Avoid the "We Have Hacked Your Website" email scam
Phishing/ScamAlso Known As: We Have Hacked Your Website spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the "We Have Hacked Your Website" email?
"We Have Hacked Your Website" is a scam email claiming that the website of the recipient's company has been hacked. The scammers state that they have obtained the databases and will leak them, unless a certain sum is paid within the given time frame.
This message is a scam and the information provided is false. Therefore, you are advised to simply ignore the "We Have Hacked Your Website" email.
More about this email scam
The email states that the recipient's company website has supposedly been hacked and the databases have been exfiltrated to an offshore server. The message instructs users to forward this email to someone who has the authority to make important decisions within the company.
Unless the listed demands are met, the email claims that the company's reputation will be damaged irreparably. A ransom to the equivalent of US$1500 (USD) in the Bitcoin cryptocurrency must be paid within five days, otherwise the information will supposedly be sold to the highest bidder.
Additionally, if the data contains any saved emails of customers/associates, they will be notified of the leak. The site will also be de-indexed. I.e., indexes will be removed from search engines and will thus not appear in any queries. The message states that the ransom is non-negotiable and recipients should not even try to respond, as they will not receive a reply.
To summarize, the "We Have Hacked Your Website" email is a scam and none of the threats it makes can actually be carried out by the scammers. These individuals have not compromised any websites associated with the recipients or stolen vulnerable information. Therefore, do not trust this message or meet its demands.
| Name | We Have Hacked Your Website Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Email claims recipient's company website has been hacked and its databases have been extracted. |
| Ransom Amount | Equivalent of US$1500 in the Bitcoin cryptocurrency. |
| Cyber Criminal Cryptowallet Addresses | 1JToMSCtc4nW3fNDUL4xV9QYqmyKJEYMdj, 3GGQxApV9d6U6CVPeXPSCMYraJdCnmz5u1, 36nmXWJ2JBTUib5UeGeds5yDT5WYm6n6Cs, 3BarXz9obgVwuLpoXhvQ4nh2mGc1pQKtoq, bc1qz0hwyvdrq5xvfwcm9m5eg7kjktvsux4r058v6g, 33Mw16wNgvQZHzmS87MCTJ3ZAJBowre1rd, bc1qmtvdfufnae8w6jq7jxkh5lw8njk2gksyh0xh0n, bc1qn7l003h3hrqugtm4d0qqzhg7pgvfc3888mpc4l |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Emails of this kind in general
Deceptive/Scam emails are sent by the thousand during large scale operations - these are called "spam campaigns". "Infect Your Family With CoronaVirus", "Microsoft Email Scam", "I infected your computer with my private trojan" and "RedCross Email Scam" are some examples of such campaigns.
The messages are usually presented as "important", "urgent", "priority", "official" and similar. The emails can even be disguised as mail from legitimate organizations, institutions, companies, service providers, etc. These messages use social engineering and scare tactics to trick recipients into performing certain actions.
For example, making monetary transactions (e.g. paying ransoms, fake fees and bills, etc.), revealing personal information (e.g. names, addresses, telephone numbers, emails, banking account and/or credit card details, etc.), opening infectious files and so on.
Regardless of the claims, requests and threats these emails make, their purpose is identical: to generate revenue for the scammers/cyber criminals behind them.
How do spam campaigns infect computers?
Systems are infected through dangerous files sent during spam campaigns. These files are attached to or linked inside deceptive/scam emails. Malicious files can be in various formats such as Microsoft Office or PDF documents, archive (RAR, ZIP, etc.) and executable (.exe, .run, etc.) files, JavaScript, etc.
When they are executed, run or otherwise opened, the infection process starts. I.e., when opened, they begin downloading/installing malware. For example, Microsoft Office documents initiate these processes by executing malicious macro commands.
Once opened, MS Office documents ask users to enable macro commands (i.e., to enable editing) - doing so for infectious documents leads to an infection.
How to avoid installation of malware
You are strongly advised not to open suspicious or irrelevant emails, especially those received from suspect/unknown senders. Any attachments or links found in dubious messages must not be opened, as this can result in high-risk system infection. Additionally, it is important to use Microsoft Office versions released after 2010.
Newer versions have "Protected View" mode, which prevents infection processes from being triggered when a malicious document is opened.
As well as spam campaigns, malware is also distributed using untrusted download channels (unofficial and free file-hosting websites, Peer-to-Peer sharing networks and other third party downloaders), illegal activation tools ("cracks") and fake updaters.
Therefore, use only verified download sources and activate and update products with tools/functions provided by legitimate developers. To ensure device and user safety, it is paramount to have reputable anti-virus/anti-spyware software installed and kept up to date.
Furthermore, these programs should be used to run regular system scans and to remove detected threats. If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
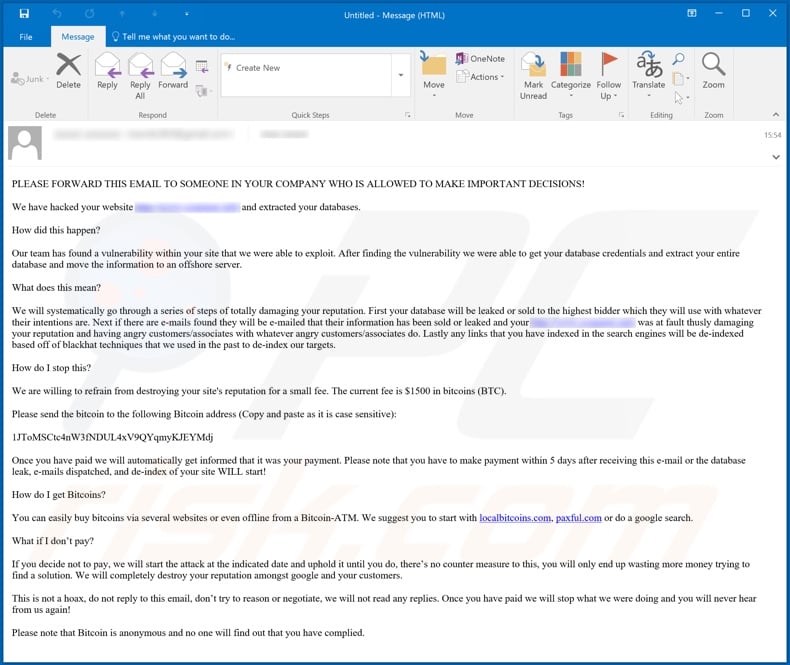
Text presented in the "We Have Hacked Your Website" email message:
PLEASE FORWARD THIS EMAIL TO SOMEONE IN YOUR COMPANY WHO IS ALLOWED TO MAKE IMPORTANT DECISIONS!
We have hacked your website - and extracted your databases.
How did this happen?
Our team has found a vulnerability within your site that we were able to exploit. After finding the vulnerability we were able to get your database credentials and extract your entire database and move the information to an offshore server.
What does this mean?
We will systematically go through a series of steps of totally damaging your reputation. First your database will be leaked or sold to the highest bidder which they will use with whatever their intentions are. Next if there are e-mails found they will be e-mailed that their information has been sold or leaked and your - was at fault thusly damaging your reputation and having angry customers/associates with whatever angry customers/associates do. Lastly any links that you have indexed in the search engines will be de-indexed based off of blackhat techniques that we used in the past to de-index our targets.
How do I stop this?
We are willing to refrain from destroying your site's reputation for a small fee. The current fee is $1500 in bitcoins (BTC).
Please send the bitcoin to the following Bitcoin address (Copy and paste as it is case sensitive):
1JToMSCtc4nW3fNDUL4xV9QYqmyKJEYMdj
Once you have paid we will automatically get informed that it was your payment. Please note that you have to make payment within 5 days after receiving this e-mail or the database leak, e-mails dispatched, and de-index of your site WILL start!
How do I get Bitcoins?
You can easily buy bitcoins via several websites or even offline from a Bitcoin-ATM. We suggest you to start with localbitcoins.com, paxful.com or do a google search.
What if I don’t pay?
If you decide not to pay, we will start the attack at the indicated date and uphold it until you do, there’s no counter measure to this, you will only end up wasting more money trying to find a solution. We will completely destroy your reputation amongst google and your customers.
This is not a hoax, do not reply to this email, don’t try to reason or negotiate, we will not read any replies. Once you have paid we will stop what we were doing and you will never hear from us again!
Please note that Bitcoin is anonymous and no one will find out that you have complied.
Another variant of this scam:
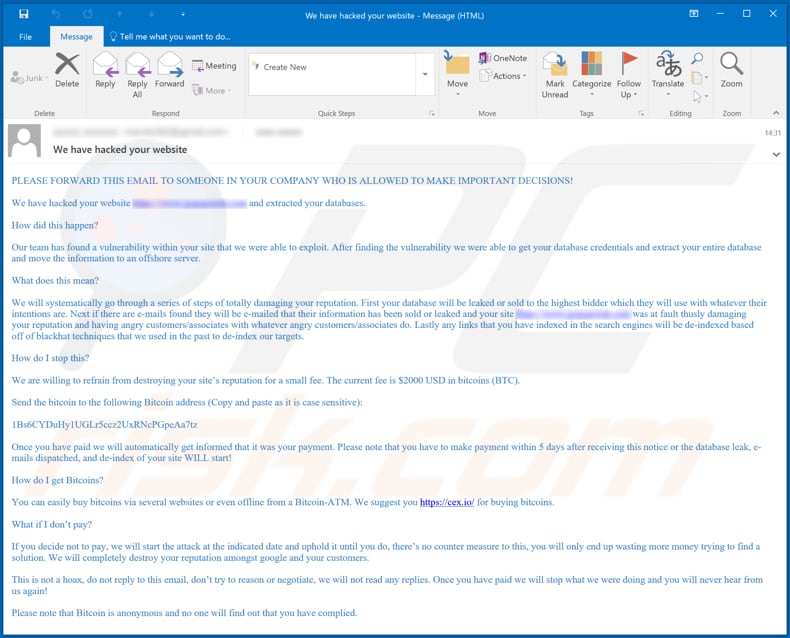
Text in this scam:
PLEASE FORWARD THIS EMAIL TO SOMEONE IN YOUR COMPANY WHO IS ALLOWED TO MAKE IMPORTANT DECISIONS!
We have hacked your website - and extracted your databases.
How did this happen?
Our team has found a vulnerability within your site that we were able to exploit. After finding the vulnerability we were able to get your database credentials and extract your entire database and move the information to an offshore server.
What does this mean?
We will systematically go through a series of steps of totally damaging your reputation. First your database will be leaked or sold to the highest bidder which they will use with whatever their intentions are. Next if there are e-mails found they will be e-mailed that their information has been sold or leaked and your site - was at fault thusly damaging your reputation and having angry customers/associates with whatever angry customers/associates do. Lastly any links that you have indexed in the search engines will be de-indexed based off of blackhat techniques that we used in the past to de-index our targets.
How do I stop this?
We are willing to refrain from destroying your site’s reputation for a small fee. The current fee is $2000 USD in bitcoins (BTC).
Send the bitcoin to the following Bitcoin address (Copy and paste as it is case sensitive):
1Bs6CYDuHy1UGLr5ccz2UxRNcPGpeAa7tz
Once you have paid we will automatically get informed that it was your payment. Please note that you have to make payment within 5 days after receiving this notice or the database leak, e-mails dispatched, and de-index of your site WILL start!
How do I get Bitcoins?
You can easily buy bitcoins via several websites or even offline from a Bitcoin-ATM. We suggest you hxxps://cex.io/ for buying bitcoins.
What if I don’t pay?
If you decide not to pay, we will start the attack at the indicated date and uphold it until you do, there’s no counter measure to this, you will only end up wasting more money trying to find a solution. We will completely destroy your reputation amongst google and your customers.
This is not a hoax, do not reply to this email, don’t try to reason or negotiate, we will not read any replies. Once you have paid we will stop what we were doing and you will never hear from us again!
Please note that Bitcoin is anonymous and no one will find out that you have complied.
Yet another example of "We Have Hacked Your Website" scam email:
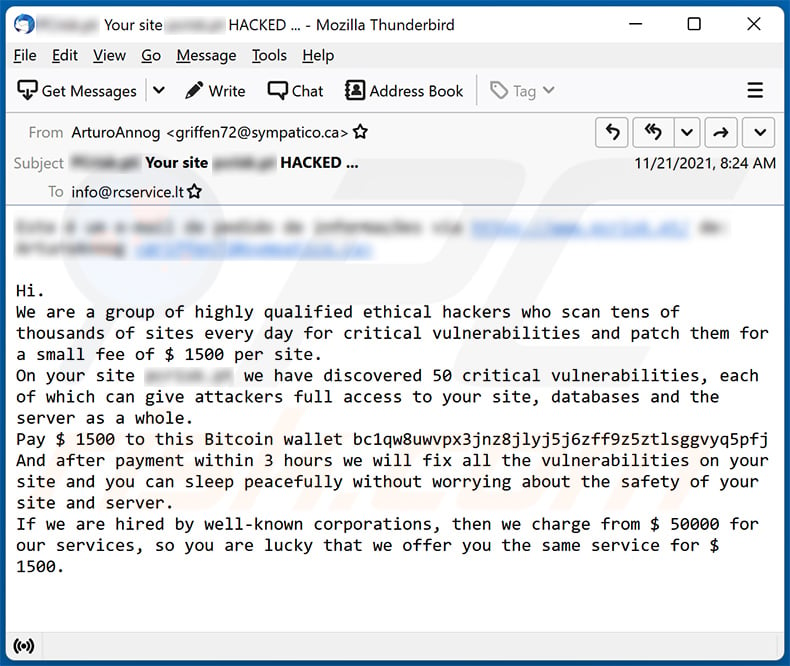
Text presented within:
Subject: Your site - HACKED ...
Hi.
We are a group of highly qualified ethical hackers who scan tens of thousands of sites every day for critical vulnerabilities and patch them for a small fee of $ 1500 per site.
On your site - we have discovered 50 critical vulnerabilities, each of which can give attackers full access to your site, databases and the server as a whole.
Pay $ 1500 to this Bitcoin wallet bc1qw8uwvpx3jnz8jlyj5j6zff9z5ztlsggvyq5pfj
And after payment within 3 hours we will fix all the vulnerabilities on your site and you can sleep peacefully without worrying about the safety of your site and server.
If we are hired by well-known corporations, then we charge from $ 50000 for our services, so you are lucky that we offer you the same service for $ 1500.
A Polish variant of "We Have Hacked Your Website" scam campaign:
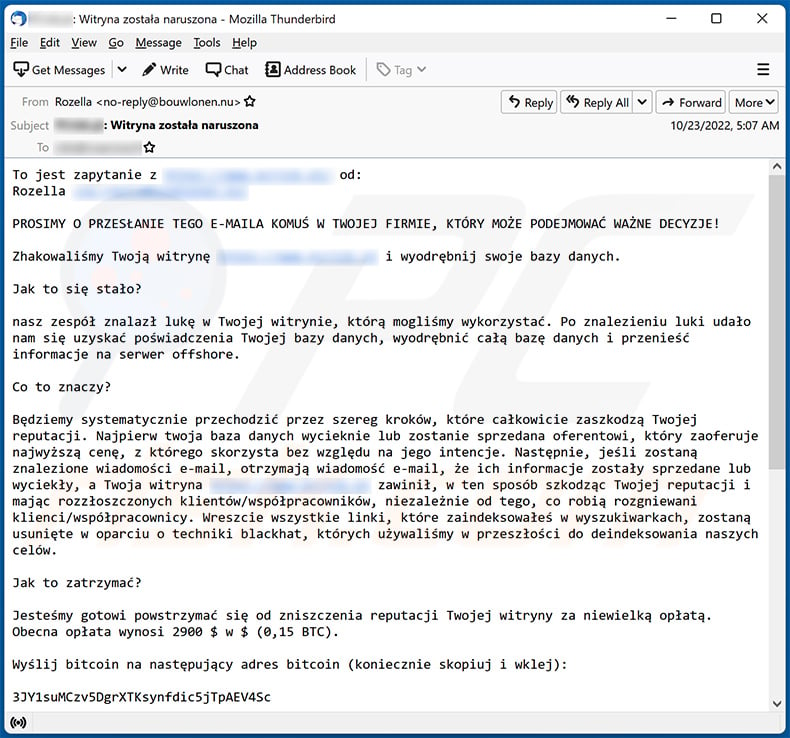
Text presented within:
Subject: ********: Witryna została naruszona
PROSIMY O PRZESŁANIE TEGO E-MAILA KOMUŚ W TWOJEJ FIRMIE, KTÓRY MOŻE PODEJMOWAĆ WAŻNE DECYZJE!
Zhakowaliśmy Twoją witrynę ******** i wyodrębnij swoje bazy danych.
Jak to się stało?
nasz zespół znalazł lukę w Twojej witrynie, którą mogliśmy wykorzystać. Po znalezieniu luki udało nam się uzyskać poświadczenia Twojej bazy danych, wyodrębnić całą bazę danych i przenieść informacje na serwer offshore.
Co to znaczy?
Będziemy systematycznie przechodzić przez szereg kroków, które całkowicie zaszkodzą Twojej reputacji. Najpierw twoja baza danych wycieknie lub zostanie sprzedana oferentowi, który zaoferuje najwyższą cenę, z którego skorzysta bez względu na jego intencje. Następnie, jeśli zostaną znalezione wiadomości e-mail, otrzymają wiadomość e-mail, że ich informacje zostały sprzedane lub wyciekły, a Twoja witryna ******** zawinił, w ten sposób szkodząc Twojej reputacji i mając rozzłoszczonych klientów/współpracowników, niezależnie od tego, co robią rozgniewani klienci/współpracownicy. Wreszcie wszystkie linki, które zaindeksowałeś w wyszukiwarkach, zostaną usunięte w oparciu o techniki blackhat, których używaliśmy w przeszłości do deindeksowania naszych celów.
Jak to zatrzymać?
Jesteśmy gotowi powstrzymać się od zniszczenia reputacji Twojej witryny za niewielką opłatą. Obecna opłata wynosi 2900 $ w $ (0,15 BTC).
Wyślij bitcoin na następujący adres bitcoin (koniecznie skopiuj i wklej):
3JY1suMCzv5DgrXTKsynfdic5jTpAEV4Sc
po dokonaniu płatności zostaniemy automatycznie poinformowani, że to była Twoja płatność. Zwróć uwagę, że musisz dokonać płatności w ciągu 5 dni od otrzymania tego e-maila lub wycieku bazy danych, wysłanych e-maili i deindeksowania Twojej witryny ZACZNIE SIĘ!
Jak mogę otrzymać bitcoins?
Możesz łatwo kupić bitcoins za pośrednictwem kilku stron internetowych lub nawet offline z bitcoin-bankomatu.
Co jeśli nie zapłacę?
jeśli zdecydujesz się nie płacić, rozpoczniemy atak we wskazanym terminie i będziemy go podtrzymywać, dopóki tego nie zrobisz, nie ma na to żadnego środka zaradczego, tylko stracisz więcej pieniędzy, próbując znaleźć rozwiązanie. Całkowicie zniszczymy Twoją reputację wśród Google i Twoich klientów.
To nie jest mistyfikacja, nie odpowiadaj na tego e-maila, nie próbuj argumentować ani negocjować, nie będziemy czytać żadnych odpowiedzi. gdy już zapłacisz, przestaniemy robić to, co robiliśmy i nigdy więcej od nas nie usłyszysz!
Pamiętaj, że bitcoin jest anonimowe i nikt nie dowie się, że spełniłeś wymagania.
Yet another example of an email from "We Have Hacked Your Website" spam campaign:
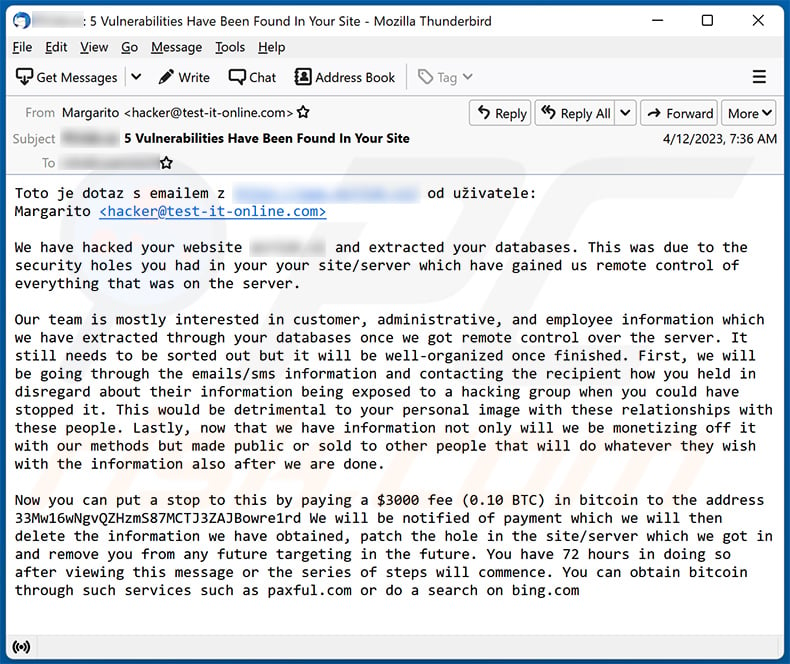
Text presented within:
Subject: -: 5 Vulnerabilities Have Been Found In Your Site
We have hacked your website - and extracted your databases. This was due to the security holes you had in your your site/server which have gained us remote control of everything that was on the server.Our team is mostly interested in customer, administrative, and employee information which we have extracted through your databases once we got remote control over the server. It still needs to be sorted out but it will be well-organized once finished. First, we will be going through the emails/sms information and contacting the recipient how you held in disregard about their information being exposed to a hacking group when you could have stopped it. This would be detrimental to your personal image with these relationships with these people. Lastly, now that we have information not only will we be monetizing off it with our methods but made public or sold to other people that will do whatever they wish with the information also after we are done.
Now you can put a stop to this by paying a $3000 fee (0.10 BTC) in bitcoin to the address 33Mw16wNgvQZHzmS87MCTJ3ZAJBowre1rd We will be notified of payment which we will then delete the information we have obtained, patch the hole in the site/server which we got in and remove you from any future targeting in the future. You have 72 hours in doing so after viewing this message or the series of steps will commence. You can obtain bitcoin through such services such as paxful.com or do a search on bing.com
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is We Have Hacked Your Website spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
This letter is not addressed to you personally. It is very likely that scammers sent it to all email addresses that they have in their database.
Is my computer actually hacked and does the sender have any information?
No, your computer is not hacked (or infected). Scammers hope that someone will believe that their computers are hacked and (or) personal information is stolen and send them money.
I have sent cryptocurrency to the address presented in such email, can I get my money back?
Unfortunately, crypto transactions are irreversible. Thus, it is not possible to retrieve the lost funds.
I have received an email containing a malicious attachment, is my computer infected?
If you have not opened that attachment, your computer is safe. Recipients cannot infect computers without opening files or links presented in emails.
Will Combo Cleaner remove malware infections that were present in email attachment?
Yes, Combo Cleaner can detect and remove almost all known malware infections. High-end malware usually hides deep in the operating system. For this reason, running a full system scan is required to eliminate such malware.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion