Do not trust the "I infected your computer with my private trojan" email
Phishing/ScamAlso Known As: I Infected Your Computer With My Private Trojan spam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the "I infected your computer with my private trojan" email?
"I infected your computer with my private trojan" is a scam email using the 'sextortion' scam model. This message attempts to blackmail recipients with videos of their sexual activity (the videos are nonexistent). The scammers claim that they have obtained this compromising material via malware they have used to infect the user's device.
The email states that should recipients fail to pay a certain sum, the videos will be publicized. This message is merely a scam, and the compromising material does not actually exist. Therefore, you should simply ignore the "I infected your computer with my private trojan" email.
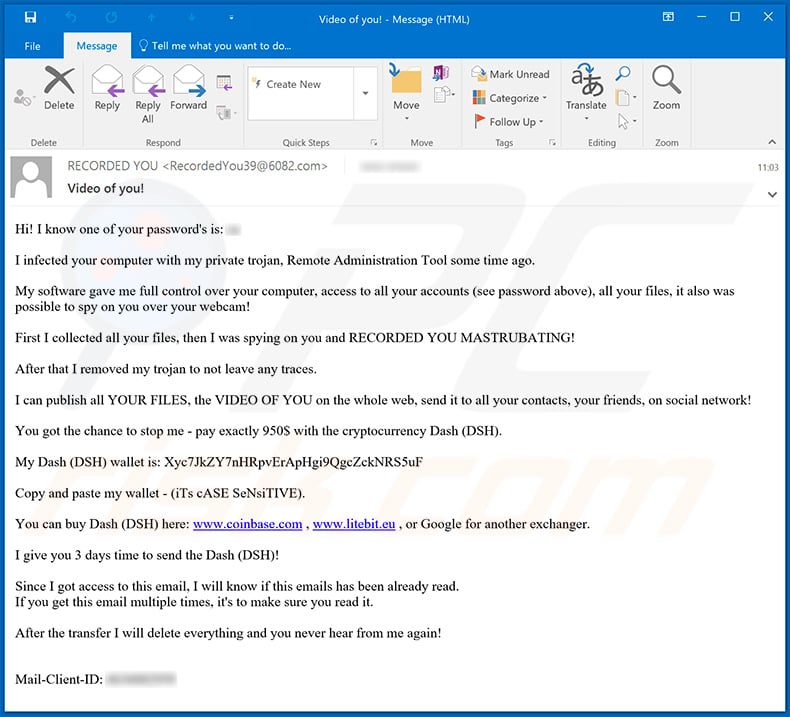
The email message entitled "Video of you!" begins by claiming that one of the recipient's account passwords is known. It has apparently been acquired through a Trojan, which the scammers have supposedly infiltrated into the user's system.
Via this fake malware infection, they allegedly gained access and control over the device (e.g. files, associated accounts and connected hardware). Firstly, the recipient's private files were exfiltrated, and videos were then made through the device's webcam. According to the email, this material contains explicit recordings of the user.
The Trojan (the system was not actually infected with this program) has supposedly been removed, leaving no traces of its presence. Unless the recipient pays 950 USD in the Dash cryptocurrency, the message warns that the obtained videos will be posted online and sent to all of the user's email and social network contacts.
The scam states that the user has three days to pay. If they pay within this period, the (nonexistent) content will be deleted. "I infected your computer with my private trojan" is a scheme designed to extort money from innocent people - all claims made in this message are false.
The scammers have not accessed or otherwise compromised the user's device/s, and they have not recorded any videos. Regardless of the validity of such claims, you are strongly advised against meeting the demands of cyber criminals, since there are no guarantees they are unlikely to honor any agreement.
| Name | I infected your computer with my private trojan Email Scam. |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | The email claims that compromising videos have been made of the recipient and, unless a specific sum is paid, they will be publicized. |
| Ransom Amount | $950 equivalent in the Dash cryptocurrency. |
| Cyber Criminal Cryptowallet Address | Xyc7JkZY7nHRpvErApHgi9QgcZckNRS5uF, 0xCE8C3c8c1a3013ca78ceb9134aA9743D1289616C, 0xCE8C3c8c1a3013ca78ceb9134aA9743D1289616C, 156tHaY89AbHxcfeAzgqUkP9wANs2oZPQT, bc1qm9v8t737crwcm3wn6gw3q5x7vncr0wfkp6pjkg, bc1q67uzflp6epem4uwceq5807655e5dzegx96tjvr, bc1q7zxsy4s66l6yeteqnuz7u43k40v6glzldxuyfd, bc1qaw9q3538uf3yh6z4shgzyhpeyzewyp9m44w9xc |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Deceptive/scam mail is sent during large scale spam campaigns. "Roundcube", "You have 46 Hours in order to make the payment", "AOL Winner", and "IFC Global Development Funding Program" are just some examples of such messages. These emails are designed to to generate revenue at users' expense.
As well as blatant scam attempts (e.g. blackmail with fake material), these messages are used to trick people into revealing their personal information - emails, social media, social networking, e-commerce (online store), banking and other account log-in credentials. They are also employed to infect systems with malicious programs (e.g. trojans, ransomware and other malware.).
How do spam campaigns infect computers?
Infections are caused via dangerous files attached to deceptive emails. Alternatively, the messages can contain download links of malicious content. Users are deceived into trusting this mail, as it is often disguised as "official", "important", "urgent", "priority" and so on. Infectious files can be in various formats.
For example, Microsoft Office and PDF documents, archive (RAR, ZIP) and executable (.exe, .run) files, JavaScript, etc. The infection process (i.e. malware download/installation) is triggered when a dangerous file is executed, run or otherwise opened. For example, Microsoft Office documents request users to enable macro commands (to enable editing).
Once they are enabled, the infection starts. Note that this process begins automatically when the document is opened in Microsoft Office versions released prior 2010.
How to avoid installation of malware
To avoid infections proliferated through spam campaigns, you are advised against opening dubious or irrelevant emails, especially those sent by unknown/suspect senders. Any attachments or links present in suspicious mail must not be opened, as doing so can result in a high-risk infection.
Additionally, use Microsoft Office versions released after 2010. The newer releases have "Protected View" mode, which prevents malicious macros from initiating an infection when the document is opened. Other popular malware proliferation methods include illegal activation tools ("cracks"), fake updates and untrusted download channels.
Therefore, it is important to activate and update products only with tools/functions provided by legitimate developers. Download software only from official and verified sources. To ensure device/user safety, have reputable anti-virus/anti-spyware installed and kept up to date.
Furthermore, this software should be used for regular system scans and removal of detected threats/issues. If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "I infected your computer with my private trojan" email message:
Subject: Video of you!
Hi! I know one of your password's is: -I infected your computer with my private trojan, Remote Administration Tool some time ago.
My software gave me full control over your computer, access to all your accounts (see password above), all your files, it also was possible to spy on you over your webcam!
First I collected all your files, then I was spying on you and RECORDED YOU MASTRUBATING!
After that I removed my trojan to not leave any traces.
I can publish all YOUR FILES, the VIDEO OF YOU on the whole web, send it to all your contacts, your friends, on social network!
You got the chance to stop me - pay exactly 950$ with the cryptocurrency Dash (DSH).
My Dash (DSH) wallet is: Xyc7JkZY7nHRpvErApHgi9QgcZckNRS5uF
Copy and paste my wallet - (iTs cASE SeNsiTIVE).
You can buy Dash (DSH) here: www.coinbase.com , www.litebit.eu , or Google for another exchanger.
I give you 3 days time to send the Dash (DSH)!
Since I got access to this email, I will know if this emails has been already read.
If you get this email multiple times, it's to make sure you read it.After the transfer I will delete everything and you never hear from me again!
Mail-Client-ID: -
Another example of "I Infected Your Computer With My Private Trojan" scam email:
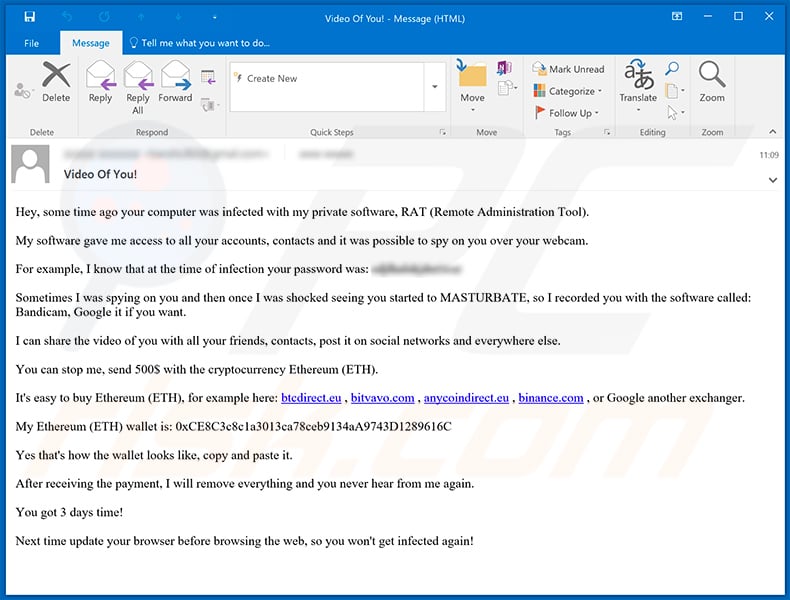
Text presented within:
Subject: Video Of You!
Hey, some time ago your computer was infected with my private software, RAT (Remote Administration Tool).
My software gave me access to all your accounts, contacts and it was possible to spy on you over your webcam.
For example, I know that at the time of infection your password was: -
Sometimes I was spying on you and then once I was shocked seeing you started to MASTURBATE, so I recorded you with the software called: Bandicam, Google it if you want.
I can share the video of you with all your friends, contacts, post it on social networks and everywhere else.
You can stop me, send 500$ with the cryptocurrency Ethereum (ETH).
It's easy to buy Ethereum (ETH), for example here: btcdirect.eu , bitvavo.com , anycoindirect.eu , binance.com , or Google another exchanger.
My Ethereum (ETH) wallet is: 0xCE8C3c8c1a3013ca78ceb9134aA9743D1289616C
Yes that's how the wallet looks like, copy and paste it.
After receiving the payment, I will remove everything and you never hear from me again.
You got 3 days time!
Next time update your browser before browsing the web, so you won't get infected again!
Another variant of "I infected your computer with my private trojan" spam email:
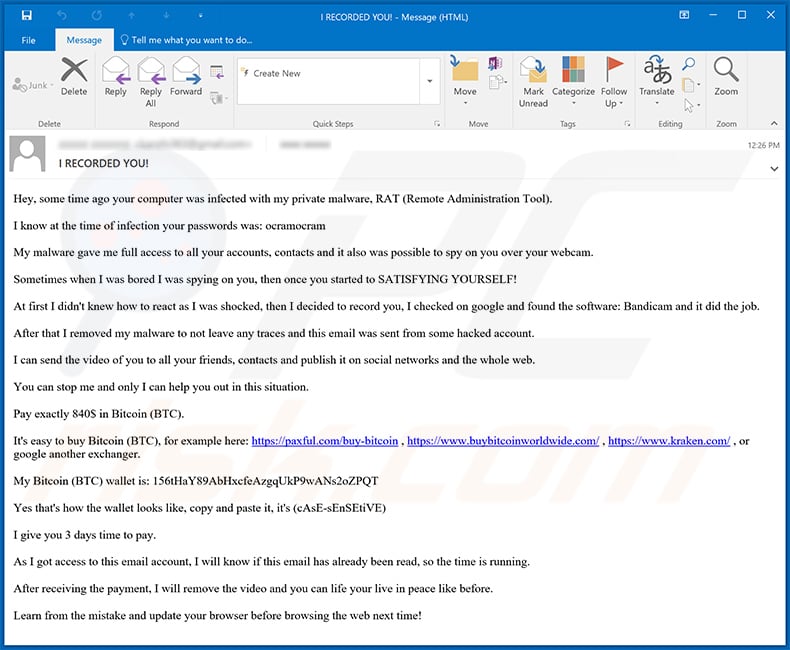
Text presented within:
Subject: I RECORDED YOU!
Hey, some time ago your computer was infected with my private malware, RAT (Remote Administration Tool).
I know at the time of infection your passwords was: ocramocram
My malware gave me full access to all your accounts, contacts and it also was possible to spy on you over your webcam.
Sometimes when I was bored I was spying on you, then once you started to SATISFYING YOURSELF!
At first I didn't knew how to react as I was shocked, then I decided to record you, I checked on google and found the software: Bandicam and it did the job.
After that I removed my malware to not leave any traces and this email was sent from some hacked account.
I can send the video of you to all your friends, contacts and publish it on social networks and the whole web.
You can stop me and only I can help you out in this situation.
Pay exactly 840$ in Bitcoin (BTC).
It's easy to buy Bitcoin (BTC), for example here: hxxps://paxful.com/buy-bitcoin , hxxps://www.buybitcoinworldwide.com/ , hxxps://www.kraken.com/ , or google another exchanger.
My Bitcoin (BTC) wallet is: 156tHaY89AbHxcfeAzgqUkP9wANs2oZPQT
Yes that's how the wallet looks like, copy and paste it, it's (cAsE-sEnSEtiVE)
I give you 3 days time to pay.
As I got access to this email account, I will know if this email has already been read, so the time is running.
After receiving the payment, I will remove the video and you can life your live in peace like before.
Learn from the mistake and update your browser before browsing the web next time!
A Polish variant of "I Infected Your Computer With My Private Trojan" scam email:
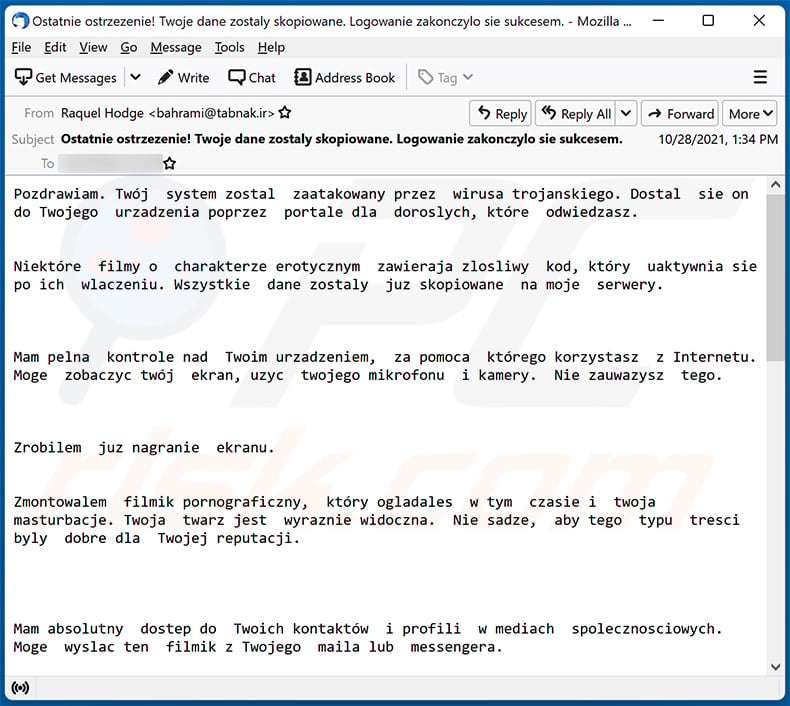
Text presented within:
Subject: Ostatnie ostrzezenie! Twoje dane zostaly skopiowane. Logowanie zakonczylo sie sukcesem.
Pozdrawiam. Twój system zostal zaatakowany przez wirusa trojanskiego. Dostal sie on do Twojego urzadzenia poprzez portale dla doroslych, które odwiedzasz.
Niektóre filmy o charakterze erotycznym zawieraja zlosliwy kod, który uaktywnia sie po ich wlaczeniu. Wszystkie dane zostaly juz skopiowane na moje serwery.
Mam pelna kontrole nad Twoim urzadzeniem, za pomoca którego korzystasz z Internetu. Moge zobaczyc twój ekran, uzyc twojego mikrofonu i kamery. Nie zauwazysz tego.
Zrobilem juz nagranie ekranu.
Zmontowalem filmik pornograficzny, który ogladales w tym czasie i twoja masturbacje. Twoja twarz jest wyraznie widoczna. Nie sadze, aby tego typu tresci byly dobre dla Twojej reputacji.
Mam absolutny dostep do Twoich kontaktów i profili w mediach spolecznosciowych. Moge wyslac ten filmik z Twojego maila lub messengera.
Jesli nie chcesz do tego dopuscic, wystarczy, ze zrobisz jeden prosty krok.
Wystarczy przelac 4700 zl (PLN) na portfel bitcoin: bc1qm9v8t737crwcm3wn6gw3q5x7vncr0wfkp6pjkg(w ekwiwalencie bitcoinów po kursie wymiany obowiazujacym w momencie dokonywania przelewu)
Instrukcje, jak to zrobic, znajdziesz w Google.
Po dokonaniu platnosci usune film i wirusa z Twojego urzadzenia. Potem nikt nie bedzie ci juz przeszkadzal.
Dam Ci 2 dni robocze.
Zostane powiadomiony, gdy przeczytasz e-mail. Natychmiast wlacza sie timer. Nie ma sensu skarzyc sie gdziekolwiek, takze na policji. Mój portfel i poczta sa nie do namierzenia.
Jesli dowiem sie, ze udostepniles te wiadomosc komukolwiek innemu, film zostanie natychmiast rozpowszechniony. Zrujnuje twoja reputacje na zawsze, a wszystkie twoje dane stana sie publiczne.
Wszyscy beda wiedziec o twojej pasji do stron porno i nie tylko. Zmiana hasel nic nie da, bo wszystkie dane sa juz na moich serwerach.
Nie zapominaj, ze reputacja jest bardzo wazna i badz rozsadny!
A German variant of "I Infected Your Computer With My Private Trojan" scam email:
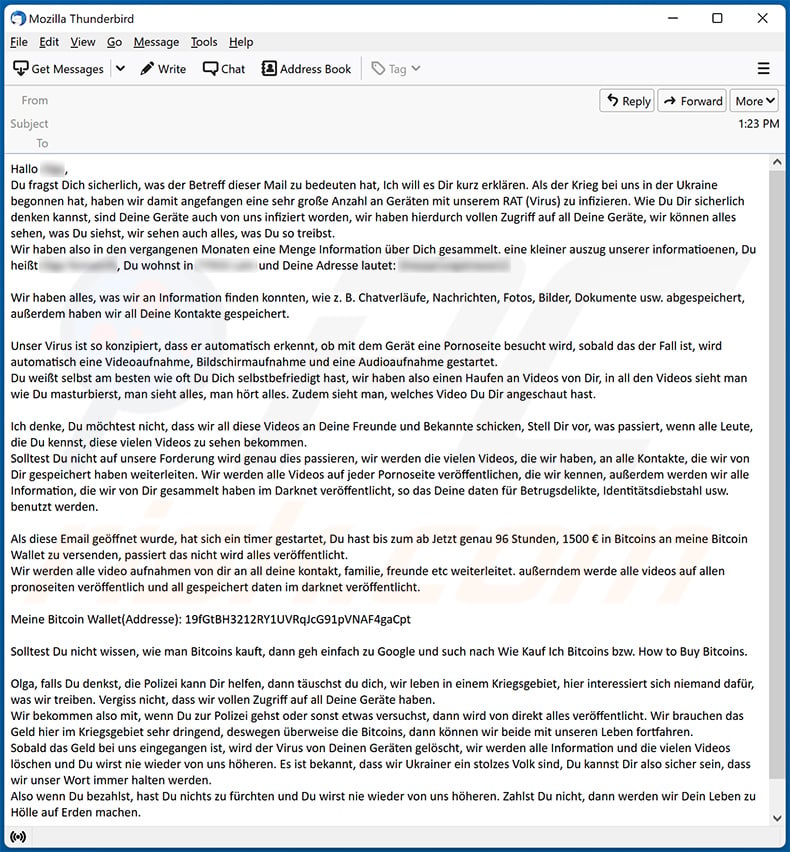
Text presented within:
Hallo **********,
Du fragst Dich sicherlich, was der Betreff dieser Mail zu bedeuten hat, Ich will es Dir kurz erklären. Als der Krieg bei uns in der Ukraine begonnen hat, haben wir damit angefangen eine sehr große Anzahl an Geräten mit unserem RAT (Virus) zu infizieren. Wie Du Dir sicherlich denken kannst, sind Deine Geräte auch von uns infiziert worden, wir haben hierdurch vollen Zugriff auf all Deine Geräte, wir können alles sehen, was Du siehst, wir sehen auch alles, was Du so treibst.
Wir haben also in den vergangenen Monaten eine Menge Information über Dich gesammelt. eine kleiner auszug unserer informatioenen, Du heißt **********, Du wohnst in ********** und Deine Adresse lautet: **********Wir haben alles, was wir an Information finden konnten, wie z. B. Chatverläufe, Nachrichten, Fotos, Bilder, Dokumente usw. abgespeichert, außerdem haben wir all Deine Kontakte gespeichert.
Unser Virus ist so konzipiert, dass er automatisch erkennt, ob mit dem Gerät eine Pornoseite besucht wird, sobald das der Fall ist, wird automatisch eine Videoaufnahme, Bildschirmaufnahme und eine Audioaufnahme gestartet.
Du weißt selbst am besten wie oft Du Dich selbstbefriedigt hast, wir haben also einen Haufen an Videos von Dir, in all den Videos sieht man wie Du masturbierst, man sieht alles, man hört alles. Zudem sieht man, welches Video Du Dir angeschaut hast.Ich denke, Du möchtest nicht, dass wir all diese Videos an Deine Freunde und Bekannte schicken, Stell Dir vor, was passiert, wenn alle Leute, die Du kennst, diese vielen Videos zu sehen bekommen.
Solltest Du nicht auf unsere Forderung wird genau dies passieren, wir werden die vielen Videos, die wir haben, an alle Kontakte, die wir von Dir gespeichert haben weiterleiten. Wir werden alle Videos auf jeder Pornoseite veröffentlichen, die wir kennen, außerdem werden wir alle Information, die wir von Dir gesammelt haben im Darknet veröffentlicht, so das Deine daten für Betrugsdelikte, Identitätsdiebstahl usw. benutzt werden.Als diese Email geöffnet wurde, hat sich ein timer gestartet, Du hast bis zum ab Jetzt genau 96 Stunden, 1500 € in Bitcoins an meine Bitcoin Wallet zu versenden, passiert das nicht wird alles veröffentlicht.
Wir werden alle video aufnahmen von dir an all deine kontakt, familie, freunde etc weiterleitet. außerndem werde alle videos auf allen pronoseiten veröffentlich und all gespeichert daten im darknet veröffentlicht.Meine Bitcoin Wallet(Addresse): 19fGtBH3212RY1UVRqJcG91pVNAF4gaCpt
Solltest Du nicht wissen, wie man Bitcoins kauft, dann geh einfach zu Google und such nach Wie Kauf Ich Bitcoins bzw. How to Buy Bitcoins.
Olga, falls Du denkst, die Polizei kann Dir helfen, dann täuschst du dich, wir leben in einem Kriegsgebiet, hier interessiert sich niemand dafür, was wir treiben. Vergiss nicht, dass wir vollen Zugriff auf all Deine Geräte haben.
Wir bekommen also mit, wenn Du zur Polizei gehst oder sonst etwas versuchst, dann wird von direkt alles veröffentlicht. Wir brauchen das Geld hier im Kriegsgebiet sehr dringend, deswegen überweise die Bitcoins, dann können wir beide mit unseren Leben fortfahren.
Sobald das Geld bei uns eingegangen ist, wird der Virus von Deinen Geräten gelöscht, wir werden alle Information und die vielen Videos löschen und Du wirst nie wieder von uns höheren. Es ist bekannt, dass wir Ukrainer ein stolzes Volk sind, Du kannst Dir also sicher sein, dass wir unser Wort immer halten werden.
Also wenn Du bezahlst, hast Du nichts zu fürchten und Du wirst nie wieder von uns höheren. Zahlst Du nicht, dann werden wir Dein Leben zu Hölle auf Erden machen.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is I Infected Your Computer With My Private Trojan spam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion