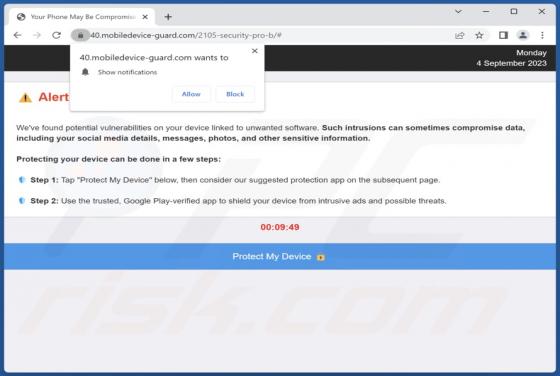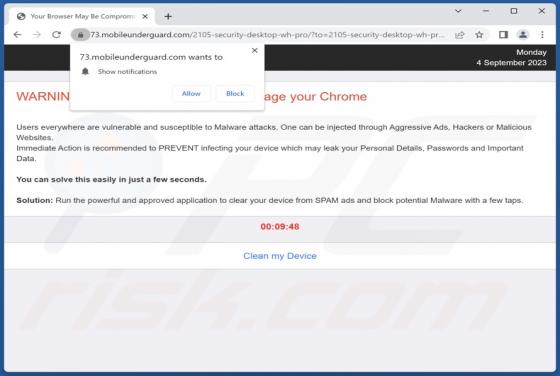
Mobileunderguard.com Ads
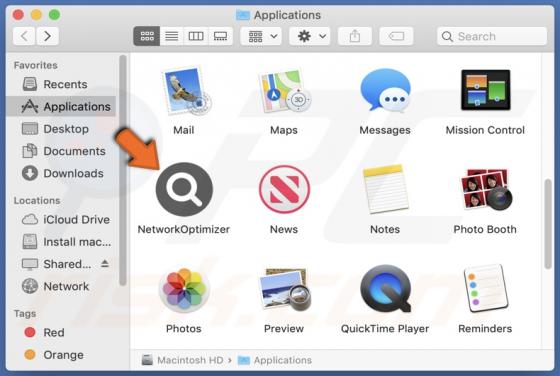
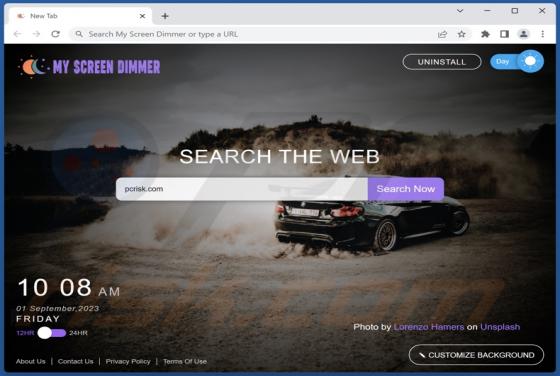
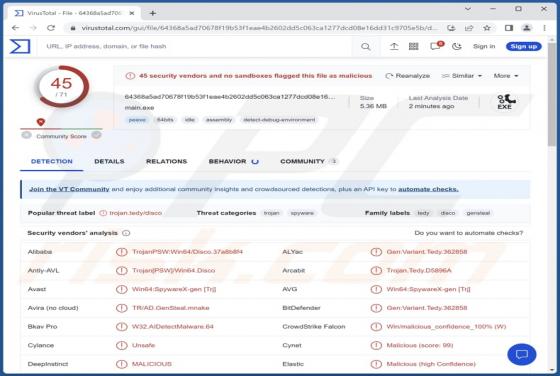
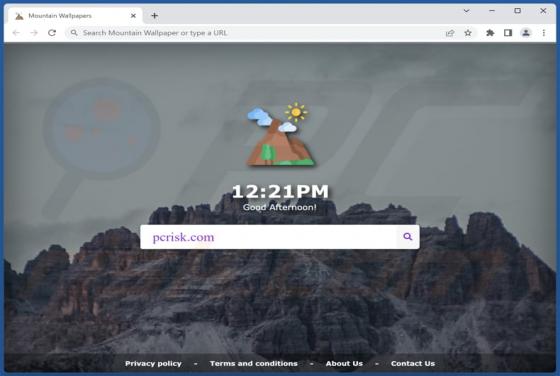
Our researchers found the mobileunderguard[.]com rogue webpage while checking suspicious sites. This page is designed to run scams and promote browser notification spam. Additionally, it can redirect visitors to different (likely unreliable/dangerous) websites. Most users access webpages like mob