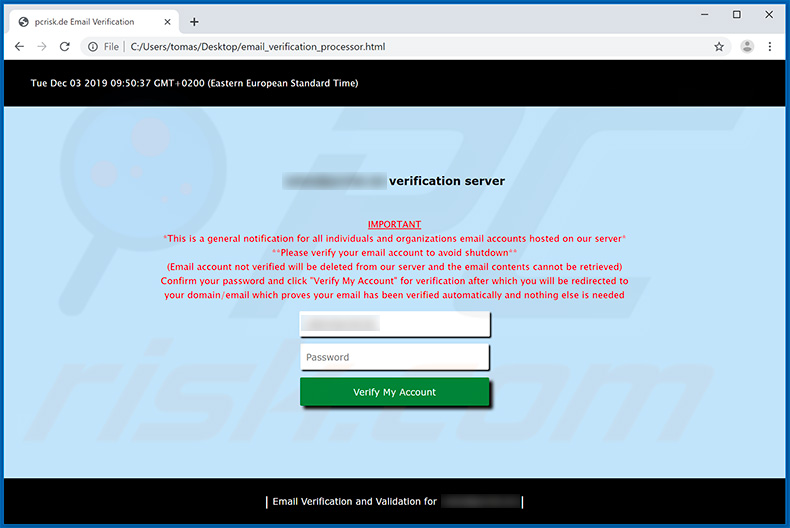
Text presented within this file:
Tue Dec 03 2019 09:50:59 GMT+0200 (Eastern European Standard Time)
******** verification server
IMPORTANT
*This is a general notification for all individuals and organizations email accounts hosted on our server*
**Please verify your email account to avoid shutdown**
(Email account not verified will be deleted from our server and the email contents cannot be retrieved)
Confirm your password and click "Verify My Account" for verification after which you will be redirected to
your domain/email which proves your email has been verified automatically and nothing else is needed
********
Password
| Email Verification and Validation for ******** |
Another email credentials phishing spam email disguised as cPanel WebMail notification:
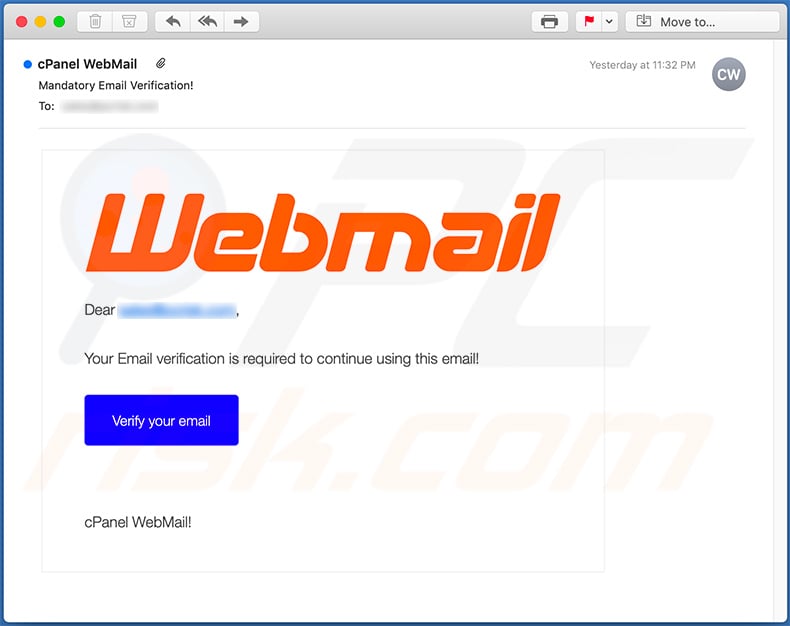
Text presented within:
Subject: cPanel WebMail
Webmail
Dear -,
Your Email verification is required to continue using this email!
Verify your email
cPanel WebMail!
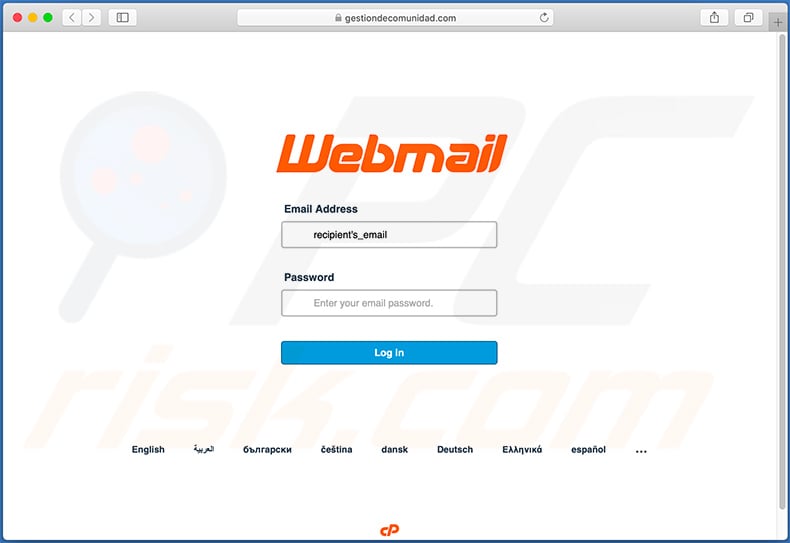
Fake cPanel WebMail login website (gestiondecomunidad[.]com) promoted via this spam email:
Another example of a Microsoft Outlook-related phishing email encouraging recipients to confirm their accounts:
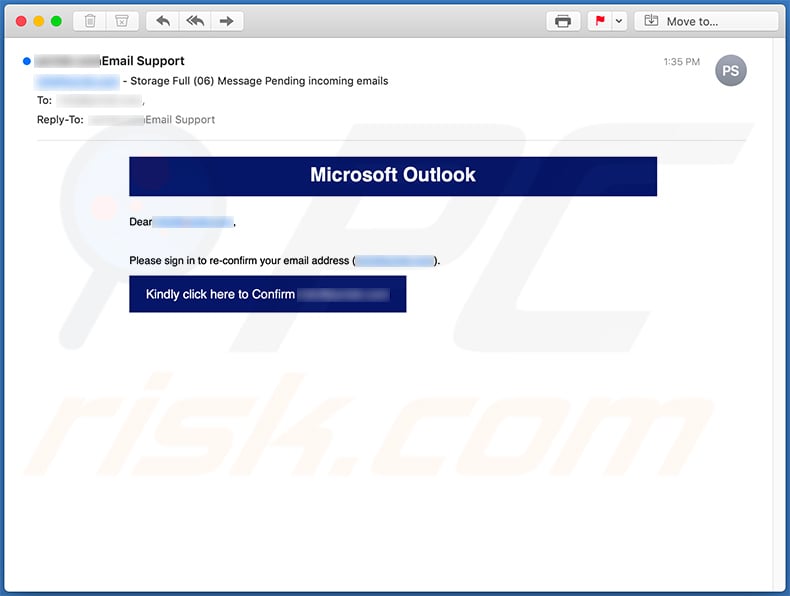
Text presented within:
Subject: ***** - Storage Full (06) Message Pending incoming emails
Microsoft Outlook
Dear *****,Please sign in to re-confirm your email address (*****).
Kindly click here to Confirm *****
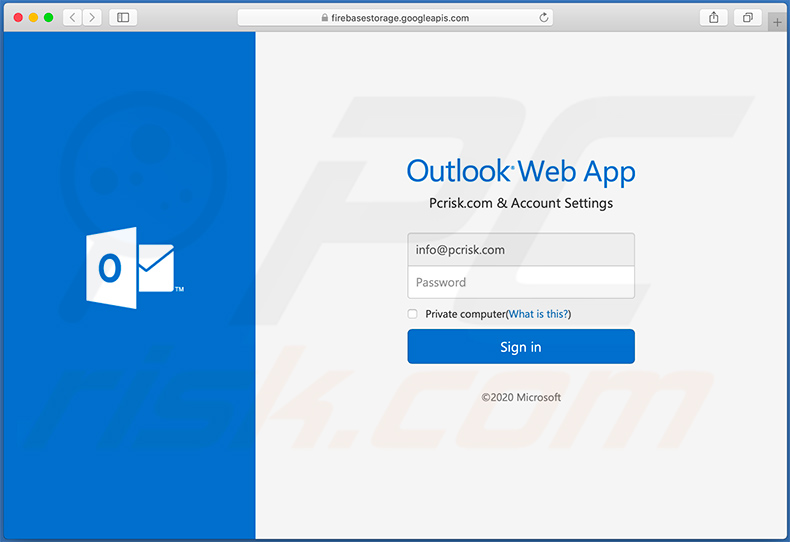
Screenshot of a phishing website (fake Outlook login site) promoted via this email:
Yet another email phishing spam campaign:
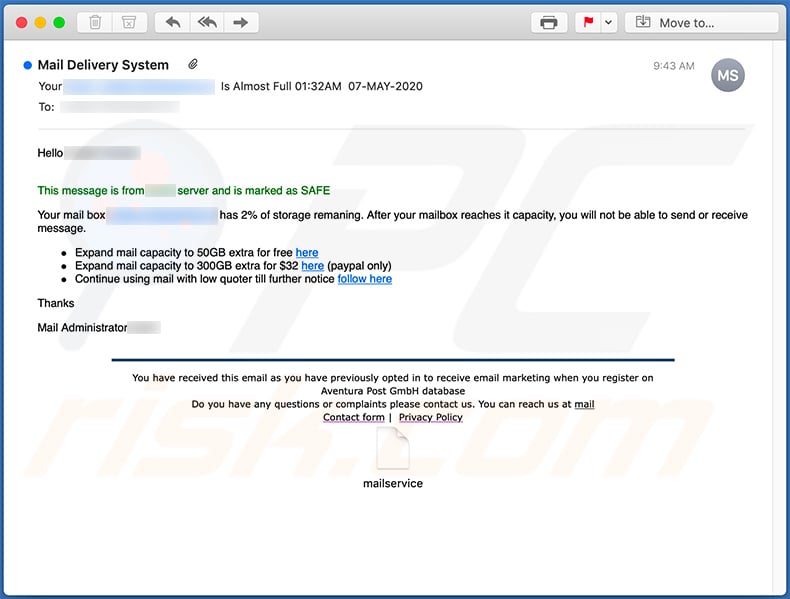
Text presented within:
Subject: Mail Delivery System
Hello -
This message is from - server and is marked as SAFEYour mail box - has 2% of storage remaning. After your mailbox reaches it capacity, you will not be able to send or receive message.
Expand mail capacity to 50GB extra for free here
Expand mail capacity to 300GB extra for $32 here (paypal only)
Continue using mail with low quoter till further notice follow here
ThanksMail Administrator -
You have received this email as you have previously opted in to receive email marketing when you register on Aventura Post GmbH database
Do you have any questions or complaints please contact us. You can reach us at mail
Contact form | Privacy Policy
Screenshot of the promoted phishing website (cybxtechnolabs[.]com - fake Webmail login):
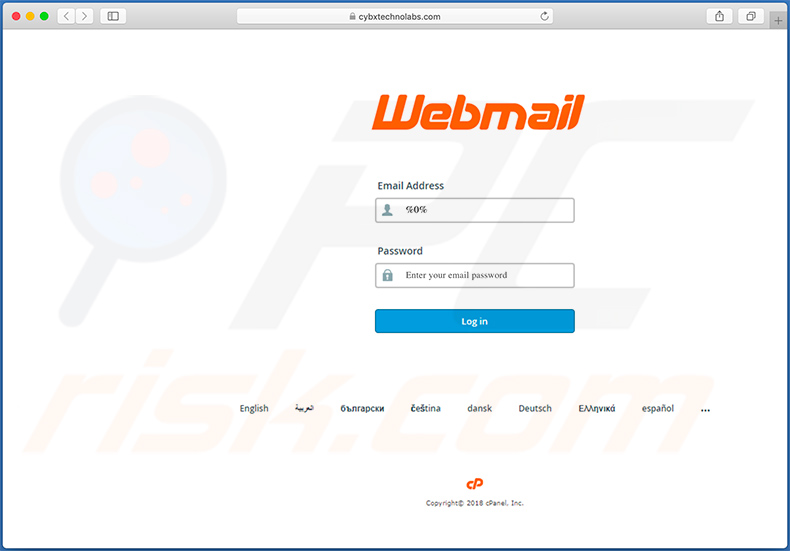
Other scam emails promoting cybxtechnolabs[.]com website:
![Spam email promoting cybxtechnolabs[.]com phishing site](/images/stories/screenshots202005/email-credentials-phishing-update-2020-05-12-another-variant-2.jpg)
Text presented within:
Hello -
We noticed login attempt from IP Address: 49.109.719.11, how ever as part of measures to keep email - safe we have stop such strange login and limited amount of incoming messages for your ID Protection. To restore full service login HERE from any device previously used by you
You have received this email from - service provider as it is authomaiclly registared to receive email marketing when you registered
Do you have any questions or complaints please contact us. You can reach us at mail
Contact form | Privacy Policy
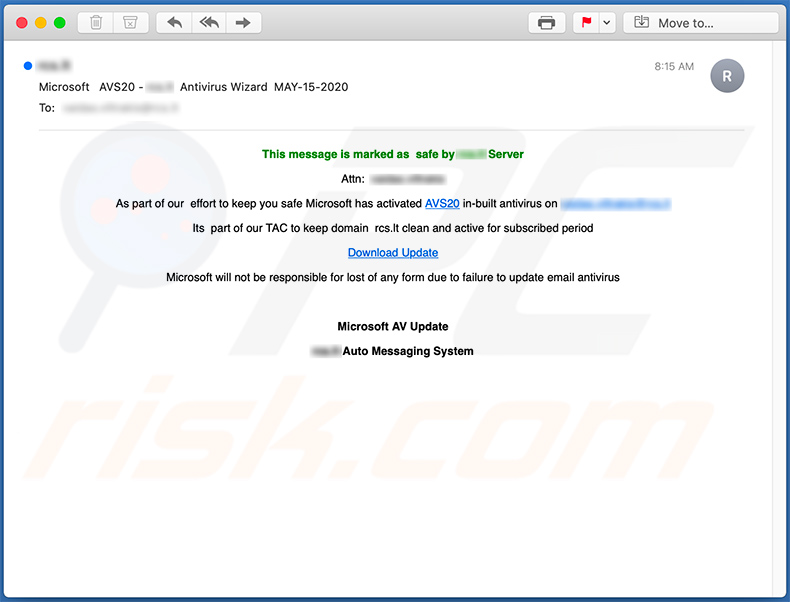
Text presented within:
Subject: Microsoft AVS20 - ***** Antivirus Wizard MAY-15-2020
This message is marked as safe by ***** Server
Attn: *****
As part of our effort to keep you safe Microsoft has activated AVS20 in-built antivirus on *****
- part of our TAC to keep domain ***** clean and active for subscribed period
Download Update
Microsoft will not be responsible for lost of any form due to failure to update email antivirus
Microsoft AV Update
***** Auto Messaging System
Yet another variant of email credentials phishing spam email:
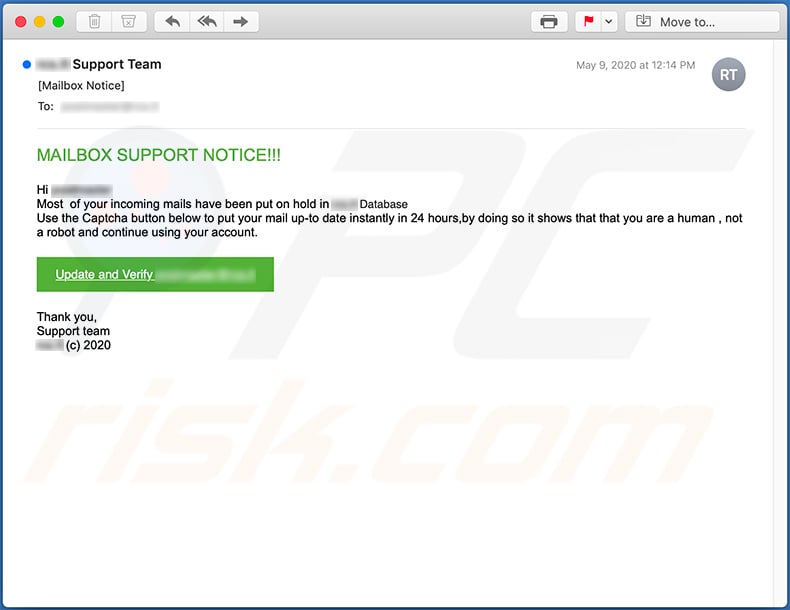
Text presented within:
MAILBOX SUPPORT NOTICE!!!
Hi -
Most of your incoming mails have been put on hold in - Database
Use the Captcha button below to put your mail up-to date instantly in 24 hours,by doing so it shows that that you are a human , not a robot and continue using your account.
Update and Verify -
Thank you,
Support team
- (c) 2020
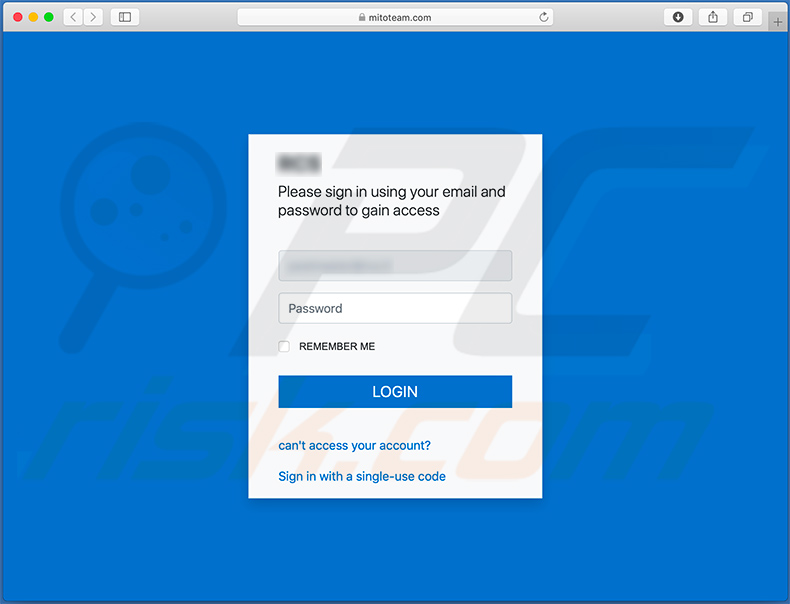
Phishing website (mitoteam[.]com) promoted via this email:
Screenshot of yet another phishing email promoting a fake email login site:
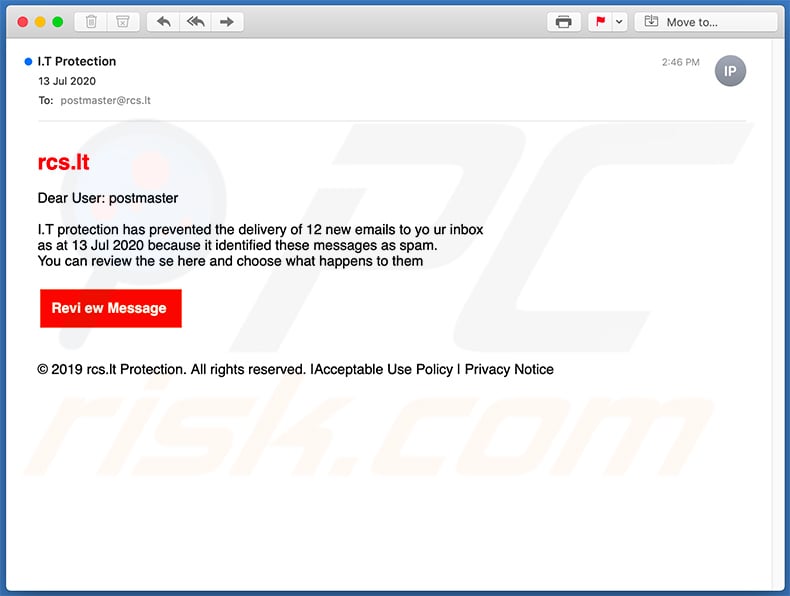
Text presented within:
Dear User: -
I.T protection has prevented the delivery of 12 new emails to yo ur inbox
as at 13 Jul 2020 because it identified these messages as spam.
You can review the se here and choose what happens to them
Revi ew Message
© 2019 rcs.lt Protection. All rights reserved. |Acceptable Use Policy | Privacy Notice
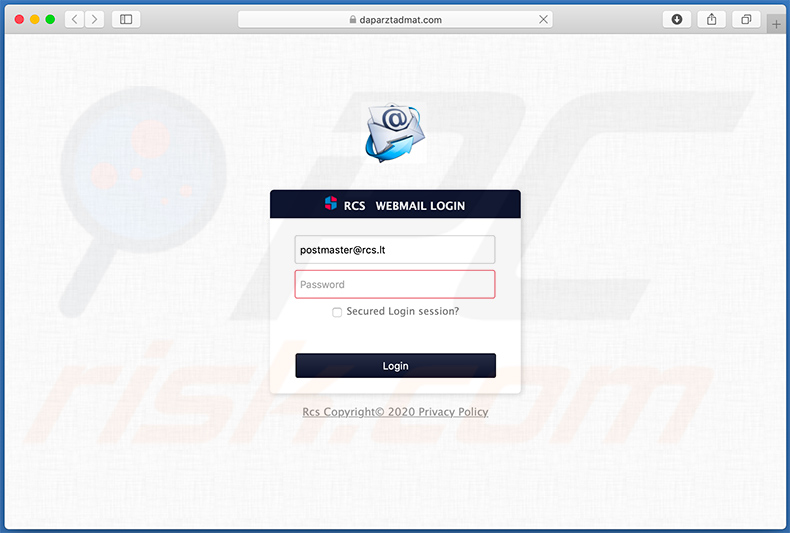
Screenshot of the promoted website (daparztadmat[.]com):
Screenshot of another spam email promoting a fake Webmail login site:
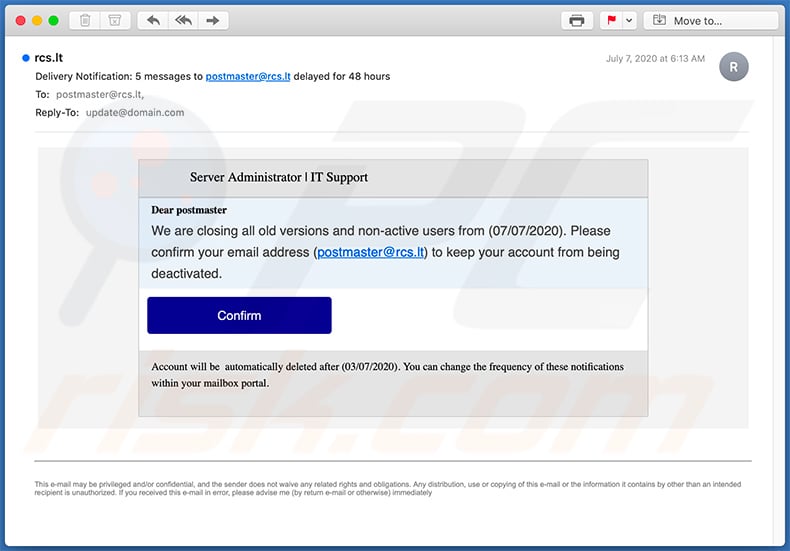
Text presented within:
Subject: Delivery Notification: 5 messages to - delayed for 48 hours
Server Administrator | IT Support
Dear postmaster
We are closing all old versions and non-active users from (07/07/2020). Please confirm your email address (-) to keep your account from being deactivated.Confirm
Account will be automatically deleted after (03/07/2020). You can change the frequency of these notifications within your mailbox portal.
This e-mail may be privileged and/or confidential, and the sender does not waive any related rights and obligations. Any distribution, use or copying of this e-mail or the information it contains by other than an intended recipient is unauthorized. If you received this e-mail in error, please advise me (by return e-mail or otherwise) immediately
Example of a DHL-themed spam email used to promote a phishing site - tings[.]biz:
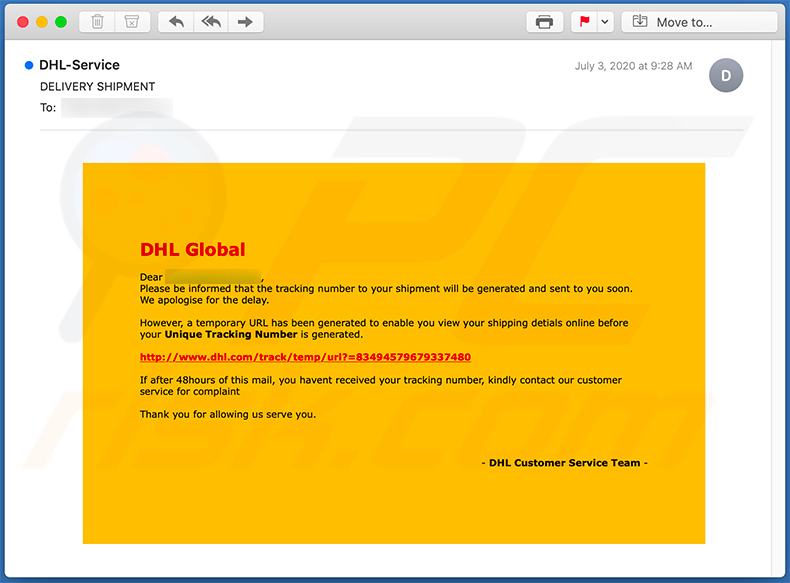
Text presented within:
Subject: DELIVERY SHIPMENT
DHL GlobalDear -,
Please be informed that the tracking number to your shipment will be generated and sent to you soon. We apologise for the delay.However, a temporary URL has been generated to enable you view your shipping detials online before your Unique Tracking Number is generated.
hxxp://www.dhl.com/track/temp/url?=83494579679337480
If after 48hours of this mail, you havent received your tracking number, kindly contact our customer service for complaint
Thank you for allowing us serve you.
- DHL Customer Service Team -
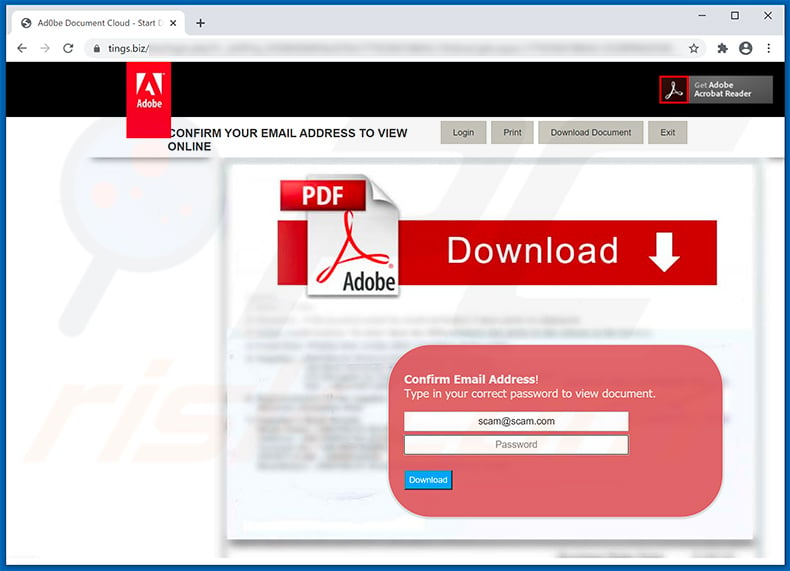
Screenshot of the promoted phishing site - tings[.]biz:
Screenshot of a Equifax-themed spam email used to promote a phishing site:
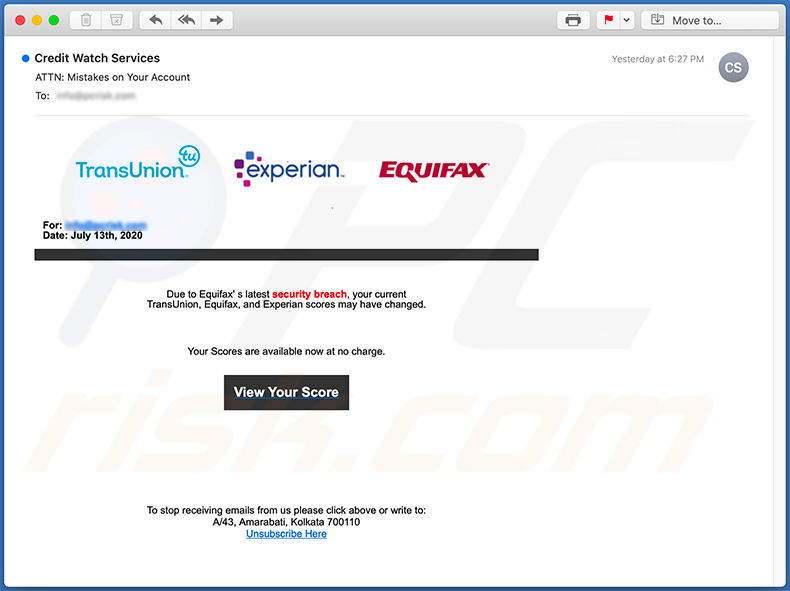
Text presented within:
Subject: ATTN: Mistakes on Your Account
Image of your report
For: -
Date: July 13th, 2020Due to Equifax' s latest security breach, your current
TransUnion, Equifax, and Experian scores may have changed.Your Scores are available now at no charge.
View Your Score
To stop receiving emails from us please click above or write to:
A/43, Amarabati, Kolkata 700110
Unsubscribe Here
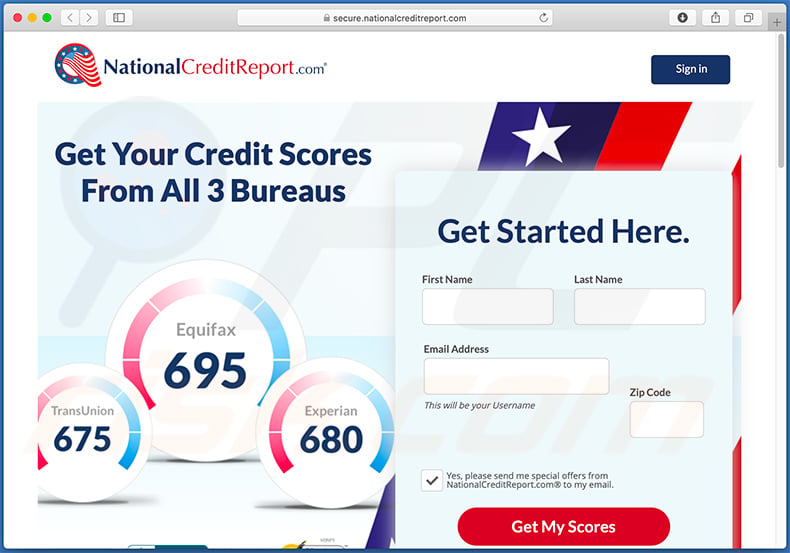
Phishing website promoted via this email:
Screenshot of yet another spam email used to promote a phishing website:
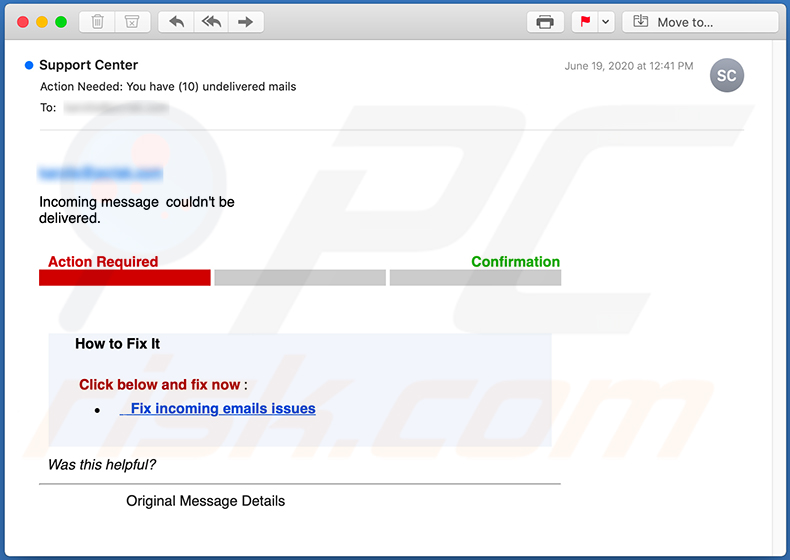
Text presented within:
Subject: Action Needed: You have (10) undelivered mails
Incoming message couldn't be
delivered.
Action Required Confirmation
How to Fix It
Click below and fix now :
Fix incoming emails issues
Was this helpful?
Original Message Details
Screenshot of yet another scam email promoting a fake Webmail login site:
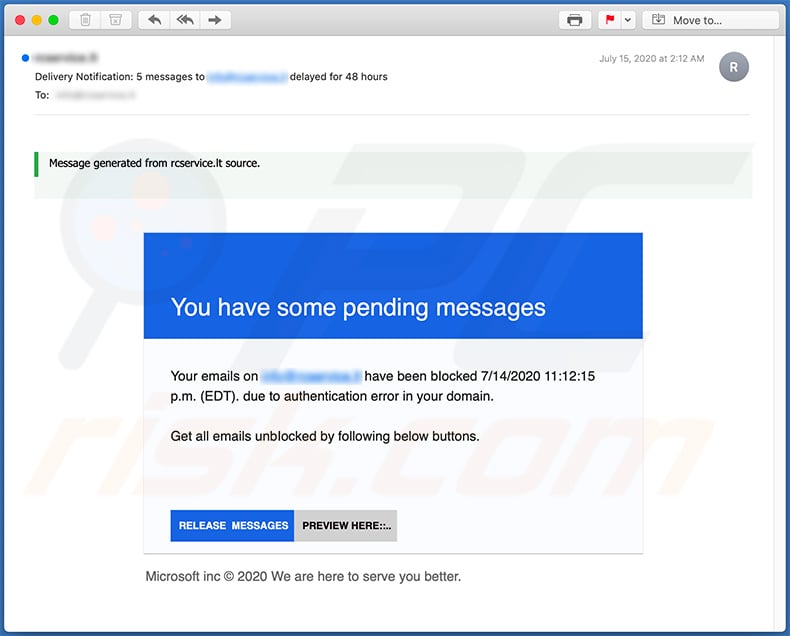
Text presented within:
Subject: Delivery Notification: 5 messages to - delayed for 48 hours
You have some pending messages
Your emails on - have been bIocked 7/14/2020 11:12:15 p.m. (EDT). due to authentication error in your domain.
Get all emails unbIocked by following below buttons.MESSAGES PREVIEW HERE::.
Microsoft inc © 2020 We are here to serve you better.
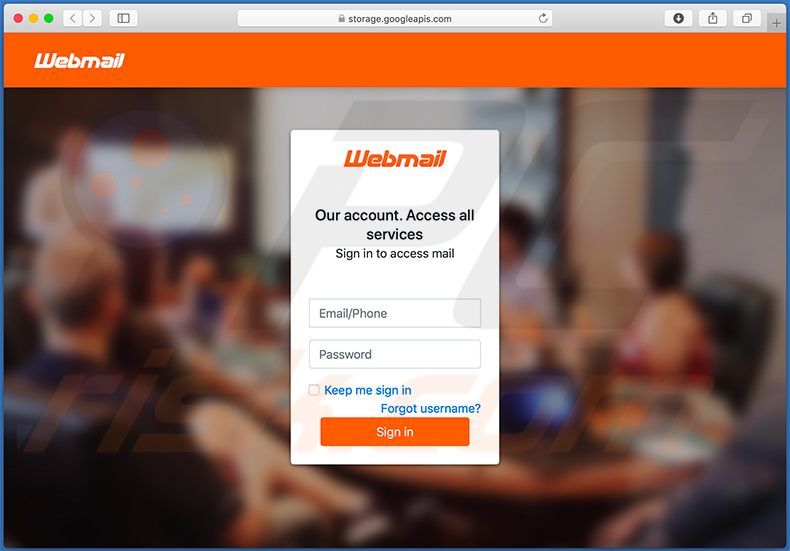
Screenshot of the promoted fake Webmail login site:
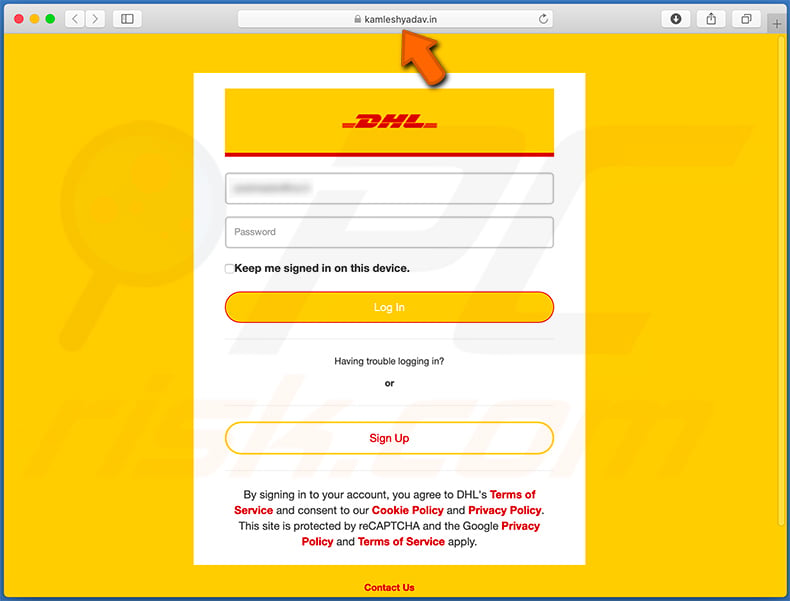
Example of yet another DHL-themed spam email used to promote a phishing website (fake DHL login site):
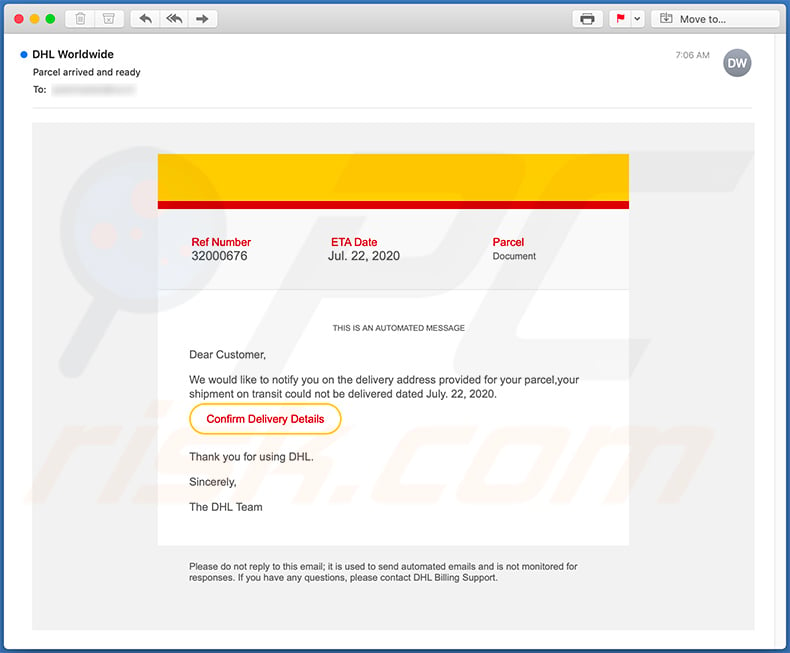
Text presented within:
Subject: Parcel arrived and ready
Ref Number
32000676
ETA Date
Jul. 22, 2020
Parcel
Document
THIS IS AN AUTOMATED MESSAGE
Dear Customer,We would like to notify you on the delivery address provided for your parcel,your shipment on transit could not be delivered dated July. 22, 2020.
Confirm Delivery Details
Thank you for using DHL.
Sincerely,
The DHL Team
Please do not reply to this email; it is used to send automated emails and is not monitored for responses. If you have any questions, please contact DHL Billing Support.
Screenshot of the promoted phishing site (kamleshyadav[.]in):
Example of yet another spam email promoting a phishing site:
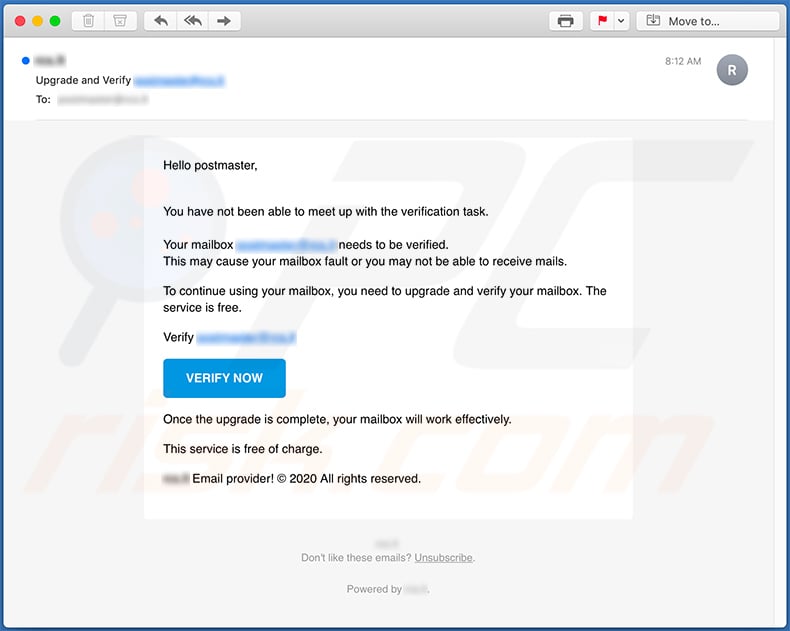
Text presented within:
Subject: Upgrade and Verify
Hello postmaster,You have not been able to meet up with the verification task.
Your mailbox - needs to be verified.
This may cause your mailbox fault or you may not be able to receive mails.To continue using your mailbox, you need to upgrade and verify your mailbox. The service is free.
Verify -
VERIFY NOW
Once the upgrade is complete, your mailbox will work effectively.This service is free of charge.
- Email provider! © 2020 All rights reserved.
-
Don't like these emails? Unsubscribe.
Powered by -.
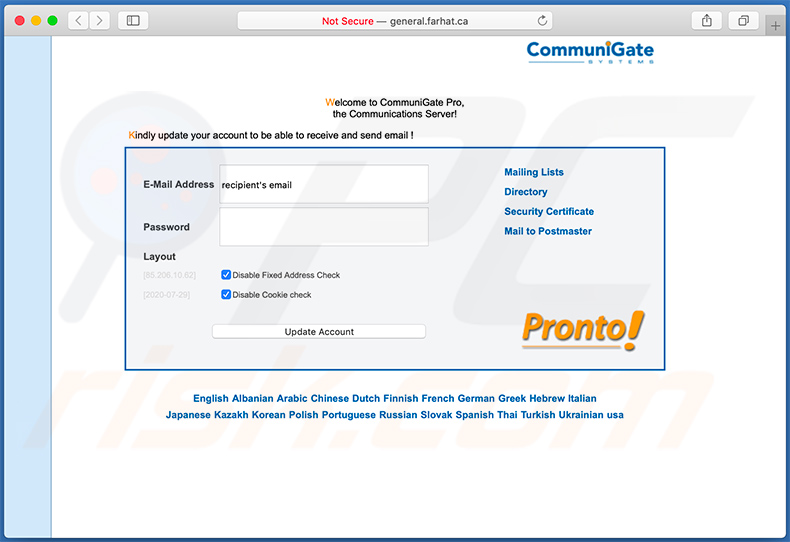
Screenshot of the promoted phishing site (general.farhat[.]ca):
Another example of a spam email used to promote a phishing site:
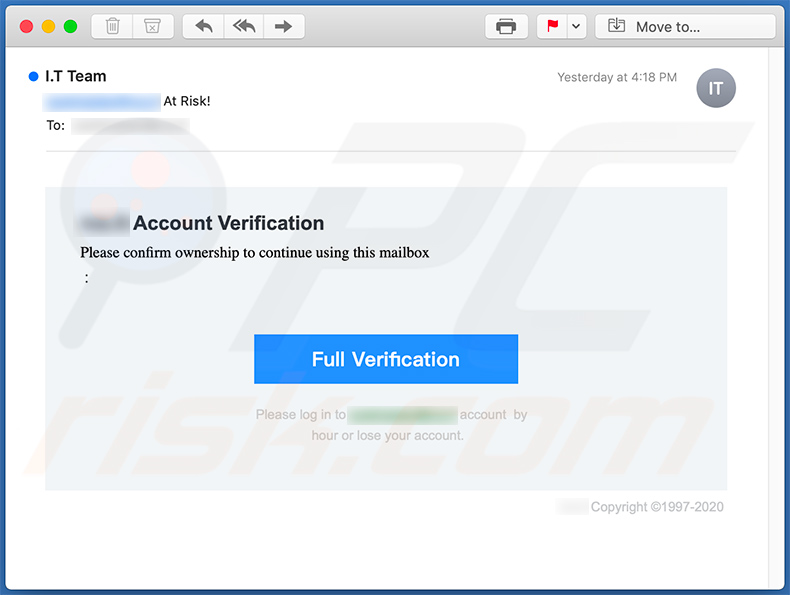
Text presented within:
Subject: - At Risk!
- Account Verification
Please confirm ownership to continue using this mailbox
:
Full Verification
Please log in to - account by hour or lose your account.- Copyright ©1997-2020
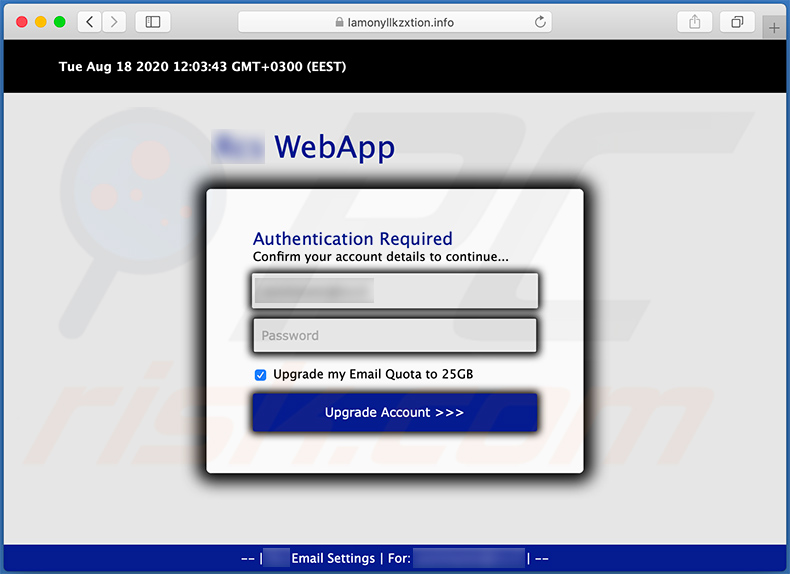
Screenshot of the promoted phishing site (lamonyllkzxtion.info):
Example of yet another spam email used for phishing purposes:
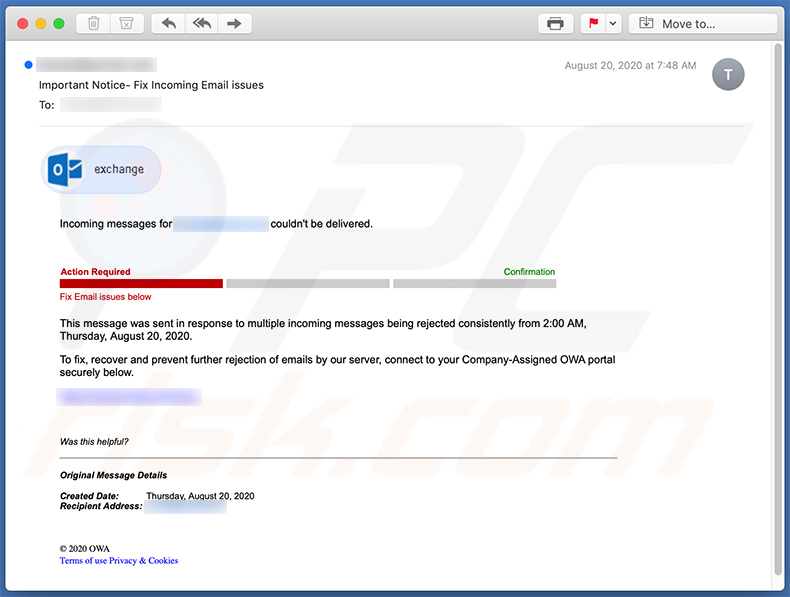
Text presented within:
Subject: Important Notice- Fix Incoming Email issues
Incoming messages for - couldn't be delivered.Action Required Confirmation
Fix Email issues belowThis message was sent in response to multiple incoming messages being rejected consistently from 2:00 AM, Thursday, August 20, 2020.
To fix, recover and prevent further rejection of emails by our server, connect to your Company-Assigned OWA portal securely below.
-
Was this helpful?
Original Message Details
Created Date: Thursday, August 20, 2020
Recipient Address: -
© 2020 OWA
Terms of use Privacy & Cookies
Yet another example of a spam email used to promote a phishing site:
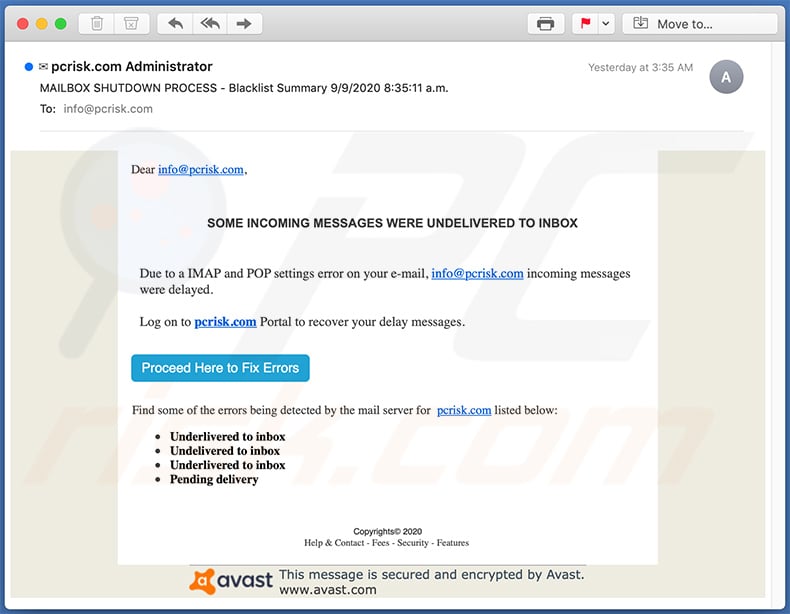
Text presented within:
Subject: MAILBOX SHUTDOWN PROCESS - Blacklist Summary 9/9/2020 8:35:11 a.m.
Dear -,SOME INCOMING MESSAGES WERE UNDELIVERED TO INBOX
Due to a IMAP and POP settings error on your e-mail, - incoming messages were delayed.
Log on to - Portal to recover your delay messages.
Proceed Here to Fix Errors
Find some of the errors being detected by the mail server for - listed below:
Underlivered to inbox
Undelivered to inbox
Underlivered to inbox
Pending deliveryCopyrights© 2020
Help & Contact - Fees - Security - Features
This message is secured and encrypted by Avast.
www.avast.com
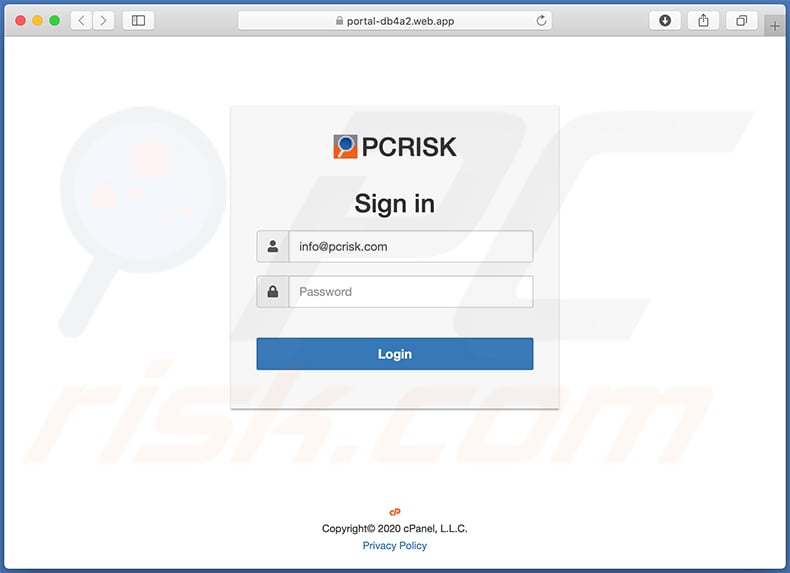
Screenshot of the promoted phishing site:
Yet another spam email (written in Italian language) used for phishing purposes:
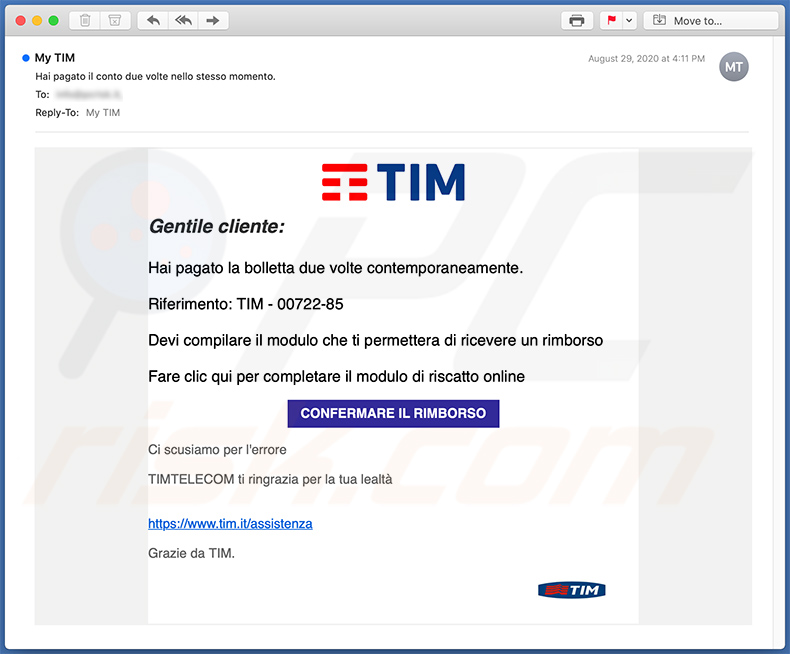
Text presented within:
Subject: Hai pagato il conto due volte nello stesso momento.
Gentile cliente:
Hai pagato la bolletta due volte contemporaneamente.
Riferimento: TIM - 00722-85
Devi compilare il modulo che ti permettera di ricevere un rimborso
Fare clic qui per completare il modulo di riscatto online
CONFERMARE IL RIMBORSO
Ci scusiamo per l'errore
TIMTELECOM ti ringrazia per la tua lealtà
hxxps://www.tim.it/assistenzaGrazie da TIM.
Yet another scam email used for phishing purposes:
Text presented within:
Subject: finance@parfumsdorsay.com sent you files via WeTransfer
Click 'Download images' to view images
-
you have received some files
3 items, 8.3 mb in total
Hello,
As Discussed,Here is the product specifications, list of required products and order.Thanks
Get your files
Download link
-
3 items
List of Items.pdf 2.1 mb
Purchase Order.pdf 0.9 mb
Specifications.pdf 5.3 mb
To make sure our emails arrive, please add noreply@wetransfer.com to your contacts.
About WeTransfer ・ Help ・ Legal ・ Report this transfer as spam
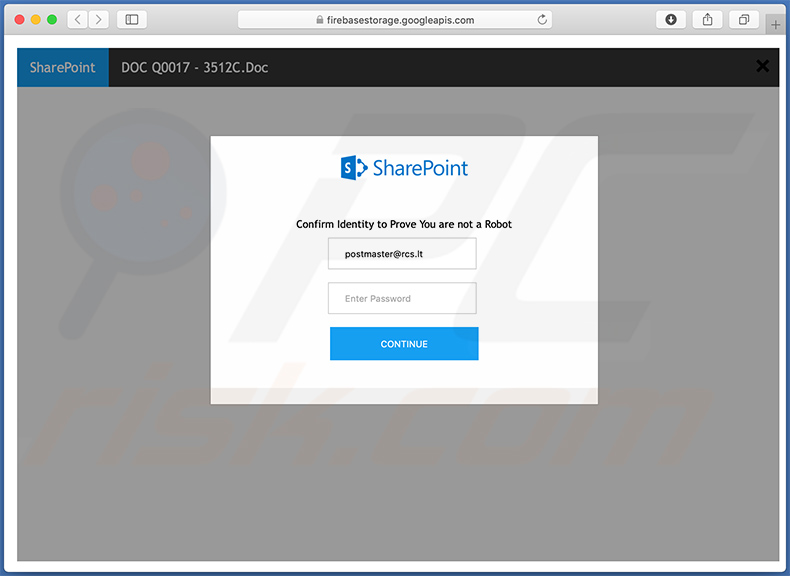
Yet another example of a spam email used for phishing purposes:
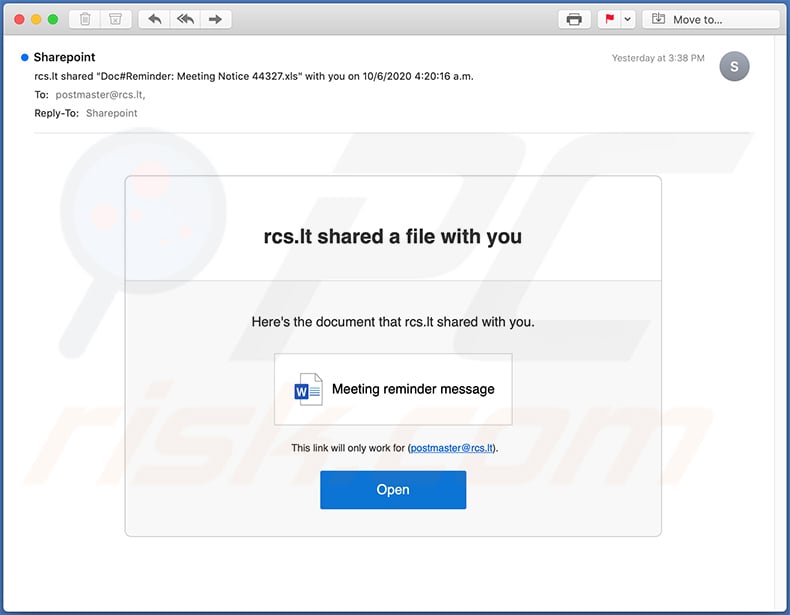
Text presented within:
Subject: - shared "Doc#Reminder: Meeting Notice 44327.xls" with you on 10/6/2020 4:20:16 a.m.
- shared a file with you
Here's the document that - shared with you.
Meeting reminder message
This link will only work for (-).
Open
Screenshot of a phishing site promoted via this email:
Yet another spam email used for phishing purposes:
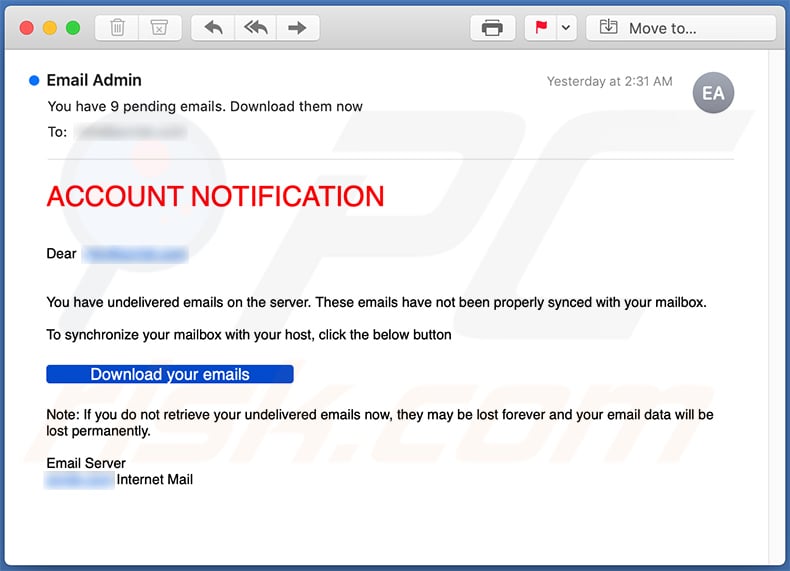
Text presented within:
Subject: You have 9 pending emails. Download them now
ACCOUNT NOTIFICATION
Dear -
You have undelivered emails on the server. These emails have not been properly synced with your mailbox.
To synchronize your mailbox with your host, click the below button
Download your emailsNote: If you do not retrieve your undelivered emails now, they may be lost forever and your email data will be lost permanently.
Email Server
- Internet Mail
Yet another spam email used for phishing purposes:
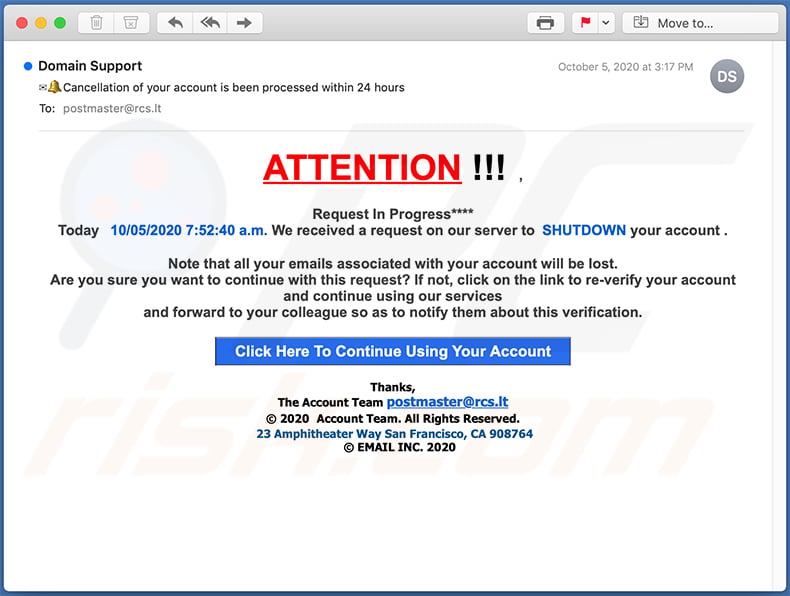
Text presented within:
Subject: Cancellation of your account is been processed within 24 hours
ATTENTION !!! ,
Request In Progress****
Today 10/05/2020 7:52:40 a.m. We received a request on our server to SHUTDOWN your account .
Note that all your emails associated with your account will be lost.
Are you sure you want to continue with this request? If not, click on the link to re-verify your account and continue using our services
and forward to your colleague so as to notify them about this verification.
Click Here To Continue Using Your AccountThanks,
The Account Team -
© 2020 Account Team. All Rights Reserved.
23 Amphitheater Way San Francisco, CA 908764
© EMAIL INC. 2020
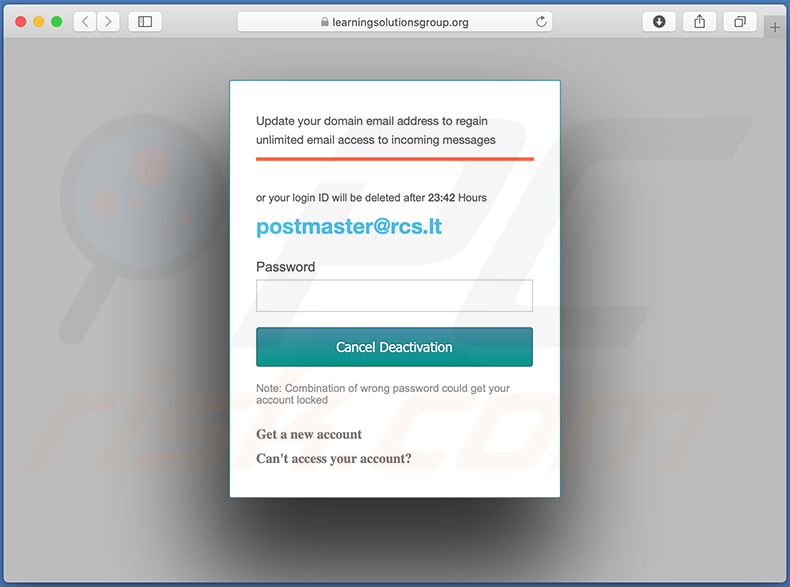
Screenshot of a phishing site (learningsolutionsgroup.org) promoted via this email:
Yet another spam email used for phishing purposes:
Text presented within:
Subject: Mobile Transaction 3831WT14991
GRUBHUB
Hello -,
Your order #50553536 is scheduled for delivery on Wednesday, September 23, at 8:00pm.
Your payment method will be charged for the amount of this order within the next 24 hours.
Please go to the order details page to manage your order.
View order detailsOrdered from
The Tipsy Taco & Cantina
Yet another spam email used for phishing purposes:
Text presented within:
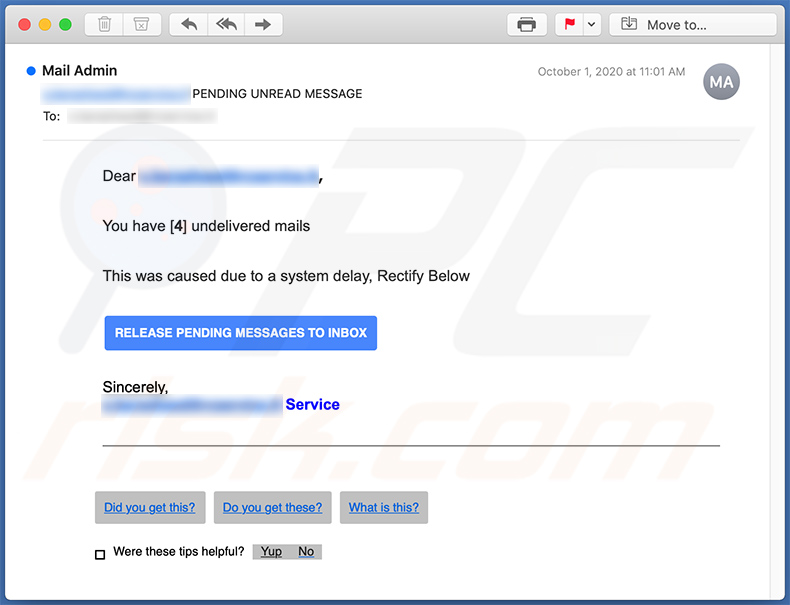
Subject: - PENDING UNREAD MESSAGE
Dear -,
You have [4] undelivered mails
This was caused due to a system delay, Rectify Below
RELEASE PENDING MESSAGES TO INBOX
Sincerely,
- ServiceDid you get this?
Create an answer with Did you get this?Do you get these?
What is this?
Were these tips helpful?YupNo
Yet another variant of a spam email used for phishing purposes:
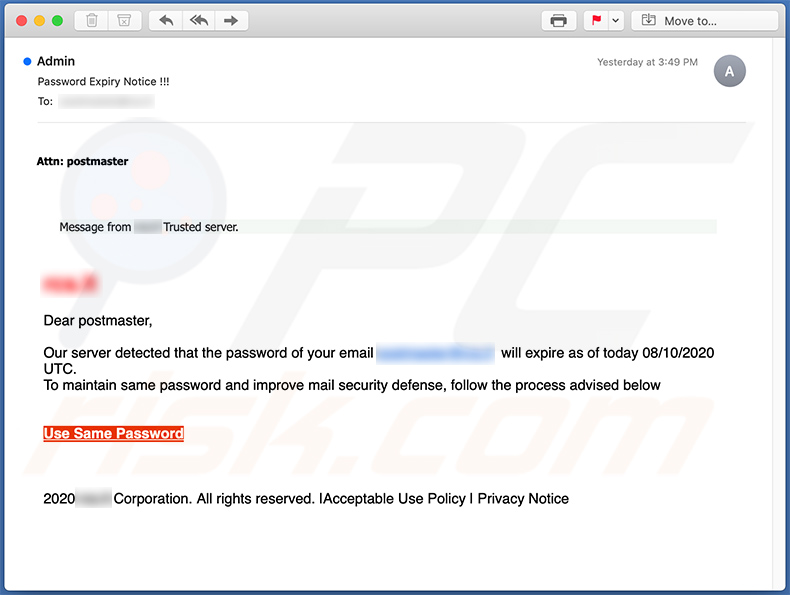
Text presented within:
Subject: Password Expiry Notice !!!
Attn: postmaster
Message from - Trusted server.
-Dear postmaster,
Our server detected that the password of your email p- will expire as of today 08/10/2020 UTC.
To maintain same password and improve mail security defense, follow the process advised belowUse Same Password
2020 - Corporation. All rights reserved. |Acceptable Use Policy | Privacy Notice
Yet another spam email used for phishing purposes:
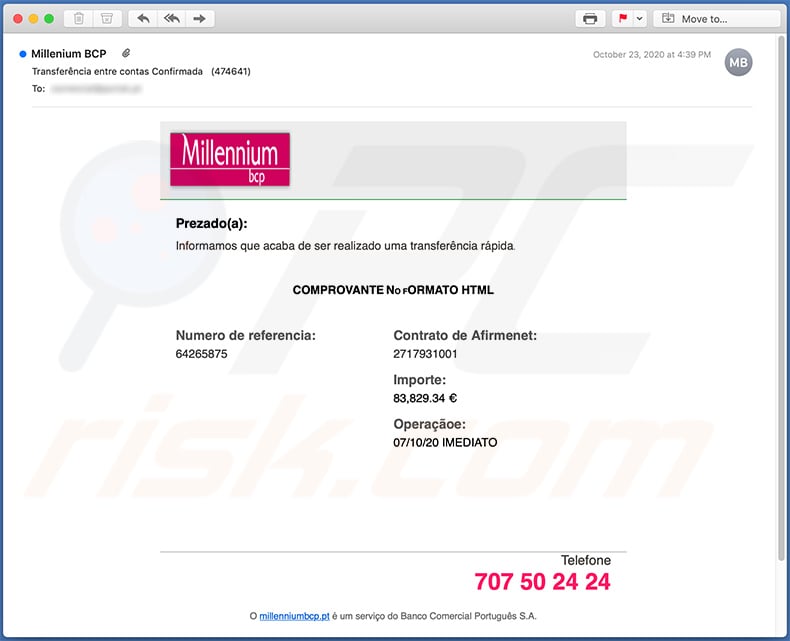
Text presented within:
Subject: Transferência entre contas Confirmada (474641)
Prezado(a):
Informamos que acaba de ser realizado uma transferência rápida.
COMPROVANTE NO FORMATO HTML
Numero de referencia:
64265875
Contrato de Afirmenet:
2717931001Importe:
83,829.34 €Operaçãoe:
07/10/20 IMEDIATOTelefone
707 50 24 24
O millenniumbcp.pt é um serviço do Banco Comercial Português S.A.
Yet another variant of a spam email used to promote a phishing site:
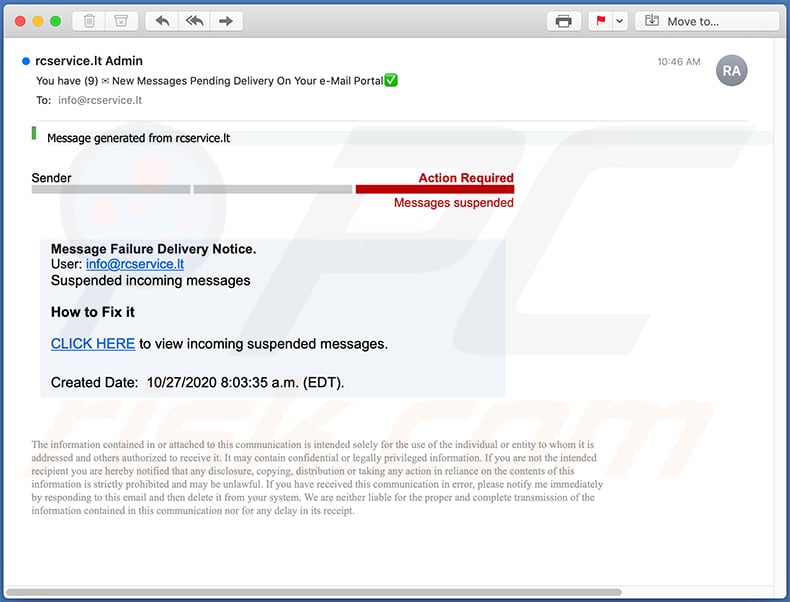
Text presented within:
Subject: You have (9) New Messages Pending Delivery On Your e-Mail Portal
Message generated from -
Action RequiredMessages suspended
Message Failure Delivery Notice.
User: -
Suspended incoming messagesHow to Fix it
CLICK HERE to view incoming suspended messages.
Created Date: 10/27/2020 8:03:35 a.m. (EDT).
The information contained in or attached to this communication is intended solely for the use of the individual or entity to whom it is addressed and others authorized to receive it. It may contain confidential or legally privileged information. If you are not the intended recipient you are hereby notified that any disclosure, copying, distribution or taking any action in reliance on the contents of this information is strictly prohibited and may be unlawful. If you have received this communication in error, please notify me immediately by responding to this email and then delete it from your system. We are neither liable for the proper and complete transmission of the information contained in this communication nor for any delay in its receipt.
Screenshot of the promoted website:
Yet another spam email used to promote a phishing website:
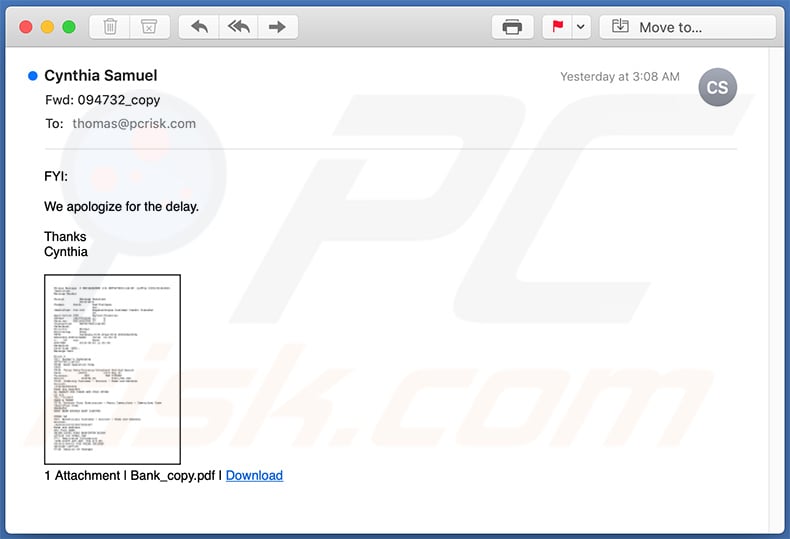
Text presented within:
Subject: Fwd: 094732_copy
FYI:
We apologize for the delay.
Thanks
Cynthia
1 Attachment | Bank_copy.pdf | Download
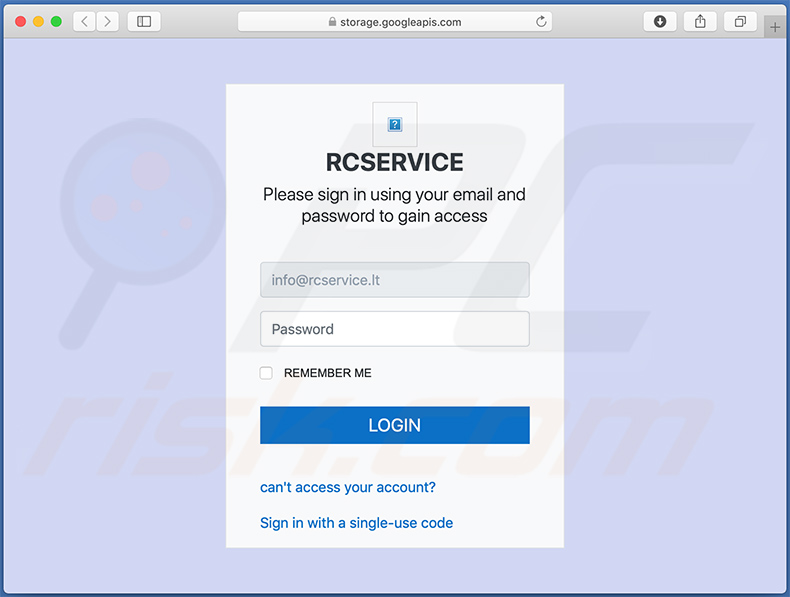
Screenshot of the promoted phishing site:
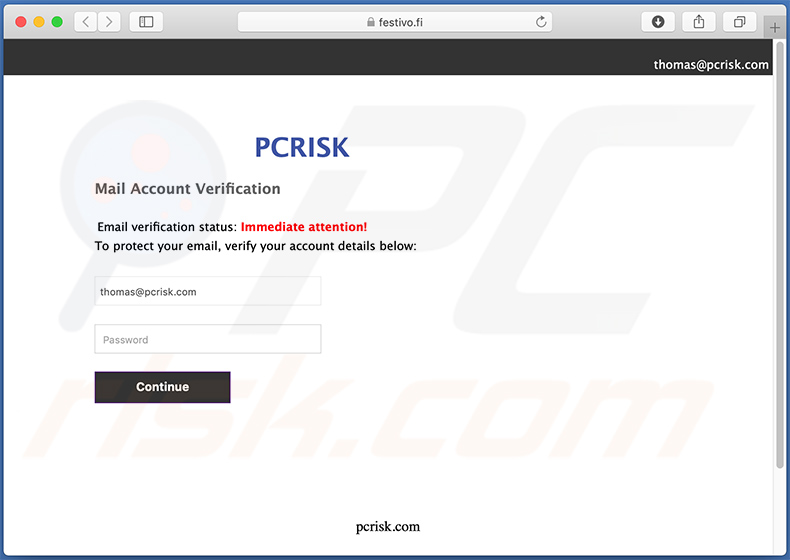
Yet another spam email used for phishing purposes:
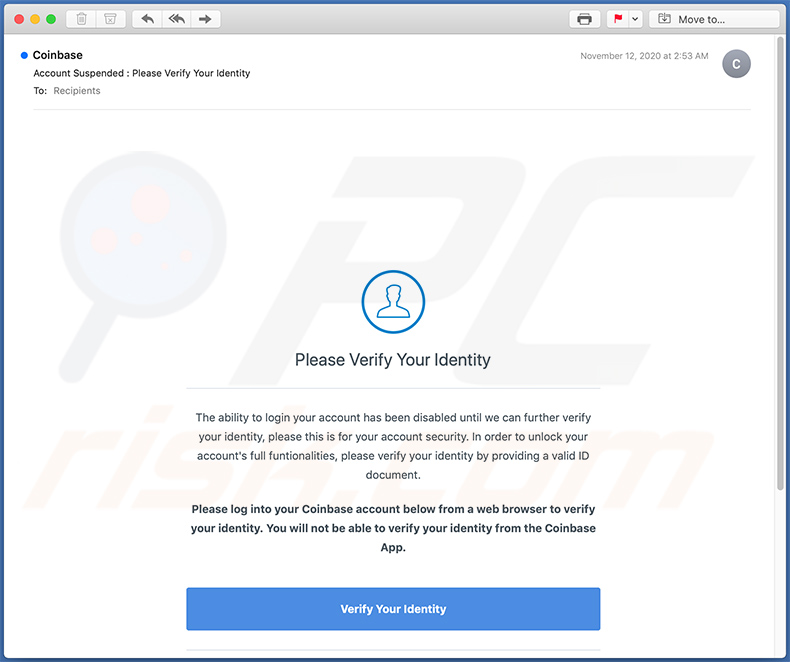
Text presented within:
Subject: Account Suspended : Please Verify Your Identity
Coinbase
Please Verify Your Identity
The ability to login your account has been disabled until we can further verify your identity, please this is for your account security. In order to unlock your account's full funtionalities, please verify your identity by providing a valid ID document.Please log into your Coinbase account below from a web browser to verify your identity. You will not be able to verify your identity from the Coinbase App.
Verify Your Identity
.
Want free Bitcoin? Invite your friends!
Terms of Service
© Coinbase 2020
Yet another example of a spam email used to promote a phishing website:
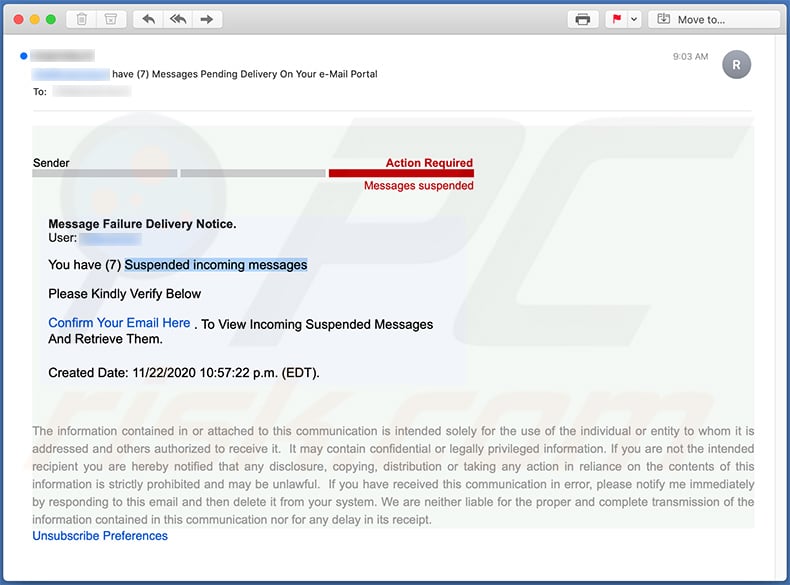
Text presented within:
Subject: ******** have (7) Messages Pending Delivery On Your e-Mail Portal
Sender
Action Required
Messages suspendedMessage Failure Delivery Notice.
User: ********You have (7) Suspended incoming messages
Please Kindly Verify Below
Confirm Your Email Here . To View Incoming Suspended Messages And Retrieve Them.
Created Date: 11/22/2020 10:57:22 p.m. (EDT).
The information contained in or attached to this communication is intended solely for the use of the individual or entity to whom it is addressed and others authorized to receive it. It may contain confidential or legally privileged information. If you are not the intended recipient you are hereby notified that any disclosure, copying, distribution or taking any action in reliance on the contents of this information is strictly prohibited and may be unlawful. If you have received this communication in error, please notify me immediately by responding to this email and then delete it from your system. We are neither liable for the proper and complete transmission of the information contained in this communication nor for any delay in its receipt.
Unsubscribe Preferences
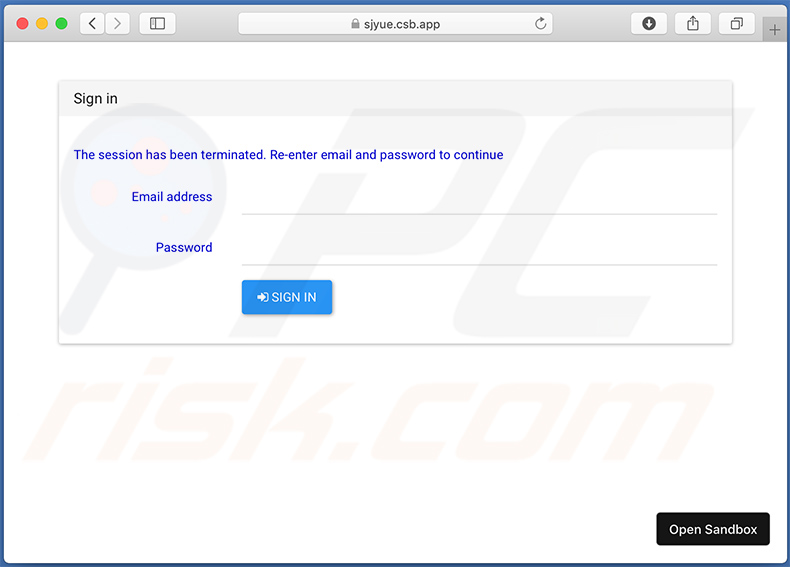
Screenshot of the promoted phishing site:
Yet another example of a spam email used to promote a phishing website (fake Microsoft Outlook login page):
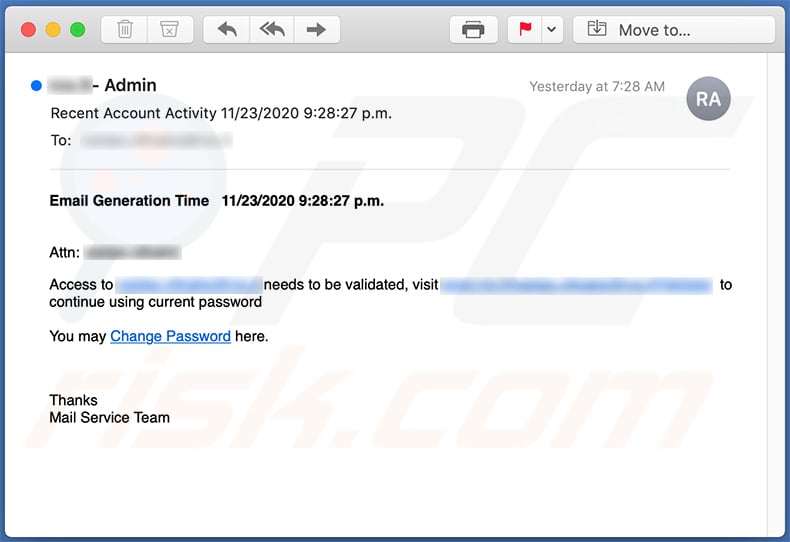
Text presented within:
Subject: Recent Account Activity 11/23/2020 9:28:27 p.m.
Email Generation Time 11/23/2020 9:28:27 p.m.Attn: ********
Access to ******** needs to be validated, visit ******************************** to continue using current password
You may Change Password here.
Thanks
Mail Service Team
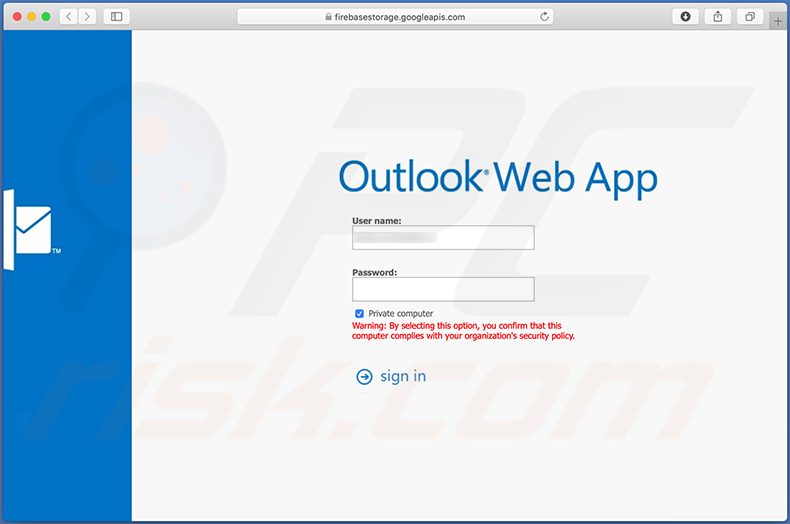
Screenshot of the promoted website:
Yet another spam email used to promote a phishing website:
Text presented within:
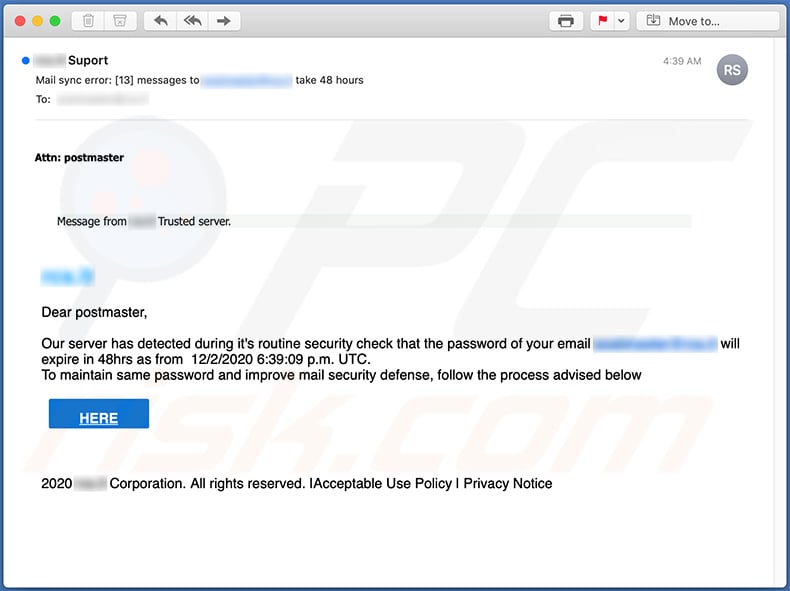
Subject: Mail sync error: [13] messages to ******** take 48 hours
Attn: postmaster
Message from ******** Trusted server.
********Dear postmaster,
Our server has detected during it's routine security check that the password of your email ******** will expire in 48hrs as from 12/2/2020 6:39:09 p.m. UTC.
To maintain same password and improve mail security defense, follow the process advised belowHERE
2020 ******** Corporation. All rights reserved. |Acceptable Use Policy | Privacy Notice
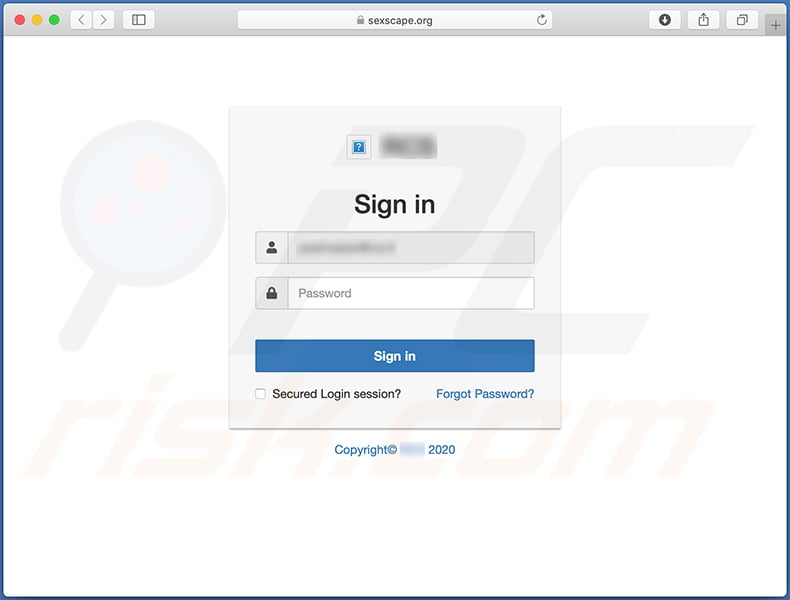
Screenshot of the promoted phishing site:
Yet another variant of a spam email used for phishing purposes:
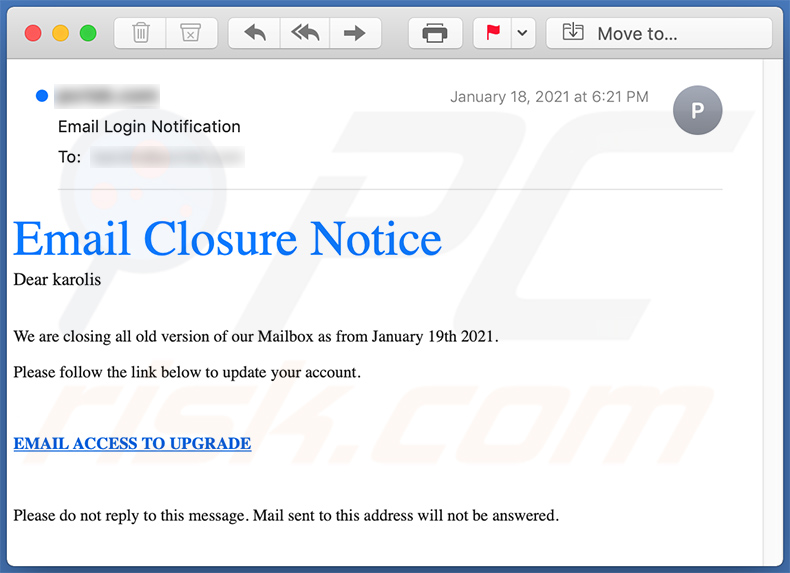
Text presented within:
Subject: Email Login Notification
Email Closure Notice
Dear -We are closing all old version of our Mailbox as from January 19th 2021.
Please follow the link below to update your account.
EMAIL ACCESS TO UPGRADE
Please do not reply to this message. Mail sent to this address will not be answered.
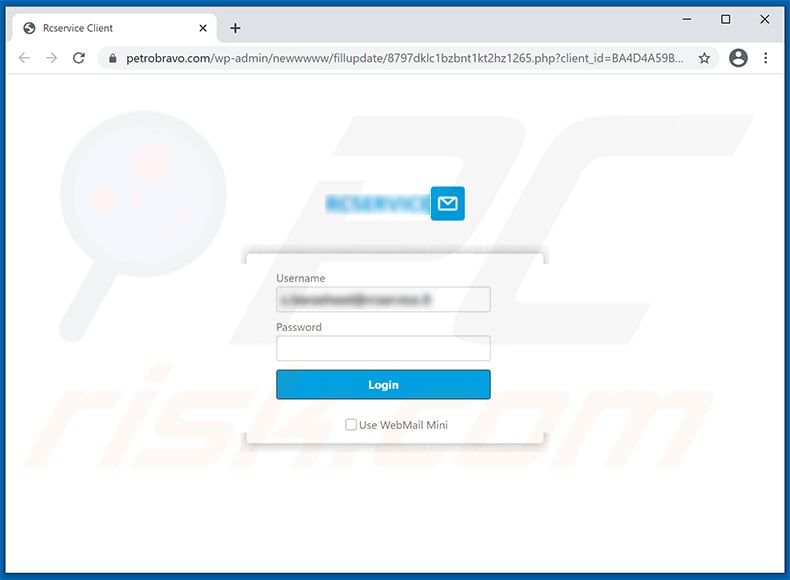
Phishing website promoted via this email:
Yet another example of a spam email used for phishing purposes:
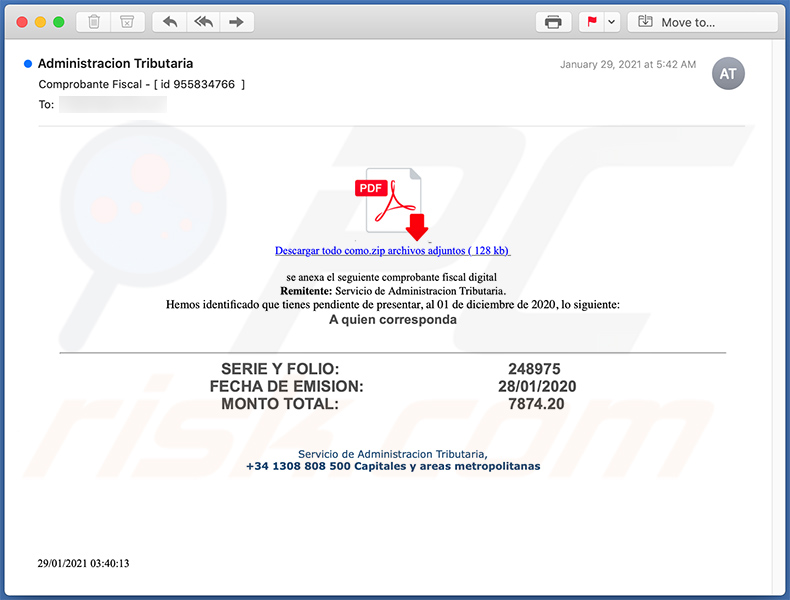
Text presented within:
Subject: Comprobante Fiscal - [ id 955834766 ]
01 Resultado de imagem para pdf
Descargar todo como.zip archivos adjuntos ( 128 kb)se anexa el seguiente comprobante fiscal digital
Remitente: Servicio de Administracion Tributaria.
Hemos identificado que tienes pendiente de presentar, al 01 de diciembre de 2020, lo siguiente:
A quien correspondaSERIE Y FOLIO: 248975
FECHA DE EMISION: 28/01/2020
MONTO TOTAL: 7874.20
Servicio de Administracion Tributaria,
+34 1308 808 500 Capitales y areas metropolitanas29/01/2021 03:40:13
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Email Credentials Phishing spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Your email address may have been leaked and used in a campaign operated by scammers. Emails like this one are not personal - they are sent to all addresses in databases that scammers have.
I have provided my personal information when tricked by this email, what should I do?
If you have provided your password, change all passwords as soon as possible (especially if scammers can use the provided password to access other accounts). If you have provided credit card details, ID card information, or other details, contact your bank or other corresponding institutions/authorities.
I have downloaded and opened a malicious file attached to this email, is my computer infected?
If that was a document (e.g., a Microsoft Office or PDF document), your computer might not be infected. Documents do not infect computers until macros commands are enabled (or other actions are performed). However, if the file attached to an email was executable, your computer may already be infected.
Was my computer actually hacked and does the sender have any information?
It is unlikely that your computer has been hacked (or infected). It is common for scammers to use old passwords retrieved from databases containing leaked data.
How did cyber criminals get my email password?
Cybercriminals may have gained access to your email after a data breach (if the information stolen from a page that you have registered to contained login credentials). You may also have provided your password on some phishing pages.
I have read the email but did not open a malicious attachment, is my computer infected?
No, reading emails is harmless. Computers cannot be infected without opening links or attachments.
Will Combo Cleaner remove malware infections that were present in email attachment?
Yes, Combo Cleaner can detect and eliminate almost all known malware. It is required to scan the operating system using a full scan to remove high-end malware. Usually, malware of this kind hides deep in the system to avoid detection.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate

▼ Show Discussion