Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is OctoRAT?
OctoRAT is a remote access Trojan built on the .NET platform. The malware supports over 70 commands, employs persistence methods, and has various ways to bypass UAC and elevate privileges, as well as broad information-gathering capabilities. The functionality and overall design indicate that it is likely offered as a Malware‑as‑a‑Service on underground markets.
More about OctoRAT
When OctoRAT is executed, it performs a setup process. One of its first actions is loading SQLite database libraries through a specific component. This step is important because modern browsers store sensitive data, such as saved passwords, cookies, and browsing history, in SQLite databases.
By loading these libraries, the malware prepares itself to access and extract that information. Next, OctoRAT checks its permission level on the system. It checks with the Windows system to determine whether it currently has admin‑level permissions. If it does not have these privileges, it attempts to escalate them.
The aforementioned attempt involves using the FodHelper UAC bypass. This method exploits a flaw that allows FodHelper.exe to run with elevated privileges. The malware creates a registry entry that tells Windows to launch OctoRAT instead of the real settings handler. When FodHelper.exe runs, it starts the malware with admin rights, without showing a UAC prompt.
Additionally, OctoRAT utilizes the Windows Task Scheduler to ensure it remains running on the system. It creates a task named WindowsUpdate so it looks like a normal Windows process and does not raise suspicion. This task ensures the malware restarts quickly if it gets terminated or removed.
Initial Information Theft
Before OctoRAT connects to its command‑and‑control server, it first steals browser data. This is done early so that attackers can obtain information, even if the malware is discovered (detected) quickly. A built-in module scans SQLite databases used by browsers such as Chrome, Firefox, and Edge.
It collects sensitive data, including saved passwords, autofill details, browsing history, and session cookies. Once gathered, the data is sent to the attacker's server.
Main Capabilities
OctoRAT includes a remote desktop control module. It can stream the victim's screen, take screenshots, change capture quality, and simulate mouse or keyboard actions. This enables cybercriminals to manipulate the cursor, click, type, scroll, and control input as if they were using the victim's device.
Also, OctoRAT has process management functions, allowing threat actors to view all running processes, terminate selected ones, or suspend them. It can also list drives and folders, upload or download files, and even execute programs on the infected machine. These capabilities allow the attacker to steal documents, plant malicious files, or run additional tools on the system.
Furthermore, OctoRAT can start and stop a keylogger to record everything the victim types, and it can also monitor the clipboard to capture copied text such as passwords or sensitive data. In addition to stealing data from browsers (as previously mentioned), the RAT can scan the system for installed crypto wallets, extract all wallet information, or target a specific wallet when needed.
The RAT targets various wallet apps, such as Atomic Wallet, Bitcoin Core, Coinomi, Electrum, and Exodus. Wallet folders usually contain data like encrypted private keys, transaction logs, address books, and settings. OctoRAT can collect all folders at once prepare them for exfiltration.
Moveover, OctoRAT can manage Windows services. Cybercriminals can list all services on the system, start specific ones, or stop them. It can also browse registry keys and values (and modify specified values), steal WiFi passwords and network data (e.g., adapter type, connection status and IP addresses), and start and stop SOCKS proxy servers.
In addition to these capabilities, OctoRAT can run scripts, check for Python, install it if missing, and execute Python code directly on the victim's device. It also includes security‑bypass commands that can disable UAC and the Windows Firewall. For self‑management, the malware can update itself or uninstall its components.
Lastly, OctoRAT includes a set of "prank" tools. It can show pop‑up messages, play sounds, flip the screen, swap mouse buttons, eject the CD tray, change the wallpaper, open websites, flood the screen with Explorer windows, and more.
| Name | OctoRAT remote access trojan |
| Threat Type | Remote Access Trojan |
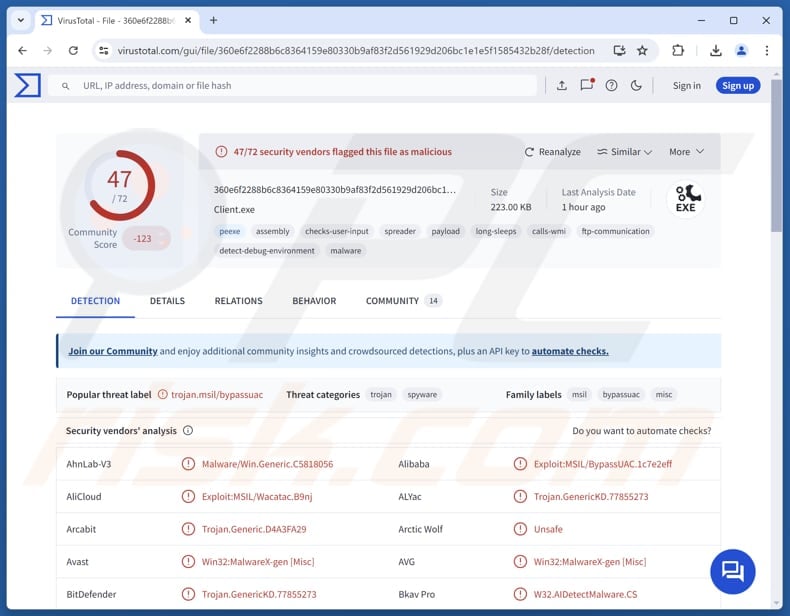
| Detection Names | Avast (Win32:MalwareX-gen [Misc]), Combo Cleaner (Trojan.GenericKD.77855273), ESET-NOD32 (MSIL/Spy.Agent.FKR Trojan), Kaspersky (HEUR:Exploit.MSIL.BypassUAC.c), Microsoft (Trojan:MSIL/Vigorf.A), Full List (VirusTotal) |
| Symptoms | Remote Administration Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Possible distribution methods | Malicious Visual Studio Code extension, Anivia loader |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet, additional infections, monetary loss (including cryptocurrency theft), identity theft, and more. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
OctoRAT is a powerful and stealthy remote access Trojan designed to control the infected system, steal data, and perform other malicious activities. Its wide range of commands, combined with evasion features, makes it a significant threat to both system security and personal data. If present on a device, the malware should be eliminated immediately.
Examples of other RATs targeting Windows are ScoringMathTea, PatoRAT, and STD.
How did OctoRAT infiltrate my computer?
OctoRAT spreads through a malicious VS Code extension uploaded to the official VSCode Marketplace. This extension serves as a tool for executing a dropper (called Anivia), which appears legitimate but secretly executes hidden code. The extension downloads a VBScript dropper named Anivia.vbs, which then launches a PowerShell loader.
This loader decrypts and runs its payload directly in memory, helping the malware avoid detection. It injects the final payload, OctoRAT, into a legitimate Windows process.
How to avoid installation of malware?
Do not use pirated software, cracking tools, or key generators. Download apps and files from official web pages or app stores. Avoid opening links or files in suspicious (e.g., irrelevant or unexpected) emails or other messages from unknown senders. Regularly update the system and installed software.
Do not trust advertisements, links, buttons, pop-ups, etc., encountered on shady pages, and never permit such sites to send you notifications. Also, use a reliable security tool and run system scans regularly. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
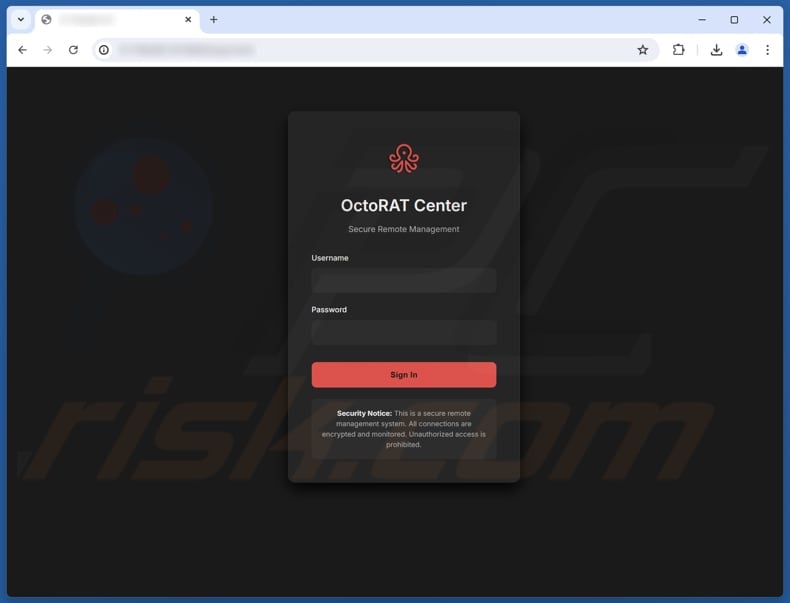
OctoRAT administration panel's login website:
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is OctoRAT?
- STEP 1. Manual removal of OctoRAT malware.
- STEP 2. Check if your computer is clean.
How to remove malware manually?
Manual malware removal is a complicated task - usually it is best to allow antivirus or anti-malware programs to do this automatically. To remove this malware we recommend using Combo Cleaner Antivirus for Windows.
If you wish to remove malware manually, the first step is to identify the name of the malware that you are trying to remove. Here is an example of a suspicious program running on a user's computer:

If you checked the list of programs running on your computer, for example, using task manager, and identified a program that looks suspicious, you should continue with these steps:
 Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:
Download a program called Autoruns. This program shows auto-start applications, Registry, and file system locations:

 Restart your computer into Safe Mode:
Restart your computer into Safe Mode:
Windows XP and Windows 7 users: Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK. During your computer start process, press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, and then select Safe Mode with Networking from the list.

Video showing how to start Windows 7 in "Safe Mode with Networking":
Windows 8 users: Start Windows 8 is Safe Mode with Networking - Go to Windows 8 Start Screen, type Advanced, in the search results select Settings. Click Advanced startup options, in the opened "General PC Settings" window, select Advanced startup.
Click the "Restart now" button. Your computer will now restart into the "Advanced Startup options menu". Click the "Troubleshoot" button, and then click the "Advanced options" button. In the advanced option screen, click "Startup settings".
Click the "Restart" button. Your PC will restart into the Startup Settings screen. Press F5 to boot in Safe Mode with Networking.

Video showing how to start Windows 8 in "Safe Mode with Networking":
Windows 10 users: Click the Windows logo and select the Power icon. In the opened menu click "Restart" while holding "Shift" button on your keyboard. In the "choose an option" window click on the "Troubleshoot", next select "Advanced options".
In the advanced options menu select "Startup Settings" and click on the "Restart" button. In the following window you should click the "F5" button on your keyboard. This will restart your operating system in safe mode with networking.

Video showing how to start Windows 10 in "Safe Mode with Networking":
 Extract the downloaded archive and run the Autoruns.exe file.
Extract the downloaded archive and run the Autoruns.exe file.

 In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.
In the Autoruns application, click "Options" at the top and uncheck "Hide Empty Locations" and "Hide Windows Entries" options. After this procedure, click the "Refresh" icon.

 Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
Check the list provided by the Autoruns application and locate the malware file that you want to eliminate.
You should write down its full path and name. Note that some malware hides process names under legitimate Windows process names. At this stage, it is very important to avoid removing system files. After you locate the suspicious program you wish to remove, right click your mouse over its name and choose "Delete".

After removing the malware through the Autoruns application (this ensures that the malware will not run automatically on the next system startup), you should search for the malware name on your computer. Be sure to enable hidden files and folders before proceeding. If you find the filename of the malware, be sure to remove it.

Reboot your computer in normal mode. Following these steps should remove any malware from your computer. Note that manual threat removal requires advanced computer skills. If you do not have these skills, leave malware removal to antivirus and anti-malware programs.
These steps might not work with advanced malware infections. As always it is best to prevent infection than try to remove malware later. To keep your computer safe, install the latest operating system updates and use antivirus software. To be sure your computer is free of malware infections, we recommend scanning it with Combo Cleaner Antivirus for Windows.
Frequently Asked Questions (FAQ)
My computer is infected with OctoRAT malware, should I format my storage device to get rid of it?
Users do not always need to format their device to clean the infection. Instead, users should run a reputable antivirus or anti‑malware tool, such as Combo Cleaner, to scan the system and safely remove OctoRAT.
What are the biggest issues that malware can cause?
Malware can be used to steal personal data, hijack accounts, encrypt files, spy on activity (e.g., record screen or capture screenshots), control the infected system remotely, execute additional payloads, steal identities, etc.
What is the purpose of OctoRAT?
OctoRAT's purpose is to give attackers full remote control of an infected system so they can steal data, access accounts, manage files, spy on the victim, and perform other malicious activities (including harassment through "prank" features).
How did OctoRAT infiltrate my computer?
OctoRAT is delivered through a fake VS Code extension on the official marketplace. The extension downloads a VBScript dropper called Anivia.vbs, which then launches a PowerShell loader. The loader decrypts and runs the malware entirely in memory and injects the final payload, OctoRAT, into a legitimate Windows process to evade detection.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner can find and eliminate most known malware, but some advanced threats can hide deep in the system. That is why running a full system scan is strongly recommended.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion