How to spot scam campaigns like "Scam Victim Compensation Funds"
Phishing/ScamAlso Known As: Scam Victim Compensation Funds scam email
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of email is "Scam Victim Compensation Funds"?
We have analyzed this email and found that it was sent by fraudsters who seek to extract money and (or) sensitive information. Scammers aim to convince recipients who have been scammed in the past that they can receive compensation of three million British pounds. It is a scam email that should be marked as spam and deleted.
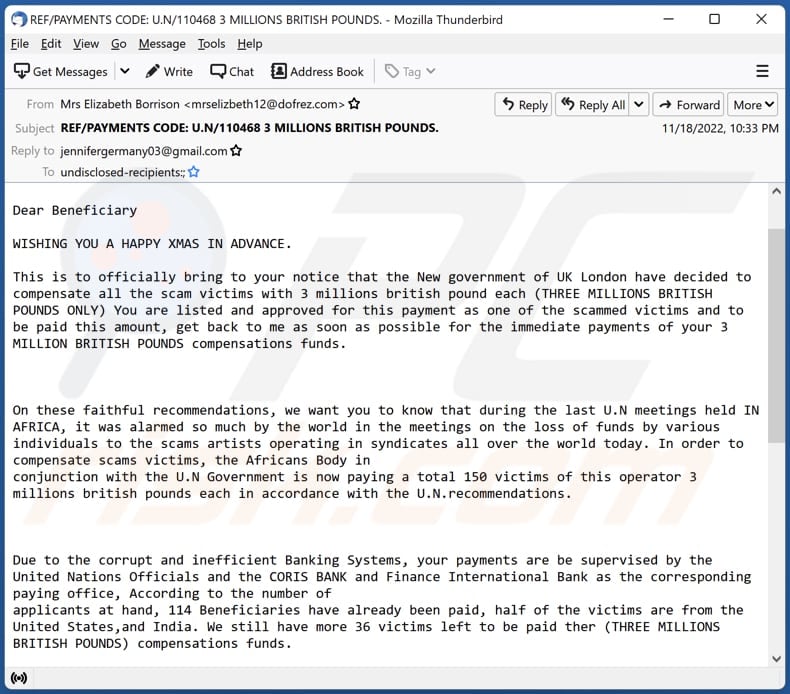
More about the "Scam Victim Compensation Funds" scam email
This scam email claims that the the new UK government has decided to pay compensation to all victims of various scams. Each victim can receive three million British pounds. The email says that only 150 victims will get compensation, and 114 beneficiaries have already been paid to lure recipients into taking immediate action.
In order to claim their compensation, recipients are supposed to contact the "approved private officer" via one of the provided email addresses. After contacting scammers behind this email, recipients will most likely be asked to provide sensitive information (e.g., credit card details) or pay some "administration" (or other) fee.
Emails promising a significant share of a large sum of money (in this case, three million British pounds) should always be ignored. People who fall for such scams (pay money to scammers) get nothing in return.
| Name | Scam Victim Compensation Funds Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Victims of scams can receive compensation (three million British pounds) |
| Scammer Email Address | nuixeia@gmail.com, jennifergermany03@gmail.com |
| Disguise | Letter from Elizbeth Borrison regarding compensations for victims of various scams. |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similar scam emails in general
These emails usually are disguised as important/official/urgent letters from legitimate companies, organizations, or other entities. They often include logos of real companies, names of existing people, etc. Scammers use these emails to extract money or sensitive information.
Examples of similar scams are "BRITISH CAMELOT ONLINE LOTTERY Email Scam", "Coordination Of Humanitarian Affairs Email Scam", and "Funding Commitments To Fight COVID-19 Email Scam". Crooks use emails not only to extract money or information but also to trick recipients into infecting computers with malware.
How do spam campaigns infect computers?
Recipients infect computers via emails by opening malicious links or attachments. Computers do not always become infected right after opening malicious files. For instance, malicious MS Office documents cannot infect computers until macros commands (editing or content) are enabled.
It is important to mention that MS Office versions released before 2010 do not include the Protected View feature. Thus, malicious documents opened with older versions infect computers after they are opened.
How to avoid installation of malware?
Do not open attachments and links in suspicious emails (e.g., irrelevant emails from unknown addresses). Remember that cybercriminals often use emails to deliver malware. They pretend to be legitimate companies, organizations, other entities, or well-known people.
Download software from official pages and stores. Avoid downloads from other sources. Do not click on suspicious links or advertisements appearing on shady websites. Keep the operating system and installed programs updated. Do not use third-party tools to update or activate any software.
If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Appearance of the "Scam Victim Compensation Funds" scam email (GIF):
Text presented in the "Scam Victim Compensation Funds" email letter:
Subject: REF/PAYMENTS CODE: U.N/110468 3 MILLIONS BRITISH POUNDS.
Dear Beneficiary
WISHING YOU A HAPPY XMAS IN ADVANCE.
This is to officially bring to your notice that the New government of UK London have decided to compensate all the scam victims with 3 millions british pound each (THREE MILLIONS BRITISH POUNDS ONLY) You are listed and approved for this payment as one of the scammed victims and to be paid this amount, get back to me as soon as possible for the immediate payments of your 3 MILLION BRITISH POUNDS compensations funds.
On these faithful recommendations, we want you to know that during the last U.N meetings held IN AFRICA, it was alarmed so much by the world in the meetings on the loss of funds by various individuals to the scams artists operating in syndicates all over the world today. In order to compensate scams victims, the Africans Body in
conjunction with the U.N Government is now paying a total 150 victims of this operator 3 millions british pounds each in accordance with the U.N.recommendations.Due to the corrupt and inefficient Banking Systems, your payments are be supervised by the United Nations Officials and the CORIS BANK and Finance International Bank as the corresponding paying office, According to the number of
applicants at hand, 114 Beneficiaries have already been paid, half of the victims are from the United States,and India. We still have more 36 victims left to be paid ther (THREE MILLIONS BRITISH POUNDS) compensations funds.For the claiming of your compensation 3 millions british pounds through the credited MASTER CARD and pin code,kindly feel free to contact our approved private officer from U.N Name: Madam Mrs. Jenn Germany Email:
(jennifergermany03@gmail.com) She will instruct what you will do in order to successfully transfer your compensation amount to you.You will receive your Compensation amount through a loaded master card payment or through Coris trust credit online bank. This is the two paying options approved by the UK LONDON Government; you will be detailed with modalities as soon as you contact the assigned approved U.N Delegate officer of the U.N and Finance International Bank.
Finally you are free to decide how you would like your compensation of 3 millions british pounds funds to be paid to you as soon as possible.
Sincerely Yours
Mrs Elizbeth BorrisonContact My Private email address here (nuixeia@gmail.com) should you have any questions.
Other examples of emails from "Scam Victim Compensation Funds" spam campaign:
Sample 1:
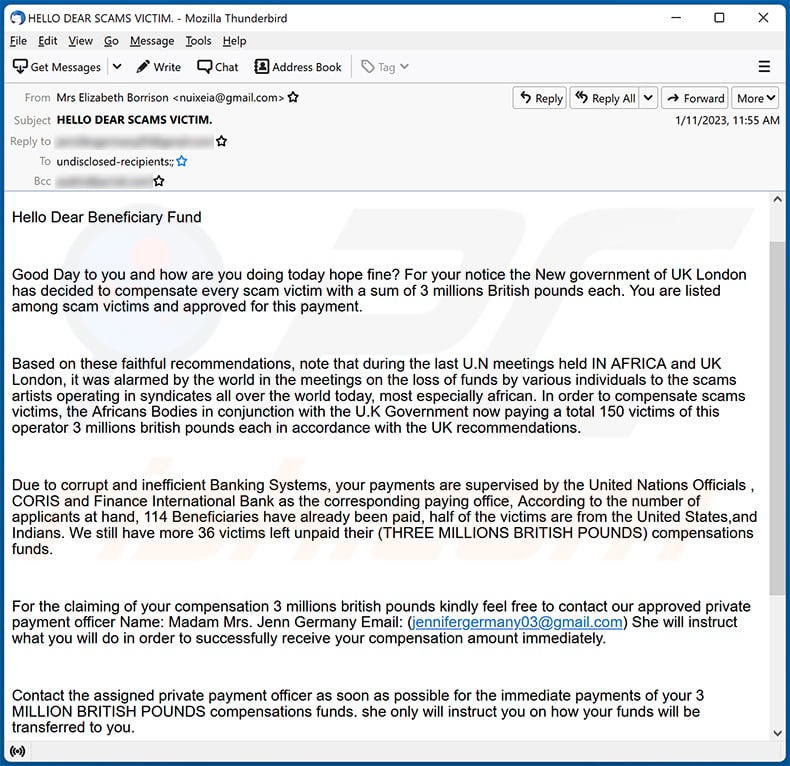
Text presented within:
Subject: HELLO DEAR SCAMS VICTIM.
Hello Dear Beneficiary Fund
Good Day to you and how are you doing today hope fine? For your notice the New government of UK London has decided to compensate every scam victim with a sum of 3 millions British pounds each. You are listed among scam victims and approved for this payment.
Based on these faithful recommendations, note that during the last U.N meetings held IN AFRICA and UK London, it was alarmed by the world in the meetings on the loss of funds by various individuals to the scams artists operating in syndicates all over the world today, most especially african. In order to compensate scams victims, the Africans Bodies in conjunction with the U.K Government now paying a total 150 victims of this operator 3 millions british pounds each in accordance with the UK recommendations.
Due to corrupt and inefficient Banking Systems, your payments are supervised by the United Nations Officials , CORIS and Finance International Bank as the corresponding paying office, According to the number of applicants at hand, 114 Beneficiaries have already been paid, half of the victims are from the United States,and Indians. We still have more 36 victims left unpaid their (THREE MILLIONS BRITISH POUNDS) compensations funds.
For the claiming of your compensation 3 millions british pounds kindly feel free to contact our approved private payment officer Name: Madam Mrs. Jenn Germany Email: (jennifergermany03@gmail.com) She will instruct what you will do in order to successfully receive your compensation amount immediately.
Contact the assigned private payment officer as soon as possible for the immediate payments of your 3 MILLION BRITISH POUNDS compensations funds. she only will instruct you on how your funds will be transferred to you.
Sincerely Yours
Mrs Elizbeth Borrison
Contact My Private email address here (nuixeia@gmail.com) should you have any questions.
Sample 2:
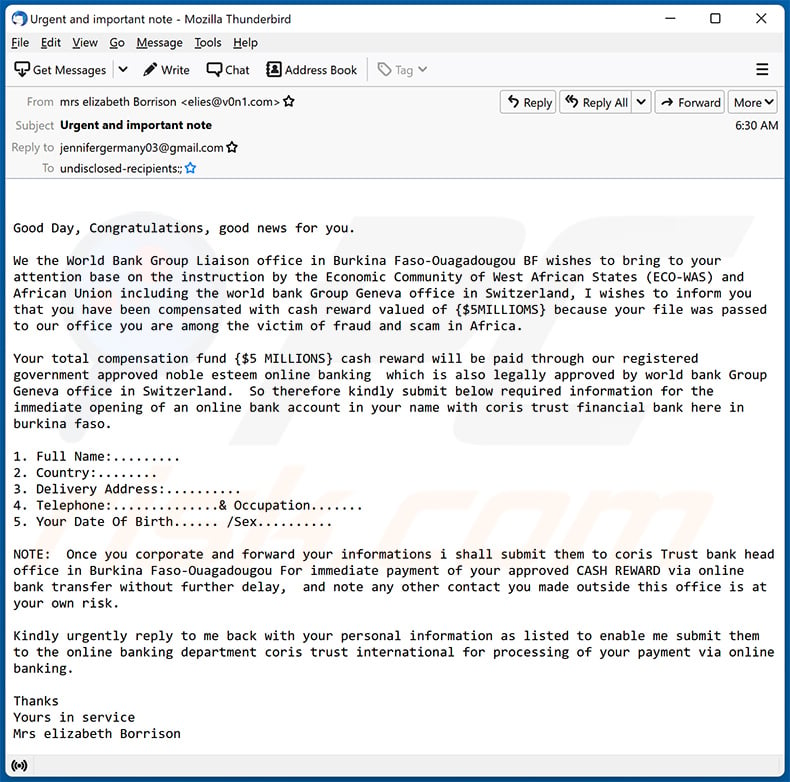
Text presented within:
Subject: Urgent and important note:
Good Day, Congratulations, good news for you.
We the World Bank Group Liaison office in Burkina Faso-Ouagadougou BF wishes to bring to your attention base on the instruction by the Economic Community of West African States (ECO-WAS) and African Union including the world bank Group Geneva office in Switzerland, I wishes to inform you that you have been compensated with cash reward valued of {$5MILLIOMS} because your file was passed to our office you are among the victim of fraud and scam in Africa.
Your total compensation fund {$5 MILLIONS} cash reward will be paid through our registered government approved noble esteem online banking which is also legally approved by world bank Group Geneva office in Switzerland. So therefore kindly submit below required information for the immediate opening of an online bank account in your name with coris trust financial bank here in burkina faso.
1. Full Name:.........
2. Country:........
3. Delivery Address:..........
4. Telephone:..............& Occupation.......
5. Your Date Of Birth...... /Sex..........NOTE: Once you corporate and forward your informations i shall submit them to coris Trust bank head office in Burkina Faso-Ouagadougou For immediate payment of your approved CASH REWARD via online bank transfer without further delay, and note any other contact you made outside this office is at your own risk.
Kindly urgently reply to me back with your personal information as listed to enable me submit them to the online banking department coris trust international for processing of your payment via online banking.
Thanks
Yours in service
Mrs elizabeth Borrison
Sample 3:
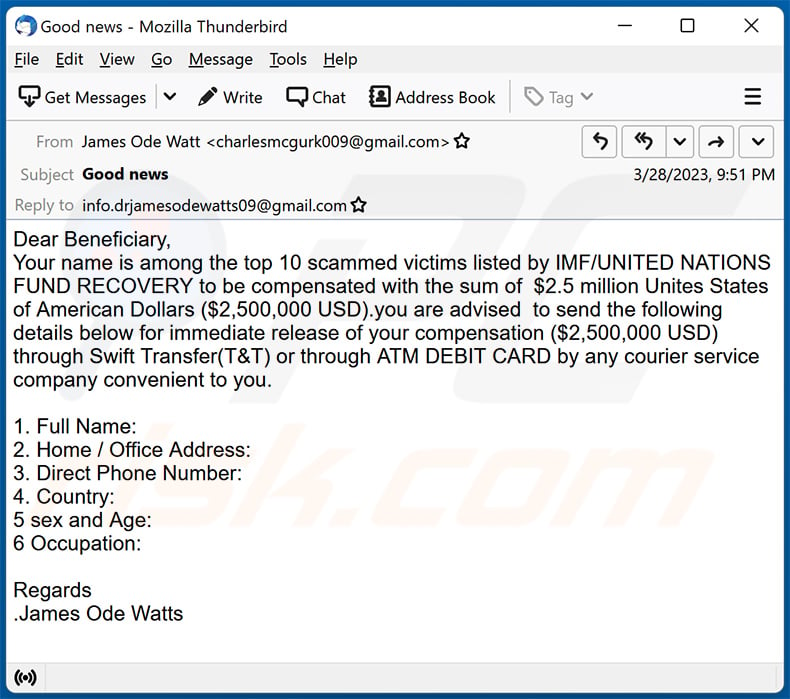
Text presented within:
Subject: Good news
Dear Beneficiary,
Your name is among the top 10 scammed victims listed by IMF/UNITED NATIONS FUND RECOVERY to be compensated with the sum of $2.5 million Unites States of American Dollars ($2,500,000 USD).you are advised to send the following details below for immediate release of your compensation ($2,500,000 USD) through Swift Transfer(T&T) or through ATM DEBIT CARD by any courier service company convenient to you.
1. Full Name:
2. Home / Office Address:
3. Direct Phone Number:
4. Country:
5 sex and Age:
6 Occupation:
Regards
.James Ode Watts
Sample 4:
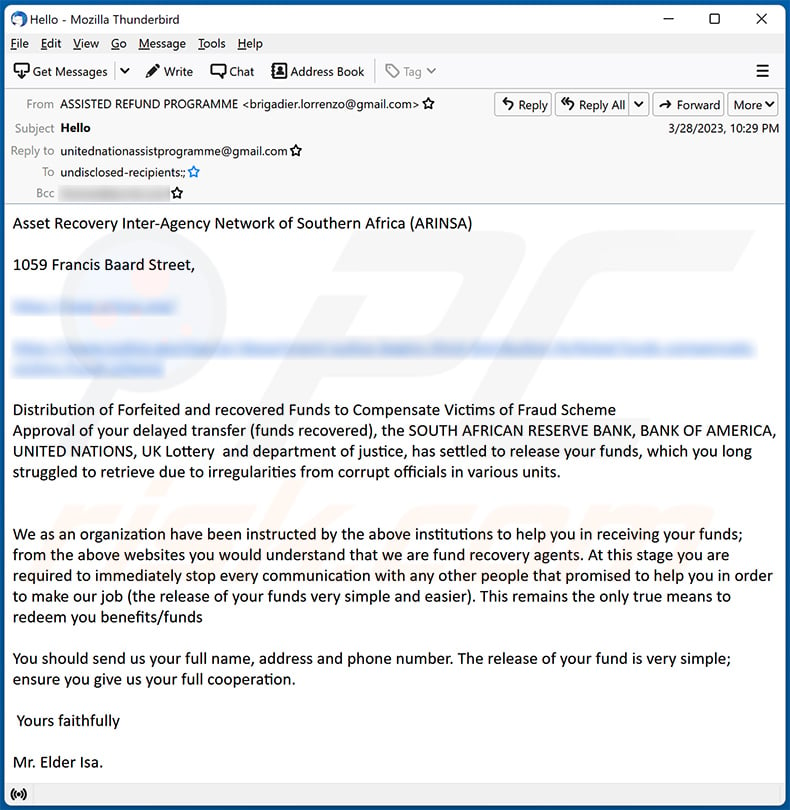
Text presented within:
Subject: Hello
Asset Recovery Inter-Agency Network of Southern Africa (ARINSA)
1059 Francis Baard Street,
-
-Distribution of Forfeited and recovered Funds to Compensate Victims of Fraud Scheme
Approval of your delayed transfer (funds recovered), the SOUTH AFRICAN RESERVE BANK, BANK OF AMERICA, UNITED NATIONS, UK Lottery and department of justice, has settled to release your funds, which you long struggled to retrieve due to irregularities from corrupt officials in various units.
We as an organization have been instructed by the above institutions to help you in receiving your funds; from the above websites you would understand that we are fund recovery agents. At this stage you are required to immediately stop every communication with any other people that promised to help you in order to make our job (the release of your funds very simple and easier). This remains the only true means to redeem you benefits/fundsYou should send us your full name, address and phone number. The release of your fund is very simple; ensure you give us your full cooperation.
Yours faithfully
Mr. Elder Isa.
Sample 5:
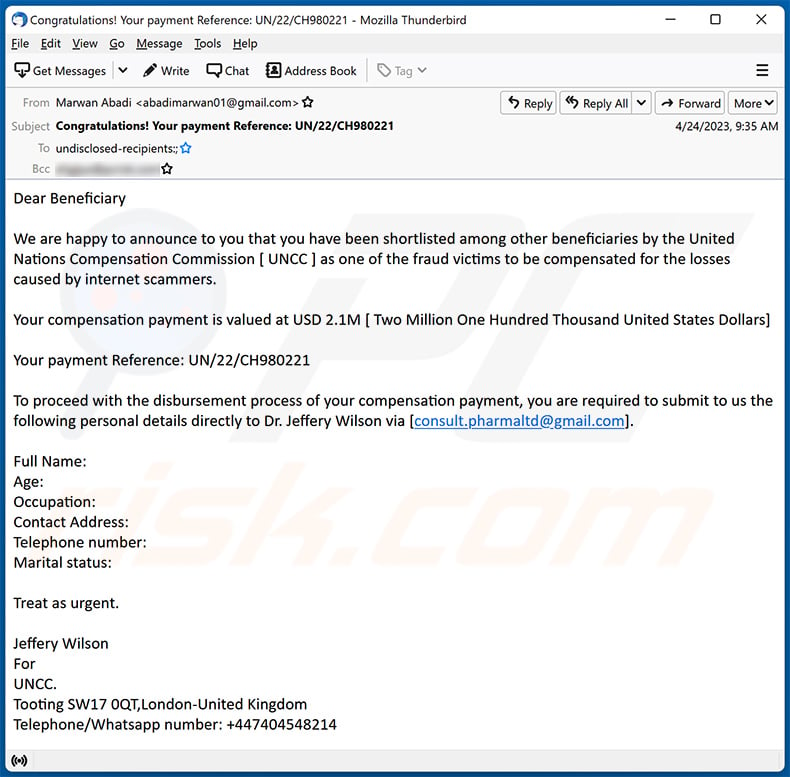
Text presented within:
Subject: Congratulations! Your payment Reference: UN/22/CH980221
Dear BeneficiaryWe are happy to announce to you that you have been shortlisted among other beneficiaries by the United Nations Compensation Commission [ UNCC ] as one of the fraud victims to be compensated for the losses caused by internet scammers.
Your compensation payment is valued at USD 2.1M [ Two Million One Hundred Thousand United States Dollars]
Your payment Reference: UN/22/CH980221
To proceed with the disbursement process of your compensation payment, you are required to submit to us the following personal details directly to Dr. Jeffery Wilson via [consult.pharmaltd@gmail.com].
Full Name:
Age:
Occupation:
Contact Address:
Telephone number:
Marital status:Treat as urgent.
Jeffery Wilson
For
UNCC.
Tooting SW17 0QT,London-United Kingdom
Telephone/Whatsapp number: +447404548214
Sample 6:
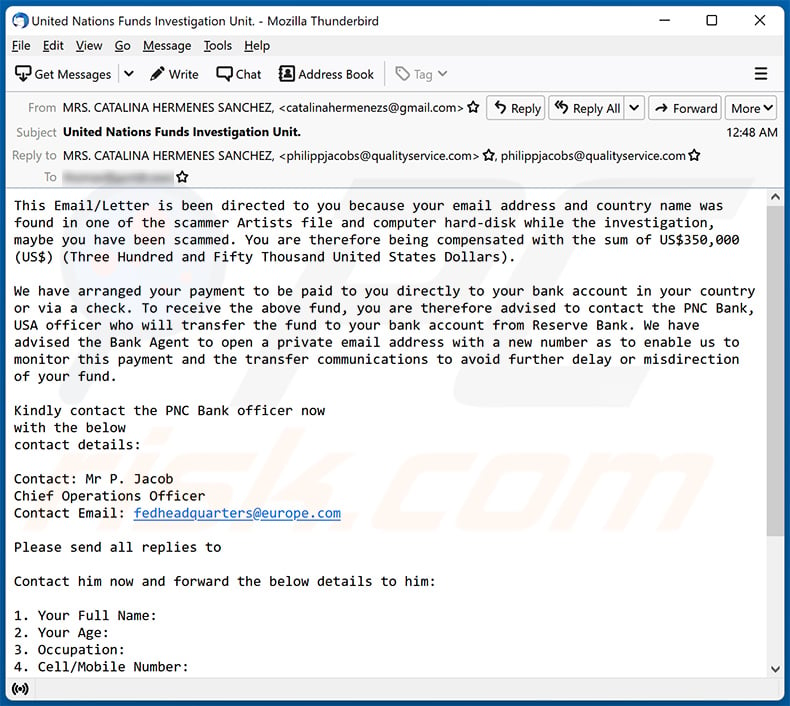
Text presented within:
Subject: United Nations Funds Investigation Unit.
This Email/Letter is been directed to you because your email address and country name was found in one of the scammer Artists file and computer hard-disk while the investigation, maybe you have been scammed. You are therefore being compensated with the sum of US$350,000 (US$) (Three Hundred and Fifty Thousand United States Dollars).
We have arranged your payment to be paid to you directly to your bank account in your country or via a check. To receive the above fund, you are therefore advised to contact the PNC Bank, USA officer who will transfer the fund to your bank account from Reserve Bank. We have advised the Bank Agent to open a private email address with a new number as to enable us to monitor this payment and the transfer communications to avoid further delay or misdirection of your fund.
Kindly contact the PNC Bank officer now
with the below
contact details:Contact: Mr P. Jacob
Chief Operations Officer
Contact Email: fedheadquarters@europe.comPlease send all replies to
Contact him now and forward the below details to him:
1. Your Full Name:
2. Your Age:
3. Occupation:
4. Cell/Mobile Number:
Yours in Service.
MR. WILSON STEWART.
United Nations Funds Investigation Unit.
Sample 7:
Text presented within:
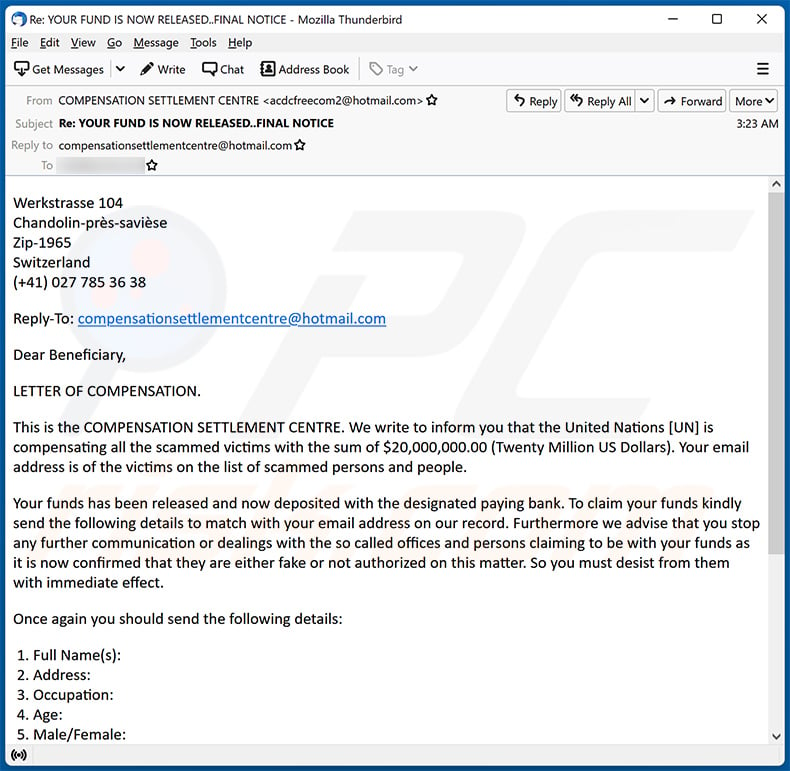
Subject: Re: YOUR FUND IS NOW RELEASED..FINAL NOTICE
Werkstrasse 104
Chandolin-près-savièse
Zip-1965
Switzerland
(+41) 027 785 36 38Reply-To: compensationsettlementcentre@hotmail.com
Dear Beneficiary,
LETTER OF COMPENSATION.
This is the COMPENSATION SETTLEMENT CENTRE. We write to inform you that the United Nations [UN] is compensating all the scammed victims with the sum of $20,000,000.00 (Twenty Million US Dollars). Your email address is of the victims on the list of scammed persons and people.
Your funds has been released and now deposited with the designated paying bank. To claim your funds kindly send the following details to match with your email address on our record. Furthermore we advise that you stop any further communication or dealings with the so called offices and persons claiming to be with your funds as
it is now confirmed that they are either fake or not authorized on this matter. So you must desist from them with immediate effect.Once again you should send the following details:
1. Full Name(s):
2. Address:
3. Occupation:
4. Age:
5. Male/Female:
6. Origin Country:
7. Residing Country
8. Mobile No:Kindly reply to this notification immediately.
Yours Faithfully,
Josh Greene
Publicity Secretary
Compensation Settlement Centre
E-mail: compensationsettlementcentre@hotmail.com
Sample 8:
Text presented within:
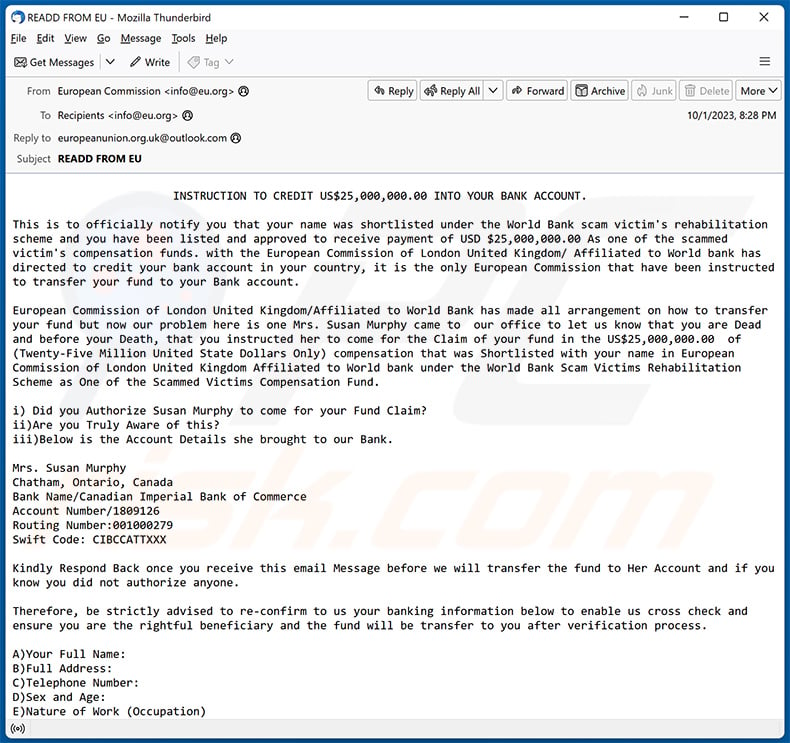
Subject: READD FROM EU
INSTRUCTION TO CREDIT US$25,000,000.00 INTO YOUR BANK ACCOUNT.This is to officially notify you that your name was shortlisted under the World Bank scam victim's rehabilitation scheme and you have been listed and approved to receive payment of USD $25,000,000.00 As one of the scammed victim's compensation funds. with the European Commission of London United Kingdom/ Affiliated to World bank has directed to credit your bank account in your country, it is the only European Commission that have been instructed to transfer your fund to your Bank account.
European Commission of London United Kingdom/Affiliated to World Bank has made all arrangement on how to transfer your fund but now our problem here is one Mrs. Susan Murphy came to our office to let us know that you are Dead and before your Death, that you instructed her to come for the Claim of your fund in the US$25,000,000.00 of (Twenty-Five Million United State Dollars Only) compensation that was Shortlisted with your name in European Commission of London United Kingdom Affiliated to World bank under the World Bank Scam Victims Rehabilitation Scheme as One of the Scammed Victims Compensation Fund.
i) Did you Authorize Susan Murphy to come for your Fund Claim?
ii)Are you Truly Aware of this?
iii)Below is the Account Details she brought to our Bank.Mrs. Susan Murphy
Chatham, Ontario, Canada
Bank Name/Canadian Imperial Bank of Commerce
Account Number/1809126
Routing Number:001000279
Swift Code: CIBCCATTXXXKindly Respond Back once you receive this email Message before we will transfer the fund to Her Account and if you know you did not authorize anyone.
Therefore, be strictly advised to re-confirm to us your banking information below to enable us cross check and ensure you are the rightful beneficiary and the fund will be transfer to you after verification process.
A)Your Full Name:
B)Full Address:
C)Telephone Number:
D)Sex and Age:
E)Nature of Work (Occupation)
F)A copy of passport:
J)Bank name:
H)Account Number:
I)Swift Code:We await your urgent response.
Yours Faithfully
Ms. Ursula von der Leyen
President of the European Commission
Sample 9:
Text presented within:
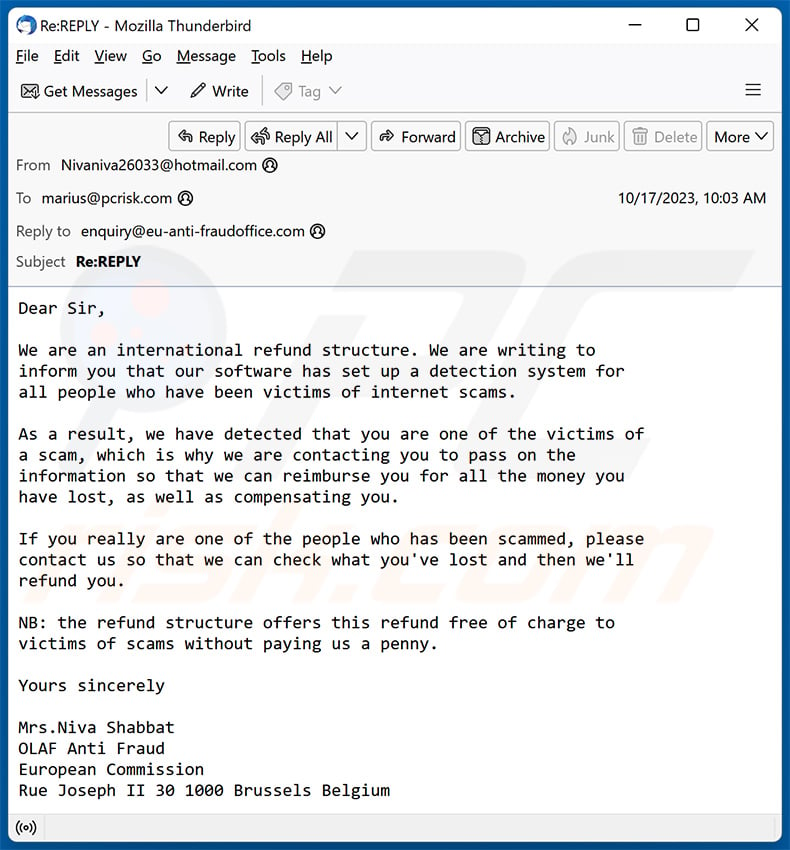
Subject: Re:REPLY
Dear Sir,We are an international refund structure. We are writing to
inform you that our software has set up a detection system for
all people who have been victims of internet scams.As a result, we have detected that you are one of the victims of
a scam, which is why we are contacting you to pass on the
information so that we can reimburse you for all the money you
have lost, as well as compensating you.If you really are one of the people who has been scammed, please
contact us so that we can check what you've lost and then we'll
refund you.NB: the refund structure offers this refund free of charge to
victims of scams without paying us a penny.Yours sincerely
Mrs.Niva Shabbat
OLAF Anti Fraud
European Commission
Rue Joseph II 30 1000 Brussels Belgium
Sample 10:
Text presented within:
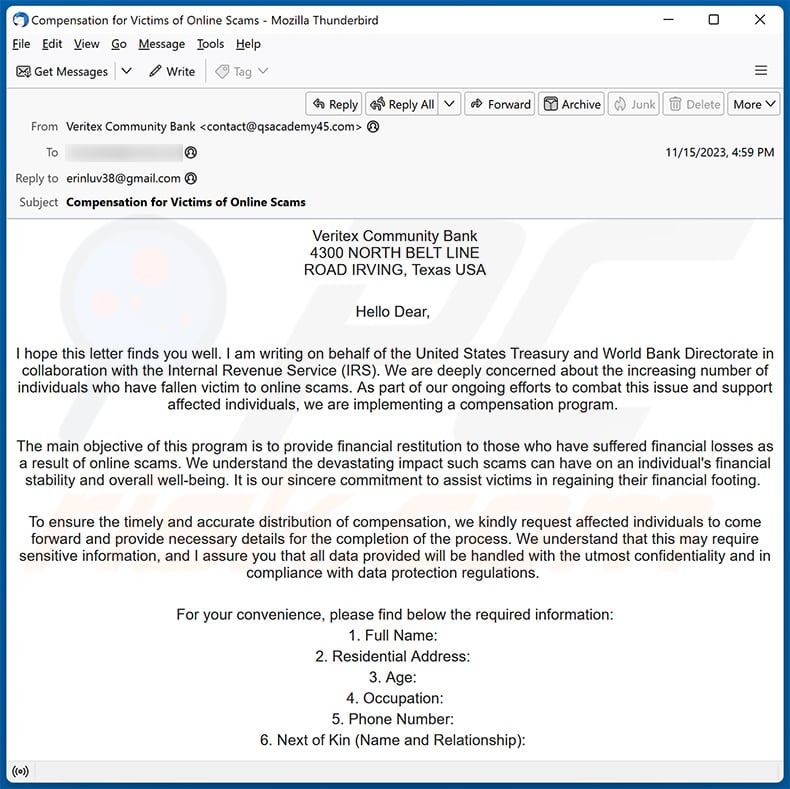
Subject: Compensation for Victims of Online Scams
Veritex Community Bank
4300 NORTH BELT LINE
ROAD IRVING, Texas USAHello Dear,
I hope this letter finds you well. I am writing on behalf of the United States Treasury and World Bank Directorate in collaboration with the Internal Revenue Service (IRS). We are deeply concerned about the increasing number of individuals who have fallen victim to online scams. As part of our ongoing efforts to combat this issue and support affected individuals, we are implementing a compensation program.
The main objective of this program is to provide financial restitution to those who have suffered financial losses as a result of online scams. We understand the devastating impact such scams can have on an individual's financial stability and overall well-being. It is our sincere commitment to assist victims in regaining their financial footing.
To ensure the timely and accurate distribution of compensation, we kindly request affected individuals to come forward and provide necessary details for the completion of the process. We understand that this may require sensitive information, and I assure you that all data provided will be handled with the utmost confidentiality and in compliance with data protection regulations.
For your convenience, please find below the required information:
1. Full Name:
2. Residential Address:
3. Age:
4. Occupation:
5. Phone Number:
6. Next of Kin (Name and Relationship):Your prompt response in furnishing the above details will enable us to expedite the compensation process and ensure that deserving individuals receive the support they need as soon as possible. We understand the urgency of this matter and are committed to providing a seamless experience for all participants.
To facilitate the verification process, victims may be required to provide supporting documentation, such as scam-related emails or receipts, if available. This will aid in confirming the authenticity of the claims and expediting the compensation disbursement.
We sincerely believe that this compensation program will assist in mitigating the financial hardships caused by online scams. By taking collective action, we can work towards a safer online environment for individuals and businesses alike.
Should you require any further information or have any questions, please do not hesitate to contact us. We are here to assist you throughout this process.
Thank you for your cooperation and dedication to addressing this critical issue. Together, we can make a difference in the lives of those affected by online scams.
Thank you for choosing Valley Bank
Best Regards,
Mr. Malcolm Holland
Veritex Community Bank
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Scam Victim Compensation Funds scam email?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
This is a non-targeted email. All recipients received the same email.
I have provided my personal information when tricked by this email, what should I do?
If you have provided any login information, change your passwords as soon as possible (especially if you use one password for two or more accounts). If you have sent your credit card details, ID card information, or other details to scammers, contact the corresponding authorities as soon as possible.
I have downloaded and opened a malicious file attached to an email, is my computer infected?
If you have opened an executable file, your computer is probably already infected. Malicious MS Office documents, archives, and other files usually cannot infect computers until users take additional steps (e.g., enable macros commands in malicious documents, extract malicious files from archive files and then open them, etc.).
I have read the email but did not open the attachment, is my computer infected?
It is safe to open emails even when they have malicious files attached to them (or include malicious links).
Will Combo Cleaner remove malware infections that were present in email attachment?
Yes, Combo Cleaner can detect and remove almost all known malware. Usually, high-end malware hides deep in the operating system. Therefore, it is required to run a full system scan to remove malware of this kind.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion