Prevent being scammed by the 'On This Day I Hacked Your OS' email
Phishing/ScamAlso Known As: On This Day I Hacked Your OS spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is "On this day I hacked your OS"?
"On this day I hacked your OS" is an email scam, which uses a blackmailing tactic called "sextortion" - it extorts money from users via threats to expose evidence of their 'sexual activity'. This scam claims to have obtained audio and visual content via the device's camera and microphone.
It informs users that this evidence will be sent to all of their contacts, unless a certain sum in transferred to the account of cyber criminals behind the rogue email. Note that these claims are false and no such compromising material exists. Emails of this type should be ignored.
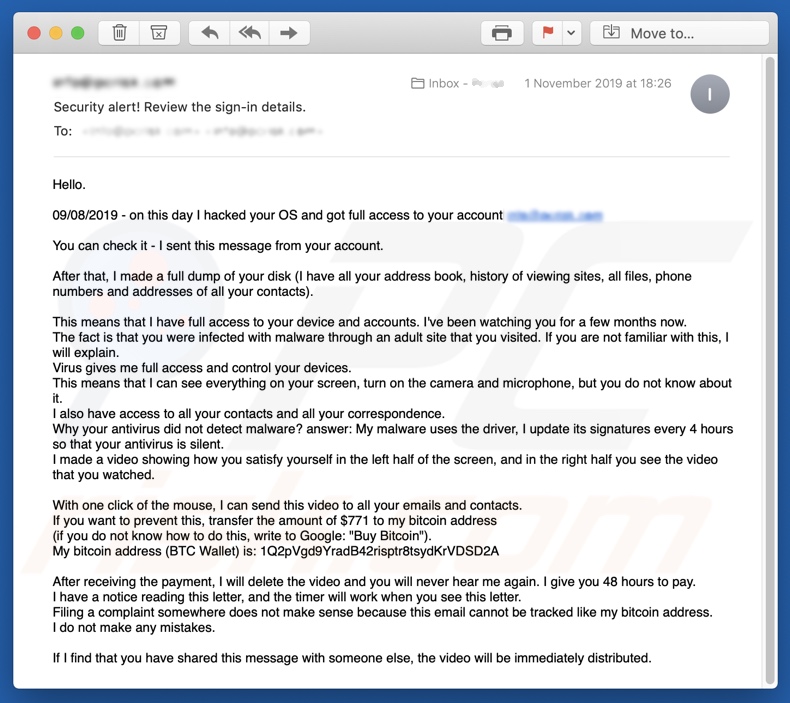
The email entitled "Security alert! Review the sign-in details." states that the users' OS (Operating Systems) have been hacked and their email accounts are within the full control of cyber criminals. They claim to have access to users' address books, browsing history, file inventory, contacts' email addresses and telephone numbers.
Furthermore, users are informed that they have been under observation for several months due to an infection from a compromised adult-site, which they have visited previously. The virus then supposedly gave the criminals full access and control of the device, including webcam and microphone.
The anti-virus software was unable to detect this infection, since the malware uses a driver and its signature is updated every four hours. Through this alleged hacking, video/audio and screen recordings were made of users "satisfying" themselves.
The cyber criminals demand 771 USD to be transferred to their Bitcoin crypto-wallet, otherwise this humiliating material will be sent to all users' contacts. If payment is not made within 48 hours, the compromising video and content watched during the recording will apparently be sent to their contacts.
Users are promised that once the transaction is made, the video will be deleted and they will not be disturbed by these individuals again. The 48-hour countdown starts from the moment the email is opened. The message informs users that filing any type of complaint will not aid them, since the email and Bitcoin addresses cannot be traced.
The message ends with a warning informing users not to share this email with anyone, as this will result in immediate distribution of the compromising video. As mentioned, "On this day I hacked your OS" is a scam and none of the alleged content exists.
Additionally, the cyber criminals behind this scam have not infected your system - no evidence of sexual activity could have been acquired and the device's integrity has not been compromised. Never trust emails such as "On this day I hacked your OS" and simply ignore them.
| Name | "On this day I hacked your OS" email spam campaign. |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Cyber criminals claim to have infected the device with malware, which allowed them to record compromising audio/video. They threaten to share this content with the victim's contacts, unless a payment is made within the given time frame. |
| Cyber Criminal Cryptowallet Address (Bitcoin) | 17Hni3UPjcS1BTKUwXFkJXoyF8oHwk7MiC, 1Q2pVgd9YradB42risptr8tsydKrVDSD2A, 17fjtBvkQCMJduzZQB4GZtxJvxgXrceSMt, 1D1CJ5msCAzvc838x5ZmfNWVv6d94U5grH |
| Ransom Size | $771 in Bitcoin |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Scam emails are distributed using massive scale spam campaigns. Various tactics can be employed, not just "sextortion".
They range from "import" alerts to "prize" announcements. "Hacker Who Has Access To Your Operating System", "Your Device Was Infected With My Private Malware", and "WannaCry Hacker Group" are a few examples of other scams similar to "On this day I hacked your OS".
Typically, they involve threats to distribute compromising videos/screenshots of the victim, unless ransoms are paid. Cyber criminals prefer these payments to be made in digital currencies (e.g. cryptocurrencies, pre-paid vouchers, etc.), as these transactions are difficult/impossible to trace.
Note that the functions of these emails can differ - they can be used to proliferate ransomware and other malware.
How do spam campaigns infect computers?
Infections via spam campaigns are caused by opening attached files found within deceptive emails. These are often marked as "official", "important", "urgent" or similarly highlighted as priority mail. The infectious attachments come in various formats, such as archive (ZIP, RAR) and executable (.exe, .run) files, Microsoft Office and PDF documents, JavaScript, etc.
When these files are run, executed or otherwise opened, they begin downloading/installing malicious software. For example, MS Office documents ask users to enable macro commands (to enable editing). If allowed, they are triggered to infect systems.
How to avoid installation of malware
Do not read suspicious/irrelevant emails, especially those received from unknown senders. Attachments found in these messages must never be opened, since the files are the source of potential infections.
Use Microsoft Office versions released after year 2010, as they have a "Protected View" mode, which prevents dangerous documents from downloading/installing malware.
Download only from official and verified sources. P2P sharing networks (BitTorrent, eMule, Gnutella, etc.), free file-hosting websites, third party downloaders and similar channels are classed as untrustworthy and should not be used. Untrusted download sources are more likely to offer content bundled with malicious software.
Programs should be activated and updated using functions/tools provided by genuine developers. Illegal activation tools ("cracks") and third party updaters are high-risk. Have a reputable anti-virus/anti-spyware suite installed and kept up-to-date. Use this software to perform regular system scans and for the removal of detected threats.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "On this day I hacked your OS" email message:
Hello.
09/08/2019 - on this day I hacked your OS and got full access to your account ************
You can check it - I sent this message from your account.
After that, I made a full dump of your disk (I have all your address book, history of viewing sites, all files, phone numbers and addresses of all your contacts).
This means that I have full access to your device and accounts. I've been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited. If you are not familiar with this, I will explain.
Virus gives me full access and control your devices.
This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it.
I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware? answer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent.
I made a video showing how you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.With one click of the mouse, I can send this video to all your emails and contacts.
If you want to prevent this, transfer the amount of $771 to my bitcoin address
(if you do not know how to do this, write to Google: "Buy Bitcoin").
My bitcoin address (BTC Wallet) is: 1Q2pVgd9YradB42risptr8tsydKrVDSD2A, 17fjtBvkQCMJduzZQB4GZtxJvxgXrceSMt, 1D1CJ5msCAzvc838x5ZmfNWVv6d94U5grHAfter receiving the payment, I will delete the video and you will never hear me again. I give you 48 hours to pay.
I have a notice reading this letter, and the timer will work when you see this letter.
Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address.
I do not make any mistakes.If I find that you have shared this message with someone else, the video will be immediately distributed.
Appearance of a Polish version of "On This Day I Hacked Your OS" email scam:
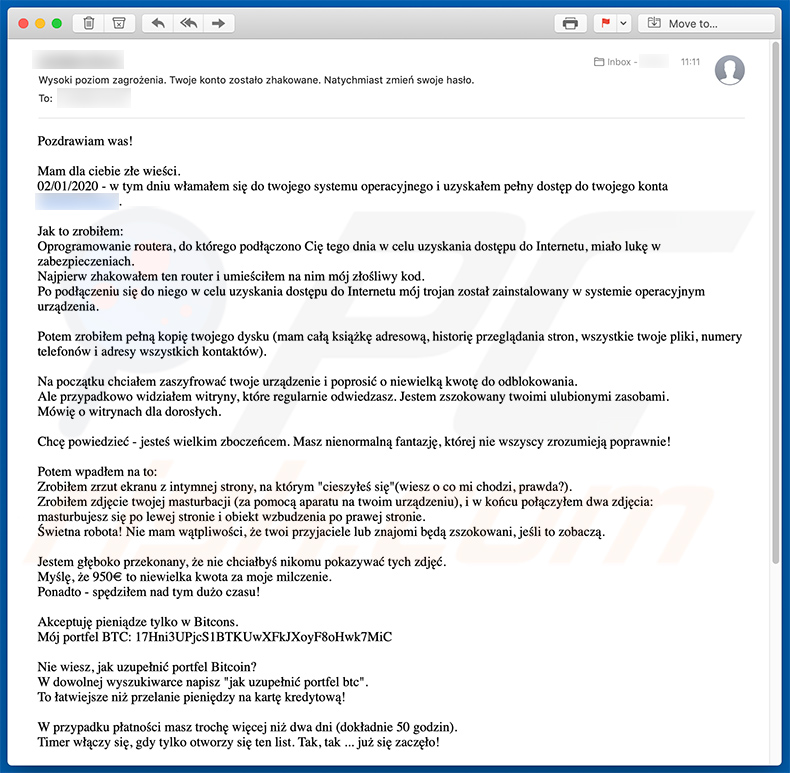
Text presented within this email:
Pozdrawiam was!
Mam dla ciebie złe wieści.
02/01/2020 - w tym dniu włamałem się do twojego systemu operacyjnego i uzyskałem pełny dostęp do twojego konta ****.Jak to zrobiłem:
Oprogramowanie routera, do którego podłączono Cię tego dnia w celu uzyskania dostępu do Internetu, miało lukę w zabezpieczeniach.
Najpierw zhakowałem ten router i umieściłem na nim mój złośliwy kod.
Po podłączeniu się do niego w celu uzyskania dostępu do Internetu mój trojan został zainstalowany w systemie operacyjnym urządzenia.Potem zrobiłem pełną kopię twojego dysku (mam całą książkę adresową, historię przeglądania stron, wszystkie twoje pliki, numery telefonów i adresy wszystkich kontaktów).
Na początku chciałem zaszyfrować twoje urządzenie i poprosić o niewielką kwotę do odblokowania.
Ale przypadkowo widziałem witryny, które regularnie odwiedzasz. Jestem zszokowany twoimi ulubionymi zasobami.
Mówię o witrynach dla dorosłych.Chcę powiedzieć - jesteś wielkim zboczeńcem. Masz nienormalną fantazję, której nie wszyscy zrozumieją poprawnie!
Potem wpadłem na to:
Zrobiłem zrzut ekranu z intymnej strony, na którym "cieszyłeś się"(wiesz o co mi chodzi, prawda?).
Zrobiłem zdjęcie twojej masturbacji (za pomocą aparatu na twoim urządzeniu), i w końcu połączyłem dwa zdjęcia:
masturbujesz się po lewej stronie i obiekt wzbudzenia po prawej stronie.
Świetna robota! Nie mam wątpliwości, że twoi przyjaciele lub znajomi będą zszokowani, jeśli to zobaczą.Jestem głęboko przekonany, że nie chciałbyś nikomu pokazywać tych zdjęć.
Myślę, że 950€ to niewielka kwota za moje milczenie.
Ponadto - spędziłem nad tym dużo czasu!Akceptuję pieniądze tylko w Bitcons.
Mój portfel BTC: 17Hni3UPjcS1BTKUwXFkJXoyF8oHwk7MiCNie wiesz, jak uzupełnić portfel Bitcoin?
W dowolnej wyszukiwarce napisz "jak uzupełnić portfel btc".
To łatwiejsze niż przelanie pieniędzy na kartę kredytową!W przypadku płatności masz trochę więcej niż dwa dni (dokładnie 50 godzin).
Timer włączy się, gdy tylko otworzy się ten list. Tak, tak ... już się zaczęło!Po dokonaniu płatności natychmiast zniszczę mojego wirusa i usuwa wszystkie pliki, które Cię narażą, a zapomnisz o tym nieprzyjemnym incydencie.
Pamiętaj, że jeśli nie otrzymam od ciebie powyższej kwoty, twoje urządzenie zostanie zablokowane, a wszystkie twoje kontakty otrzymają zdjęcia z twoją masturbacją.Chcę, abyście zrozumieli powagę tej sytuacji:
- Nie próbuj znaleźć i zniszczyć mojego wirusa! (Wszystkie twoje dane są już przesłane na serwer zdalny).
- Nie próbuj się ze mną kontaktować (nie jest to możliwe, wysłałem ci ten e-mail z twojego zhakowanego konta).
- Różne usługi bezpieczeństwa nie pomogą, formatowanie dysku lub niszczenie urządzenia również nie pomoże, ponieważ dane są już na serwerze zdalnym.P.S. Gwarantuję ci, że nie będę ci przeszkadzał po wypłacie, ponieważ nie jesteś jedyną osobą, z którą "pracuję".
To jest kod honoru hakera.Od tej pory radzę korzystać z dobrych programów antywirusowych i aktualizować je regularnie (kilka razy dziennie)!
Nie bądź na mnie zły, każdy ma własną pracę.
Do widzenia
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is On This Day I Hacked Your OS spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion