How to recognize fraudulent emails like "Business Proposal"
Phishing/ScamAlso Known As: Business Proposal advance-fee scam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of scam is "Business Proposal"?
Upon reviewing the email, we have determined that it is a fraudulent message masquerading as a business proposal. The scammers intend to entice recipients into participating in an advance-fee scheme. Furthermore, it is imperative to exercise caution and refrain from disclosing any information in response to such deceptive communications or sending money.
More about the "Business Proposal" scam email
The email begins with an attempt to establish credibility by claiming to be from a specific bank in South Africa. The sender alleges to have discovered an unclaimed sum of USD 16 million belonging to a deceased client who supposedly passed away during the COVID-19 pandemic. They propose that the recipient pose as the deceased client's next of kin in order to facilitate the release of the funds.
The promise of a 50% share of the funds is used as bait to entice the recipient into participating in the scam. The urgency of the matter and the request for confidentiality are common tactics employed to pressure the victim into responding quickly without seeking verification or advice.
Finally, the email provides a contact email address for further communication, indicating a desire to move the scam into a more private setting. Overall, the email is designed to manipulate the recipient into providing personal and financial information or making payments upfront, with the false promise of a lucrative reward.
Recovery of lost funds can be extremely difficult, if not impossible, and victims may also become targets for future scams as their information is circulated within criminal networks. Falling for such scams can have devastating consequences for victims, impacting their financial stability and sense of security.
| Name | Business Proposal Email Scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Recipients are promised a significant sum of money in exchange for their assistance |
| Disguise | Letter from a person named Ibrahim Mustafa regarding a business proposal |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Similar scams in general
Emails of this kind typically have an urgent or enticing subject line, aiming to grab the recipient's attention. The body of the email usually contains a fabricated story or proposal, often involving a large sum of money and a sense of urgency. Scammers frequently request personal or financial information and emphasize the need for confidentiality.
Grammatical errors, spelling mistakes, and inconsistencies in language or formatting are other common indicators of fraudulent activity. These emails exploit human vulnerabilities such as greed, curiosity, and urgency to deceive recipients into providing sensitive information or making payments.
Examples of similar scams are "Western Union Money Transfer", "Publishers Clearing House", and "Scam Relief Fund Initiative". It is important to be aware that cybercriminals often employ email as a tool to trick users into infecting their computers.
How do spam campaigns infect computers?
Cybercriminals behind emails intended to deliver malware aim to lure recipients into causing computer infections through malicious attachments or links. These attachments, such as documents or images, may appear harmless but contain malware and infect systems once opened.
Similarly, clicking on links within the email can lead users to fake websites or download pages that distribute malware onto their devices. Not every file received via email can infect computers upon opening. Certain files may necessitate further actions from users to trigger the embedded malware.
For instance, malicious MS Office documents cannot introduce malware unless users enable macros commands. Some examples of types of files used to distribute malware are executable files (.exe), script files (.js or .vbs), document files (.docx or .pdf), compressed files (.zip or .rar), and shortcut files (.lnk).
How to avoid installation of malware?
Exercise caution when encountering links or attachments from unknown addresses, particularly if emails appear unexpected or irrelevant. Obtain files and applications from reputable sources such as official websites or trusted app stores. Avoid clicking on dubious links, pop-ups, or ads.
Regularly update your software and operating system to mitigate potential vulnerabilities. Refrain from downloading pirated software or using cracking tools to activate software. Employ dependable antivirus or anti-malware software as an added layer of protection.
If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "Business Proposal" email letter:
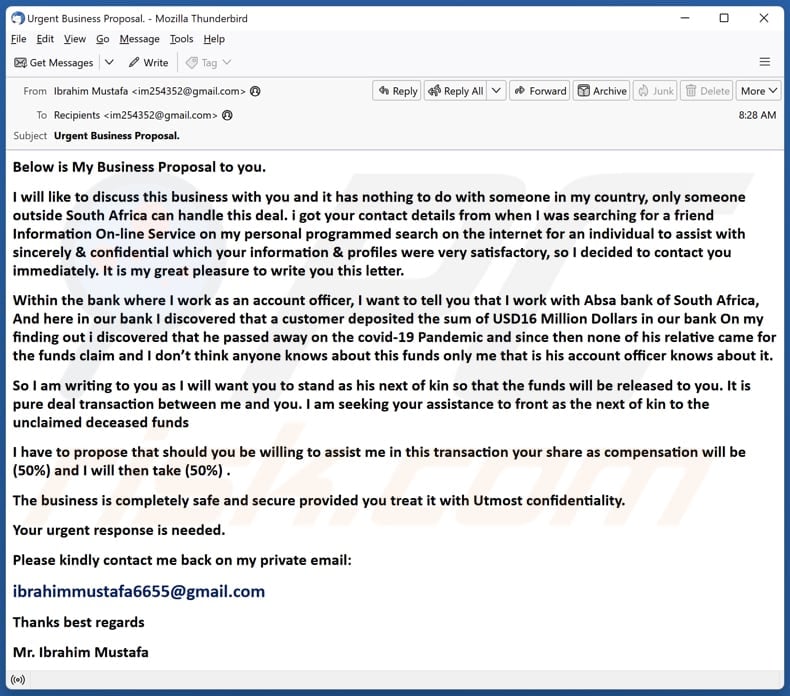
Subject: Urgent Business Proposal.
Below is My Business Proposal to you.
I will like to discuss this business with you and it has nothing to do with someone in my country, only someone outside South Africa can handle this deal. i got your contact details from when I was searching for a friend Information On-line Service on my personal programmed search on the internet for an individual to assist with sincerely & confidential which your information & profiles were very satisfactory, so I decided to contact you immediately. It is my great pleasure to write you this letter.
Within the bank where I work as an account officer, I want to tell you that I work with Absa bank of South Africa, And here in our bank I discovered that a customer deposited the sum of USD16 Million Dollars in our bank On my finding out i discovered that he passed away on the covid-19 Pandemic and since then none of his relative came for the funds claim and I don’t think anyone knows about this funds only me that is his account officer knows about it.
So I am writing to you as I will want you to stand as his next of kin so that the funds will be released to you. It is pure deal transaction between me and you. I am seeking your assistance to front as the next of kin to the unclaimed deceased funds
I have to propose that should you be willing to assist me in this transaction your share as compensation will be (50%) and I will then take (50%) .
The business is completely safe and secure provided you treat it with Utmost confidentiality.
Your urgent response is needed.
Please kindly contact me back on my private email:
ibrahimmustafa6655@gmail.com
Thanks best regards
Mr. Ibrahim Mustafa
Other examples of business proposal-themed spam emails:
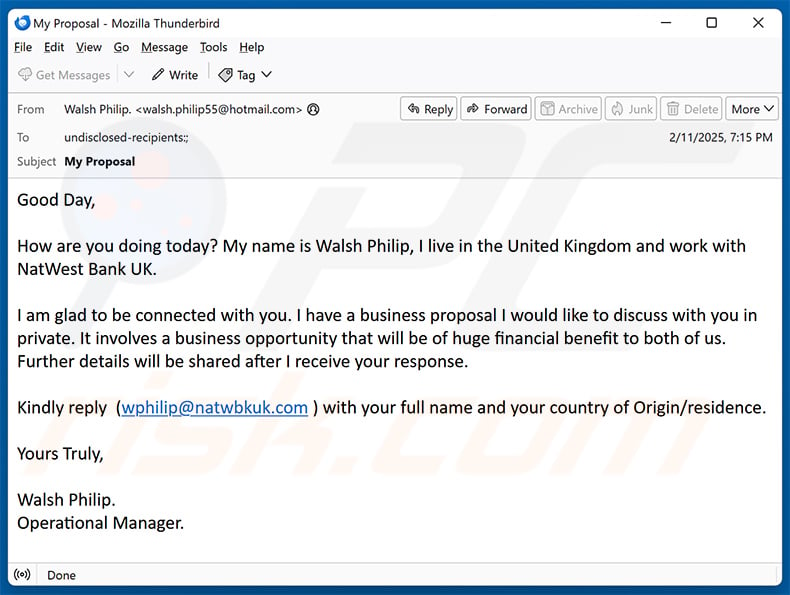
Sample 1:
Text presented within:
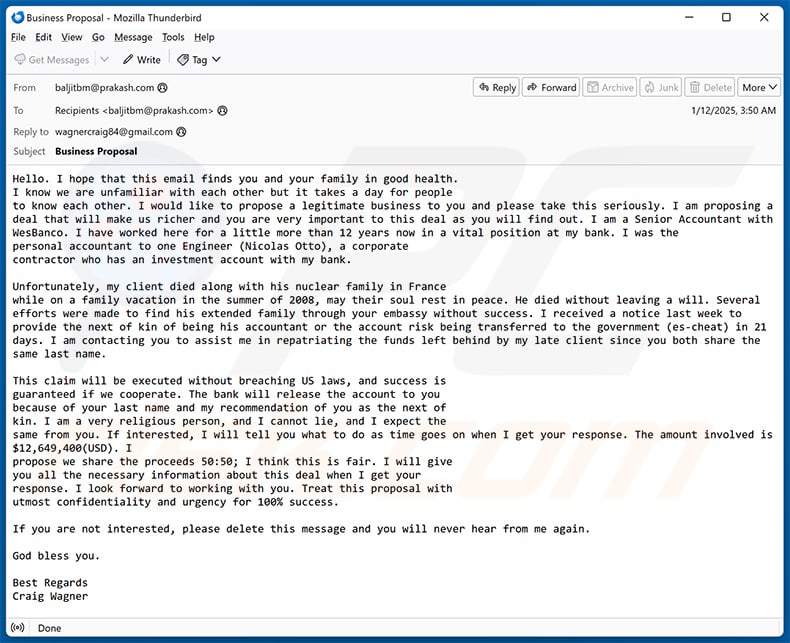
Subject: Business Proposal
Hello. I hope that this email finds you and your family in good health.
I know we are unfamiliar with each other but it takes a day for people
to know each other. I would like to propose a legitimate business to you and please take this seriously. I am proposing a deal that will make us richer and you are very important to this deal as you will find out. I am a Senior Accountant with WesBanco. I have worked here for a little more than 12 years now in a vital position at my bank. I was the
personal accountant to one Engineer (Nicolas Otto), a corporate
contractor who has an investment account with my bank.Unfortunately, my client died along with his nuclear family in France
while on a family vacation in the summer of 2008, may their soul rest in peace. He died without leaving a will. Several efforts were made to find his extended family through your embassy without success. I received a notice last week to provide the next of kin of being his accountant or the account risk being transferred to the government (es-cheat) in 21 days. I am contacting you to assist me in repatriating the funds left behind by my late client since you both share the same last name.This claim will be executed without breaching US laws, and success is
guaranteed if we cooperate. The bank will release the account to you
because of your last name and my recommendation of you as the next of
kin. I am a very religious person, and I cannot lie, and I expect the
same from you. If interested, I will tell you what to do as time goes on when I get your response. The amount involved is $12,649,400(USD). I
propose we share the proceeds 50:50; I think this is fair. I will give
you all the necessary information about this deal when I get your
response. I look forward to working with you. Treat this proposal with
utmost confidentiality and urgency for 100% success.If you are not interested, please delete this message and you will never hear from me again.
God bless you.
Best Regards
Craig Wagner
Sample 2:
Text presented within:
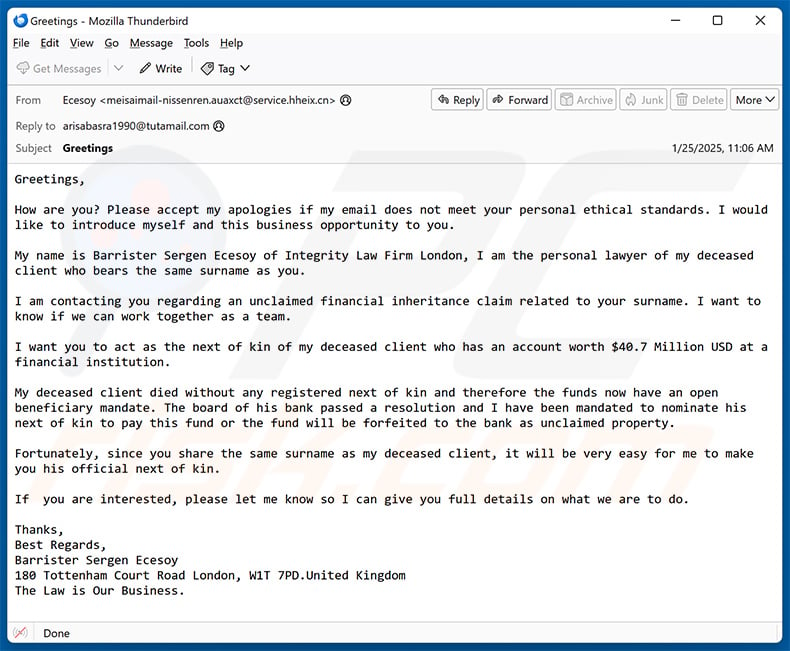
Greetings,
How are you? Please accept my apologies if my email does not meet your personal ethical standards. I would like to introduce myself and this business opportunity to you.
My name is Barrister Sergen Ecesoy of Integrity Law Firm London, I am the personal lawyer of my deceased client who bears the same surname as you.
I am contacting you regarding an unclaimed financial inheritance claim related to your surname. I want to know if we can work together as a team.
I want you to act as the next of kin of my deceased client who has an account worth $40.7 Million USD at a financial institution.
My deceased client died without any registered next of kin and therefore the funds now have an open beneficiary mandate. The board of his bank passed a resolution and I have been mandated to nominate his next of kin to pay this fund or the fund will be forfeited to the bank as unclaimed property.
Fortunately, since you share the same surname as my deceased client, it will be very easy for me to make you his official next of kin.
If you are interested, please let me know so I can give you full details on what we are to do.
Thanks,
Best Regards,
Barrister Sergen Ecesoy
180 Tottenham Court Road London, W1T 7PD.United Kingdom
The Law is Our Business.
Sample 3:
Text presented within:
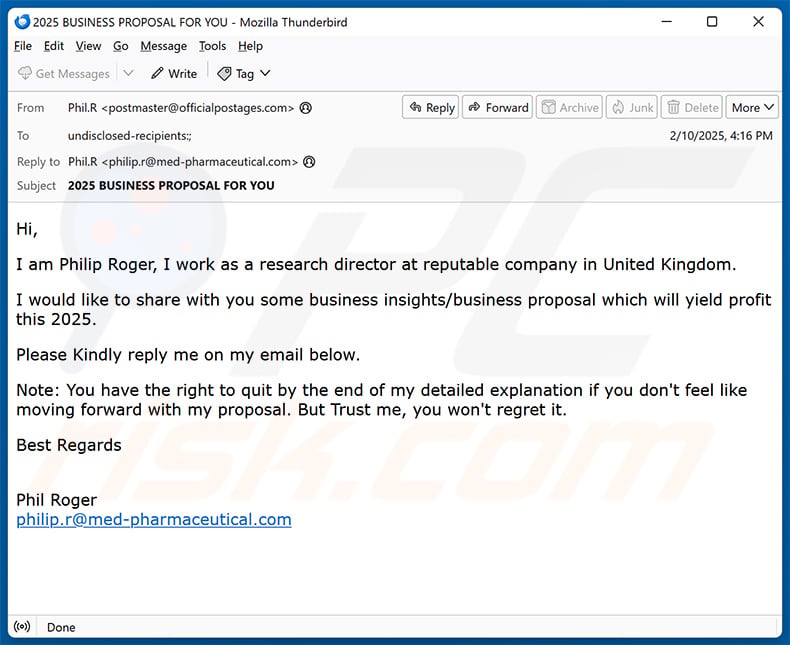
Subject: 2025 BUSINESS PROPOSAL FOR YOU
Hi,I am Philip Roger, I work as a research director at reputable company in United Kingdom.
I would like to share with you some business insights/business proposal which will yield profit this 2025.
Please Kindly reply me on my email below.
Note: You have the right to quit by the end of my detailed explanation if you don't feel like moving forward with my proposal. But Trust me, you won't regret it.
Best Regards
Phil Roger
philip.r@med-pharmaceutical.com
Sample 4:
Text presented within:
Subject: My Proposal
Good Day,How are you doing today? My name is Walsh Philip, I live in the United Kingdom and work with NatWest Bank UK.
I am glad to be connected with you. I have a business proposal I would like to discuss with you in private. It involves a business opportunity that will be of huge financial benefit to both of us.
Further details will be shared after I receive your response.Kindly reply (wphilip@natwbkuk.com ) with your full name and your country of Origin/residence.
Yours Truly,
Walsh Philip.
Operational Manager.
Sample 5:
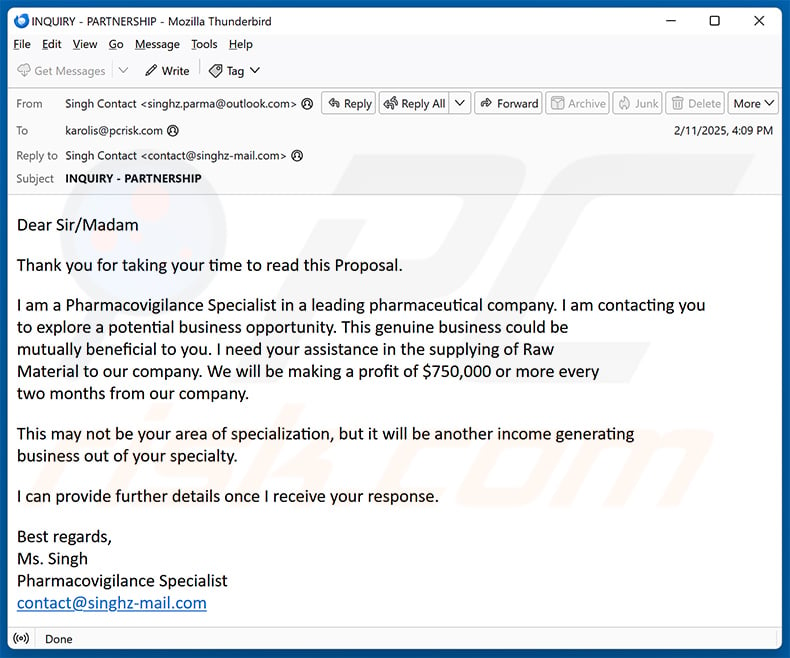
Text presented within:
Subject: INQUIRY - PARTNERSHIP
Dear Sir/Madam
Thank you for taking your time to read this Proposal.
I am a Pharmacovigilance Specialist in a leading pharmaceutical company. I am contacting you
to explore a potential business opportunity. This genuine business could be
mutually beneficial to you. I need your assistance in the supplying of Raw
Material to our company. We will be making a profit of $750,000 or more every
two months from our company.This may not be your area of specialization, but it will be another income generating
business out of your specialty.I can provide further details once I receive your response.
Best regards,
Ms. Singh
Pharmacovigilance Specialist
contact@singhz-mail.com
Sample 6:
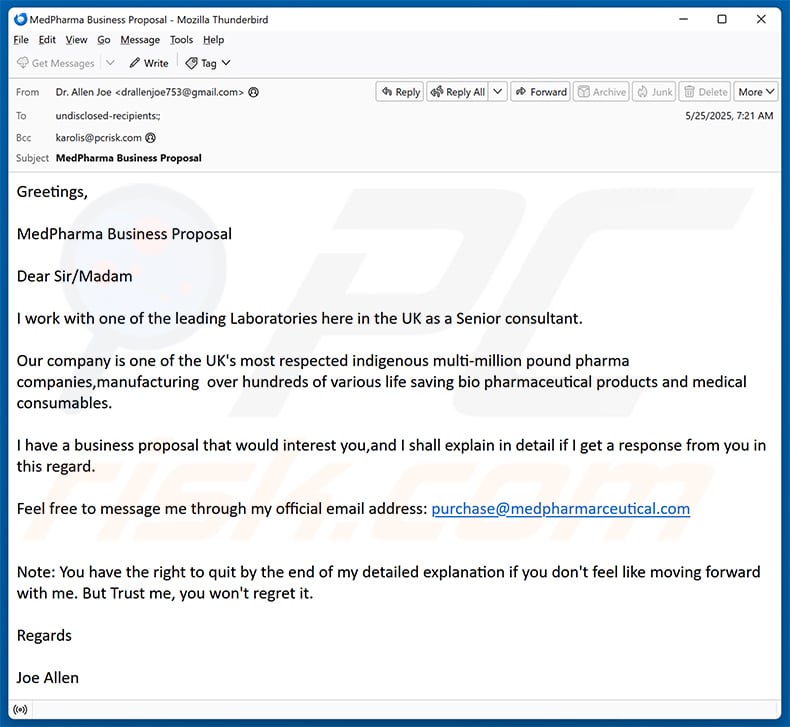
Text presented within:
Subject: MedPharma Business Proposal
Greetings,
MedPharma Business Proposal
Dear Sir/Madam
I work with one of the leading Laboratories here in the UK as a Senior consultant.
Our company is one of the UK's most respected indigenous multi-million pound pharma companies,manufacturing over hundreds of various life saving bio pharmaceutical products and medical consumables.
I have a business proposal that would interest you,and I shall explain in detail if I get a response from you in this regard.
Feel free to message me through my official email address: purchase@medpharmarceutical.com
Note: You have the right to quit by the end of my detailed explanation if you don't feel like moving forward with me. But Trust me, you won't regret it.
Regards
Joe Allen
Sample 7:
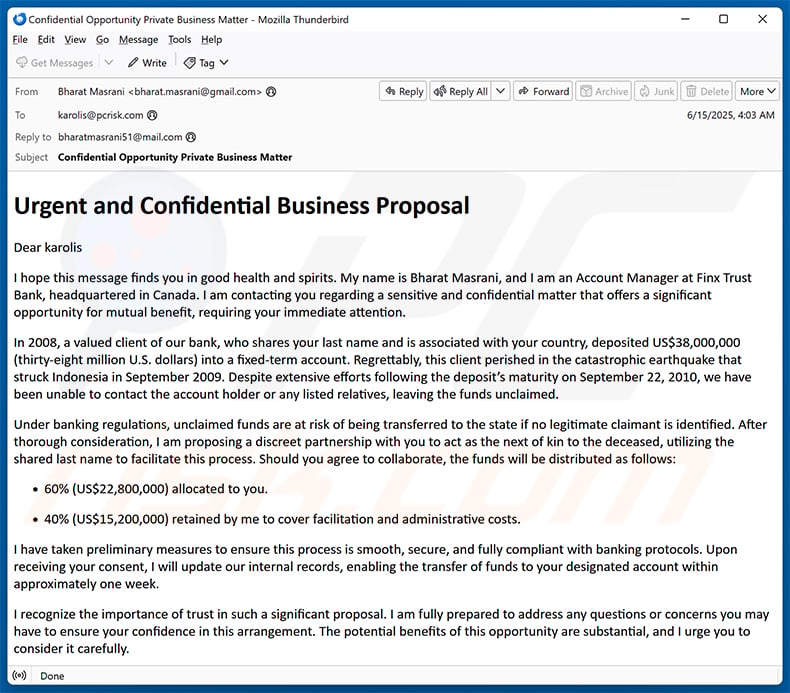 Text presented within:
Text presented within:
Subject: Confidential Opportunity Private Business Matter
Urgent and Confidential Business Proposal
Dear -
I hope this message finds you in good health and spirits. My name is Bharat Masrani, and I am an Account Manager at Finx Trust Bank, headquartered in Canada. I am contacting you regarding a sensitive and confidential matter that offers a significant opportunity for mutual benefit, requiring your immediate attention.
In 2008, a valued client of our bank, who shares your last name and is associated with your country, deposited US$38,000,000 (thirty-eight million U.S. dollars) into a fixed-term account. Regrettably, this client perished in the catastrophic earthquake that struck Indonesia in September 2009. Despite extensive efforts following the deposit's maturity on September 22, 2010, we have been unable to contact the account holder or any listed relatives, leaving the funds unclaimed.
Under banking regulations, unclaimed funds are at risk of being transferred to the state if no legitimate claimant is identified. After thorough consideration, I am proposing a discreet partnership with you to act as the next of kin to the deceased, utilizing the shared last name to facilitate this process. Should you agree to collaborate, the funds will be distributed as follows:
60% (US$22,800,000) allocated to you.
40% (US$15,200,000) retained by me to cover facilitation and administrative costs.
I have taken preliminary measures to ensure this process is smooth, secure, and fully compliant with banking protocols. Upon receiving your consent, I will update our internal records, enabling the transfer of funds to your designated account within approximately one week.
I recognize the importance of trust in such a significant proposal. I am fully prepared to address any questions or concerns you may have to ensure your confidence in this arrangement. The potential benefits of this opportunity are substantial, and I urge you to consider it carefully.
To proceed or seek further clarification, please contact me directly at my personal email: bharatmasrani51@mail.com
For reasons of security and confidentiality, I kindly request your response within five business days.
Thank you for your time and careful consideration. I look forward to your prompt reply and the prospect of working together on this exceptional opportunity.
Sincerely,
Bharat Masrani
Account Manager
Finx Trust Bank, Canada
Sample 8:
Text presented within:
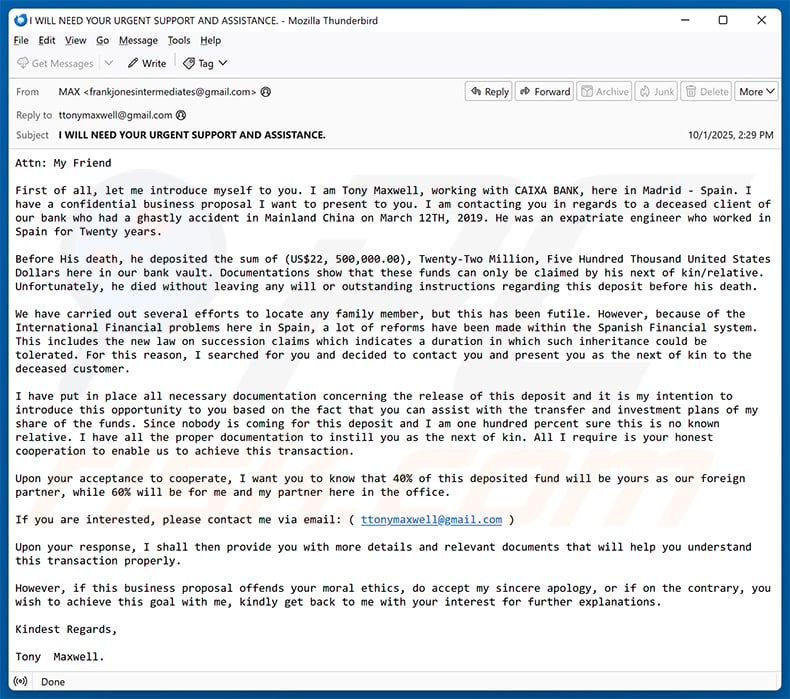
Subject: I WILL NEED YOUR URGENT SUPPORT AND ASSISTANCE.
Attn: My Friend
First of all, let me introduce myself to you. I am Tony Maxwell, working with CAIXA BANK, here in Madrid - Spain. I have a confidential business proposal I want to present to you. I am contacting you in regards to a deceased client of our bank who had a ghastly accident in Mainland China on March 12TH, 2019. He was an expatriate engineer who worked in Spain for Twenty years.
Before His death, he deposited the sum of (US$22, 500,000.00), Twenty-Two Million, Five Hundred Thousand United States Dollars here in our bank vault. Documentations show that these funds can only be claimed by his next of kin/relative. Unfortunately, he died without leaving any will or outstanding instructions regarding this deposit before his death.
We have carried out several efforts to locate any family member, but this has been futile. However, because of the International Financial problems here in Spain, a lot of reforms have been made within the Spanish Financial system. This includes the new law on succession claims which indicates a duration in which such inheritance could be tolerated. For this reason, I searched for you and decided to contact you and present you as the next of kin to the deceased customer.
I have put in place all necessary documentation concerning the release of this deposit and it is my intention to introduce this opportunity to you based on the fact that you can assist with the transfer and investment plans of my share of the funds. Since nobody is coming for this deposit and I am one hundred percent sure this is no known relative. I have all the proper documentation to instill you as the next of kin. All I require is your honest cooperation to enable us to achieve this transaction.
Upon your acceptance to cooperate, I want you to know that 40% of this deposited fund will be yours as our foreign partner, while 60% will be for me and my partner here in the office.
If you are interested, please contact me via email: ( ttonymaxwell@gmail.com )
Upon your response, I shall then provide you with more details and relevant documents that will help you understand this transaction properly.
However, if this business proposal offends your moral ethics, do accept my sincere apology, or if on the contrary, you wish to achieve this goal with me, kindly get back to me with your interest for further explanations.
Kindest Regards,
Tony Maxwell.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Business Proposal advance-fee scam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:

What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Phishing attacks typically entail the mass distribution of emails to a wide array of recipients, with the aim of ensnaring unsuspecting individuals in the scam. These emails are often sent out indiscriminately, utilizing email addresses sourced from public platforms, leaked databases, or prior data breaches.
I have provided my personal information when tricked by this email, what should I do?
If you have shared banking or credit card details, notify your bank or credit card provider. For ID card disclosures, inform the local government agency handling identity theft. Also, mark the email as spam or phishing with your service provider.
I have downloaded and opened a malicious file attached to an email, is my computer infected?
The risk level differs based on the file type. For example, executing an executable file poses a significant risk of infection, while document files like .pdf or .doc are less likely to cause immediate harm.
I have sent cryptocurrency to the address presented in such email, can I get my money back?
Cryptocurrency transactions are fundamentally untraceable, rendering their reversal nearly impossible.
I have read the email but did not open the attachment, is my computer infected?
Simply opening an email does not pose a risk. However, clicking on links or opening attached files can lead to computer infections.
Will Combo Cleaner remove malware infections that were present in email attachment?
Combo Cleaner is capable of detecting and removing the majority of known malware infections. Advanced malware often hides deeply within the system. Therefore, conducting a thorough system scan is essential to eradicate hidden threats.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion