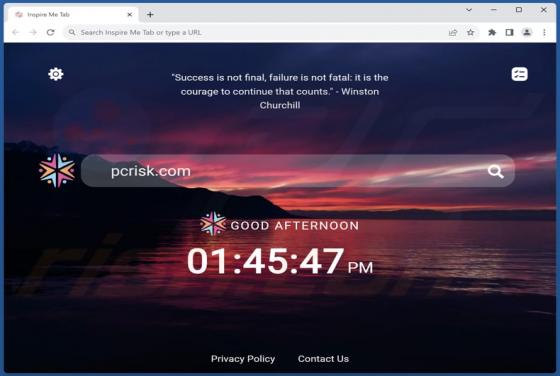
Inspire Me Tab Browser Hijacker
The examination of the Inspire Me Tab extension revealed its role as a browser hijacker. The primary objective of the Inspire Me Tab app is to seize control of a browser by manipulating its settings and promoting a fake search engine. Apps of this type should not be trusted and should be removed i