Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is RustyBuer malware?
RustyBuer is the name of a new variant of the Buer loader. The main difference between the new and the original variants is that one is written in Rust multi-paradigm programming language, and another one is written in C programming language. Both RustyBuer and Buer function as loaders - they infect computers with other malware.
RustyBuer in detail
It is likely that RustyBuer and the original version are written in different languages because by developing the new variant in Rust language, cybercriminals give it the ability to evade anti-malware detections that are based on features of the malware written in the C language.
RustyBuer has various options on how to download and execute a payload (install malicious software). Some of RustyBuer's samples were (or still are) used to distribute Cobalt Strike Beacon as a second-stage payload, which means cybercriminals may be selling access to infected machines on the dark web, hacker forums.
It is known that RustyBuer was already used to proliferate more than one ransomware strain. Ransomware is a type of malware that encrypts data (locks files) and generates a ransom demanding message with instructions on how to pay for data decryption.
It is worth mentioning that RustyBuer can check for installed virtual machines to avoid being examined by malware analysts. It is very likely that cybercriminals behind RustyBuer are continuing to improve their malware, so it could be more difficult to detect by security vendors.
To summarize, it is known that the new Buer loader variant was already used to distribute Cobalt Strike Beacon and multiple ransomware strains. Sine RustyBuer has numerous options on how to download and execute a payload, this malware could be used to distribute other malicious software as well.
More examples of malware designed to distribute other software of this kind are BazarLoader, HimeraLoader, and AbSent-Loader. It is common that loaders are capable of evading detection, which allows them to distribute malware without being detected and removed by installed anti-virus solutions.
| Name | RustyBuer loader |
| Threat Type | Malware loader |
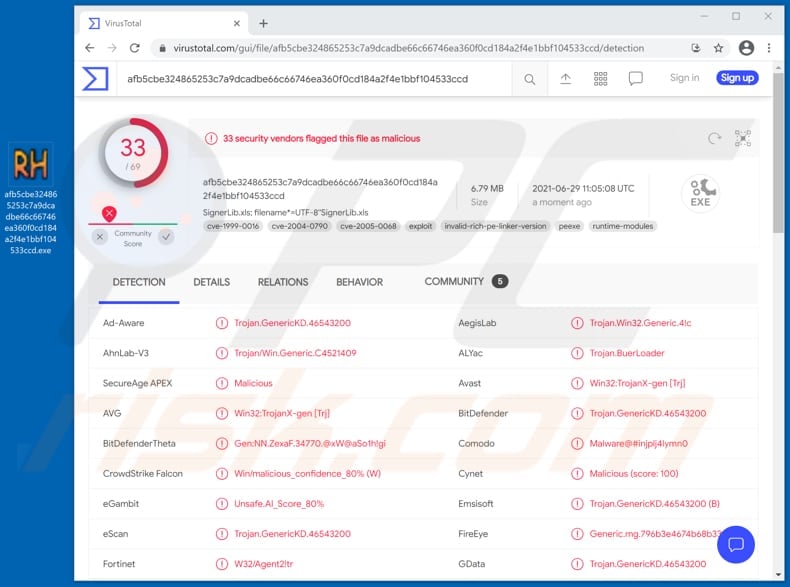
| Detection Names | Avast (Win32:TrojanX-gen [Trj]), BitDefender (Trojan.GenericKD.46543200), Emsisoft (Trojan.GenericKD.46543200 (B)), Kaspersky (HEUR:Trojan.Win32.Agent2.gen), Microsoft (Trojan:Win32/Casdet!rfn), Full List (VirusTotal) |
| Payload | Cobalt Strike Beacon, ransomware and possibly other malware |
| Symptoms | Loaders are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
RustyBuer in general
To summarize, it is known that the new Buer loader variant was already used to distribute Cobalt Strike Beacon and multiple ransomware strains. Sine RustyBuer has numerous options on how to download and execute a payload, this malware could be used to distribute other malicious software as well.
More examples of malware designed to distribute other software of this kind are BazarLoader, HimeraLoader, and AbSent-Loader. It is common that loaders are capable of evading detection, which allows them to distribute malware without being detected and removed by installed anti-virus solutions.
How did RustyBuer infiltrate my computer?
Research shows that RustyBuer is distributed via emails disguised as letters regarding COVID-19 vaccination information. It is not the first time when cybercriminals are taking advantage of the coronavirus disease to extract personal information, money or distribute malicious software.
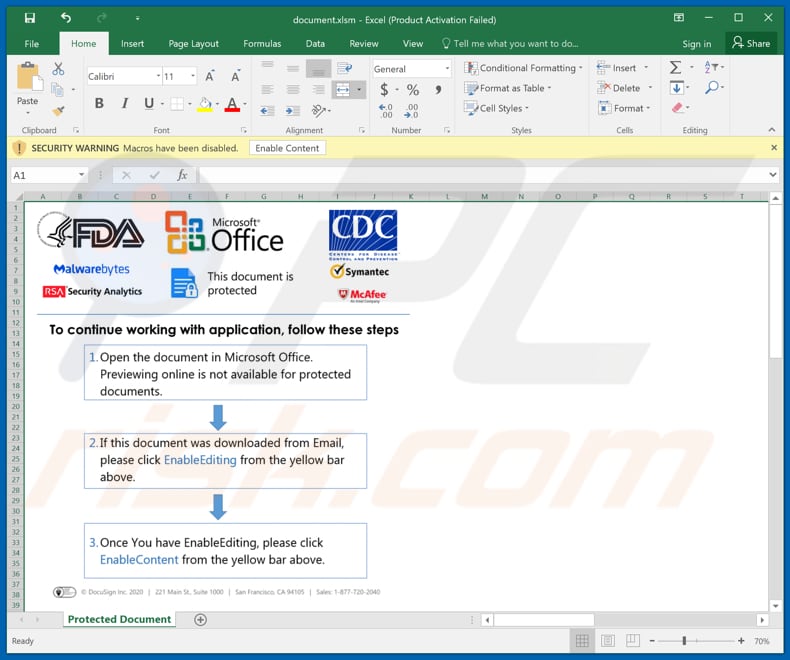
As written in this particular email, CDC and FDA have compiled a complete summary containing information regarding contraindications, complications that may be caused by vaccines available in the United States. The main purpose of this email is to trick recipients into opening the attached Microsoft Excel document and enabling macros commands in it (enabling editing/content).
When users enable macros in malicious MS Office documents, they allow those documents to start the infection chain. It is important to mention that malicious documents opened with older MS Office versions (released prior to the year 2010) do not have the "Protected View" mode - they infect computers automatically.
It is worth mentioning that cybercriminals can use PDF documents, JavaScript files, executable files like EXE, archive files like ZIP, RAR, and other files to deliver malware via email as well. Typically, they disguise their emails as important, official letters from legitimate companies, organizations (for example, CDF, FDA).
How to avoid installation of malware?
Software and files should be downloaded from legitimate websites and via direct links. It is recommended to avoid using Peer-to-Peer networks, unofficial websites, third-party downloaders, unofficial sites, third-party installers, and other sources of this kind to download or install programs.
The operating system and installed on it have to be updated and activated with implemented functions or tools provided by their official developers. It is common that unofficial activation ('cracking') tools and third-party updaters to have malware hidden inside them. Besides, it is not legal to activate licensed programs with various third-party tools.
Attachments and website links in irrelevant emails received from suspicious, unknown senders should not be opened without carefully examining them first. It is common that cybercriminals use such emails as tools to deliver their malware. It is worth mentioning that they often disguise their emails as important, official, and so on.
Additionally, is is recommended to have a reputable antivirus or anti-spyware software installed on the operating system and run virus scans with it regularly. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Email containing file designed to install RustyBuer:
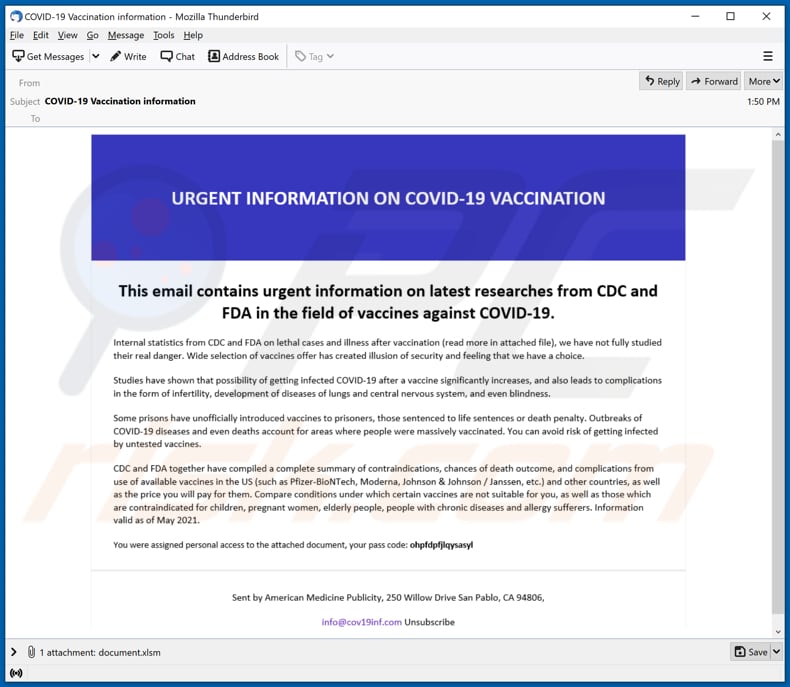
Text in this email:
Subject: COVID-19 Vaccination information
URGENT INFORMATION ON COVID-19 VACCINATION
This email contains urgent information on latest researches from CDC and FDA in the field of vaccines against COVID-19.
Internal statistics from CDC and FDA on lethal cases and illness after vaccination (read more in attached file), we have not fully studied their real danger. Wide selection of vaccines offer has created illusion of security and feeling that we have a choice.
Studies have shown that possibility of getting infected COVID-10 after a vaccine significantly increases, and also leads to complications in the form of infertility, development of diseases of lungs and central nervous system, and even blindness.
Some prisons have unofficially introduced vaccines to prisoners, those sentenced to life sentences or death penalty. Outbreaks of COVID-19 diseases and even deaths account for areas where people were massively vaccinated. You can avoid risk of getting infected by untested vaccines.
CDC and FDA together have compiled a complete summary of contraindications, chances of death outcome, and complications from use of available vaccines in the US (such as Pfizer-BioNTech, Moderna, Johnson & Johnson / Janssen, etc.) and other countries, as well as the price you will pay for them. Compare conditions under which certain vaccines are not suitable for you, as well as those which are contraindicated for children, pregnant women, elderly people, people with chronic diseases and allergy sufferers. Information valid as of May 2021.
You were assigned personal access to the attached document, your pass code: ohpfdpfjlqysasyl
Sent by American Medicine Publicity, 250 Willow Drive San Pablo, CA 94806,
info@cov19inf.com Unsubscribe
Malicious attachment distributing RustyBuer:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is RustyBuer?
- STEP 1. Manual removal of RustyBuer malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion