How to remove the RedEnergy malware from your computer
TrojanAlso Known As: RedEnergy Stealer-as-a-Ransomware
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is RedEnergy Stealer?
RedEnergy is the name of an information stealer that employs a fake update campaign to target multiple industry sectors. This malicious software has the capability to extract information from different web browsers, allowing sensitive data to be stolen. Additionally, it incorporates various modules to facilitate ransomware activities.
Since RedEnergy possesses the unique ability to function as both a stealer and ransomware, it is categorized as Stealer-as-a-Ransomware.
More about RedEnergy Stealer
When triggered, the malicious RedEnergy executable disguises itself as a genuine browser update, effectively camouflaging its true nature. It cunningly presents itself as a legitimate update from well-known browsers like Google Chrome, Microsoft Edge, Firefox, and Opera, aiming to deceive unsuspecting users.
The malware then deposits four files (two temporary files and two executables) onto the targeted system. Among these files, one serves as the malicious payload. Concurrently, the malware initiates an additional background process representing the malicious payload. As this payload is executed, it shows an insulting message to the victim.
Also, RedEnergy incorporates a persistence mechanism that allows it to remain on an infected system even after restarting or shutting down. This mechanism ensures that the malware remains active and can continue its malicious activities without interruption.
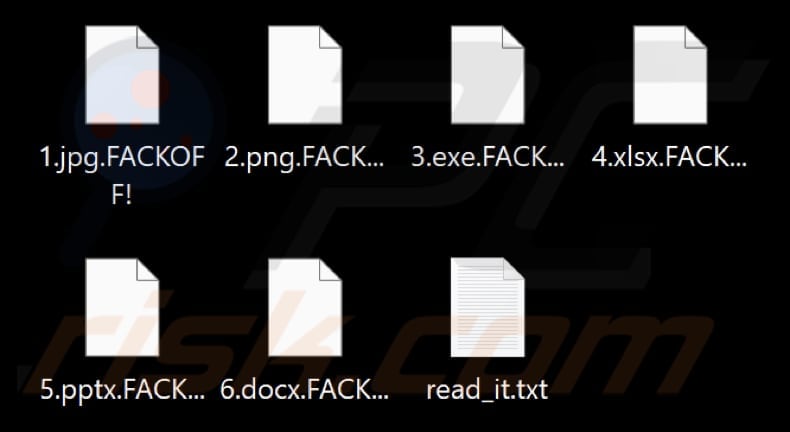
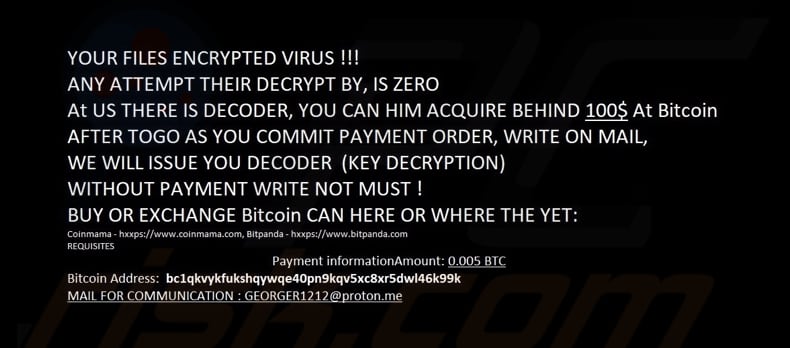
As part of its operation, RedEnergy integrates ransomware modules into its payload, encrypting the victim's data and appending the ".FACKOFF!" extension to the names of all encrypted files. It then presents the victim with a ransom message ("read_it.txt") demanding payment to restore access to the files and changes the desktop wallpaper.
Another action performed by the ransomware modules is the deletion of data from the shadow drive, effectively eliminating any potential backups.
Additionally, the malicious executable modifies the desktop.ini file, which holds important configuration settings for file system folders. Through this modification, RedEnergy gains the ability to manipulate the appearance of file system folders, potentially enhancing its ability to hide its presence and actions on the compromised system.
Lastly, RedEnergy is capable of stealing data from various web browsers. This can result in the theft of personal information, login credentials, financial data, online activities, session-related information, and other data.
| Name | RedEnergy Stealer-as-a-Ransomware |
| Threat Type | Information stealer, ransomware |
| Encrypted Files Extension | .FACKOFF! |
| Ransom Demanding Message | read_it.txt |
| Cyber Criminal Contact | georger1212@proton.me |
| Ransom Amount | 0.005 BTC |
| BTC Wallet | bc1qkvykfukshqywqe40pn9kqv5xc8xr5dwl46k99k |
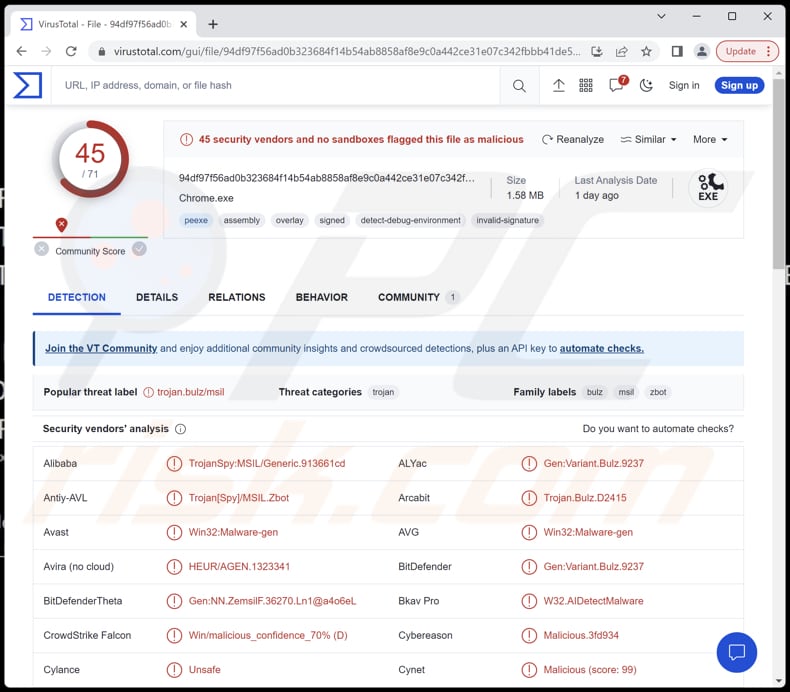
| Detection Names | Avast (Win32:Malware-gen), Combo Cleaner (Gen:Variant.Bulz.9237), Emsisoft (Gen:Variant.Bulz.9237 (B)), Kaspersky (HEUR:Trojan-Spy.MSIL.Zbot.gen), Microsoft (Trojan:Win32/Casdet!rfn), Full List (VirusTotal) |
| Symptoms | Cannot open files stored on your computer, previously functional files now have a different extension (.FACKOFF!). A ransom demand message is displayed on your desktop. |
| Distribution methods | Malicious links on Linkedin sites, fake software updates, and fake websites. Other distirbution channels may include infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, data encryption. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
In conclusion, RedEnergy is a sophisticated malware that operates as a stealer and ransomware. It employs deceptive techniques, such as masquerading as legitimate browser updates and utilizing persistence mechanisms to maintain its presence on infected systems.
With its ability to steal sensitive information, encrypt files, and demand ransom for their release, RedEnergy poses a significant risk to individuals and organizations, underscoring the importance of robust cybersecurity measures and vigilant online behavior.
How did RedEnergy Stealer infiltrate my computer?
RedEnergy employs a deceptive redirection technique to infect computers, targeting industries with notable LinkedIn pages. Users who try to access a targeted company's website through their LinkedIn profile are unknowingly redirected to a malicious site.
Once there, they are prompted to install what appears to be a legitimate browser update. However, they inadvertently download the RedEnergy executable instead of a genuine update.
To further deceive victims, the campaign uses a disguised download domain that poses as a ChatGPT site, enticing users to download a fake offline version of ChatGPT. This fake version also contains a malicious executable used to distribute RedEnergy.
Multiple related campaigns have been discovered, all employing the FAKEUPDATES tactic and reusing infrastructure and tactics to maximize their impact and profits. The cybercriminals responsible for these campaigns target organizations across various industries, leveraging their established reputations and online presence to effectively deceive unsuspecting users.
How to avoid installation of malware?
In order to protect a computer, it is crucial to maintain regular updates for your operating system and software. When dealing with email attachments or encountering suspicious links, especially from unfamiliar or untrusted sources, exercise caution and remain vigilant.
It is also recommended to use reputable antivirus or anti-malware software to provide an additional layer of protection and to conduct regular system scans to identify and address potential threats. In addition, avoid downloading files from untrusted websites and be cautious of pop-up advertisements or deceptive download buttons that may lead to malicious content.
If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Files encrypted by the RedEnergy malware (with the ".FACKOFF!" extension):
Desktop wallpaper changed by RedEnergy:
Ransom note provided by RedEnergy ("read_it.txt"):
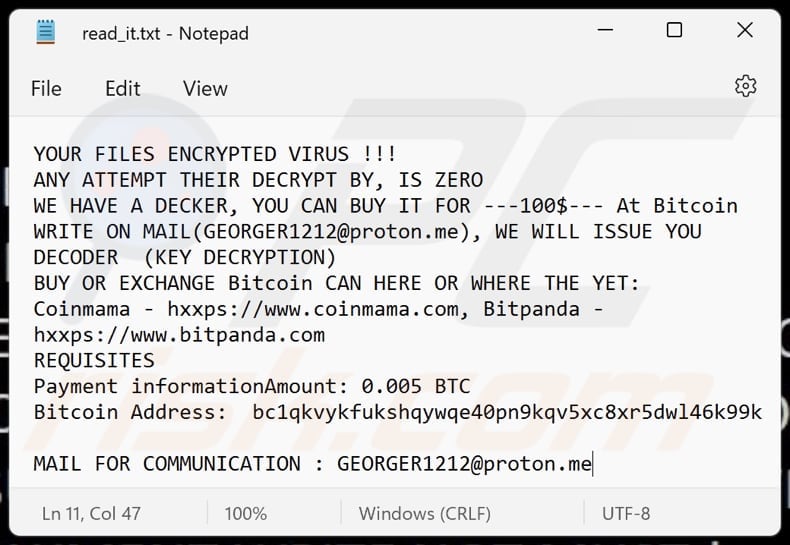
Text in the ransom note and wallpaper:
YOUR FILES ENCRYPTED VIRUS !!!
ANY ATTEMPT THEIR DECRYPT BY, IS ZERO
WE HAVE A DECKER, YOU CAN BUY IT FOR ---100$--- At Bitcoin
WRITE ON MAIL(GEORGER1212@proton.me), WE WILL ISSUE YOU DECODER (KEY DECRYPTION)
BUY OR EXCHANGE Bitcoin CAN HERE OR WHERE THE YET:
Coinmama - hxxps://www.coinmama.com, Bitpanda - hxxps://www.bitpanda.com
REQUISITES
Payment informationAmount: 0.005 BTC
Bitcoin Address: bc1qkvykfukshqywqe40pn9kqv5xc8xr5dwl46k99kMAIL FOR COMMUNICATION : GEORGER1212@proton.me
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is RedEnergy Stealer?
- STEP 1. Manual removal of RedEnergy Stealer malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with RedEnergy malware, should I format my storage device to get rid of it?
If your computer is infected with the RedEnergy malware, formatting your storage device can effectively remove the malware. However, it is recommended to run a thorough scan of your system using reputable antivirus or anti-malware software first. Formatting a storage device will remove all data.
What are the biggest issues that malware can cause?
The consequences of malware can vary depending on its type, ranging from identity theft and financial losses to diminished computer performance and increased vulnerability to additional infections.
What is the purpose of RedEnergy malware?
The purpose of RedEnergy malware is dual-fold. It functions as a data stealer, aiming to extract sensitive information from various web browsers. Additionally, it incorporates ransomware modules, enabling it to encrypt the user's data and demand a ransom for restoring access to the encrypted files.
How to open ".FACKOFF!" files?
Your files have been encrypted due to a ransomware infection, and in order to access them, a decryption process is necessary.
Where should I look for free decryption tools?
In case of a ransomware attack you should check the No More Ransom project website (more information above).
I can pay you a lot of money, can you decrypt files for me?
We do not offer the service of decrypting files encrypted by ransomware. Generally, it is extremely difficult to decrypt such files without the involvement of cybercriminals behind the attack unless there are flaws in the ransomware itself. Therefore, if a third party claims to provide decryption for a fee, they are likely either acting as a middleman or attempting to deceive you.
How did RedEnergy malware infiltrate my computer?
RedEnergy disguises itself as a legitimate browser update and prompts users to install it. Another method is through deceptive redirection techniques, where users attempting to visit a targeted company's website are redirected to a malicious site that initiates malware download. More information is provided in our article.
Will Combo Cleaner protect me from malware?
Combo Cleaner can identify and remove nearly all recognized malware infections. Sophisticated malware often conceals itself deeply within the system. Therefore, a full system scan is essential to ensure the thorough detection and elimination of potential threats.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion