Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is the fake Google Docs Offline extension?
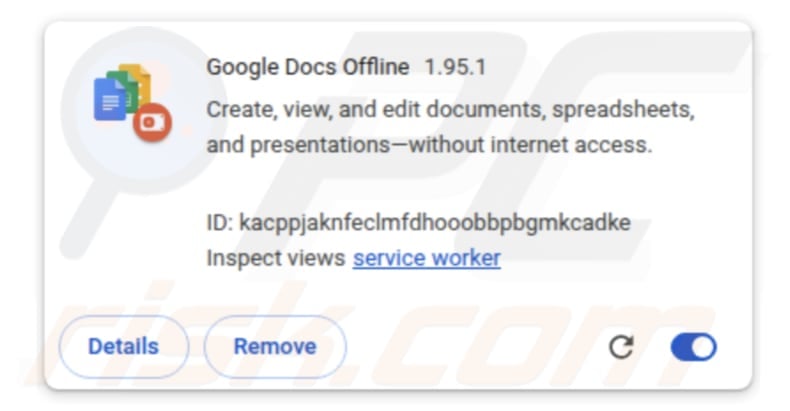
The fake Google Docs Offline extension is a malicious Chrome extension that masquerades as a real Google tool. It is injected as part of a larger attack and is used to spy on users. Once planted, it can log what victims type, steal cookies, login sessions, and capture screenshots. If present on a browser, the fake Google Docs Offline extension should be removed.
Fake Google Docs Offline extension in detail
In attacks (a campaign known as GlassWorm), the fake Google Docs Offline extension appears in the browser as a normal-looking Chrome extension. It is added by another malware (which is already present on infected devices) via a malicious script. Once it appears, it mimics a trusted Google tool with the same name.
The fake Google Docs Offline extension functions as a remote administration Trojan (RAT). This malicious browser extension can grab the full code of active tabs, steal cookies (sometimes of specific sites), copy saved website data, take screenshots of opened tabs, read data stored in the clipboard, and steal saved bookmarks.
Also, the extension can grab up to 5000 entries from the browsing history, collect device and browser details (hardware info, GPU/WebGL data), check what extensions are added, and record everything typed in the browser, including form inputs and page context. All of this stolen data is packaged and sent to cybercriminals.
This malicious extension can expose sensitive information inside the browser. This can include private emails, messages, documents, and other data. Financial activity, such as banking pages, payment details, and crypto account information, can also be exposed if they are accessed in the browser.
Cybercriminals can use this data to take over accounts, steal money, impersonate victims, and engage in other malicious activities. If used on a work device, the extension can lead to a serious company breach.
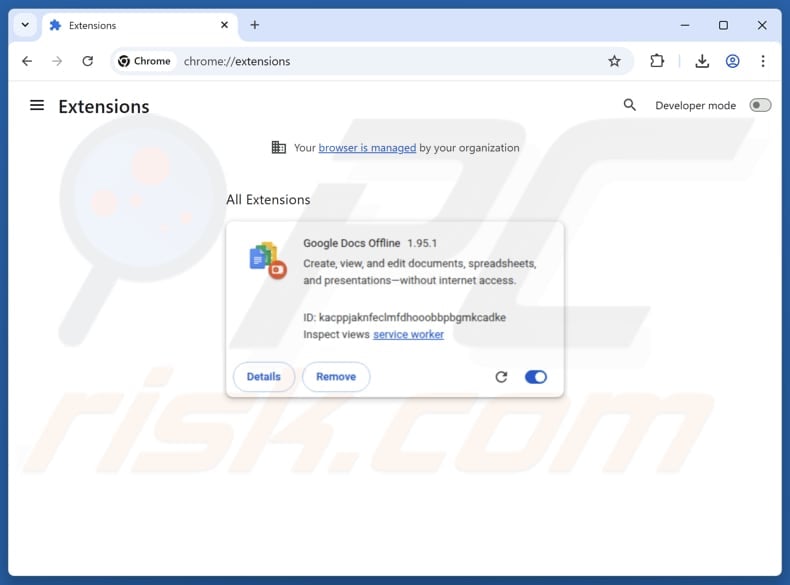
In addition to operating as a RAT, the fake Google Docs Offline extension exploits the "Managed by your organization" feature. Normally, this feature is visible when a company or IT administrator officially controls a browser. Exploiting this feature can prevent normal removal or restrict what the user can change in browser settings.
| Name | Google Docs Offline RAT |
| Threat Type | Remote Access Trojan (RAT) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution methods | GitHub, npm packages, extension stores, fake updates. |
| Damage | Stolen passwords and banking information, identity theft, financial loss, account hijacking. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Conclusion
Overall, this malware is disguised as a legitimate extension and can steal sensitive data, monitor user activity, and enable long-term account compromise without the victim noticing. If the fake Google Docs Offline extension is found in a browser, it (and the associated malicious components) should be eliminated immediately.
How did the fake Google Docs Offline extension infiltrated my browser?
The fake Google Docs Offline extension spreads through a chain attack that leverages compromised sources such as GitHub, npm packages, and extension stores. Threat actors hide malicious code within seemingly normal projects, so they appear safe to install or update.
When the infected software is installed, the hidden code activates and silently injects the fake extension. It can also be delivered through fake or compromised update processes that look legitimate.
How to avoid installation of unwanted applications?
Only download software and applications from verified sources like official websites or well-known app stores, and avoid using cracked programs, pirated apps, or key generators. Be cautious with emails or messages from unknown senders, especially if they include links or attachments, and do not open anything that looks suspicious or untrustworthy.
Also, avoid interacting with pop-ups, ads, or links on unsafe websites, and never allow questionable sites to send browser notifications. Moreover, update your operating system and all installed applications regularly. If your computer is already infected with rogue applications, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Fake Google Docs Offline extension?
- STEP 1. Uninstall applications using Control Panel.
- STEP 2. Remove rogue plug-ins from Google Chrome.
- STEP 3. Remove unwanted extensions from Mozilla Firefox.
- STEP 4. Remove malicious extensions from Safari.
- STEP 5. Remove rogue plug-ins from Microsoft Edge.
Unwanted applications removal:
Windows 11 users:
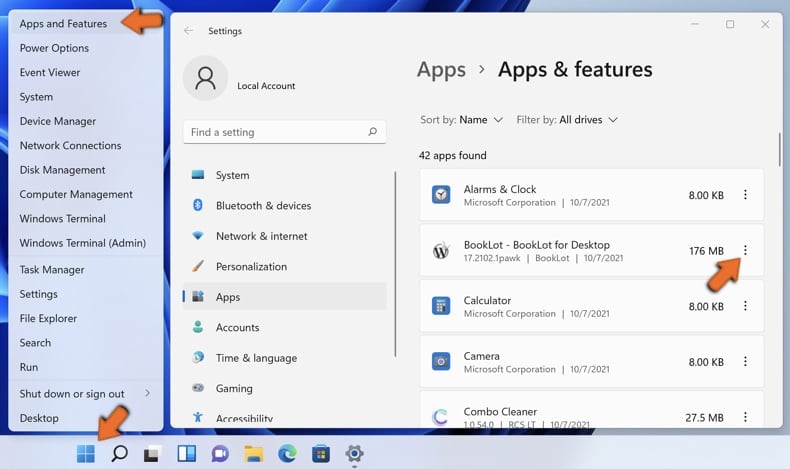
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
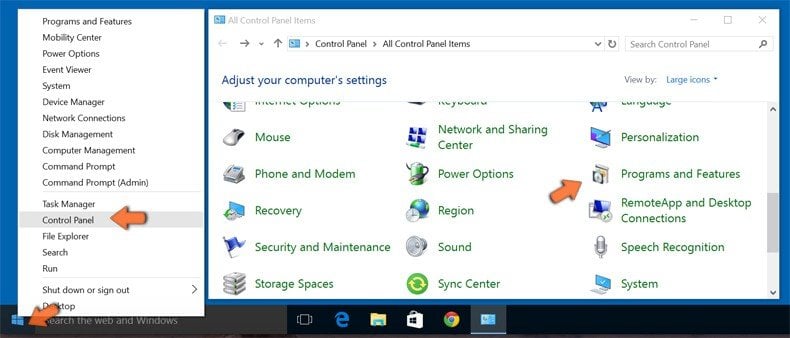
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.
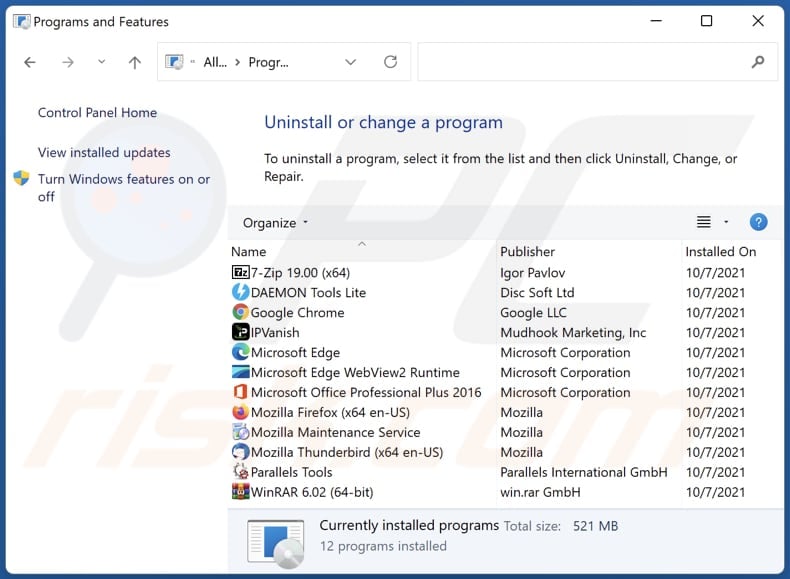
In the uninstall programs window, look for any unwanted applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the unwanted application, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove adware from Internet browsers:
Video showing how to remove unwanted browser add-ons:
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
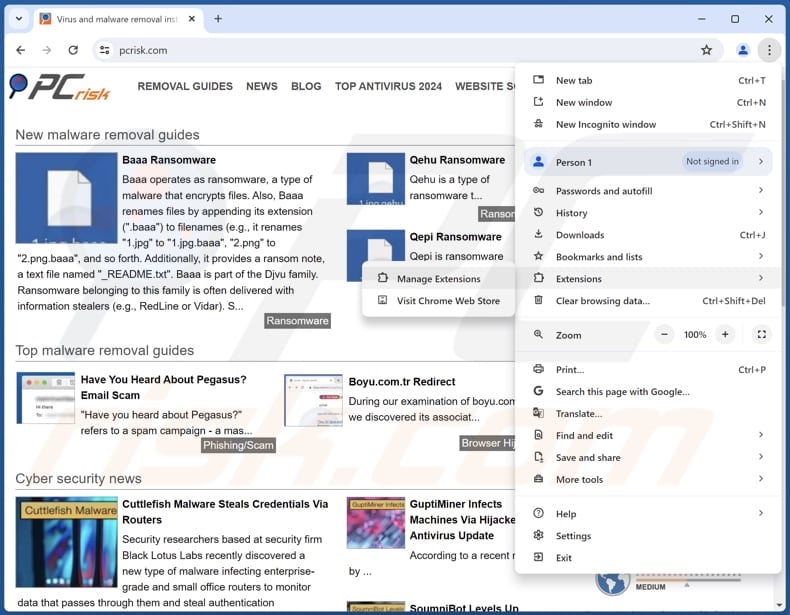
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate "Google Docs Offline" and other recently-installed suspicious extensions, select these entries and click "Remove".
(at the top right corner of Google Chrome), select "Extensions" and click "Manage Extensions". Locate "Google Docs Offline" and other recently-installed suspicious extensions, select these entries and click "Remove".
Optional method:
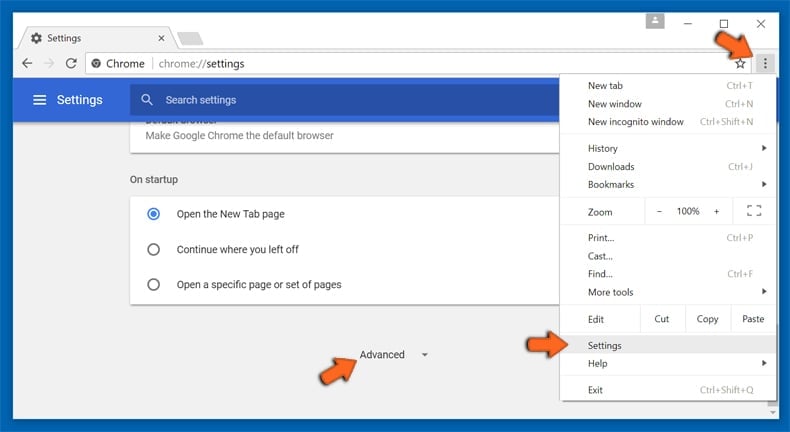
If you continue to have problems with removal of the google docs offline rat, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
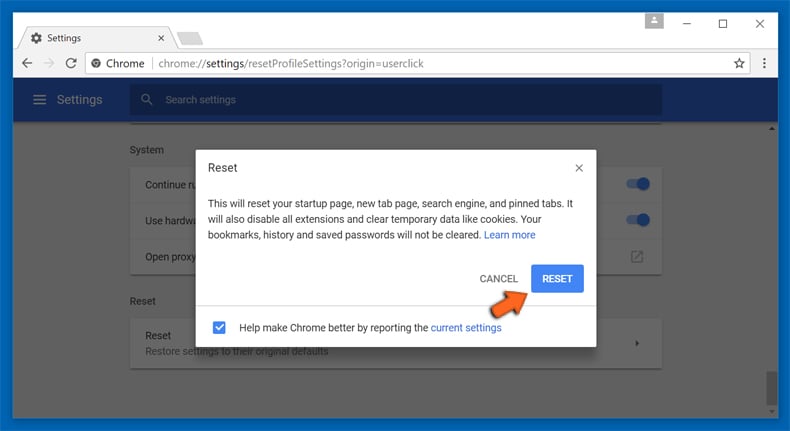
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
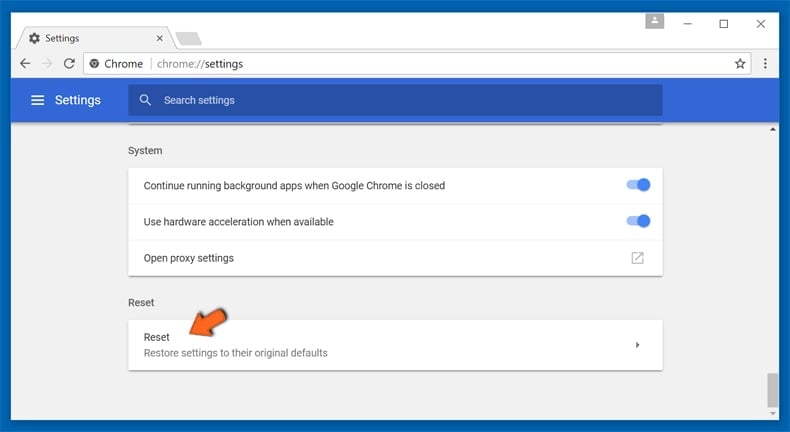
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious plug-ins from Mozilla Firefox:
Remove malicious plug-ins from Mozilla Firefox:
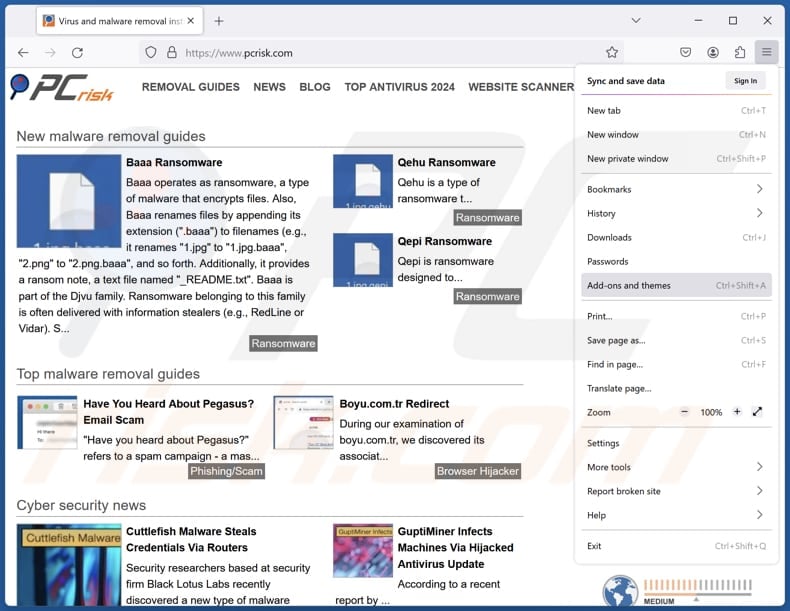
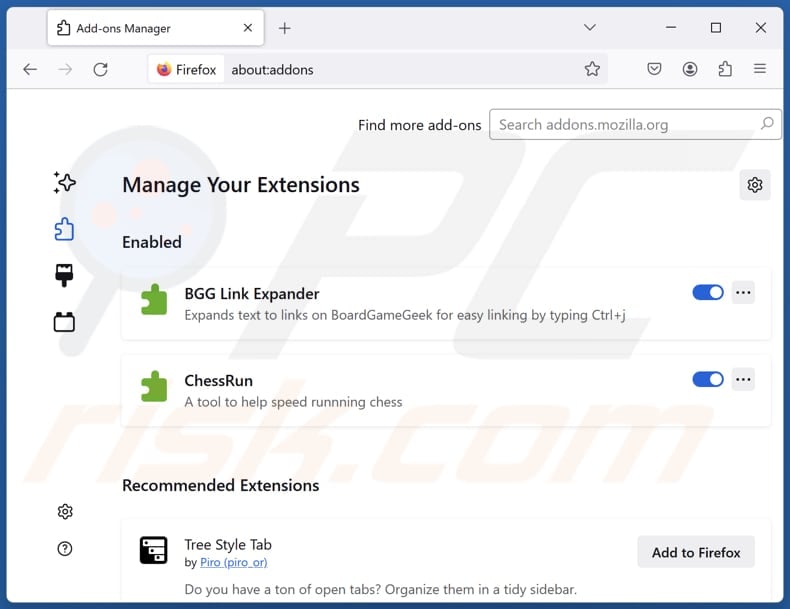
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
(at the top right corner of the main window), select "Add-ons and themes". Click "Extensions", in the opened window locate all recently-installed suspicious extensions, click on the three dots and then click "Remove".
Optional method:
Computer users who have problems with google docs offline rat removal can reset their Mozilla Firefox settings.
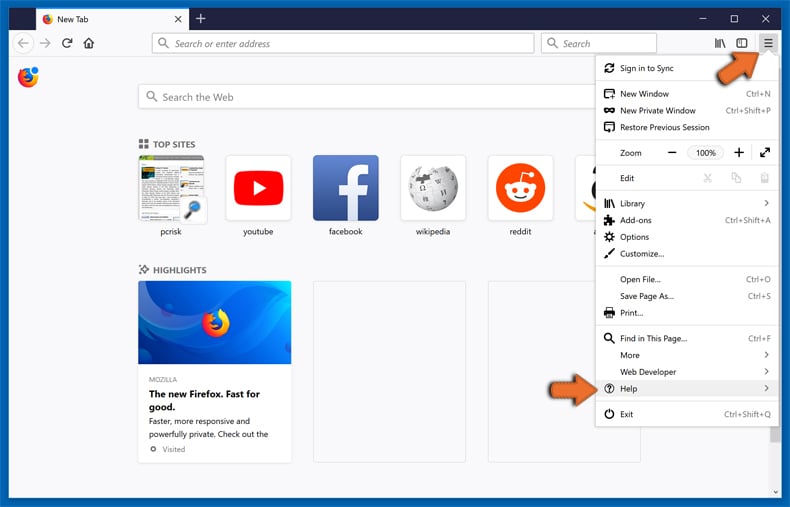
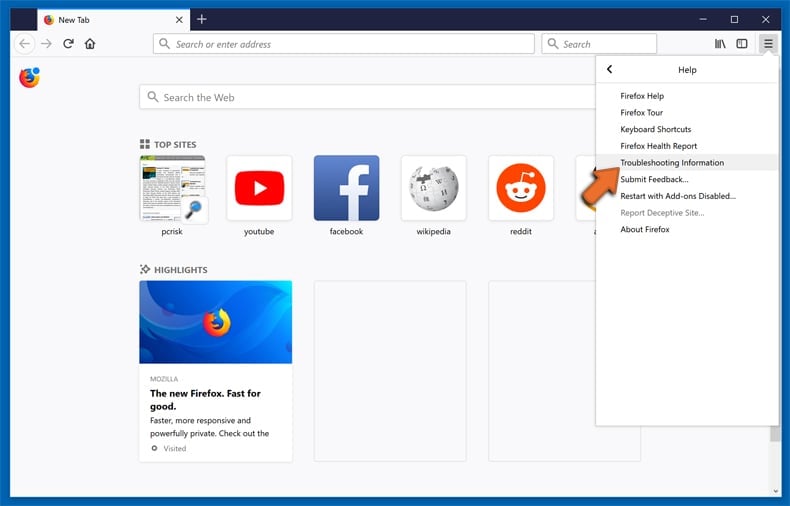
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
Select Troubleshooting Information.
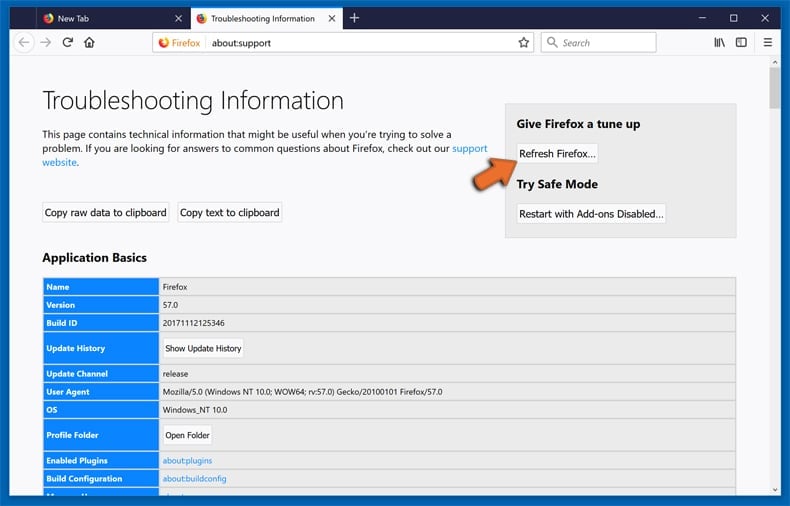
In the opened window, click the Refresh Firefox button.
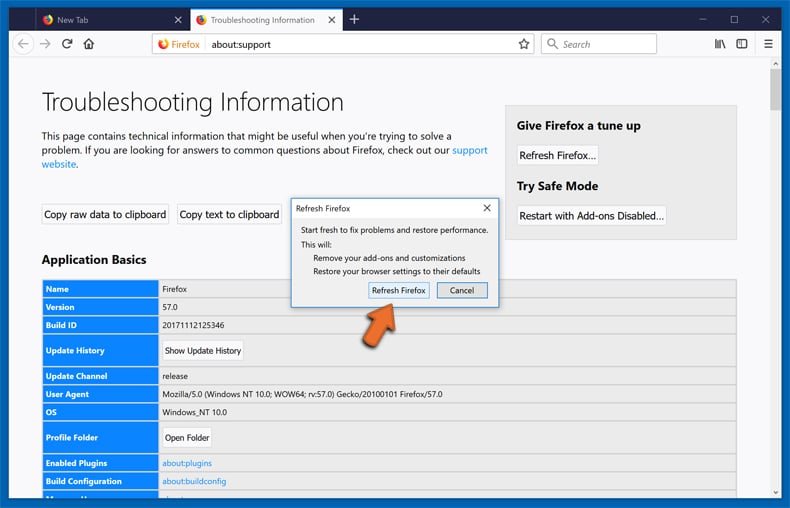
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
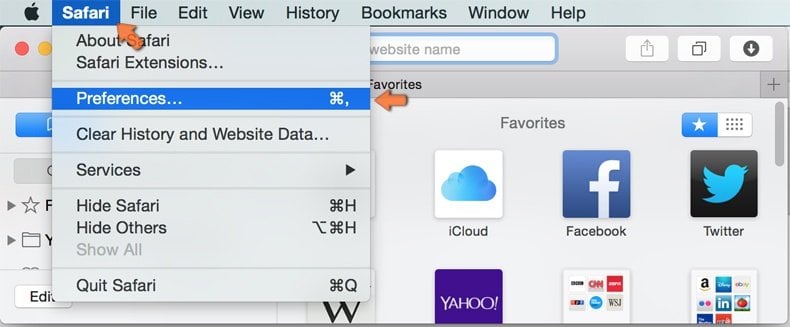
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
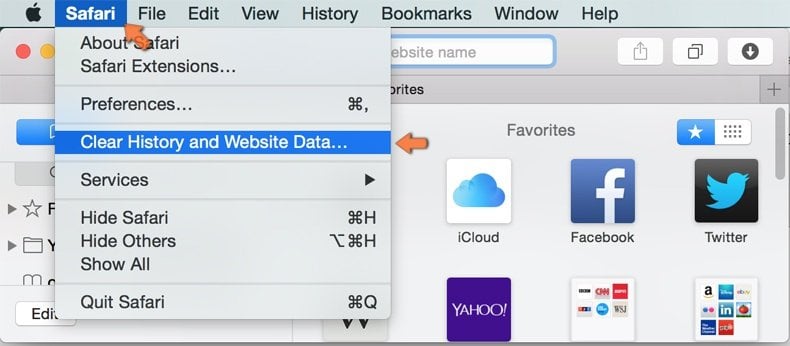
In the opened window select all history and click the Clear History button.

 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
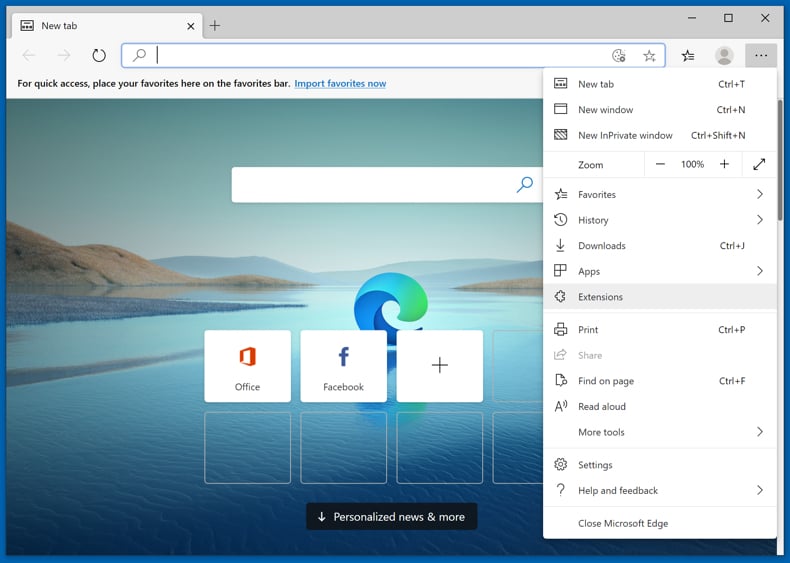
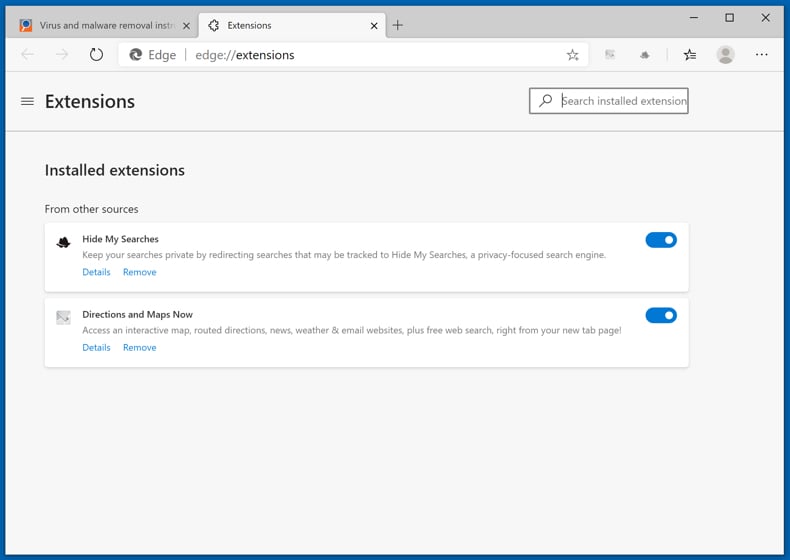
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
Optional method:
If you continue to have problems with removal of the google docs offline rat, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
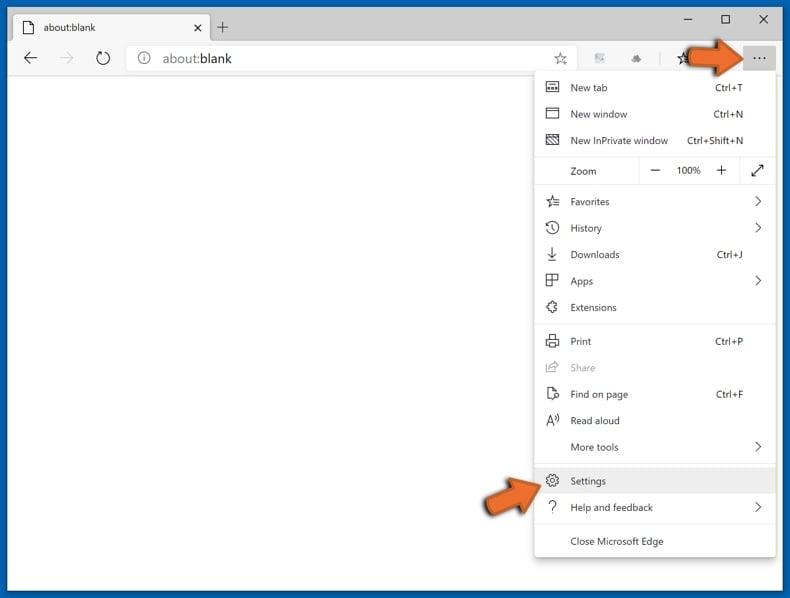
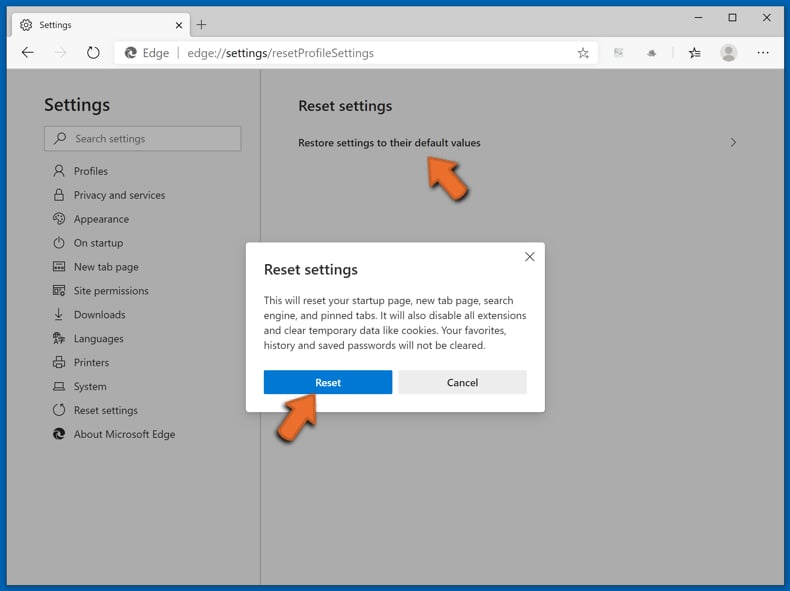
In the opened settings menu select Reset settings.
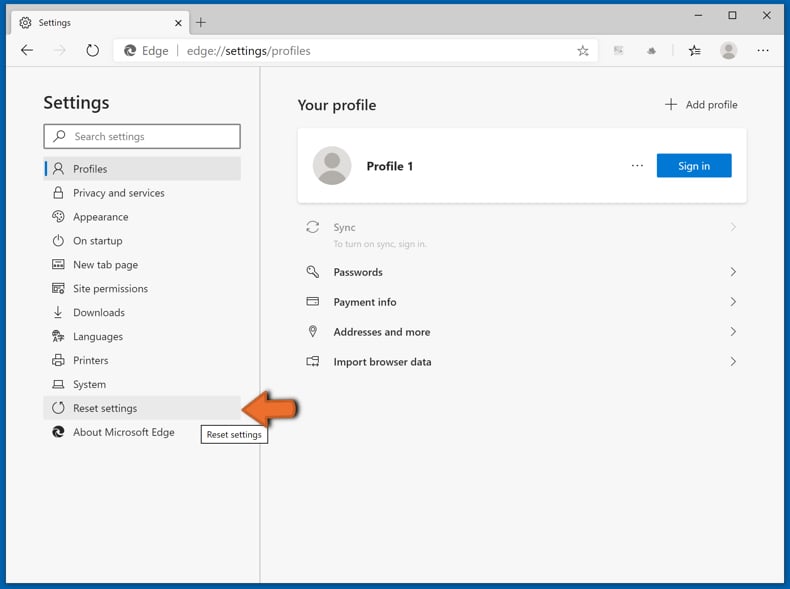
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
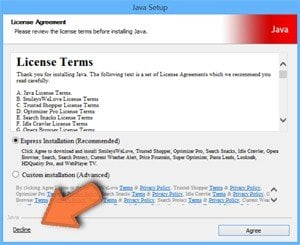 Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Post a comment:
If you have additional information on google docs offline rat or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
My browser is infected with the fake Google Docs Offline extension, should I format my storage device to get rid of it?
In most cases, victims do not need to format their storage device to remove a malicious Chrome extension like the fake Google Docs Offline one. Instead, users can remove it by resetting Chrome, deleting suspicious extensions, and scanning their system with a trusted antivirus/anti-malware tool like Combo Cleaner.
What are the biggest issues that malware can cause?
Cybercriminals can use malware to steal sensitive information, install extra malicious payloads, damage or delete important files, and remotely control the infected system. This can result in serious consequences such as identity theft, financial fraud, account compromise, data loss, and further malware infections.
What is the purpose of the fake Google Docs Offline extension?
The purpose of the fake Google Docs Offline extension is to act as a spyware tool inside the browser. It is designed to look legitimate while secretly collecting sensitive data like login sessions, browsing activity, and user input. It also allows attackers to remotely control the browser.
How did the fake Google Docs Offline extension infiltrate my device?
The fake Google Docs Offline extension spreads throug GitHub, npm, and extension stores. Malicious code is hidden inside normal-looking projects. When executed, the code activates and silently add the fake extension. It can also be delivered through fake or compromised update processes.
Will Combo Cleaner protect me from malware?
Combo Cleaner can remove many known malware, but some advanced threats may still be harder to detect. Because of this, running a full system scan is essential to inspect the device. It helps ensure that any hidden malware is found and eliminated.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion