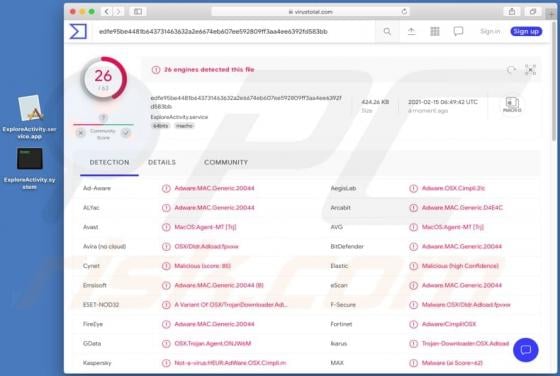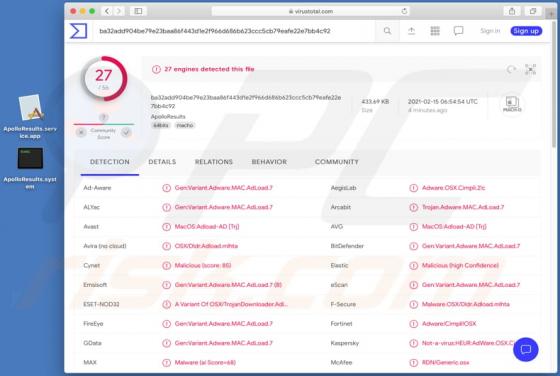
ApolloResults Adware (Mac)
ApolloResults displays advertisements and changes certain browser settings to promote a fake search engine. There is a high probability that it might also collect details relating to browsing activities and other information. This app is classified as adware and a browser hijacker. ApolloResult